NetAcad Cisco CCNA 1 v7 and ITN v7.02 Modules 1 – 3 Exam Answers 100% in 2023 and 2024
Discover the definitive collection of NetAcad Cisco CCNA 1 v7 and ITN v7.02 Modules 1 – 3 exam answers for 2023 and 2024. This resource includes all questions and expertly verified answers for the ITN (Version 7.00) – Basic Network Connectivity and Communications exams. With a focus on providing accurate and comprehensive solutions, this guide ensures you achieve a full 100% mark. Perfect for students and professionals alike, these answers will bolster your understanding of networking fundamentals and help you excel in your Cisco certification exams. Dive in to prepare thoroughly and succeed with confidence.
ITN (Version 7.00) – Basic Network Connectivity and Communications Exam Answers 2023 2024 Full 100%
In the show running-config command, which part of the syntax is represented by running-config ?
- the command
- a keyword
- a variable
- a prompt
In the show running-config command, the part of the syntax represented by running-config is:
A keyword Here’s a detailed explanation for each option:
So, within the |
An employee at a branch office is creating a quote for a customer. In order to do this, the employee needs to access confidential pricing information from internal servers at the Head Office. What type of network would the employee access?
- an intranet
- the Internet
- an extranet
- a local area network
| In this scenario, the employee at a branch office would access:
An intranet Here’s an explanation of each option:
Therefore, the appropriate type of network the employee would access is an intranet. |
Which statement describes the use of powerline networking technology?
- New “smart” electrical cabling is used to extend an existing home LAN.
- A home LAN is installed without the use of physical cabling.
- A device connects to an existing home LAN using an adapter and an existing electrical outlet.
- Wireless access points use powerline adapters to distribute data through the home LAN.
| The statement that describes the use of powerline networking technology is:
A device connects to an existing home LAN using an adapter and an existing electrical outlet. Here’s an explanation of each option:
Therefore, the correct statement is: A device connects to an existing home LAN using an adapter and an existing electrical outlet. |
Match the requirements of a reliable network with the supporting network architecture. (Not all options are used.)
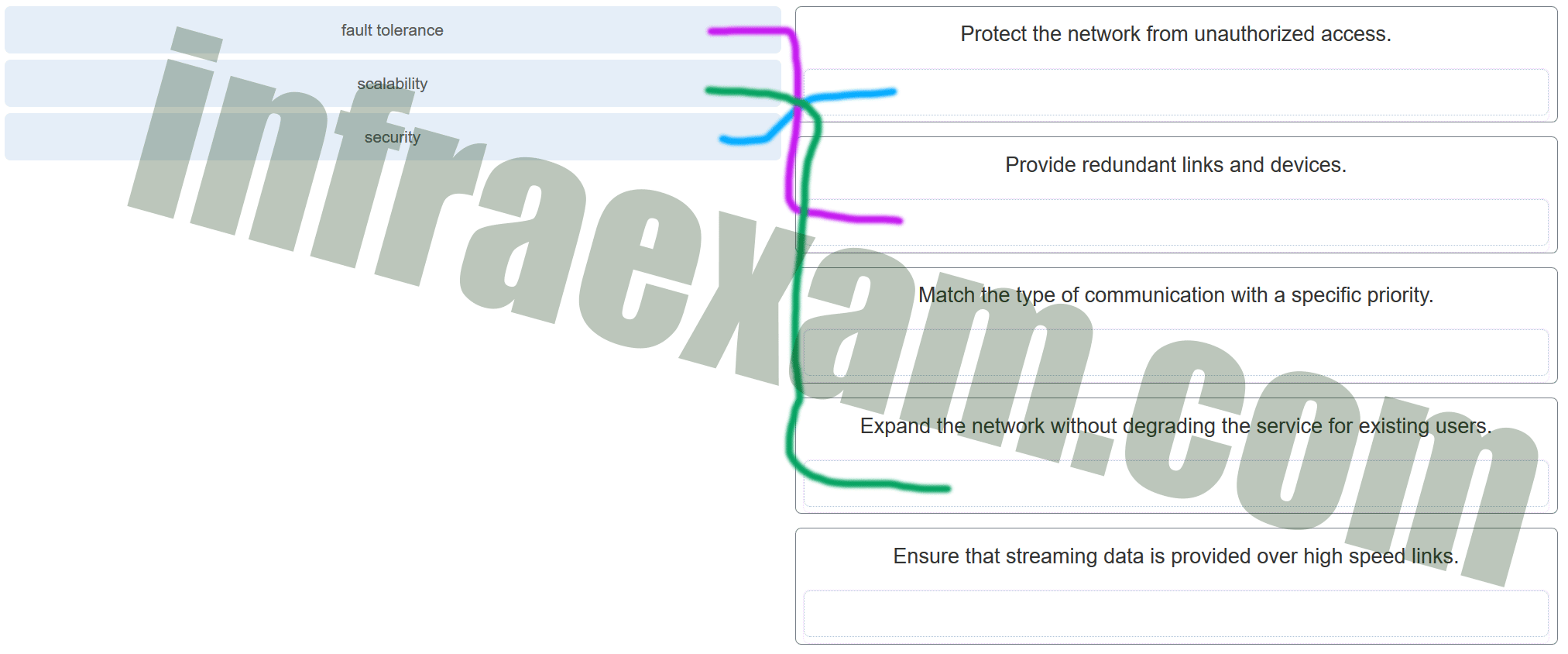
- fault tolerance ==> Provide redundant links and devices.
- scalability ==> Expand the network without degrading the service for existing users.
- security ==> Protect the network from unauthorized access.
- Not Matched ==> Match the type of communication with a specific priority.
- Not Matched ==> Ensure that streaming data is provided over high speed links.
Fault Tolerance ==> Provide redundant links and devices.
Scalability ==> Expand the network without degrading the service for existing users.
Security ==> Protect the network from unauthorized access.
Not Matched ==> Match the type of communication with a specific priority.
Not Matched ==> Ensure that streaming data is provided over high speed links.
By providing redundant links and devices, expanding the network without degrading service, and protecting against unauthorized access, a reliable network can achieve fault tolerance, scalability, and security. Matching communication types with specific priorities and ensuring high-speed links for streaming data are also important but were not matched in this context. |
A networking technician is working on the wireless network at a medical clinic. The technician accidentally sets up the wireless network so that patients can see the medical records data of other patients. Which of the four network characteristics has been violated in this situation?
- fault tolerance
- scalability
- security
- Quality of Service (QoS)
- reliability
| In this situation, the network characteristic that has been violated is:
Security Explanation:
Therefore, the violation pertains to Security, as it involves unauthorized access to sensitive and confidential medical records. |
Match each characteristic to its corresponding Internet connectivity type. (Not all options are used.)
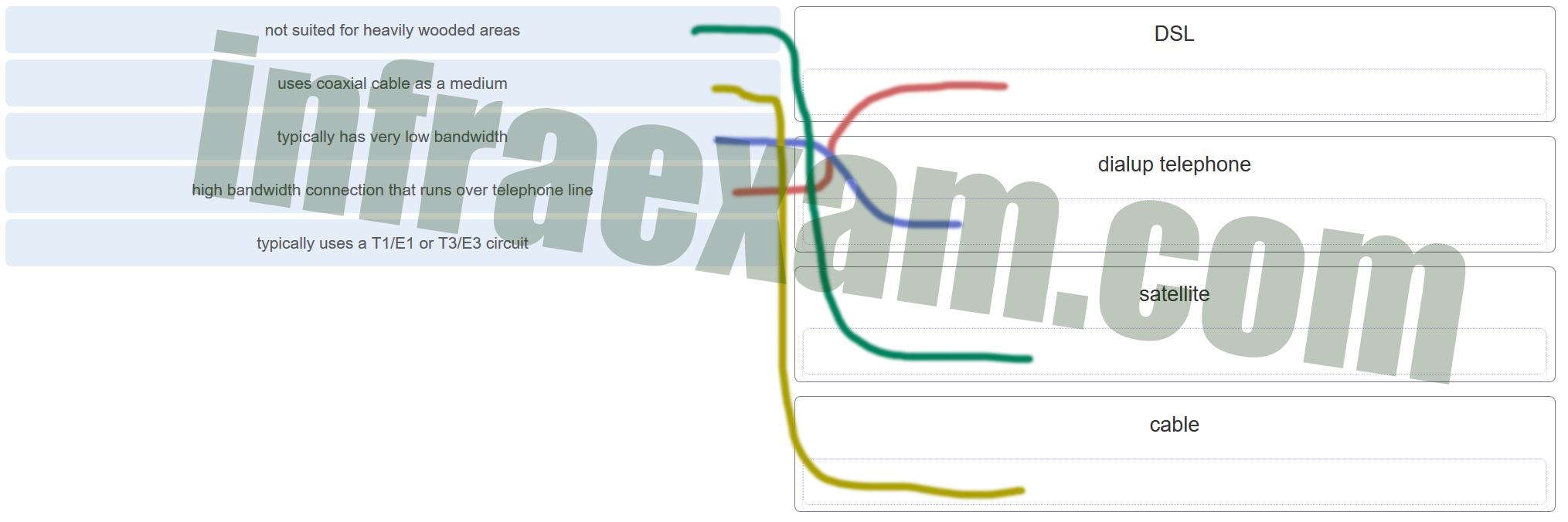
- not suited for heavily wooded areas ==> satellite
- uses coaxial cable as a medium ==> cable
- typically has very low bandwidth ==> dialup telephone
- high bandwidth connection that runs over telephone line ==> DSL
- typically uses a T1/E1 or T3/E3 circuit ==> Not Macth
Not suited for heavily wooded areas ==> Satellite
Uses coaxial cable as a medium ==> Cable
Typically has very low bandwidth ==> Dial-up telephone
High bandwidth connection that runs over telephone line ==> DSL
Typically uses a T1/E1 or T3/E3 circuit ==> Not Matched
|
What two criteria are used to help select a network medium from various network media? (Choose two.)
- the types of data that need to be prioritized
- the cost of the end devices utilized in the network
- the distance the selected medium can successfully carry a signal
- the number of intermediate devices installed in the network
- the environment where the selected medium is to be installed
The types of data that need to be prioritized:
The cost of the end devices utilized in the network:
The distance the selected medium can successfully carry a signal:
The number of intermediate devices installed in the network:
The environment where the selected medium is to be installed:
To summarize, the primary criteria for selecting a network medium are:
|
What type of network traffic requires QoS?
- on-line purchasing
- video conferencing
- wiki
| The type of network traffic that requires Quality of Service (QoS) is:
Video Conferencing Explanation:
Thus, the correct answer is video conferencing. |
A user is implementing security on a small office network. Which two actions would provide the minimum security requirements for this network? (Choose two.)
- implementing a firewall
- installing a wireless network
- installing antivirus software
- implementing an intrusion detection system
- adding a dedicated intrusion prevention device
To provide the minimum security requirements for a small office network, the two actions that should be implemented are:
Other options explained:
Thus, the two actions providing the minimum security requirements are:
|
Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.)
- VTY interface
- console interface
- Ethernet interface
- boot IOS mode
- privileged EXEC mode
- router configuration mode
Passwords can be used to restrict access to specific modes and interfaces of the Cisco IOS. The modes and interfaces that can be protected with passwords are:
Other options explained:
Therefore, the modes and interfaces that can be protected with passwords are:
|
Which interface allows remote management of a Layer 2 switch?
- the AUX interface
- the console port interface
- the switch virtual interface
- the first Ethernet port interface
| The interface that allows remote management of a Layer 2 switch is:
The switch virtual interface (SVI) Explanation:
Therefore, the correct answer is the switch virtual interface (SVI). |
What function does pressing the Tab key have when entering a command in IOS?
- It aborts the current command and returns to configuration mode.
- It exits configuration mode and returns to user EXEC mode.
- It moves the cursor to the beginning of the next line.
- It completes the remainder of a partially typed word in a command.
| Pressing the Tab key when entering a command in IOS:
It completes the remainder of a partially typed word in a command. Explanation:
Therefore, the correct answer is: It completes the remainder of a partially typed word in a command. |
While trying to solve a network issue, a technician made multiple changes to the current router configuration file. The changes did not solve the problem and were not saved. What action can the technician take to discard the changes and work with the file in NVRAM?
- Issue the reload command without saving the running configuration.
- Delete the vlan.dat file and reboot the device.
- Close and reopen the terminal emulation software.
- Issue the copy startup-config running-config command.
| To discard the changes made to the current router configuration file and revert to the configuration stored in NVRAM, the technician should:
Issue the reload command without saving the running configuration. Explanation:
Therefore, the correct action is to issue the reload command without saving the running configuration. |
An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?
- to restart the ping process
- to interrupt the ping process
- to exit to a different configuration mode
- to allow the user to complete the command
| An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command:
To interrupt the ping process Explanation:
Therefore, the purpose of using the Ctrl-Shift-6 key combination is to interrupt the ping process. |
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?
- letmein
- secretin
- lineconin
- linevtyin
| To determine which password is needed to access user EXEC mode via a console connection to switch SW1, let’s examine the configuration snippet provided in the exhibit.
Here is the configuration typically shown in such scenarios: enable secret secretin line con 0 password lineconin login line vty 0 4 password linevtyin login Based on this configuration:
Given this information:
Therefore, the password needed to access user EXEC mode via a console connection is lineconin. |
A technician configures a switch with these commands:
SwitchA(config)# interface vlan 1
SwitchA(config-if)# ip address 192.168.1.1 255.255.255.0
SwitchA(config-if)# no shutdown
What is the technician configuring?
- Telnet access
- SVI
- password encryption
- physical switchport access
| The technician is configuring:
SVI (Switch Virtual Interface) Explanation:
Therefore, the technician is configuring an SVI (Switch Virtual Interface). |
Which command or key combination allows a user to return to the previous level in the command hierarchy?
- end
- exit
- Ctrl-Z
- Ctrl-C
| The command that allows a user to return to the previous level in the command hierarchy is:
exit Explanation:
Therefore, the command to return to the previous level in the command hierarchy is exit. |
What are two characteristics of RAM on a Cisco device? (Choose two.)
- RAM provides nonvolatile storage.
- The configuration that is actively running on the device is stored in RAM.
- The contents of RAM are lost during a power cycle.
- RAM is a component in Cisco switches but not in Cisco routers.
- RAM is able to store multiple versions of IOS and configuration files.
The two characteristics of RAM on a Cisco device are:
Other options explained:
Therefore, the correct characteristics are:
|
Which two host names follow the guidelines for naming conventions on Cisco IOS devices? (Choose two.)
- Branch2!
- RM-3-Switch-2A4
- Floor(15)
- HO Floor 17
- SwBranch799
The two host names that follow the guidelines for naming conventions on Cisco IOS devices are:
Explanation: Cisco IOS naming conventions typically require that host names:
Here are the details for each option:
Therefore, the correct host names are RM-3-Switch-2A4 and SwBranch799. |
How is SSH different from Telnet?
- SSH makes connections over the network, whereas Telnet is for out-of-band access.
- SSH provides security to remote sessions by encrypting messages and using user authentication. Telnet is considered insecure and sends messages in plaintext.
- SSH requires the use of the PuTTY terminal emulation program. Tera Term must be used to connect to devices through the use of Telnet.
- SSH must be configured over an active network connection, whereas Telnet is used to connect to a device from a console connection.
| The key difference between SSH and Telnet is:
SSH provides security to remote sessions by encrypting messages and using user authentication. Telnet is considered insecure and sends messages in plaintext. Explanation:
Therefore, the correct statement is: SSH provides security to remote sessions by encrypting messages and using user authentication. Telnet is considered insecure and sends messages in plaintext. |
An administrator is configuring a switch console port with a password. In what order will the administrator travel through the IOS modes of operation in order to reach the mode in which the configuration commands will be entered? (Not all options are used.)
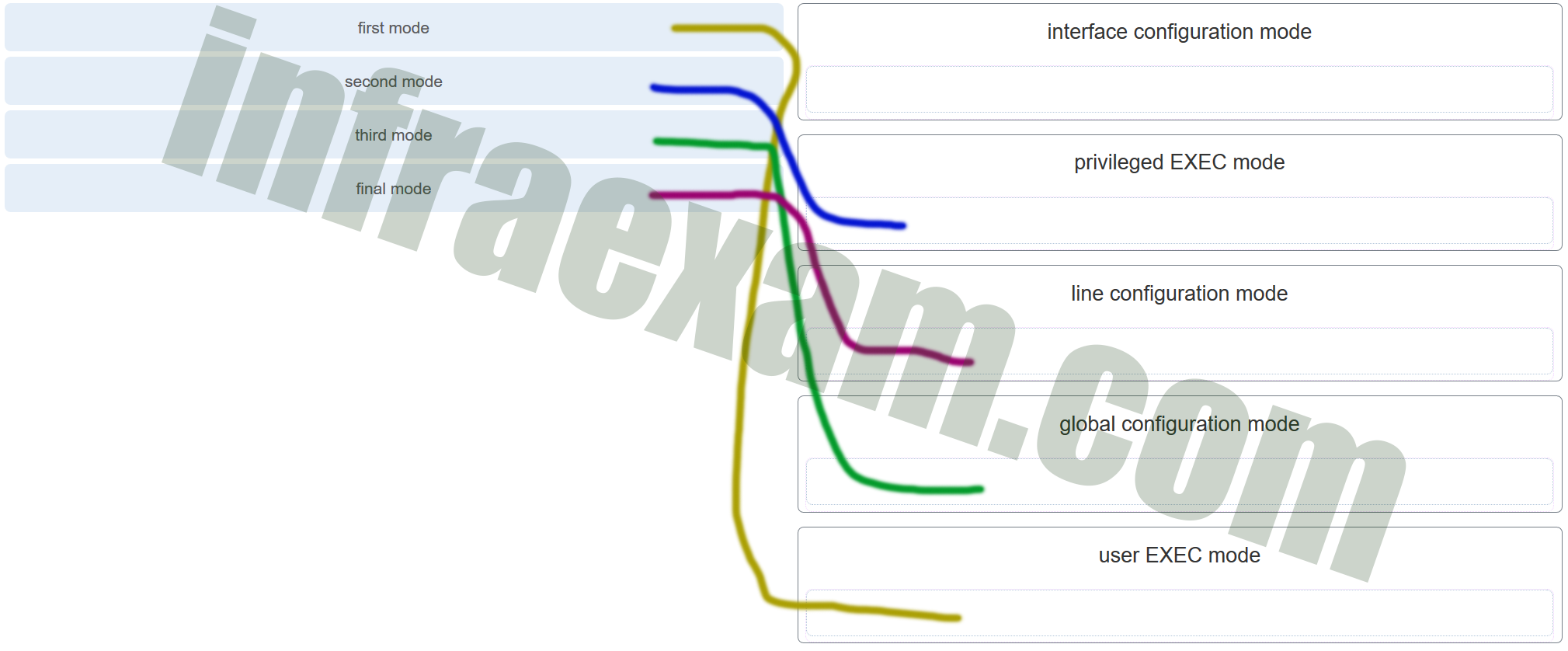
Match the description with the associated IOS mode. (Not all options are used.)
- first mode ==> user EXEC mode
- second mode ==> privileged EXEC mode
- third mode ==> global configuration mode
- final mode ==>line configuration mode
- interface configuration mode ==> Not Match
To configure a switch console port with a password, the administrator will travel through the following IOS modes of operation in this order:
The correct sequence to reach the mode in which the configuration commands will be entered is:
Therefore, the path through the modes is:
|
What are three characteristics of an SVI? (Choose three.)
- It is designed as a security protocol to protect switch ports.
- It is not associated with any physical interface on a switch.
- It is a special interface that allows connectivity by different types of media.
- It is required to allow connectivity by any device at any location.
- It provides a means to remotely manage a switch.
- It is associated with VLAN1 by default.
The three characteristics of an SVI (Switch Virtual Interface) are:
Other options explained:
Therefore, the correct characteristics of an SVI are:
|
What command is used to verify the condition of the switch interfaces, including the status of the interfaces and a configured IP address?
- ipconfig
- ping
- traceroute
- show ip interface brief
| The command used to verify the condition of the switch interfaces, including the status of the interfaces and a configured IP address, is:
show ip interface brief Explanation:
Therefore, the correct command is: show ip interface brief |
Match the description with the associated IOS mode. (Not all options are used.)
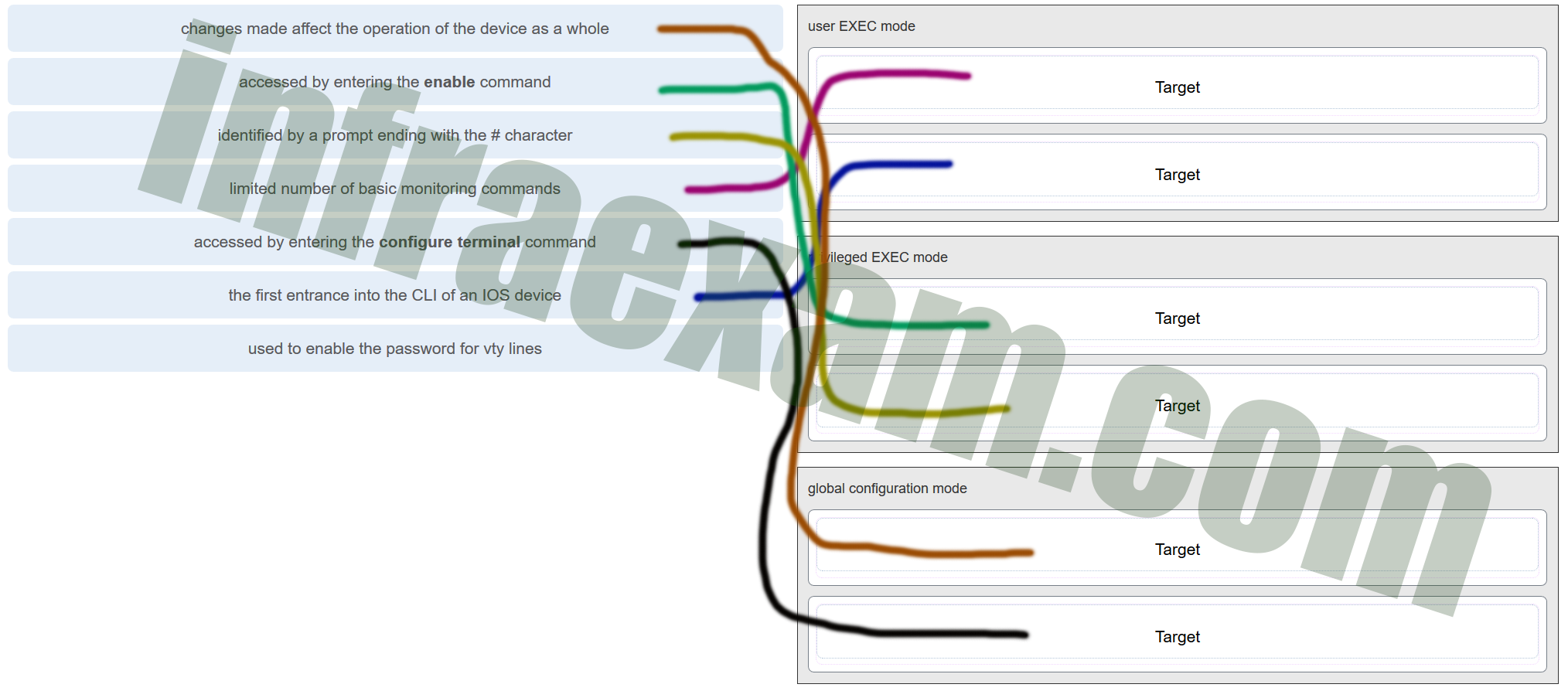
- changes made affect the operation of the device as a whole ==> global configuration mode
- accessed by entering the enable command ==> privileged EXEC mode
- identified by a prompt ending with the # character ==> privileged EXEC mode
- limited number of basic monitoring commands ==> user EXEC mode
- accessed by entering the configure terminal command ==> global configuration mode
- the first entrance into the CLI of an IOS device ==> user EXEC mode
- used to enable the password for vty lines ==> Not Match
Therefore, the matches are:
|
Match the definitions to their respective CLI hot keys and shortcuts. (Not all options are used.)
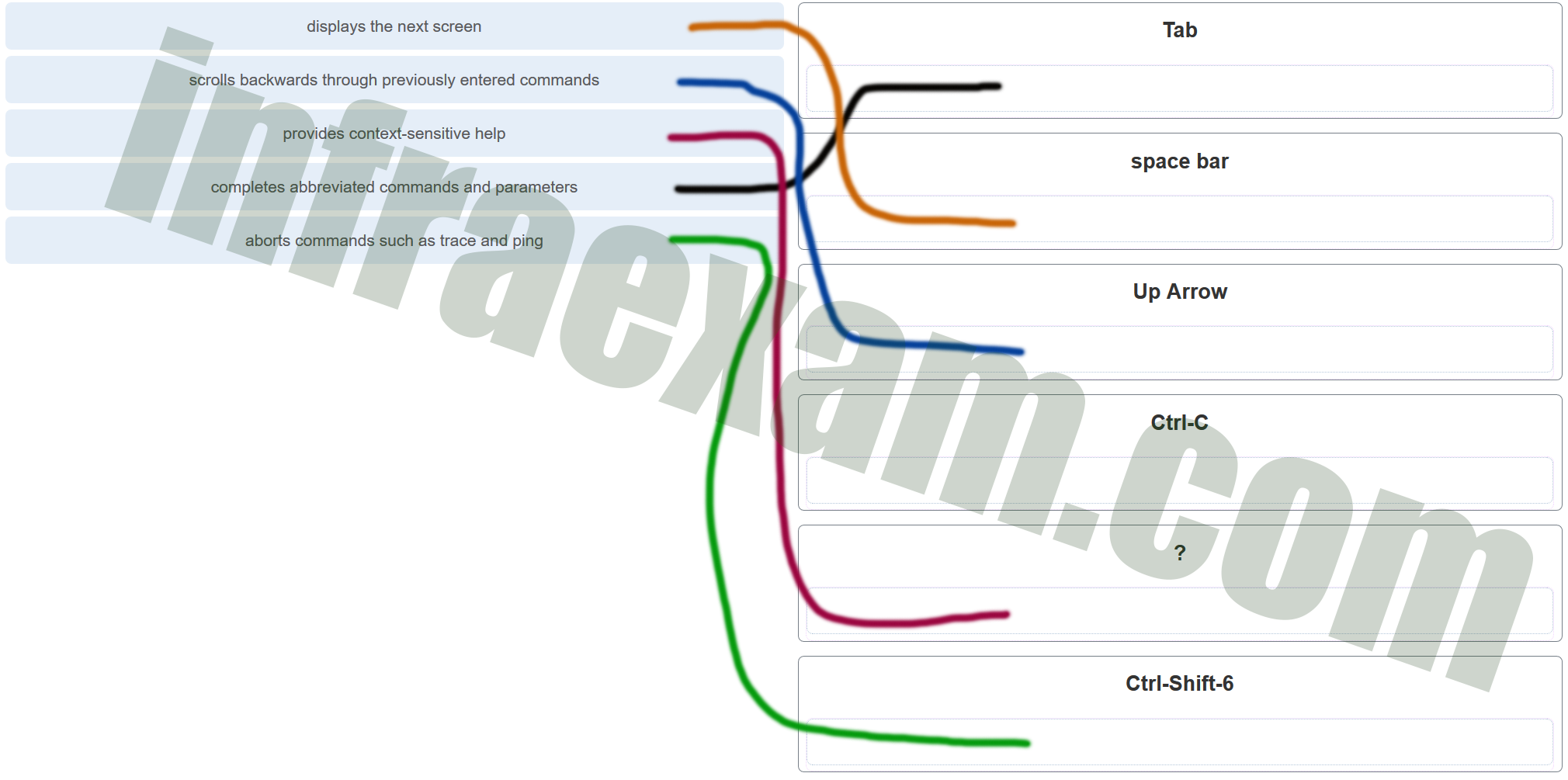
- displays the next screen ==> space bar
- scrolls backwards through previously entered commands ==> Up Arrow
- provides context-sensitive help ==> ?
- completes abbreviated commands and parameters ==> Tab
- aborts commands such as trace and ping ==> Ctrl-Shift-6
- Ctrl-C ==> Not Match
Therefore, the correct matches are:
|
In the show running-config command, which part of the syntax is represented by running-config?
- the command
- a keyword
- a variable
- a prompt
| Answers Explanation & Hints:
In the A keyword Explanation:
So, within the |
After making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?
- The new configuration will be stored in flash memory.
- The new configuration will be loaded if the switch is restarted.
- The current IOS file will be replaced with the newly configured file.
- The configuration changes will be removed and the original configuration will be restored.
After making configuration changes on a Cisco switch, a network administrator issues the copy running-config startup-config command. The result of issuing this command is:
The new configuration will be loaded if the switch is restarted. Explanation:
Therefore, issuing the |
What command will prevent all unencrypted passwords from displaying in plain text in a configuration file?
- (config)# enable password secret
- (config)# enable secret Secret_Password
- (config-line)# password secret
- (config)# service password-encryption
- (config)# enable secret Encrypted_Password
| Answers Explanation & Hints:
To prevent all configured passwords from appearing in plain text in configuration files, an administrator can execute the service password-encryption command. This command encrypts all configured passwords in the configuration file. |
A network administrator enters the service password-encryption command into the configuration mode of a router. What does this command accomplish?
- This command encrypts passwords as they are transmitted across serial WAN links.
- This command prevents someone from viewing the running configuration passwords.
- This command enables a strong encryption algorithm for the enable secret password command.
- This command automatically encrypts passwords in configuration files that are currently stored in NVRAM.
- This command provides an exclusive encrypted password for external service personnel who are required to do router maintenance.
| Answers Explanation & Hints:
The startup-config and running-config files display most passwords in plaintext. Use the service password-encryption global config command to encrypt all plaintext passwords in these files. |
What method can be used by two computers to ensure that packets are not dropped because too much data is being sent too quickly?
- encapsulation
- flow control
- access method
- response timeout
| Answers Explanation & Hints:
In order for two computers to be able to communicate effectively, there must be a mechanism that allows both the source and destination to set the timing of the transmission and receipt of data. Flow control allows for this by ensuring that data is not sent too fast for it to be received properly. |
Which statement accurately describes a TCP/IP encapsulation process when a PC is sending data to the network?
- Data is sent from the internet layer to the network access layer.
- Packets are sent from the network access layer to the transport layer.
- Segments are sent from the transport layer to the internet layer.
- Frames are sent from the network access layer to the internet layer.
| Answers Explanation & Hints:
When the data is traveling from the PC to the network, the transport layer sends segments to the internet layer. The internet layer sends packets to the network access layer, which creates frames and then converts the frames to bits. The bits are released to the network media. |
What three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)
- ARP
- DHCP
- DNS
- FTP
- NAT
- PPP
| Answers Explanation & Hints:
DNS, DHCP, and FTP are all application layer protocols in the TCP/IP protocol suite. ARP and PPP are network access layer protocols, and NAT is an internet layer protocol in the TCP/IP protocol suite. |
Match the description to the organization. (Not all options are used.)

- This organization is responsible for overseeing and managing IP address allocation, domain name management, and protocol identifiers. ==> IANA
- This organization is the largest developer of international standards in the world for a wide variety of products and services. It is known for its Open Systems Interconnection (OSI) reference model. ==> ISO
- This organization promotes the open development, evolution, and use of the Internet throughout the world. ==> ISOC
- EIA ==> Not Match
| Answers Explanation & Hints:
The EIA is an international standards and trade organization for electronics organizations. It is best known for its standards related to electrical wiring, connectors, and the 19-inch racks used to mount networking equipment. |
Which name is assigned to the transport layer PDU?
- bits
- data
- frame
- packet
- segment
| Answers Explanation & Hints:
Application data is passed down the protocol stack on its way to be transmitted across the network media. During the process, various protocols add information to it at each level. At each stage of the process, a PDU (protocol data unit) has a different name to reflect its new functions. The PDUs are named according to the protocols of the TCP/IP suite: Data – The general term for the PDU used at the application layer. |
When IPv4 addressing is manually configured on a web server, which property of the IPv4 configuration identifies the network and host portion for an IPv4 address?
- DNS server address
- subnet mask
- default gateway
- DHCP server address
| Answers Explanation & Hints:
There are several components that need to be entered when configuring IPv4 for an end device: IPv4 address – uniquely identifies an end device on the network |
What process involves placing one PDU inside of another PDU?
- encapsulation
- encoding
- segmentation
- flow control
| Answers Explanation & Hints:
When a message is placed inside of another message, this is known as encapsulation. On networks, encapsulation takes place when one protocol data unit is carried inside of the data field of the next lower protocol data unit. |
What layer is responsible for routing messages through an internetwork in the TCP/IP model?
- internet
- transport
- network access
- session
| Answers Explanation & Hints:
The TCP/IP model consists of four layers: application, transport, internet, and network access. Of these four layers, it is the internet layer that is responsible for routing messages. The session layer is not part of the TCP/IP model but is rather part of the OSI model. |
For the TCP/IP protocol suite, what is the correct order of events when a Telnet message is being prepared to be sent over the network?
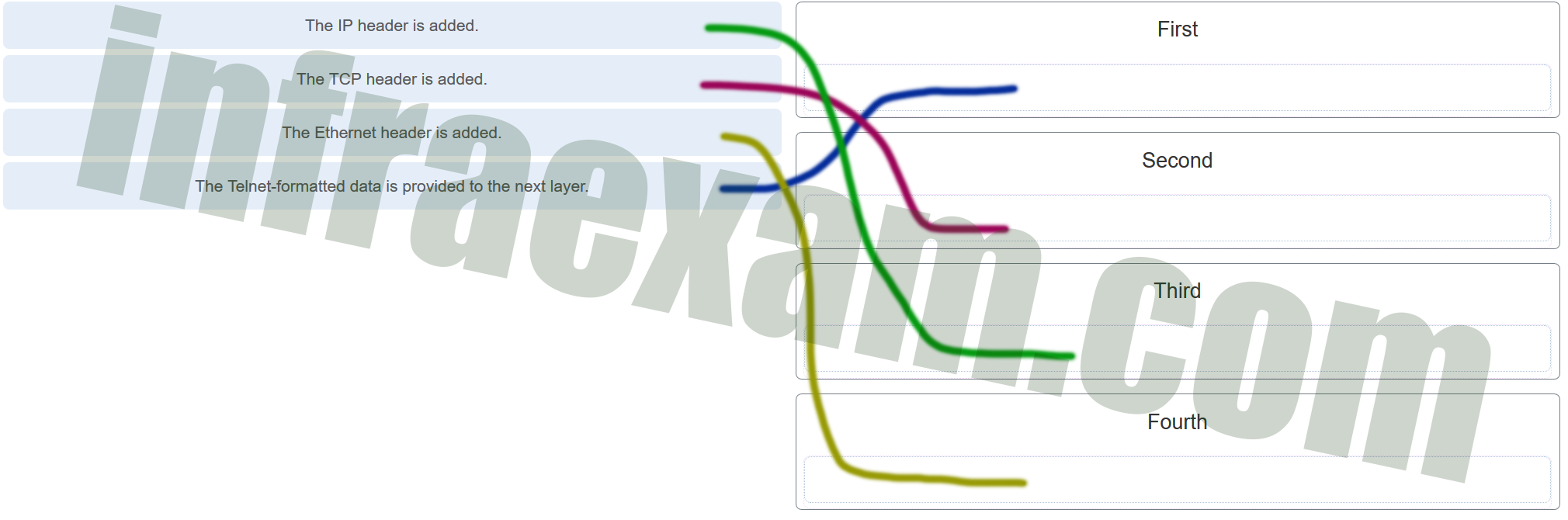
- The IP header is added. ==> Third
- The TCP header is added. ==> Second
- The Ethernet header is added. ==> Fourth
- The Telnet-formatted data is provided to the next layer. ==> First
Explanation & Hint:
These organizations play a critical role in the maintenance and advancement of internet technologies and standards. |
Which PDU format is used when bits are received from the network medium by the NIC of a host?
- file
- frame
- packet
- segment
| Answers Explanation & Hints:
When received at the physical layer of a host, the bits are formatted into a frame at the data link layer. A packet is the PDU at the network layer. A segment is the PDU at the transport layer. A file is a data structure that may be used at the application layer. |
Refer to the exhibit. ServerB is attempting to contact HostA. Which two statements correctly identify the addressing that ServerB will generate in the process? (Choose two.)
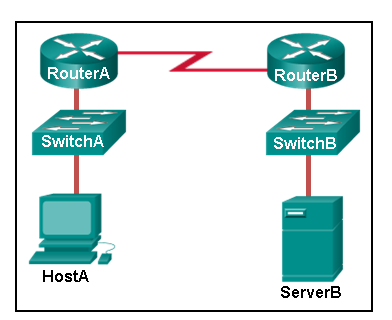
- ServerB will generate a packet with the destination IP address of RouterB.
- ServerB will generate a frame with the destination MAC address of SwitchB.
- ServerB will generate a packet with the destination IP address of RouterA.
- ServerB will generate a frame with the destination MAC address of RouterB.
- ServerB will generate a packet with the destination IP address of HostA.
- ServerB will generate a frame with the destination MAC address of RouterA.
| Answers Explanation & Hints:
In order to send data to HostA, ServerB will generate a packet that contains the IP address of the destination device on the remote network and a frame that contains the MAC address of the default gateway device on the local network. |
Which method allows a computer to react accordingly when it requests data from a server and the server takes too long to respond?
- encapsulation
- flow control
- access method
- response timeout
| Answers Explanation & Hints:
If a computer makes a request and does not hear a response within an acceptable amount of time, the computer assumes that no answer is coming and reacts accordingly. |
A web client is receiving a response for a web page from a web server. From the perspective of the client, what is the correct order of the protocol stack that is used to decode the received transmission?
- Ethernet, IP, TCP, HTTP
- HTTP, TCP, IP, Ethernet
- Ethernet, TCP, IP, HTTP
- HTTP, Ethernet, IP, TCP
| Answers Explanation & Hints:
1. HTTP governs the way that a web server and client interact. |
Which two OSI model layers have the same functionality as a single layer of the TCP/IP model? (Choose two.)
- data link
- network
- physical
- session
- transport
| Answers Explanation & Hints:
The OSI data link and physical layers together are equivalent to the TCP/IP network access layer. The OSI transport layer is functionally equivalent to the TCP/IP transport layer, and the OSI network layer is equivalent to the TCP/IP internet layer. The OSI application, presentation, and session layers are functionally equivalent to the application layer within the TCP/IP model. |
At which layer of the OSI model would a logical address be added during encapsulation?
- physical layer
- data link layer
- network layer
- transport layer
| Answers Explanation & Hints:
Logical addresses, also known as IP addresses, are added at the network layer. Physical addresses are edded at the data link layer. Port addresses are added at the transport layer. No addresses are added at the physical layer. |
What is a characteristic of multicast messages?
- They are sent to a select group of hosts.
- They are sent to all hosts on a network.
- They must be acknowledged.
- They are sent to a single destination.
| Answers Explanation & Hints:
Multicast is a one-to-many type of communication. Multicast messages are addressed to a specific multicast group. |
Which statement is correct about network protocols?
- Network protocols define the type of hardware that is used and how it is mounted in racks.
- They define how messages are exchanged between the source and the destination.
- They all function in the network access layer of TCP/IP.
- They are only required for exchange of messages between devices on remote networks.
| Answers Explanation & Hints:
Network protocols are implemented in hardware, or software, or both. They interact with each other within different layers of a protocol stack. Protocols have nothing to do with the installation of the network equipment. Network protocols are required to exchange information between source and destination devices in both local and remote networks. |
What is an advantage of network devices using open standard protocols?
- Network communications is confined to data transfers between devices from the same vendor.
- A client host and a server running different operating systems can successfully exchange data.
- Internet access can be controlled by a single ISP in each market.
- Competition and innovation are limited to specific types of products.
| Answers Explanation & Hints:
An advantage of network devices implementing open standard protocols, such as from the TCP/IP suite, is that clients and servers running different operating systems can communicate with each other. Open standard protocols facilitate innovation and competition between vendors and across markets, and can reduce the occurrence of monopolies in networking markets. |
Which device performs the function of determining the path that messages should take through internetworks?
- a router
- a firewall
- a web server
- a DSL modem
| Answers Explanation & Hints:
A router is used to determine the path that the messages should take through the network. A firewall is used to filter incoming and outgoing traffic. A DSL modem is used to provide Internet connection for a home or an organization. |
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.

What is the IP address of the switch virtual interface (SVI) on Switch0?
- 192.168.5.10
- 192.168.10.5
- 192.168.10.1
- 192.168.5.0
| Answers Explanation & Hints:
After the enable command is issued, the show running-configuration command or the show ip interfaces brief command will display the IP address of the switch virtual interface (SVI). |
Why would a Layer 2 switch need an IP address?
- to enable the switch to send broadcast frames to attached PCs
- to enable the switch to function as a default gateway
- to enable the switch to be managed remotely
- to enable the switch to receive frames from attached PCs
| Answers Explanation & Hints:
A switch, as a Layer 2 device, does not need an IP address to transmit frames to attached devices. However, when a switch is accessed remotely through the network, it must have a Layer 3 address. The IP address must be applied to a virtual interface rather than to a physical interface. Routers, not switches, function as default gateways. |
Refer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?
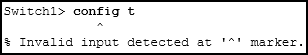
- The entire command, configure terminal, must be used.
- The administrator is already in global configuration mode.
- The administrator must first enter privileged EXEC mode before issuing the command.
- The administrator must connect via the console port to access global configuration mode.
| Answers Explanation & Hints:
In order to enter global configuration mode, the command configure terminal , or a shortened version such as config t , must be entered from privileged EXEC mode. In this scenario the administrator is in user EXEC mode, as indicated by the > symbol after the hostname. The administrator would need to use the enable command to move into privileged EXEC mode before entering the configure terminal command. |
What term describes a network owned by one organization that provides safe and secure access to individuals who work for a different organization?
- extranet
- cloud
- BYOD
- quality of servic
| Explanation & Hint:
The term that describes a network owned by one organization that provides safe and secure access to individuals who work for a different organization is “extranet.” An extranet is a private network that allows authorized users from external organizations to access certain resources, such as files, applications, or communication tools, while maintaining security and controlled access. |
What term describes storing personal files on servers over the internet to provide access anywhere, anytime, and on any device?
- cloud
- BYOD
- quality of service
- converged network
| Explanation & Hint:
The term that describes storing personal files on servers over the internet to provide access anywhere, anytime, and on any device is “cloud.” This approach is commonly referred to as “cloud storage” or “cloud computing,” where data is stored and managed in remote data centers accessible via the internet, offering convenience and accessibility across various devices and locations. |
What term describes a network where one computer can be both client and server?
- peer-to-peer
- cloud
- BYOD
- quality of service
| Explanation & Hint:
The term that describes a network where one computer can be both a client and a server is “peer-to-peer” (P2P) networking. In a peer-to-peer network, each computer (or peer) can act as both a client and a server, allowing them to share resources and information directly with one another without the need for a centralized server. |
What term describes a type of network used by people who work from home or from a small remote office?
- SOHO network
- BYOD
- quality of service
- converged network
| Explanation & Hint:
The term that describes a type of network used by people who work from home or from a small remote office is a “SOHO network.” SOHO stands for “Small Office/Home Office,” and it refers to networks designed to meet the needs of individuals or small businesses working from home or in small remote office locations. These networks are typically smaller in scale compared to large corporate networks and are tailored to the requirements of remote or home-based workers. |
What term describes a computing model where server software runs on dedicated computers?
- client/server
- internet
- intranet
- extranet
| Explanation & Hint:
The term that describes a computing model where server software runs on dedicated computers is “client/server.” In a client/server computing model, dedicated server computers provide services or resources to client computers, which request and use these services. This architecture is common in networked systems where multiple clients interact with one or more dedicated server machines to access data, applications, or resources. |
What term describes a type of network used by people who work from home or from a small remote office?
- SOHO network
- internet
- intranet
- extranet
| Explanation & Hint:
The term that describes a type of network used by people who work from home or from a small remote office is a “SOHO network.” SOHO stands for “Small Office/Home Office,” and it refers to networks designed to meet the needs of individuals or small businesses working from home or in small remote office locations. These networks are typically smaller in scale compared to large corporate networks and are tailored to the requirements of remote or home-based workers. |
What term describes a technology that allows devices to connect to the LAN using an electrical outlet?
- powerline networking
- internet
- intranet
- extranet
| Explanation & Hint:
The term that describes a technology that allows devices to connect to the LAN (Local Area Network) using an electrical outlet is “powerline networking.” Powerline networking uses a building’s existing electrical wiring to transmit data signals between devices, effectively turning electrical outlets into network connections. This technology is a convenient way to extend network connectivity within a building without the need for additional Ethernet cables or Wi-Fi networks. |
What term describes a policy that allows network devices to manage the flow of data to give priority to voice and video?
- quality of service
- internet
- intranet
- extranet
| Explanation & Hint:
The term that describes a policy that allows network devices to manage the flow of data to give priority to voice and video is “quality of service” or “QoS.” Quality of service is a set of techniques and mechanisms used to prioritize certain types of data traffic over others to ensure a consistent and acceptable level of service quality, especially for real-time or latency-sensitive applications like voice and video communication. QoS policies help manage and allocate network resources to ensure a smoother and more reliable experience for these applications. |
What term describes a private collection of LANs and WANs that belongs to an organization?
- intranet
- internet
- extranet
- peer-to-peer
| Explanation & Hint:
The term that describes a private collection of LANs and WANs that belongs to an organization is “intranet.” An intranet is a network that is used internally within an organization to facilitate communication, collaboration, and information sharing among its employees, typically in a secure and private manner. It is not accessible to the public and is designed to serve the organization’s internal needs. |
What term describes the ability to use personal devices across a business or campus network?
- BYOD
- internet
- intranet
- extranet
| Explanation & Hint:
The term that describes the ability to use personal devices across a business or campus network is “BYOD,” which stands for “Bring Your Own Device.” BYOD is a policy or practice that allows employees, students, or users to bring their personal devices, such as smartphones, tablets, or laptops, and connect them to a business or campus network to access resources, applications, and services. |
At which OSI layer is a source IP address added to a PDU during the encapsulation process?
- network layer
- data link layer
- transport layer
- application layer
| Explanation & Hint:
The source IP address is added to a Protocol Data Unit (PDU) at the “network layer,” which is also known as OSI Layer 3. The network layer is responsible for routing and forwarding data between different networks, and IP addresses are used to uniquely identify the source and destination of data at this layer. |
At which OSI layer is a destination port number added to a PDU during the encapsulation process?
- transport layer
- data link layer
- network layer
- application layer
| Explanation & Hint:
A destination port number is added to a Protocol Data Unit (PDU) during the encapsulation process at the “transport layer,” which is also known as OSI Layer 4. Port numbers are used to direct data to specific services or processes on a device, allowing for the proper delivery and communication of data between applications. |
At which OSI layer is data added to a PDU during the encapsulation process?
- application layer
- data link layer
- network layer
- transport layer
| Explanation & Hint:
Data is added to a Protocol Data Unit (PDU) during the encapsulation process at the “application layer,” which is also known as OSI Layer 7. The application layer is responsible for providing the interface between the software applications and the lower layers of the OSI model, allowing applications to exchange data. Data from an application is divided into PDUs at the application layer, and then it is encapsulated in lower-layer PDUs as it moves down the OSI model. |
At which OSI layer is a source IP address added to a PDU during the encapsulation process?
- network layer
- data link layer
- application layer
- presentation layer
| Explanation & Hint:
A source IP address is added to a Protocol Data Unit (PDU) during the encapsulation process at the “network layer,” which is also known as OSI Layer 3. The network layer is responsible for routing and forwarding data between different networks, and IP addresses are used to uniquely identify the source and destination of data at this layer. |
At which OSI layer is data added to a PDU during the encapsulation process?
- application layer
- transport layer
- network layer
- presentation layer
| Explanation & Hint:
Data is added to a Protocol Data Unit (PDU) during the encapsulation process at the “application layer,” which is also known as OSI Layer 7. The application layer is responsible for providing the interface between the software applications and the lower layers of the OSI model, allowing applications to exchange data. Data from an application is divided into PDUs at the application layer, and then it is encapsulated in lower-layer PDUs as it moves down the OSI model. |
At which OSI layer is a destination IP address added to a PDU during the encapsulation process?
- network layer
- application layer
- transport layer
- presentation layer
| Explanation & Hint:
A destination IP address is added to a Protocol Data Unit (PDU) during the encapsulation process at the “network layer,” which is also known as OSI Layer 3. The network layer is responsible for routing and forwarding data between different networks, and IP addresses are used to uniquely identify the source and destination of data at this layer. |
At which OSI layer is a source MAC address added to a PDU during the encapsulation process?
- data link layer
- application layer
- transport layer
- presentation layer
| Explanation & Hint:
A source MAC (Media Access Control) address is added to a Protocol Data Unit (PDU) during the encapsulation process at the “data link layer,” which is also known as OSI Layer 2. The data link layer is responsible for the addressing and control of data frames on the local network segment, and MAC addresses are used to identify individual devices on the same network segment at this layer. |
At which OSI layer is a source port number added to a PDU during the encapsulation process?
- transport layer
- application layer
- network layer
- presentation layer
| Explanation & Hint:
A source port number is added to a Protocol Data Unit (PDU) during the encapsulation process at the “transport layer,” which is also known as OSI Layer 4. Port numbers are used to identify specific processes or services on a device, and they are utilized at the transport layer to ensure that data is delivered to the correct application or service on the receiving end |
At which OSI layer is a destination MAC address added to a PDU during the encapsulation process?
- data link layer
- transport layer
- application layer
- network layer
| Explanation & Hint:
A destination MAC (Media Access Control) address is added to a Protocol Data Unit (PDU) during the encapsulation process at the “data link layer,” which is also known as OSI Layer 2. The data link layer is responsible for addressing and controlling data frames within the local network segment, and MAC addresses are used to identify specific devices on the same network segment at this layer. |
At which OSI layer is a source port number added to a PDU during the encapsulation process?
- transport layer
- network layer
- application layer
- data link layer
| Explanation & Hint:
A source port number is added to a Protocol Data Unit (PDU) during the encapsulation process at the “transport layer,” which is also known as OSI Layer 4. Port numbers are used to identify specific processes or services on a device, and they are utilized at the transport layer to ensure that data is delivered to the correct application or service on the receiving end. |