CAS-003 : CompTIA Advanced Security Practitioner (CASP+) CAS-003 : Part 12
CAS-003 : CompTIA Advanced Security Practitioner (CASP+) CAS-003 : Part 12
-
A security analyst is reviewing the following packet capture of communication between a host and a company’s router:
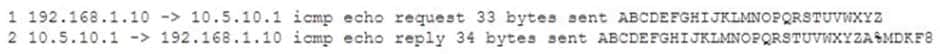
CAS-003 Part 12 Q01 072 Which of the following actions should the security analyst take to remove this vulnerability?
- Update the router code
- Implement a router ACL
- Disconnect the host from the network
- Install the latest antivirus definitions
- Deploy a network-based IPS
-
An information security manager conducted a gap analysis, which revealed a 75% implementation of security controls for high-risk vulnerabilities, 90% for medium vulnerabilities, and 10% for low-risk vulnerabilities. To create a road map to close the identified gaps, the assurance team reviewed the likelihood of exploitation of each vulnerability and the business impact of each associated control. To determine which controls to implement, which of the following is the MOST important to consider?
- KPI
- KRI
- GRC
- BIA
-
A development team is testing an in-house-developed application for bugs. During the test, the application crashes several times due to null pointer exceptions. Which of the following tools, if integrated into an IDE during coding, would identify these bugs routinely?
- Issue tracker
- Static code analyzer
- Source code repository
- Fuzzing utility
-
A legacy web application, which is being used by a hospital, cannot be upgraded for 12 months. A new vulnerability is found in the legacy application, and the networking team is tasked with mitigation. Middleware for mitigation will cost $100,000 per year. Which of the following must be calculated to determine ROI? (Choose two.)
- ALE
- RTO
- MTBF
- ARO
- RPO
-
A security engineer is assisting a developer with input validation, and they are studying the following code block:

CAS-003 Part 12 Q05 073 The security engineer wants to ensure strong input validation is in place for customer-provided account identifiers. These identifiers are ten-digit numbers. The developer wants to ensure input validation is fast because a large number of people use the system.
Which of the following would be the BEST advice for the security engineer to give to the developer?
- Replace code with Java-based type checks
- Parse input into an array
- Use regular expressions
- Canonicalize input into string objects before validation
-
A project manager is working with a software development group to collect and evaluate user stories related to the organization’s internally designed CRM tool. After defining requirements, the project manager would like to validate the developer’s interpretation and understanding of the user’s request. Which of the following would BEST support this objective?
- Peer review
- Design review
- Scrum
- User acceptance testing
- Unit testing
-
A network printer needs Internet access to function. Corporate policy states all devices allowed on the network must be authenticated. Which of the following is the MOST secure method to allow the printer on the network without violating policy?
- Request an exception to the corporate policy from the risk management committee
- Require anyone trying to use the printer to enter their username and password
- Have a help desk employee sign in to the printer every morning
- Issue a certificate to the printer and use certificate-based authentication
-
The Chief Information Security Officer (CISO) of an e-retailer, which has an established security department, identifies a customer who has been using a fraudulent credit card. The CISO calls the local authorities, and when they arrive on-site, the authorities ask a security engineer to create a point-in-time copy of the running database in their presence. This is an example of:
- creating a forensic image
- deploying fraud monitoring
- following a chain of custody
- analyzing the order of volatility
-
A technician is configuring security options on the mobile device manager for users who often utilize public Internet connections while travelling. After ensuring that full disk encryption is enabled, which of the following security measures should the technician take? (Choose two.)
- Require all mobile device backups to be encrypted
- Ensure all mobile devices back up using USB OTG
- Issue a remote wipe of corporate and personal partitions
- Restrict devices from making long-distance calls during business hours
- Implement an always-on VPN
-
A systems administrator receives an advisory email that a recently discovered exploit is being used in another country and the financial institutions have ceased operations while they find a way to respond to the attack. Which of the following BEST describes where the administrator should look to find information on the attack to determine if a response must be prepared for the systems? (Choose two.)
- Bug bounty websites
- Hacker forums
- Antivirus vendor websites
- Trade industry association websites
- CVE database
- Company’s legal department
-
A security assessor is working with an organization to review the policies and procedures associated with managing the organization’s virtual infrastructure. During a review of the virtual environment, the assessor determines the organization is using servers to provide more than one primary function, which violates a regulatory requirement. The assessor reviews hardening guides and determines policy allows for this configuration. It would be MOST appropriate for the assessor to advise the organization to:
- segment dual-purpose systems on a hardened network segment with no external access
- assess the risks associated with accepting non-compliance with regulatory requirements
- update system implementation procedures to comply with regulations
- review regulatory requirements and implement new policies on any newly provisioned servers
-
While conducting a BIA for a proposed acquisition, the IT integration team found that both companies outsource CRM services to competing and incompatible third-party cloud services. The decision has been made to bring the CRM service in-house, and the IT team has chosen a future solution. With which of the following should the Chief Information Security Officer (CISO) be MOST concerned? (Choose two.)
- Data remnants
- Sovereignty
- Compatible services
- Storage encryption
- Data migration
- Chain of custody
-
A newly hired Chief Information Security Officer (CISO) is reviewing the organization’s security budget from the previous year. The CISO notices $100,000 worth of fines were paid for not properly encrypting outbound email messages. The CISO expects next year’s costs associated with fines to double and the volume of messages to increase by 100%. The organization sent out approximately 25,000 messages per year over the last three years. Given the table below:
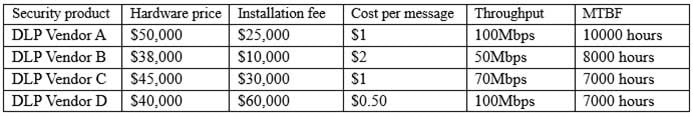
CAS-003 Part 12 Q13 074 Which of the following would be BEST for the CISO to include in this year’s budget?
- A budget line for DLP Vendor A
- A budget line for DLP Vendor B
- A budget line for DLP Vendor C
- A budget line for DLP Vendor D
- A budget line for paying future fines
-
The Chief Information Security Officer (CISO) suspects that a database administrator has been tampering with financial data to the administrator’s advantage. Which of the following would allow a third-party consultant to conduct an on-site review of the administrator’s activity?
- Separation of duties
- Job rotation
- Continuous monitoring
- Mandatory vacation
-
While investigating suspicious activity on a server, a security administrator runs the following report:
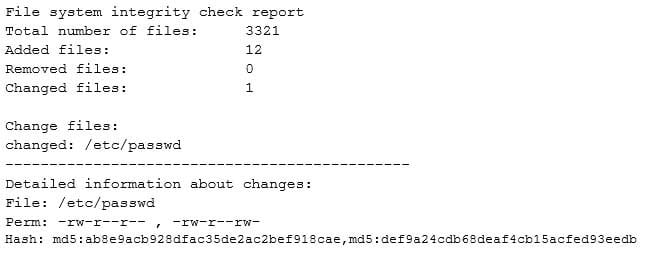
CAS-003 Part 12 Q15 075 In addition, the administrator notices changes to the /etc/shadow file that were not listed in the report. Which of the following BEST describe this scenario? (Choose two.)
- An attacker compromised the server and may have used a collision hash in the MD5 algorithm to hide the changes to the /etc/shadow file
- An attacker compromised the server and may have also compromised the file integrity database to hide the changes to the /etc/shadow file
- An attacker compromised the server and may have installed a rootkit to always generate valid MD5 hashes to hide the changes to the /etc/shadow file
- An attacker compromised the server and may have used MD5 collision hashes to generate valid passwords, allowing further access to administrator accounts on the server
- An attacker compromised the server and may have used SELinux mandatory access controls to hide the changes to the /etc/shadow file
-
Following the successful response to a data-leakage incident, the incident team lead facilitates an exercise that focuses on continuous improvement of the organization’s incident response capabilities. Which of the following activities has the incident team lead executed?
- Lessons learned review
- Root cause analysis
- Incident audit
- Corrective action exercise
-
Following a recent network intrusion, a company wants to determine the current security awareness of all of its employees. Which of the following is the BEST way to test awareness?
- Conduct a series of security training events with comprehensive tests at the end
- Hire an external company to provide an independent audit of the network security posture
- Review the social media of all employees to see how much proprietary information is shared
- Send an email from a corporate account, requesting users to log onto a website with their enterprise account
-
A company’s security policy states any remote connections must be validated using two forms of network-based authentication. It also states local administrative accounts should not be used for any remote access. PKI currently is not configured within the network. RSA tokens have been provided to all employees, as well as a mobile application that can be used for 2FA authentication. A new NGFW has been installed within the network to provide security for external connections, and the company has decided to use it for VPN connections as well. Which of the following should be configured? (Choose two.)
- Certificate-based authentication
- TACACS+
- 802.1X
- RADIUS
- LDAP
- Local user database
-
The finance department has started to use a new payment system that requires strict PII security restrictions on various network devices. The company decides to enforce the restrictions and configure all devices appropriately. Which of the following risk response strategies is being used?
- Avoid
- Mitigate
- Transfer
- Accept
-
A security administrator is updating a company’s SCADA authentication system with a new application. To ensure interoperability between the legacy system and the new application, which of the following stakeholders should be involved in the configuration process before deployment? (Choose two.)
- Network engineer
- Service desk personnel
- Human resources administrator
- Incident response coordinator
- Facilities manager
- Compliance manager