SCS-C01 : AWS Certified Security – Specialty : Part 10
SCS-C01 : AWS Certified Security – Specialty : Part 10
-
A company’s web application is hosted on Amazon EC2 instances running behind an Application Load Balancer (ALB) in an Auto Scaling group. An AWS WAF web ACL is associated with the ALB. AWS CloudTrail is enabled, and stores logs in Amazon S3 and Amazon CloudWatch Logs.
The Operations team has observed some EC2 instances reboot at random. After rebooting, all access logs on the instances have been deleted. During an investigation, the Operations team found that each reboot happened just after a PHP error occurred on the new-user-creation.php file. The Operations team needs to view log information to determine if the company is being attacked.
Which set of actions will identify the suspect attacker’s IP address for future occurrences?
- Configure VPC Flow Logs on the subnet where the ALB is located, and stream the data CloudWatch. Search for the new-user-creation.php occurrences in CloudWatch.
- Configure the CloudWatch agent on the ALB. Configure the agent to send application logs to CloudWatch. Update the instance role to allow CloudWatch Logs access. Export the logs to CloudWatch. Search for the new-user-creation.php occurrences in CloudWatch.
- Configure the ALB to export access logs to an Amazon Elasticsearch Service cluster, and use the service to search for the new-user-creation.php occurrences.
- Configure the web ACL to send logs to Amazon Kinesis Data Firehose, which delivers the logs to an S3 bucket. Use Amazon Athena to query the logs and find the new-user-creation.php occurrences.
-
A company has hundreds of AWS accounts, and a centralized Amazon S3 bucket used to collect AWS CloudTrail logs for all of these accounts. A Security Engineer wants to create a solution that will enable the company to run ad hoc queries against its CloudTrail logs dating back 3 years from when the trails were first enabled in the company’s AWS account.
How should the company accomplish this with the least amount of administrative overhead?
- Run an Amazon EMR cluster that uses a MapReduce job to examine the CloudTrail trails.
- Use the events history feature of the CloudTrail console to query the CloudTrail trails.
- Write an AWS Lambda function to query the CloudTrail trails. Configure the Lambda function to be executed whenever a new file is created in the CloudTrail S3 bucket.
- Create an Amazon Athena table that looks at the S3 bucket the CloudTrail trails are being written to. Use Athena to run queries against the trails.
-
A Security Engineer is troubleshooting a connectivity issue between a web server that is writing log files to the logging server in another VPC. The Engineer has confirmed that a peering relationship exists between the two VPCs. VPC flow logs show that requests sent from the web server are accepted by the logging server, but the web server never receives a reply.
Which of the following actions could fix this issue?
- Add an inbound rule to the security group associated with the logging server that allows requests from the web server.
- Add an outbound rule to the security group associated with the web server that allows requests to the logging server.
- Add a route to the route table associated with the subnet that hosts the logging server that targets the peering connection.
- Add a route to the route table associated with the subnet that hosts the web server that targets the peering connection.
-
A Security Engineer accidentally deleted the imported key material in an AWS KMS CMK.
What should the Security Engineer do to restore the deleted key material?
- Create a new CMK. Download a new wrapping key and a new import token to import the original key material.
- Create a new CMK. Use the original wrapping key and import token to import the original key material.
- Download a new wrapping key and a new import token. Import the original key material into the existing CMK.
- Use the original wrapping key and import token. Import the original key material into the existing CMK.
-
A company’s Security Engineer is copying all application logs to centralized Amazon S3 buckets. Currently, each of the company’s application is in its own AWS account, and logs are pushed into S3 buckets associated with each account. The Engineer will deploy an AWS Lambda function into each account that copies the relevant log files to the centralized S3 bucket.
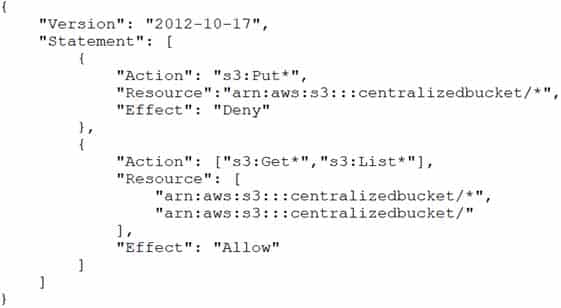
The Security Engineer is unable to access the log files in the centralized S3 bucket. The Engineer’s IAM user policy from the centralized account looks like this:
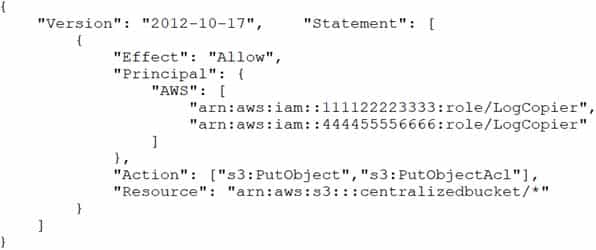
SCS-C01 AWS Certified Security – Specialty Part 10 Q05 033 The centralized S3 bucket policy looks like this:
SCS-C01 AWS Certified Security – Specialty Part 10 Q05 034 Why is the Security Engineer unable to access the log files?
- The S3 bucket policy does not explicitly allow the Security Engineer access to the objects in the bucket.
- The object ACLs are not being updated to allow the users within the centralized account to access the objects.
- The Security Engineer’s IAM policy does not grant permissions to read objects in the S3 bucket.
- The s3:PutObject and s3:PutObjectAcl permissions should be applied at the S3 bucket level.
-
An application running on Amazon EC2 instances generates log files in a folder on a Linux file system. The instances block access to the console and file transfer utilities, such as Secure Copy Protocol (SCP) and Secure File Transfer Protocol (SFTP). The Application Support team wants to automatically monitor the application log files so the team can set up notifications in the future.
A Security Engineer must design a solution that meets the following requirements:
– Make the log files available through an AWS managed service.
– Allow for automatic monitoring of the logs.
– Provide an interface for analyzing logs.
– Minimize effort.Which approach meets these requirements?
- Modify the application to use the AWS SDK. Write the application logs to an Amazon S3 bucket.
- Install the unified Amazon CloudWatch agent on the instances. Configure the agent to collect the application log files on the EC2 file system and send them to Amazon CloudWatch Logs.
- Install AWS Systems Manager Agent on the instances. Configure an automation document to copy the application log files to AWS DeepLens.
- Install Amazon Kinesis Agent on the instances. Stream the application log files to Amazon Kinesis Data Firehose and set the destination to Amazon Elasticsearch Service.
-
A company has multiple AWS accounts that are part of AWS Organizations. The company’s Security team wants to ensure that even those Administrators with full access to the company’s AWS accounts are unable to access the company’s Amazon S3 buckets.
How should this be accomplished?
- Use SCPs.
- Add a permissions boundary to deny access to Amazon S3 and attach it to all roles.
- Use an S3 bucket policy.
- Create a VPC endpoint for Amazon S3 and deny statements for access to Amazon S3.
-
A Security Engineer has several thousand Amazon EC2 instances split across production and development environments. Each instance is tagged with its environment. The Engineer needs to analyze and patch all the development EC2 instances to ensure they are not currently exposed to any common vulnerabilities or exposures (CVEs).
Which combination of steps is the MOST efficient way for the Engineer to meet these requirements? (Choose two.)
- Log on to each EC2 instance, check and export the different software versions installed, and verify this against a list of current CVEs.
- Install the Amazon Inspector agent on all development instances. Build a custom rule package, and configure Inspector to perform a scan using this custom rule on all instances tagged as being in the development environment.
- Install the Amazon Inspector agent on all development instances. Configure Inspector to perform a scan using this CVE rule package on all instances tagged as being in the development environment.
- Install the Amazon EC2 System Manager agent on all development instances. Issue the Run command to EC2 System Manager to update all instances.
- Use AWS Trusted Advisor to check that all EC2 instances have been patched to the most recent version of operating system and installed software.
-
A company has decided to use encryption in its AWS account to secure the objects in Amazon S3 using server-side encryption. Object sizes range from 16,000 B to 5 MB. The requirements are as follows:
– The key material must be generated and stored in a certified Federal Information Processing Standard (FIPS) 140-2 Level 3 machine.
– The key material must be available in multiple Regions.Which option meets these requirements?
- Use an AWS KMS customer managed key and store the key material in AWS with replication across Regions.
- Use an AWS customer managed key, import the key material into AWS KMS using in-house AWS CloudHSM, and store the key material securely in Amazon S3.
- Use an AWS KMS custom key store backed by AWS CloudHSM clusters, and copy backups across Regions.
- Use AWS CloudHSM to generate the key material and backup keys across Regions. Use the Java Cryptography Extension (JCE) and Public Key Cryptography Standards #11 (PKCS #11) encryption libraries to encrypt and decrypt the data.
-
An organization has a multi-petabyte workload that it is moving to Amazon S3, but the CISO is concerned about cryptographic wear-out and the blast radius if a key is compromised.
How can the CISO be assured that AWS KMS and Amazon S3 are addressing the concerns? (Choose two.)
- There is no API operation to retrieve an S3 object in its encrypted form.
- Encryption of S3 objects is performed within the secure boundary of the KMS service.
- S3 uses KMS to generate a unique data key for each individual object.
- Using a single master key to encrypt all data includes having a single place to perform audits and usage validation.
- The KMS encryption envelope digitally signs the master key during encryption to prevent cryptographic wear-out.
-
A company has a compliance requirement to rotate its encryption keys on an annual basis. A Security Engineer needs a process to rotate the KMS Customer Master Keys (CMKs) that were created using imported key material.
How can the Engineer perform the key rotation process MOST efficiently?
- Create a new CMK, and redirect the existing Key Alias to the new CMK.
- Select the option to auto-rotate the key.
- Upload new key material into the existing CMK.
- Create a new CMK, and change the application to point to the new CMK.
-
A company’s Chief Security Officer has requested that a Security Analyst review and improve the security posture of each company AWS account. The Security Analyst decides to do this by improving AWS account root user security.
Which actions should the Security Analyst take to meet these requirements? (Choose three.)
- Delete the access keys for the account root user in every account.
- Create an admin IAM user with administrative privileges and delete the account root user in every account.
- Implement a strong password to help protect account-level access to the AWS Management Console by the account root user.
- Enable multi-factor authentication (MFA) on every account root user in all accounts.
- Create a custom IAM policy to limit permissions to required actions for the account root user and attach the policy to the account root user.
- Attach an IAM role to the account root user to make use of the automated credential rotation in AWS STS.
-
A large company wants its Compliance team to audit its Amazon S3 buckets to identify if personally identifiable information (PII) is stored in them. The company has hundreds of S3 buckets and has asked the Security Engineers to scan every bucket.
How can this task be accomplished?
- Configure Amazon CloudWatch Events to trigger Amazon Inspector to scan the S3 buckets daily for PII. Configure Amazon Inspector to publish Amazon SNS notifications to the Compliance team if PII is detected.
- Configure Amazon Macie to classify data in the S3 buckets and check the dashboard for PII findings. Configure Amazon CloudWatch Events to capture Macie alerts and target an Amazon SNS topic to be notified if PII is detected.
- Check the AWS Trusted Advisor data loss prevention page in the AWS Management Console. Download the Amazon S3 data confidentiality report and send it to the Compliance team. Configure Amazon CloudWatch Events to capture Trusted Advisor alerts and target an Amazon SNS topic to be notified if PII is detected.
- Enable Amazon GuardDuty in multiple Regions to scan the S3 buckets. Configure Amazon CloudWatch Events to capture GuardDuty alerts and target an Amazon SNS topic to be notified if PII is detected.
-
During a manual review of system logs from an Amazon Linux EC2 instance, a Security Engineer noticed that there are sudo commands that were never properly alerted or reported on the Amazon CloudWatch Logs agent.
Why were there no alerts on the sudo commands?
- There is a security group blocking outbound port 80 traffic that is preventing the agent from sending the logs.
- The IAM instance profile on the EC2 instance was not properly configured to allow the CloudWatch Logs agent to push the logs to CloudWatch.
- CloudWatch Logs status is set to ON versus SECURE, which prevents if from pulling in OS security event logs.
- The VPC requires that all traffic go through a proxy, and the CloudWatch Logs agent does not support a proxy configuration.
-
A company has an AWS account and allows a third-party contractor, who uses another AWS account, to assume certain IAM roles. The company wants to ensure that IAM roles can be assumed by the contractor only if the contractor has multi-factor authentication enabled on their IAM user accounts.
What should the company do to accomplish this?
- Add the following condition to the IAM policy attached to all IAM roles “Effect”: “Deny”,”Condition” : { “BoolItExists” : { “aws:MultiFactorAuthPresent” : false } }
- Add the following condition to the IAM policy attached to all IAM roles:
"Effect": "Deny", "Condition" : { "Bool" : { "aws:MultiFactorAuthPresent" : false } } - Add the following condition to the IAM policy attached to all IAM roles:
"Effect": "Allow", "Condition" : { "Null" : { "aws:MultiFactorAuthPresent" : false } } - Add the following condition to the IAM policy attached to all IAM roles:
"Effect": "Allow", "Condition" : { "BoolItExists" : { "aws:MultiFactorAuthPresent" : false } }
-
A large corporation is creating a multi-account strategy and needs to determine how its employees should access the AWS Infrastructure.
Which of the following solutions would provide the MOST scalable solution?
- Create dedicated IAM users within each AWS account that employees can assume though federation based upon group membership in their existing identity provider.
- Use a centralized account with IAM roles that employees can assume through federation with their existing identity provider. Use cross-account roles to allow the federated users to assume their target role in the resource accounts.
- Configure the AWS Security Token Service to use Kerberos tokens so that users can use their existing corporate user names and passwords to access AWS resources directly.
- Configure the IAM trust policies within each account’s role to set up a trust back to the corporation’s existing identity provider, allowing users to assume the role based off their SAML token.
-
A company wants to deploy a distributed web application on a fleet of EC2 instances. The fleet will be fronted by a Classic Load Balancer that will be configured to terminate the TLS connection. The company wants to make sure that all past and current TLS traffic to the Classic Load Balancer stays secure, even if the certificate private key is leaked.
To ensure the company meets these requirements, a Security Engineer can configure a Classic Load Balancer with:
- An HTTPS listener that uses a certificate that is managed by Amazon Certification Manager.
- An HTTPS listener that uses a custom security policy that allows only perfect forward secrecy cipher suites.
- An HTTPS listener that uses the latest AWS predefined ELBSecurityPolicy-TLS-1-2-2017-01 security policy.
- A TCP listener that uses a custom security policy that allows only perfect forward secrecy cipher suites.
-
Users report intermittent availability of a web application hosted on AWS. Monitoring systems report an excess of abnormal network traffic followed by high CPU utilization on the application web tier.
Which of the following techniques will improve the availability of the application? (Choose two.)
- Deploy AWS WAF to block all unsecured web applications from accessing the internet.
- Deploy an Intrusion Detection/Prevention Systems (IDS/IPS) to monitor or block unusual incoming network traffic.
- Configure security groups to allow outgoing network traffic only from hosts that are protected with up-to-date antivirus software.
- Create Amazon CloudFront distribution and configure AWS WAF rules to protect the web applications from malicious traffic.
- Use the default Amazon VPC for external-facing systems to allow AWS to actively block malicious network traffic affecting Amazon EC2 instances.
-
A company has an application hosted in an Amazon EC2 instance and wants the application to access secure strings stored in AWS Systems Manager Parameter Store. When the application tries to access the secure string key value, it fails.
Which factors could be the cause of this failure? (Choose two.)
- The EC2 instance role does not have decrypt permissions on the AWS Key Management Service (AWS KMS) key used to encrypt the secret.
- The EC2 instance role does not have read permissions to read the parameters in Parameter Store.
- Parameter Store does not have permission to use AWS Key Management Service (AWS KMS) to decrypt the parameter.
- The EC2 instance role does not have encrypt permissions on the AWS Key Management Service (AWS KMS) key associated with the secret.
- The EC2 instance does not have any tags asso
-
A security engineer received an Amazon GuardDuty alert indicating a finding involving the Amazon EC2 instance that hosts the company’s primary website. The GuardDuty finding received read:
UnauthorizedAccess:IAMUser/InstanceCredentialExfiltration.
The security engineer confirmed that a malicious actor used API access keys intended for the EC2 instance from a country where the company does not operate. The security engineer needs to deny access to the malicious actor.
What is the first step the security engineer should take?
- Open the EC2 console and remove any security groups that allow inbound traffic from 0.0.0.0/0.
- Install the AWS Systems Manager Agent on the EC2 instance and run an inventory report.
- Install the Amazon Inspector agent on the host and run an assessment with the CVE rules package.
- Open the IAM console and revoke all IAM sessions that are associated with the instance profile.