CAS-003 : CompTIA Advanced Security Practitioner (CASP+) CAS-003 : Part 03
CAS-003 : CompTIA Advanced Security Practitioner (CASP+) CAS-003 : Part 03
-
A security engineer has implemented an internal user access review tool so service teams can baseline user accounts and group memberships. The tool is functional and popular among its initial set of onboarded teams. However, the tool has not been built to cater to a broader set of internal teams yet. The engineer has sought feedback from internal stakeholders, and a list of summarized requirements is as follows:
– The tool needs to be responsive so service teams can query it, and then perform an automated response action.
– The tool needs to be resilient to outages so service teams can perform the user access review at any point in time and meet their own SLAs.
– The tool will become the system-of-record for approval, reapproval, and removal life cycles of group memberships and must allow for data retrieval after failure.Which of the following need specific attention to meet the requirements listed above? (Choose three.)
- Scalability
- Latency
- Availability
- Usability
- Recoverability
- Maintainability
-
The board of a financial services company has requested that the senior security analyst acts as a cybersecurity advisor in order to comply with recent federal legislation. The analyst is required to give a report on current cybersecurity and threat trends in the financial services industry at the next board meeting. Which of the following would be the BEST methods to prepare this report? (Choose two.)
- Review the CVE database for critical exploits over the past year
- Use social media to contact industry analysts
- Use intelligence gathered from the Internet relay chat channels
- Request information from security vendors and government agencies
- Perform a penetration test of the competitor’s network and share the results with the board
-
The Chief Information Security Officer (CISO) has asked the security team to determine whether the organization is susceptible to a zero-day exploit utilized in the banking industry and whether attribution is possible. The CISO has asked what process would be utilized to gather the information, and then wants to apply signatureless controls to stop these kinds of attacks in the future. Which of the following are the MOST appropriate ordered steps to take to meet the CISO’s request?
- 1. Perform the ongoing research of the best practices
2. Determine current vulnerabilities and threats
3. Apply Big Data techniques
4. Use antivirus control - 1. Apply artificial intelligence algorithms for detection
2. Inform the CERT team
3. Research threat intelligence and potential adversaries
4. Utilize threat intelligence to apply Big Data techniques - 1. Obtain the latest IOCs from the open source repositories
2. Perform a sweep across the network to identify positive matches
3. Sandbox any suspicious files
4. Notify the CERT team to apply a future proof threat model - 1. Analyze the current threat intelligence
2. Utilize information sharing to obtain the latest industry IOCs
3. Perform a sweep across the network to identify positive matches
4. Apply machine learning algorithms
- 1. Perform the ongoing research of the best practices
-
A software development team is conducting functional and user acceptance testing of internally developed web applications using a COTS solution. For automated testing, the solution uses valid user credentials from the enterprise directory to authenticate to each application. The solution stores the username in plain text and the corresponding password as an encoded string in a script within a file, located on a globally accessible network share. The account credentials used belong to the development team lead. To reduce the risks associated with this scenario while minimizing disruption to ongoing testing, which of the following are the BEST actions to take? (Choose two.)
- Restrict access to the network share by adding a group only for developers to the share’s ACL
- Implement a new COTS solution that does not use hard-coded credentials and integrates with directory services
- Obfuscate the username within the script file with encoding to prevent easy identification and the account used
- Provision a new user account within the enterprise directory and enable its use for authentication to the target applications. Share the username and password with all developers for use in their individual scripts
- Redesign the web applications to accept single-use, local account credentials for authentication
-
A security consultant is attempting to discover if the company is utilizing databases on client machines to store the customer data. The consultant reviews the following information:
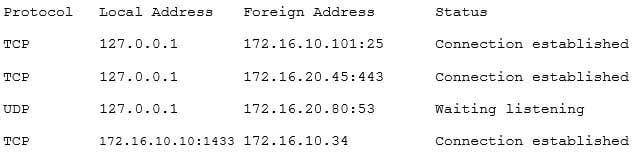
CAS-003 Part 03 Q05 017 Which of the following commands would have provided this output?
-
arp -s
-
netstat -a -
ifconfig -arp
-
sqlmap -w
-
-
Management is reviewing the results of a recent risk assessment of the organization’s policies and procedures. During the risk assessment it is determined that procedures associated with background checks have not been effectively implemented. In response to this risk, the organization elects to revise policies and procedures related to background checks and use a third-party to perform background checks on all new employees. Which of the following risk management strategies has the organization employed?
- Transfer
- Mitigate
- Accept
- Avoid
- Reject
-
A company wants to perform analysis of a tool that is suspected to contain a malicious payload. A forensic analyst is given the following snippet:
^32^[34fda19(fd^43gfd/home/user/lib/module.so.343jk^rfw(342fds43g
Which of the following did the analyst use to determine the location of the malicious payload?
- Code deduplicators
- Binary reverse-engineering
- Fuzz testing
- Security containers
-
An advanced threat emulation engineer is conducting testing against a client’s network. The engineer conducts the testing in as realistic a manner as possible. Consequently, the engineer has been gradually ramping up the volume of attacks over a long period of time. Which of the following combinations of techniques would the engineer MOST likely use in this testing? (Choose three.)
- Black box testing
- Gray box testing
- Code review
- Social engineering
- Vulnerability assessment
- Pivoting
- Self-assessment
- White teaming
- External auditing
-
A security engineer must establish a method to assess compliance with company security policies as they apply to the unique configuration of individual endpoints, as well as to the shared configuration policies of common devices.

CAS-003 Part 03 Q09 018 Which of the following tools is the security engineer using to produce the above output?
- Vulnerability scanner
- SIEM
- Port scanner
- SCAP scanner
-
A newly hired systems administrator is trying to connect a new and fully updated, but very customized, Android device to access corporate resources. However, the MDM enrollment process continually fails. The administrator asks a security team member to look into the issue. Which of the following is the MOST likely reason the MDM is not allowing enrollment?
- The OS version is not compatible
- The OEM is prohibited
- The device does not support FDE
- The device is rooted
-
A hospital uses a legacy electronic medical record system that requires multicast for traffic between the application servers and databases on virtual hosts that support segments of the application. Following a switch upgrade, the electronic medical record is unavailable despite physical connectivity between the hypervisor and the storage being in place. The network team must enable multicast traffic to restore access to the electronic medical record. The ISM states that the network team must reduce the footprint of multicast traffic on the network.

CAS-003 Part 03 Q11 019 Using the above information, on which VLANs should multicast be enabled?
- VLAN201, VLAN202, VLAN400
- VLAN201, VLAN202, VLAN700
- VLAN201, VLAN202, VLAN400, VLAN680, VLAN700
- VLAN400, VLAN680, VLAN700
-
A security administrator wants to allow external organizations to cryptographically validate the company’s domain name in email messages sent by employees. Which of the following should the security administrator implement?
- SPF
- S/MIME
- TLS
- DKIM
-
An organization is preparing to develop a business continuity plan. The organization is required to meet regulatory requirements relating to confidentiality and availability, which are well-defined. Management has expressed concern following initial meetings that the organization is not fully aware of the requirements associated with the regulations. Which of the following would be MOST appropriate for the project manager to solicit additional resources for during this phase of the project?
- After-action reports
- Gap assessment
- Security requirements traceability matrix
- Business impact assessment
- Risk analysis
-
A SaaS-based email service provider often receives reports from legitimate customers that their IP netblocks are on blacklists and they cannot send email. The SaaS has confirmed that affected customers typically have IP addresses within broader network ranges and some abusive customers within the same IP ranges may have performed spam campaigns. Which of the following actions should the SaaS provider perform to minimize legitimate customer impact?
- Inform the customer that the service provider does not have any control over third-party blacklist entries. The customer should reach out to the blacklist operator directly
- Perform a takedown of any customer accounts that have entries on email blacklists because this is a strong indicator of hostile behavior
- Work with the legal department and threaten legal action against the blacklist operator if the netblocks are not removed because this is affecting legitimate traffic
- Establish relationship with a blacklist operators so broad entries can be replaced with more granular entries and incorrect entries can be quickly pruned
-
An agency has implemented a data retention policy that requires tagging data according to type before storing it in the data repository. The policy requires all business emails be automatically deleted after two years. During an open records investigation, information was found on an employee’s work computer concerning a conversation that occurred three years prior and proved damaging to the agency’s reputation. Which of the following MOST likely caused the data leak?
- The employee manually changed the email client retention settings to prevent deletion of emails
- The file that contained the damaging information was mistagged and retained on the server for longer than it should have been
- The email was encrypted and an exception was put in place via the data classification application
- The employee saved a file on the computer’s hard drive that contained archives of emails, which were more than two years old
-
A forensics analyst suspects that a breach has occurred. Security logs show the company’s OS patch system may be compromised, and it is serving patches that contain a zero-day exploit and backdoor. The analyst extracts an executable file from a packet capture of communication between a client computer and the patch server. Which of the following should the analyst use to confirm this suspicion?
- File size
- Digital signature
- Checksums
- Anti-malware software
- Sandboxing
-
A company is acquiring incident response and forensic assistance from a managed security service provider in the event of a data breach. The company has selected a partner and must now provide required documents to be reviewed and evaluated. Which of the following documents would BEST protect the company and ensure timely assistance? (Choose two.)
- RA
- BIA
- NDA
- RFI
- RFQ
- MSA
-
A security architect is implementing security measures in response to an external audit that found vulnerabilities in the corporate collaboration tool suite. The report identified the lack of any mechanism to provide confidentiality for electronic correspondence between users and between users and group mailboxes. Which of the following controls would BEST mitigate the identified vulnerability?
- Issue digital certificates to all users, including owners of group mailboxes, and require S/MIME with AES-256.
- Federate with an existing PKI provider, and reject all non-signed emails
- Implement two-factor email authentication, and require users to hash all email messages upon receipt
- Provide digital certificates to all systems, and eliminate the user group or shared mailboxes
-
Which of the following BEST represents a risk associated with merging two enterprises during an acquisition?
- The consolidation of two different IT enterprises increases the likelihood of the data loss because there are now two backup systems
- Integrating two different IT systems might result in a successful data breach if threat intelligence is not shared between the two enterprises
- Merging two enterprise networks could result in an expanded attack surface and could cause outages if trust and permission issues are not handled carefully
- Expanding the set of data owners requires an in-depth review of all data classification decisions, impacting availability during the review
-
Two competing companies experienced similar attacks on their networks from various threat actors. To improve response times, the companies wish to share some threat intelligence about the sources and methods of attack. Which of the following business documents would be BEST to document this engagement?
- Business partnership agreement
- Memorandum of understanding
- Service-level agreement
- Interconnection security agreement