PT0-001 : CompTIA PenTest+ Certification Exam : Part 01
PT0-001 : CompTIA PenTest+ Certification Exam : Part 01
-
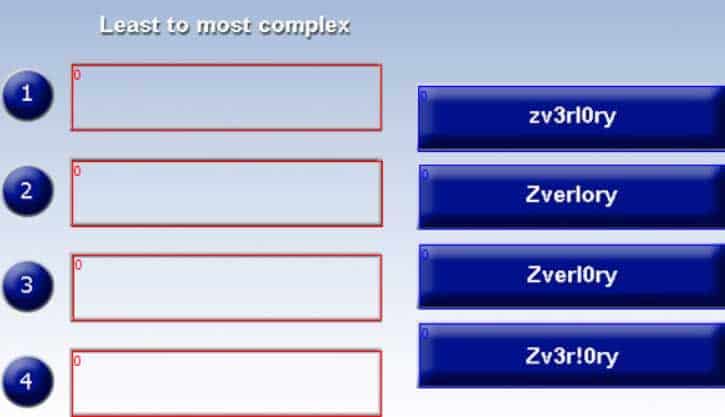
DRAG DROP
Place each of the following passwords in order of complexity from least complex (1) to most complex (4), based on the character sets represented. Each password may be used only once.
PT0-001 Part 01 Q01 001 Question 
PT0-001 Part 01 Q01 001 Answer -
DRAG DROP
A manager calls upon a tester to assist with diagnosing an issue within the following Python script:
#!/usr/bin/python s = “Administrator”
The tester suspects it is an issue with string slicing and manipulation. Analyze the following code segment and drag and drop the correct output for each string manipulation to its corresponding code segment. Options may be used once or not at all.

PT0-001 Part 01 Q02 002 Question 
PT0-001 Part 01 Q02 002 Answer -
A penetration tester has compromised a Windows server and is attempting to achieve persistence. Which of the following would achieve that goal?
-
schtasks.exe /create/tr “powershell.exe” Sv.ps1 /run
-
net session server | dsquery -user | net use c$
-
powershell && set-executionpolicy unrestricted
-
reg save HKLM\System\CurrentControlSet\Services\Sv.reg
-
-
A client has scheduled a wireless penetration test. Which of the following describes the scoping target information MOST likely needed before testing can begin?
- The physical location and network ESSIDs to be tested
- The number of wireless devices owned by the client
- The client’s preferred wireless access point vendor
- The bands and frequencies used by the client’s devices
-
Which of the following BEST describes some significant security weaknesses with an ICS, such as those used in electrical utility facilities, natural gas facilities, dams, and nuclear facilities?
- ICS vendors are slow to implement adequate security controls.
- ICS staff are not adequately trained to perform basic duties.
- There is a scarcity of replacement equipment for critical devices.
- There is a lack of compliance for ICS facilities.
-
A security analyst was provided with a detailed penetration report, which was performed against the organization’s DMZ environment. It was noted on the report that a finding has a CVSS base score of 10.0. Which of the following levels of difficulty would be required to exploit this vulnerability?
- Very difficult; perimeter systems are usually behind a firewall.
- Somewhat difficult; would require significant processing power to exploit.
- Trivial; little effort is required to exploit this finding.
- Impossible; external hosts are hardened to protect against attacks.
-
A penetration tester has gained access to a marketing employee’s device. The penetration tester wants to ensure that if the access is discovered, control of the device can be regained. Which of the following actions should the penetration tester use to maintain persistence to the device? (Select TWO.)
- Place an entry in HKLM\Software\Microsoft\CurrentVersion\Run to call au57d.ps1.
- Place an entry in C:\windows\system32\drivers\etc\hosts for 12.17.20.10 badcomptia.com.
- Place a script in C:\users\%username\local\appdata\roaming\temp\au57d.ps1.
- Create a fake service in Windows called RTAudio to execute manually.
- Place an entry for RTAudio in HKLM\CurrentControlSet\Services\RTAudio.
- Create a schedule task to call C:\windows\system32\drivers\etc\hosts.
-
Which of the following tools is used to perform a credential brute force attack?
- Hydra
- John the Ripper
- Hashcat
- Peach
-
Which of the following situations would cause a penetration tester to communicate with a system owner/client during the course of a test? (Select TWO.)
- The tester discovers personally identifiable data on the system.
- The system shows evidence of prior unauthorized compromise.
- The system shows a lack of hardening throughout.
- The system becomes unavailable following an attempted exploit.
- The tester discovers a finding on an out-of-scope system.
-
A penetration tester has performed a security assessment for a startup firm. The report lists a total of ten vulnerabilities, with five identified as critical. The client does not have the resources to immediately remediate all vulnerabilities. Under such circumstances, which of the following would be the BEST suggestion for the client?
- Apply easy compensating controls for critical vulnerabilities to minimize the risk, and then reprioritize remediation.
- Identify the issues that can be remediated most quickly and address them first.
- Implement the least impactful of the critical vulnerabilities’ remediations first, and then address other critical vulnerabilities
- Fix the most critical vulnerability first, even if it means fixing the other vulnerabilities may take a very long lime.
-
Which of the following is the reason why a penetration tester would run the chkconfig –del servicename command at the end of an engagement?
- To remove the persistence
- To enable persistence
- To report persistence
- To check for persistence
-
A penetration tester wants to target NETBIOS name service. Which of the following is the MOST likely command to exploit the NETBIOS name service?
-
arpspoof
-
nmap -
responder
-
burpsuite
-
-
A security consultant receives a document outlining the scope of an upcoming penetration test. This document contains IP addresses and times that each can be scanned. Which of the following would contain this information?
- Rules of engagement
- Request for proposal
- Master service agreement
- Business impact analysis
-
A penetration tester executes the following commands:

PT0-001 Part 01 Q14 003 Which of the following is a local host vulnerability that the attacker is exploiting?
- Insecure file permissions
- Application whitelisting
- Shell escape
- Writable service
-
A penetration tester reviews the scan results of a web application. Which of the following vulnerabilities is MOST critical and should be prioritized for exploitation?
- Stored XSS
- Fill path disclosure
- Expired certificate
- Clickjacking
-
A penetration tester observes that several high-numbered ports are listening on a public web server. However, the system owner says the application only uses port 443. Which of the following would be BEST to recommend?
- Transition the application to another port.
- Filter port 443 to specific IP addresses.
- Implement a web application firewall.
- Disable unneeded services.
-
A penetration tester was able to enter an SQL injection command into a text box and gain access to the information store on the database. Which of the following is the BEST recommendation that would mitigate the vulnerability?
- Randomize the credentials used to log in.
- Install host-based intrusion detection.
- Implement input normalization.
- Perform system hardening.
-
Black box penetration testing strategy provides the tester with:
- a target list
- a network diagram
- source code
- privileged credentials
-
Which of the following tools would a penetration tester leverage to conduct OSINT? (Select TWO).
- Shodan
- SET
- BeEF
- Wireshark
- Maltego
- Dynamo
-
A penetration tester is performing ARP spoofing against a switch. Which of the following should the penetration tester spoof to get the MOST information?
- MAC address of the client
- MAC address of the domain controller
- MAC address of the web server
- MAC address of the gateway