MS-500 : Microsoft 365 Security Administration : Part 01
MS-500 : Microsoft 365 Security Administration : Part 01
-
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Fabrikam, Inc. is manufacturing company that sells products through partner retail stores. Fabrikam has 5,000 employees located in offices throughout Europe.Existing Environment
Network Infrastructure
The network contains an Active Directory forest named fabrikam.com. Fabrikam has a hybrid Microsoft Azure Active Directory (Azure AD) environment.The company maintains some on-premises servers for specific applications, but most end-user applications are provided by a Microsoft 365 E5 subscription.
Problem Statements
Fabrikam identifies the following issues:– Since last Friday, the IT team has been receiving automated email messages that contain “Unhealthy Identity Synchronization Notification” in the subject line.
– Several users recently opened email attachments that contained malware. The process to remove the malware was time consuming.Requirements
Planned Changes
Fabrikam plans to implement the following changes:– Fabrikam plans to monitor and investigate suspicious sign-ins to Active Directory
– Fabrikam plans to provide partners with access to some of the data stored in Microsoft 365Application Administration
Fabrikam identifies the following application requirements for managing workload applications:– User administrators will work from different countries
– User administrators will use the Azure Active Directory admin center
– Two new administrators named Admin1 and Admin2 will be responsible for managing Microsoft Exchange Online onlySecurity Requirements
Fabrikam identifies the following security requirements:– Access to the Azure Active Directory admin center by the user administrators must be reviewed every seven days. If an administrator fails to respond to an access request within three days, access must be removed
– Users who manage Microsoft 365 workloads must only be allowed to perform administrative tasks for up to three hours at a time. Global administrators must be exempt from this requirement
– Users must be prevented from inviting external users to view company data. Only global administrators and a user named User1 must be able to send invitations
– Microsoft Defender for Identity must capture security group modifications for sensitive groups, such as Domain Admins in Active Directory
– Workload administrators must use multi-factor authentication (MFA) when signing in from an anonymous or an unfamiliar location
– The location of the user administrators must be audited when the administrators authenticate to Azure AD
– Email messages that include attachments containing malware must be delivered without the attachment
The principle of least privilege must be used whenever possible-
An administrator configures Azure AD Privileged Identity Management as shown in the following exhibit.
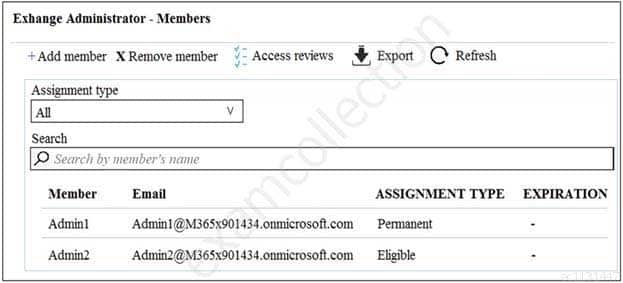
MS-500 Microsoft 365 Security Administration Part 01 Q01 001 What should you do to meet the security requirements?
- Change the Assignment Type for Admin2 to Permanent
- From the Azure Active Directory admin center, assign the Exchange administrator role to Admin2
- From the Azure Active Directory admin center, remove the Exchange administrator role to Admin1
- Change the Assignment Type for Admin1 to Eligible
-
You need to recommend a solution for the user administrators that meets the security requirements for auditing.
Which blade should you recommend using from the Azure Active Directory admin center?
- Sign-ins
- Azure AD Identity Protection
- Authentication methods
- Access review
-
HOTSPOT
You plan to configure an access review to meet the security requirements for the workload administrators. You create an access review policy and specify the scope and a group.
Which other settings should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
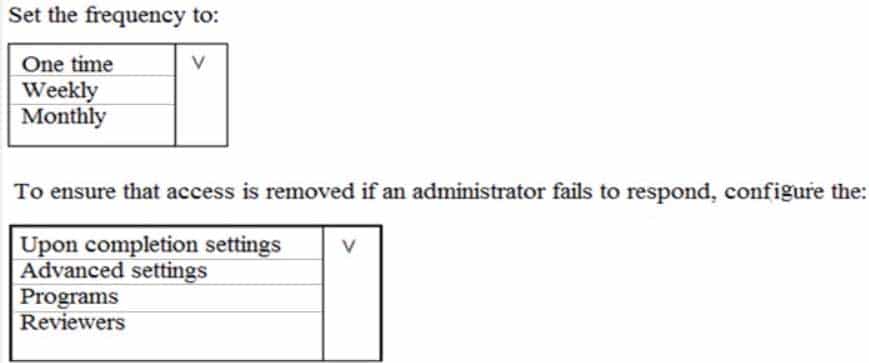
MS-500 Microsoft 365 Security Administration Part 01 Q01 002 Question 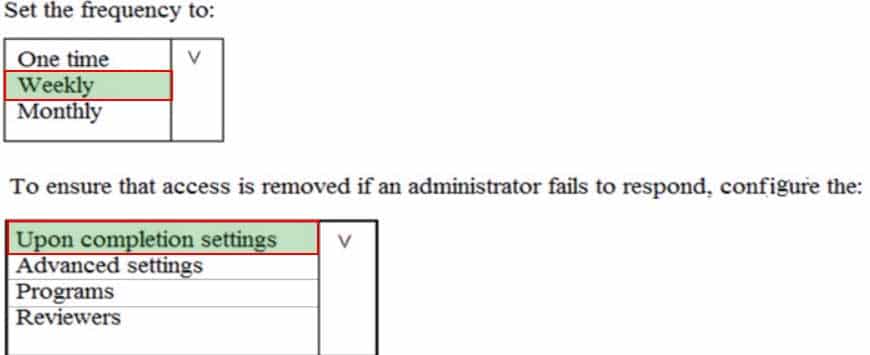
MS-500 Microsoft 365 Security Administration Part 01 Q01 002 Answer -
You need to recommend a solution to protect the sign-ins of Admin1 and Admin2.
What should you include in the recommendation?
- a device compliance policy
- an access review
- a user risk policy
- a sign-in risk policy
-
You need to resolve the issue that generates the automated email messages to the IT team.
Which tool should you run first?
- Synchronization Service Manager
- Azure AD Connect wizard
- Synchronization Rules Editor
- IdFix
-
-
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Litware, Inc. is a financial company that has 1,000 users in its main office in Chicago and 100 users in a branch office in San Francisco.Existing Environment
Internal Network Infrastructure
The network contains a single domain forest. The forest functional level is Windows Server 2016.Users are subject to sign-in hour restrictions as defined in Active Directory.
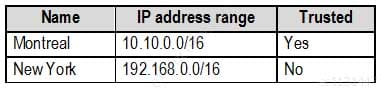
The network has the IP address ranges shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q02 003 The offices connect by using Multiprotocol Label Switching (MPLS).
The following operating systems are used on the network:
– Windows Server 2016
– Windows 10 Enterprise
– Windows 8.1 EnterpriseThe internal network contains the systems shown in the following table.
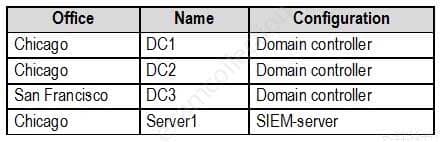
MS-500 Microsoft 365 Security Administration Part 01 Q02 004 Litware uses a third-party email system.
Cloud Infrastructure
Litware recently purchased Microsoft 365 subscription licenses for all users.Microsoft Azure Active Directory (Azure AD) Connect is installed and uses the default authentication settings. User accounts are not yet synced to Azure AD.
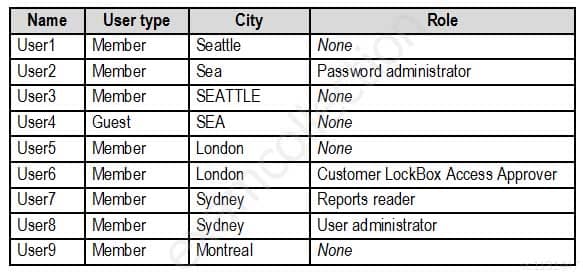
You have the Microsoft 365 users and groups shown in the following table.
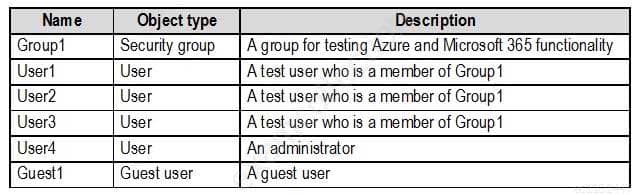
MS-500 Microsoft 365 Security Administration Part 01 Q02 005 Requirements
Planned Changes
Litware plans to implement the following changes:– Migrate the email system to Microsoft Exchange Online
– Implement Azure AD Privileged Identity ManagementSecurity Requirements
Litware identifies the following security requirements:
– Create a group named Group3 that will be used for publishing sensitivity labels to pilot users. – Group3 must only contain user accounts
– Use Microsoft Defender for Identity to detect any security threats that target the forest
– Prevent users locked out of Active Directory from signing in to Azure AD and Active Directory
– Implement a permanent eligible assignment of the Compliance administrator role for User1
– Configure domain-joined servers to ensure that they report sensor data to Microsoft Defender for Endpoint
– Prevent access to Azure resources for the guest user accounts by default
– Ensure that all domain-joined computers are registered to Azure ADMulti-factor authentication (MFA) Requirements
Security features of Microsoft Office 365 and Azure will be tested by using pilot Azure user accounts.
You identify the following requirements for testing MFA:
– Pilot users must use MFA unless they are signing in from the internal network of the Chicago office. MFA must NOT be used on the Chicago office internal network.
– If an authentication attempt is suspicious, MFA must be used, regardless of the user location.
– Any disruption of legitimate authentication attempts must be minimized.General Requirements
Litware wants to minimize the deployment of additional servers and services in the Active Directory forest.-
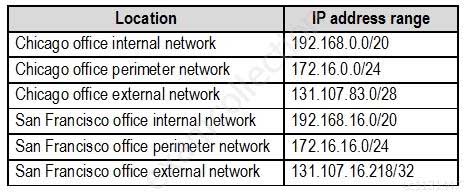
Which IP address space should you include in the Trusted IP MFA configuration?
- 131.107.83.0/28
- 192.168.16.0/20
- 172.16.0.0/24
- 192.168.0.0/20
Explanation:
Pilot users must use MFA unless they are signing in from the internal network of the Chicago office. MFA must NOT be used on the Chicago office internal network. We must therefore use the IP range of the external network. -
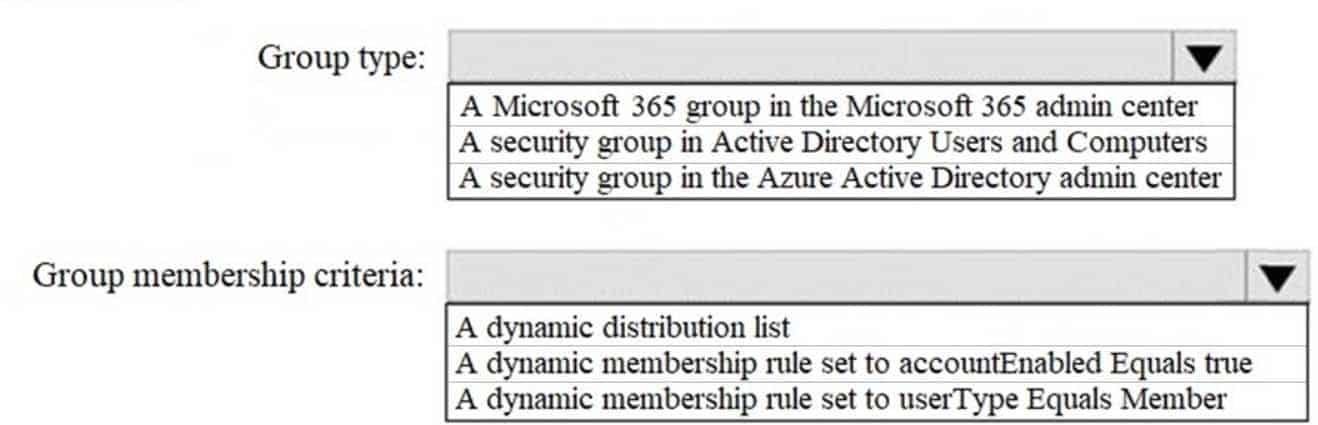
HOTSPOT
How should you configure Group3? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
MS-500 Microsoft 365 Security Administration Part 01 Q02 006 Question 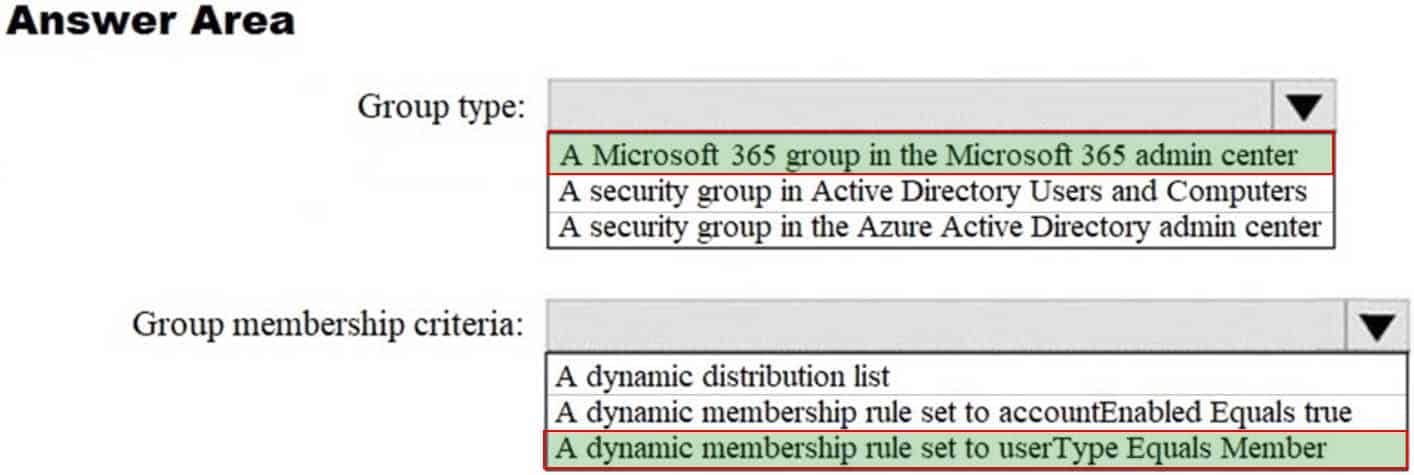
MS-500 Microsoft 365 Security Administration Part 01 Q02 006 Answer -
HOTSPOT
How should you configure Azure AD Connect? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
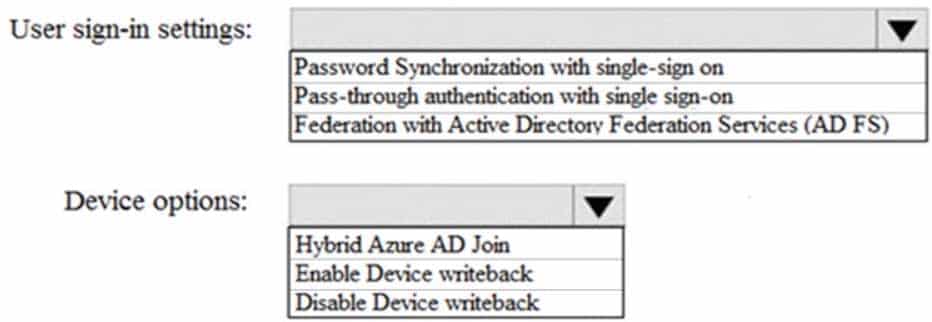
MS-500 Microsoft 365 Security Administration Part 01 Q02 007 Question 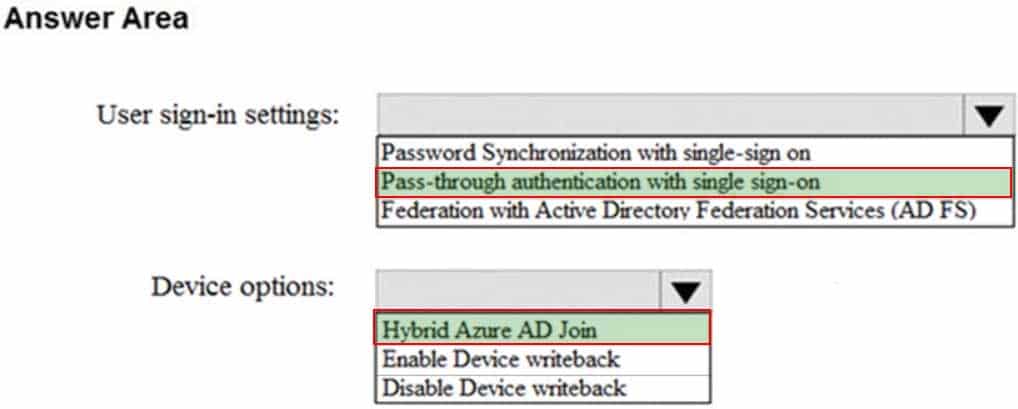
MS-500 Microsoft 365 Security Administration Part 01 Q02 007 Answer -
You need to create Group3.
What are two possible ways to create the group?
- a Microsoft 365 group in the Microsoft 365 admin center
- a mail-enabled security group in the Microsoft 365 admin center
- a security group in the Microsoft 365 admin center
- a distribution list in the Microsoft 365 admin center\
- a security group in the Azure AD admin center
-
-
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and two branch offices in Seattle and New York.
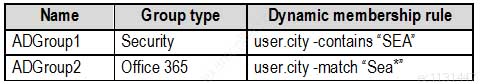
The company has the offices shown in the following table.
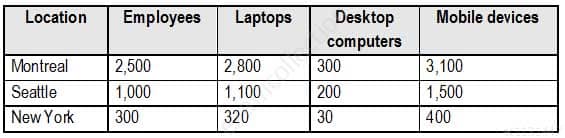
MS-500 Microsoft 365 Security Administration Part 01 Q03 008 Contoso has IT, human resources (HR), legal, marketing, and finance departments. Contoso uses Microsoft 365.
Existing Environment
Infrastructure
The network contains an Active Directory domain named contoso.com that is synced to a Microsoft Azure Active Directory (Azure AD) tenant. Password writeback is enabled.
The domain contains servers that run Windows Server 2016. The domain contains laptops and desktop computers that run Windows 10 Enterprise.
Each client computer has a single volume.
Each office connects to the Internet by using a NAT device. The offices have the IP addresses shown in the following table.
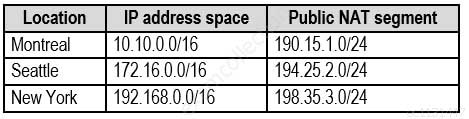
MS-500 Microsoft 365 Security Administration Part 01 Q03 009 Named locations are defined in Azure AD as shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q03 010 From the Multi-Factor Authentication page, an address space of 198.35.3.0/24 is defined in the trusted IPs list.
Azure Multi-Factor Authentication (MFA) is enabled for the users in the finance department.
The tenant contains the users shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q03 011 The tenant contains the groups shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q03 012 Customer Lockbox is enabled in Microsoft 365.
Microsoft Endpoint Manager Configuration
The devices enrolled in Microsoft Endpoint Manager are configured as shown in the following table.
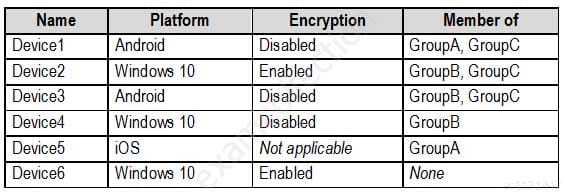
MS-500 Microsoft 365 Security Administration Part 01 Q03 013 The device compliance policies in Microsoft Endpoint Manager are configured as shown in the following table.
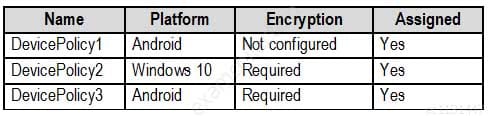
MS-500 Microsoft 365 Security Administration Part 01 Q03 014 The device compliance policies have the assignments shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q03 015 The Mark devices with no compliance policy assigned as setting is set to Compliant.
Requirements
Technical Requirements
Contoso identifies the following technical requirements:
– Use the principle of least privilege
– Enable User1 to assign the Reports reader role to users
– Ensure that User6 approves Customer Lockbox requests as quickly as possible
– Ensure that User9 can enable and configure Azure AD Privileged Identity Management-
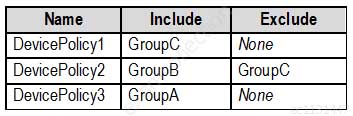
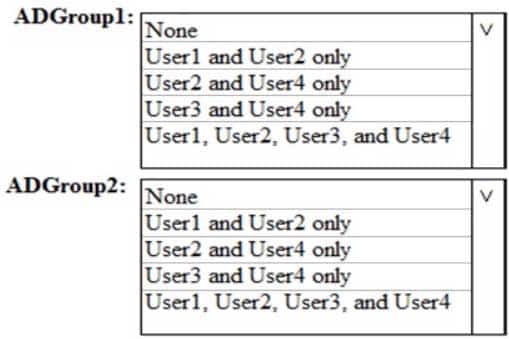
HOTSPOT
Which users are members of ADGroup1 and ADGroup2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
MS-500 Microsoft 365 Security Administration Part 01 Q03 016 Question 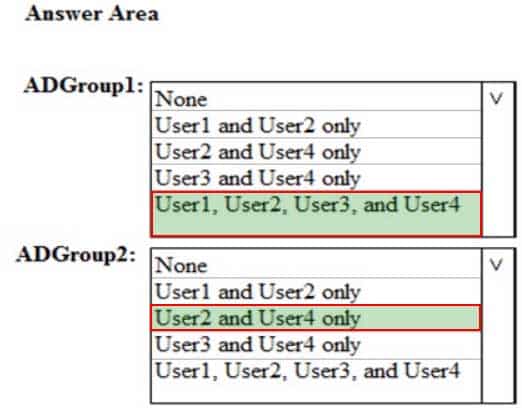
MS-500 Microsoft 365 Security Administration Part 01 Q03 016 Answer -
HOTSPOT
You are evaluating which finance department users will be prompted for Azure MFA credentials.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
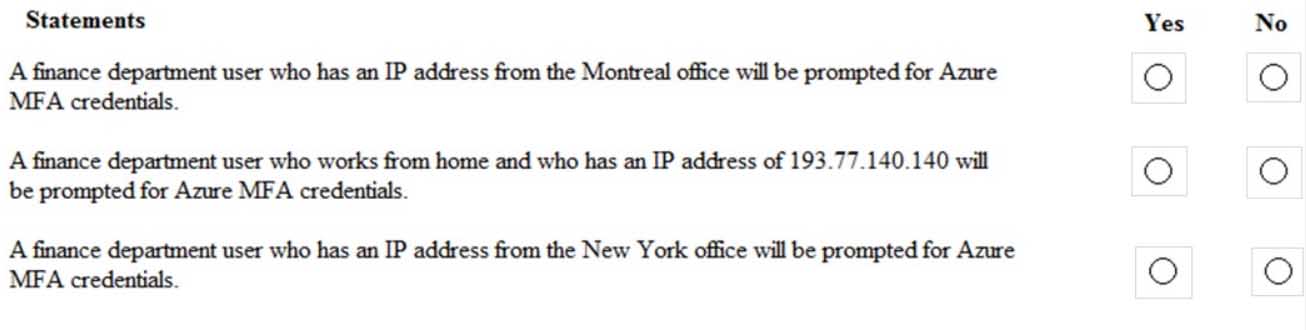
MS-500 Microsoft 365 Security Administration Part 01 Q03 017 Question 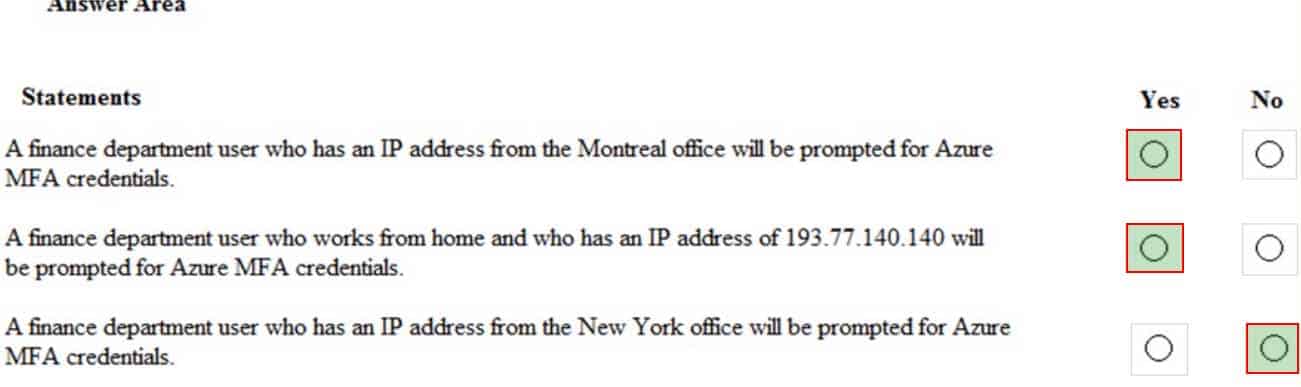
MS-500 Microsoft 365 Security Administration Part 01 Q03 017 Answer -
Which user passwords will User2 be prevented from resetting?
- User6 and User7
- User4 and User6
- User4 only
- User7 and User8
- User8 only
Explanation:
Assign the Password admin role to a user who needs to reset passwords for non-administrators and Password Administrators. -
You need to meet the technical requirements for User9. What should you do?
- Assign the Privileged administrator role to User9 and configure a mobile phone number for User9
- Assign the Compliance administrator role to User9 and configure a mobile phone number for User9
- Assign the Security administrator role to User9
- Assign the Global administrator role to User9
Explanation:
To implement PIM, you must be a global admin. -
Which role should you assign to User1?
- Global administrator
- User administrator
- Privileged role administrator
- Security administrator
Explanation:
Privileged Role Administrator can manage role assignments in Azure Active Directory, as well as within Azure AD Privileged Identity Management.
-
-
You have several Conditional Access policies that block noncompliant devices from connecting to services.
You need to identity which devices are blocked by which policies.
What should you use?
- the Setting compliance report in the Microsoft Endpoint Manager admin center
- Sign-ins in the Azure Active Directory admin center
- Activity log in the Cloud App Security admin center
- Audit logs in the Azure Active Directory admin center
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 E5 subscription that is associated to a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com.
You use Active Directory Federation Services (AD FS) to federate on-premises Active Directory and the tenant. Azure AD Connect has the following settings:
– Source Anchor: object GUID
– Password Hash Synchronization: Disabled
– Password writeback: Disabled
– Directory extension attribute sync: Disabled
– Azure AD app and attribute filtering: Disabled
– Exchange hybrid deployment: Disabled
– User writeback: DisabledYou need to ensure that you can use leaked credentials detection in Azure AD Identity Protection.
Solution: You modify the Azure AD app and attribute filtering settings.
Does that meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 E5 subscription that is associated to a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com.
You use Active Directory Federation Services (AD FS) to federate on-premises Active Directory and the tenant. Azure AD Connect has the following settings:
– Source Anchor: object GUID
– Password Hash Synchronization: Disabled
– Password writeback: Disabled
– Directory extension attribute sync: Disabled
– Azure AD app and attribute filtering: Disabled
– Exchange hybrid deployment: Disabled
– User writeback: DisabledYou need to ensure that you can use leaked credentials detection in Azure AD Identity Protection.
Solution: You modify the Password Hash Synchronization settings.
Does that meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 E5 subscription that is associated to a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com.
You use Active Directory Federation Services (AD FS) to federate on-premises Active Directory and the tenant. Azure AD Connect has the following settings:
– Source Anchor: object GUID
– Password Hash Synchronization: Disabled
– Password writeback: Disabled
– Directory extension attribute sync: Disabled
– Azure AD app and attribute filtering: Disabled
– Exchange hybrid deployment: Disabled
– User writeback: DisabledYou need to ensure that you can use leaked credentials detection in Azure AD Identity Protection.
Solution: You modify the Source Anchor settings.
Does that meet the goal?
- Yes
- No
-
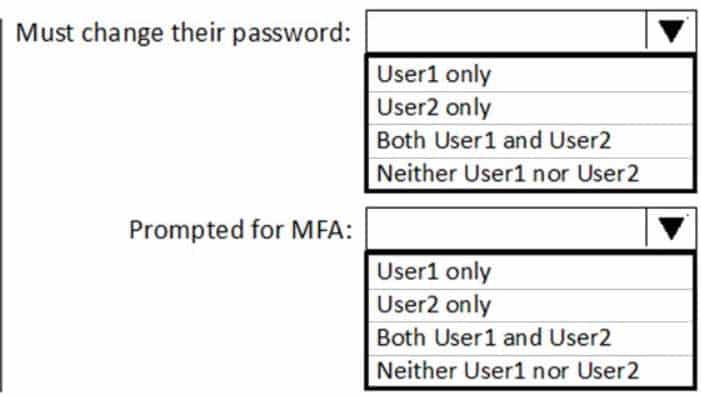
HOTSPOT
You have a Microsoft 365 subscription that uses a default domain name of contoso.com.
The multi-factor authentication (MFA) service settings are configured as shown in the exhibit. (Click the Exhibit tab.)
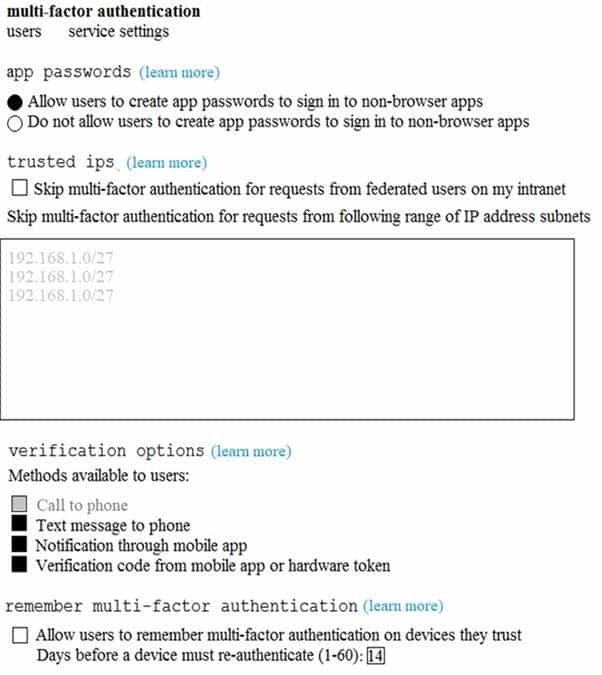
MS-500 Microsoft 365 Security Administration Part 01 Q08 018 In contoso.com, you create the users shown in the following table.

MS-500 Microsoft 365 Security Administration Part 01 Q08 019 What is the effect of the configuration? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
MS-500 Microsoft 365 Security Administration Part 01 Q08 020 Question 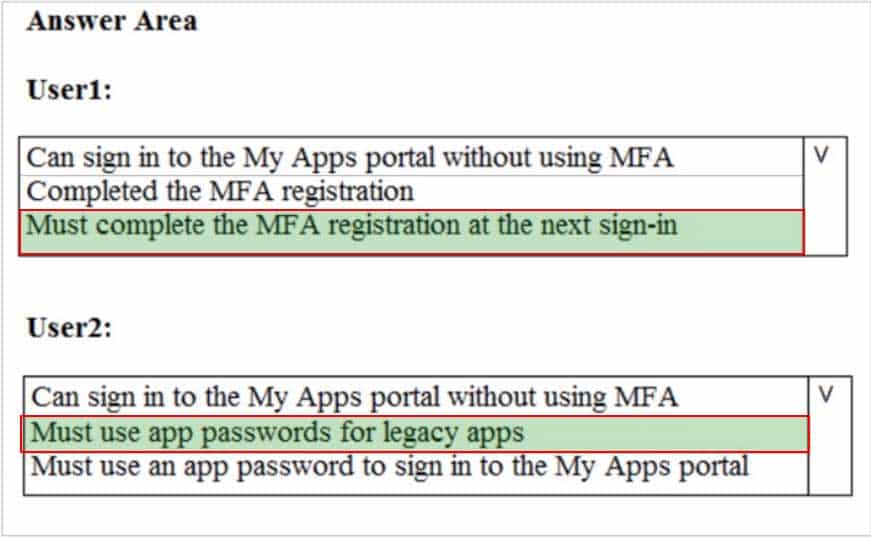
MS-500 Microsoft 365 Security Administration Part 01 Q08 020 Answer -
HOTSPOT
You configure Microsoft Azure Active Directory (Azure AD) Connect as shown in the following exhibit.
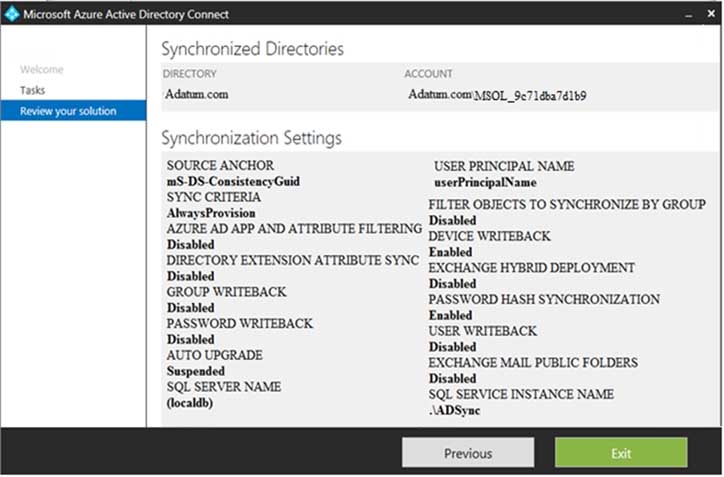
MS-500 Microsoft 365 Security Administration Part 01 Q09 021 Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
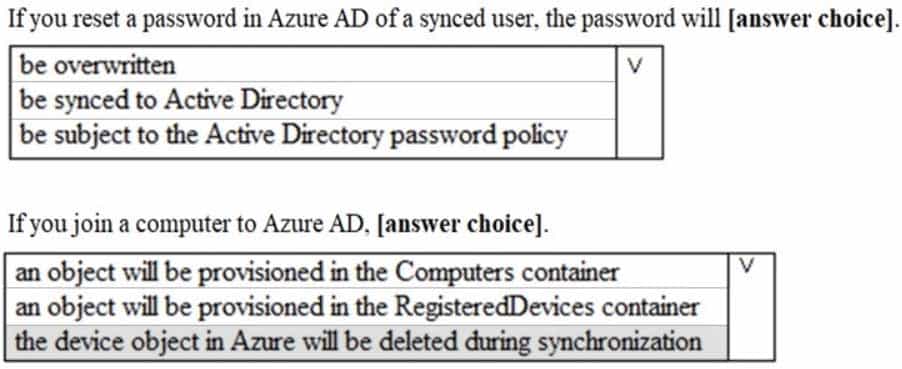
MS-500 Microsoft 365 Security Administration Part 01 Q09 022 Question 
MS-500 Microsoft 365 Security Administration Part 01 Q09 022 Answer -
You have a hybrid Microsoft 365 environment. All computers run Windows 10 and are managed by using Microsoft Intune.
You need to create a Microsoft Azure Active Directory (Azure AD) conditional access policy that will allow only Windows 10 computers marked as compliant to establish a VPN connection to the on-premises network.
What should you do first?
- From the Azure Active Directory admin center, create a new certificate
- Enable Application Proxy in Azure AD
- From Active Directory Administrative Center, create a Dynamic Access Control policy
- From the Azure Active Directory admin center, configure authentication methods
-
You have a Microsoft 365 subscription.
From the Microsoft 365 admin center, you create a new user.
You plan to assign the Reports reader role to the user.
You need to view the permissions of the Reports reader role.
Which admin center should you use?
- Azure Active Directory
- Cloud App Security
- Security & Compliance
- Microsoft 365
-
You have a Microsoft 365 E5 subscription.
You need to ensure that users who are assigned the Exchange administrator role have time-limited permissions and must use multi-factor authentication (MFA) to request the permissions.
What should you use to achieve the goal?
- Security & Compliance permissions
- Microsoft Azure Active Directory (Azure AD) Privileged Identity Management
- Microsoft Azure AD group management
- Microsoft Office 365 user management
-
Your company has a Microsoft 365 subscription.
The company does not permit users to enroll personal devices in mobile device management (MDM).
Users in the sales department have personal iOS devices.
You need to ensure that the sales department users can use the Microsoft Power BI app from iOS devices to access the Power BI data in your tenant.
The users must be prevented from backing up the app’s data to iCloud.
What should you create?
- a conditional access policy in Microsoft Azure Active Directory (Azure AD) that has a device state condition
- an app protection policy in Microsoft Endpoint Manager
- a conditional access policy in Microsoft Azure Active Directory (Azure AD) that has a client apps condition
- a device compliance policy in Microsoft Endpoint Manager
-
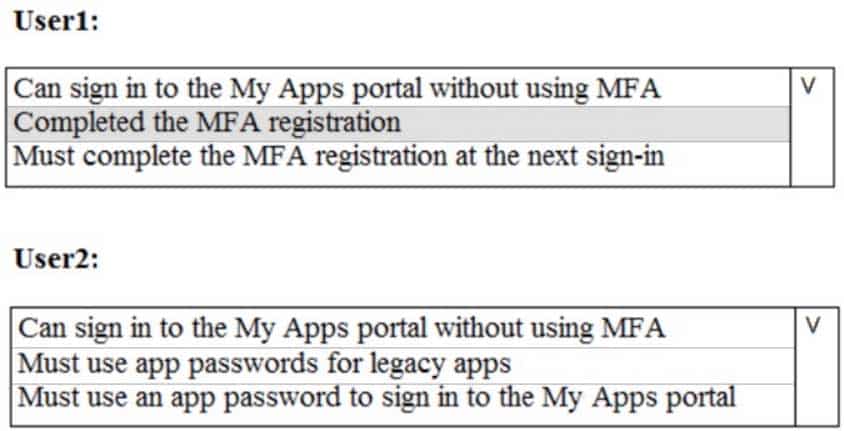
HOTSPOT
You have a Microsoft 365 E5 subscription.
Users and device objects are added and removed daily. Users in the sales department frequently change their device.
You need to create three following groups:
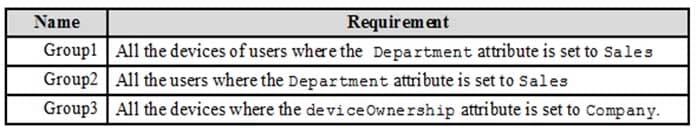
MS-500 Microsoft 365 Security Administration Part 01 Q14 023 The solution must minimize administrative effort.
What is the minimum number of groups you should create for each type of membership? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
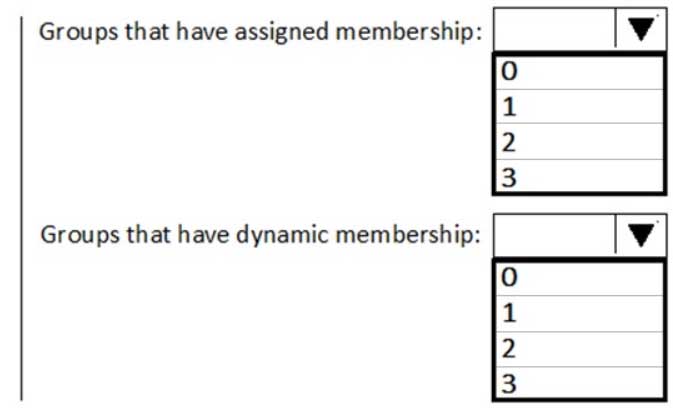
MS-500 Microsoft 365 Security Administration Part 01 Q14 024 Question 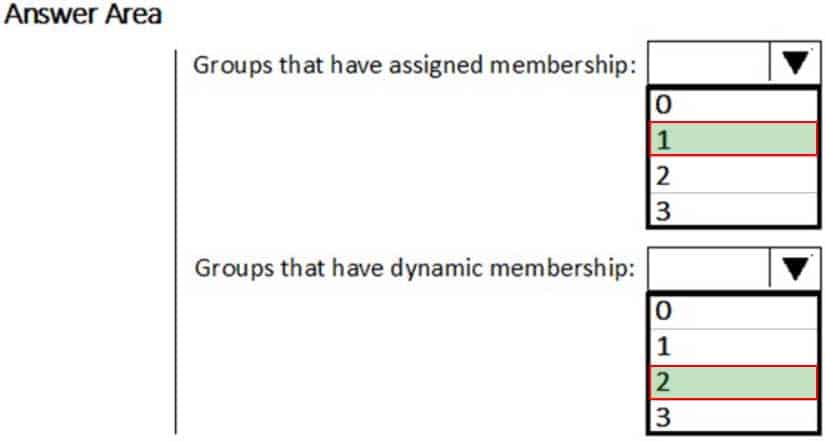
MS-500 Microsoft 365 Security Administration Part 01 Q14 024 Answer Explanation:Group 1 has to be assigned because you can’t create a device group based on the device owners’ attributes.
Group 2 can be dynamic because a user does have a department attribute.
Group 3 can be dynamic because a device does have a device ownership attribute. -
Your company has a main office and a Microsoft 365 subscription.
You need to enforce Microsoft Azure Multi-Factor Authentication (MFA) by using conditional access for all users who are NOT physically present in the office.
What should you include in the configuration?
- a user risk policy
- a sign-in risk policy
- a named location in Azure Active Directory (Azure AD)
- an Azure MFA Server
-
HOTSPOT
You have a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com that contains the users shown in the following table.
MS-500 Microsoft 365 Security Administration Part 01 Q16 025 You create and enforce an Azure AD Identity Protection user risk policy that has the following settings:
– Assignments: Include Group1, Exclude Group2
– Conditions: Sign-in risk of Low and above
– Access: Allow access, Require password changeYou need to identify how the policy affects User1 and User2.
What occurs when User1 and User2 sign in from an unfamiliar location? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
MS-500 Microsoft 365 Security Administration Part 01 Q16 026 Question 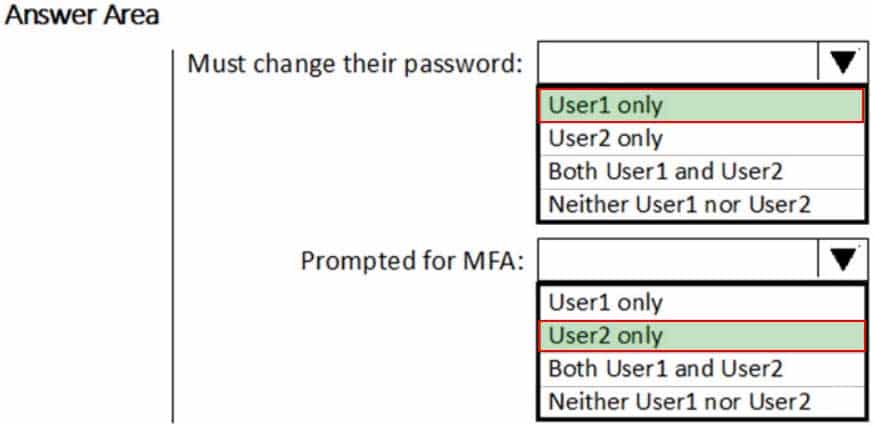
MS-500 Microsoft 365 Security Administration Part 01 Q16 026 Answer Explanation:Box 1: User1 only
The Azure AD Identity Protection user risk policy is excluded from Group2. Exclusion overrides inclusion. Therefore, the policy will not affect User2. Thus, only User 1 needs to change the Password.Box 2: User2 only
MFA will be triggered for User 2. -
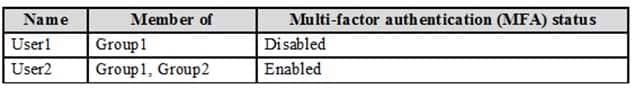
HOTSPOT
You have a Microsoft Azure Active Directory (Azure AD) tenant named contoso.com that contains the users shown in the following table.
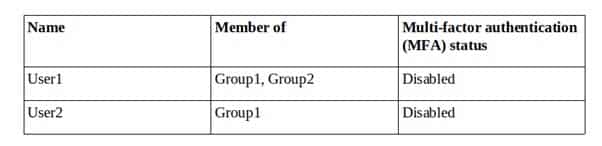
MS-500 Microsoft 365 Security Administration Part 01 Q17 027 You create and enforce an Azure AD Identity Protection sign-in risk policy that has the following settings:
– Assignments: Include Group1, Exclude Group2
– Conditions: Sign-in risk of Low and above
– Access: Allow access, Require multi-factor authenticationYou need to identify how the policy affects User1 and User2.
What occurs when each user signs in from an anonymous IP address? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
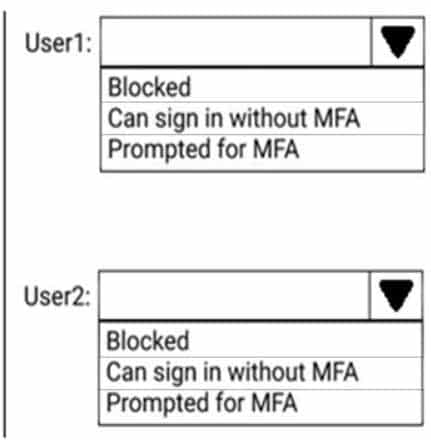
MS-500 Microsoft 365 Security Administration Part 01 Q17 028 Question 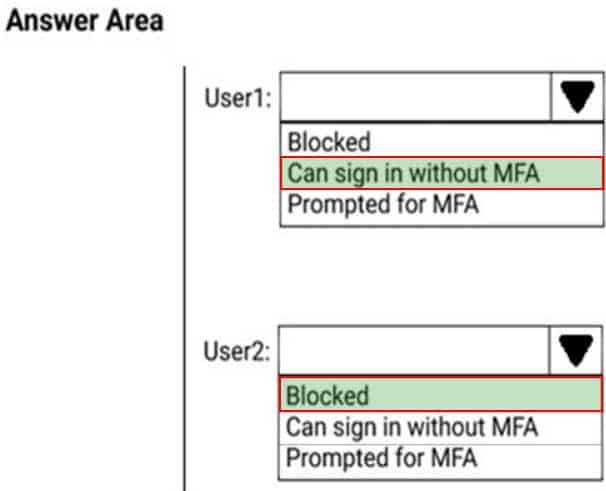
MS-500 Microsoft 365 Security Administration Part 01 Q17 028 Answer -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an on-premises Active Directory domain named contoso.com.
You install and run Azure AD Connect on a server named Server1 that runs Windows Server.
You need to view Azure AD Connect events.
You use the Security event log on Server1.
Does that meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an on-premises Active Directory domain named contoso.com.
You install and run Azure AD Connect on a server named Server1 that runs Windows Server.
You need to view Azure AD Connect events.
You use the Directory Service event log on Server1.
Does that meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an on-premises Active Directory domain named contoso.com.
You install and run Azure AD Connect on a server named Server1 that runs Windows Server.
You need to view Azure AD Connect events.
You use the System event log on Server1.
Does that meet the goal?
- Yes
- No