SC-200 : Microsoft Security Operations Analyst : Part 03
SC-200 : Microsoft Security Operations Analyst : Part 03
-
You have an Azure subscription that contains a Log Analytics workspace.
You need to enable just-in-time (JIT) VM access and network detections for Azure resources.
Where should you enable Azure Defender?
- at the subscription level
- at the workspace level
- at the resource level
-
You use Azure Defender.
You have an Azure Storage account that contains sensitive information.
You need to run a PowerShell script if someone accesses the storage account from a suspicious IP address.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- From Azure Security Center, enable workflow automation.
- Create an Azure logic app that has a manual trigger.
- Create an Azure logic app that has an Azure Security Center alert trigger.
- Create an Azure logic app that has an HTTP trigger.
- From Azure Active Directory (Azure AD), add an app registration.
-
HOTSPOT
You manage the security posture of an Azure subscription that contains two virtual machines name vm1 and vm2.
The secure score in Azure Security Center is shown in the Security Center exhibit. (Click the Security Center tab.)
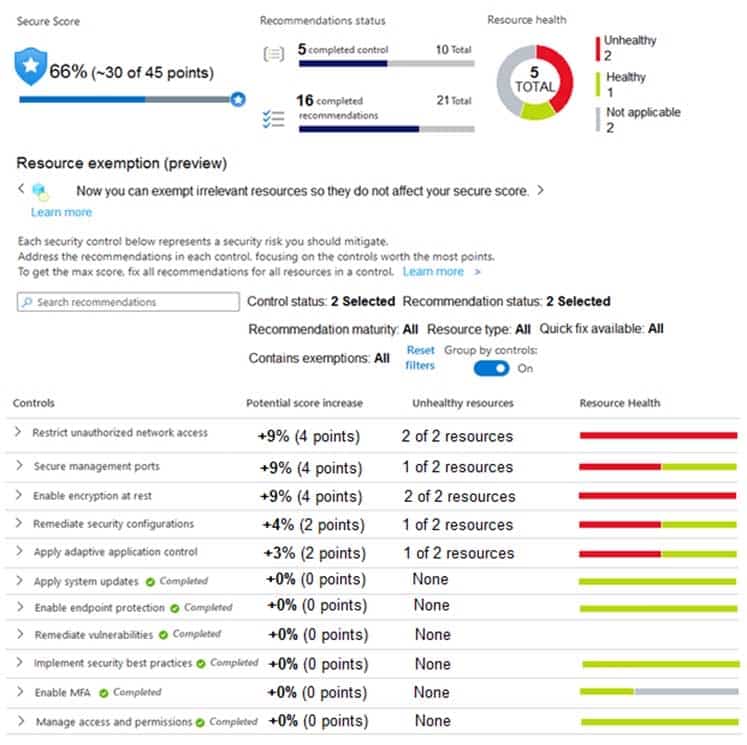
SC-200 Microsoft Security Operations Analyst Part 03 Q03 024 Azure Policy assignments are configured as shown in the Policies exhibit. (Click the Policies tab.)
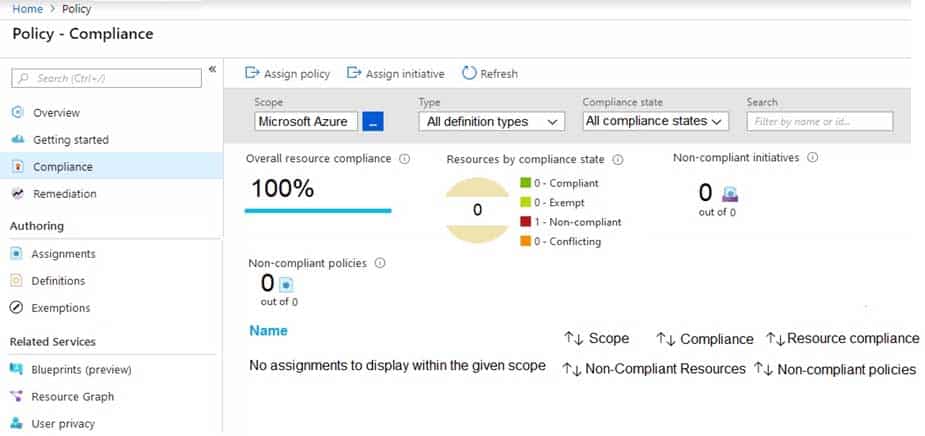
SC-200 Microsoft Security Operations Analyst Part 03 Q03 025 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
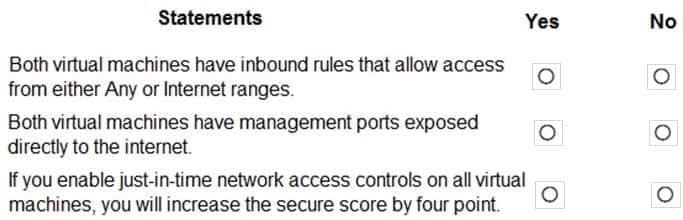
SC-200 Microsoft Security Operations Analyst Part 03 Q03 026 Question 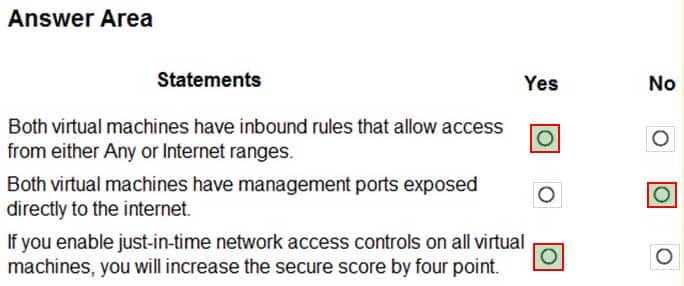
SC-200 Microsoft Security Operations Analyst Part 03 Q03 026 Answer -
DRAG DROP
You are informed of a new common vulnerabilities and exposures (CVE) vulnerability that affects your environment.
You need to use Microsoft Defender Security Center to request remediation from the team responsible for the affected systems if there is a documented active exploit available.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
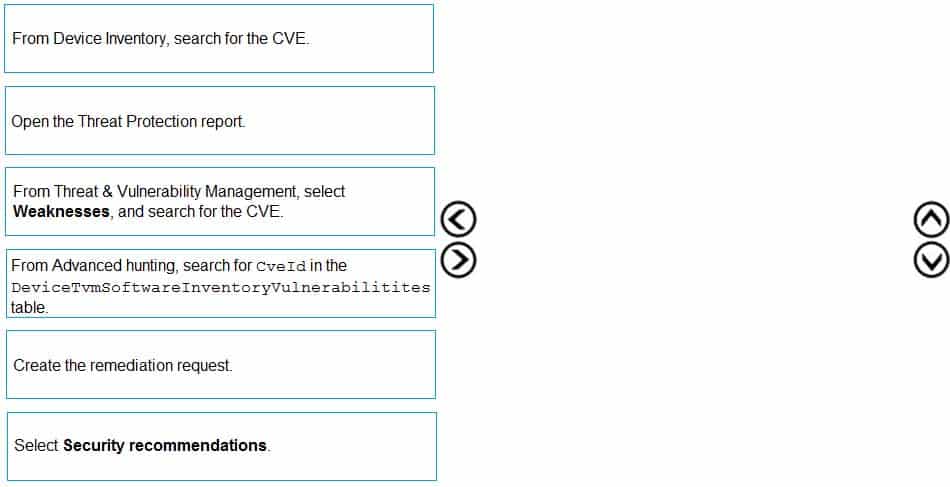
SC-200 Microsoft Security Operations Analyst Part 03 Q04 027 Question 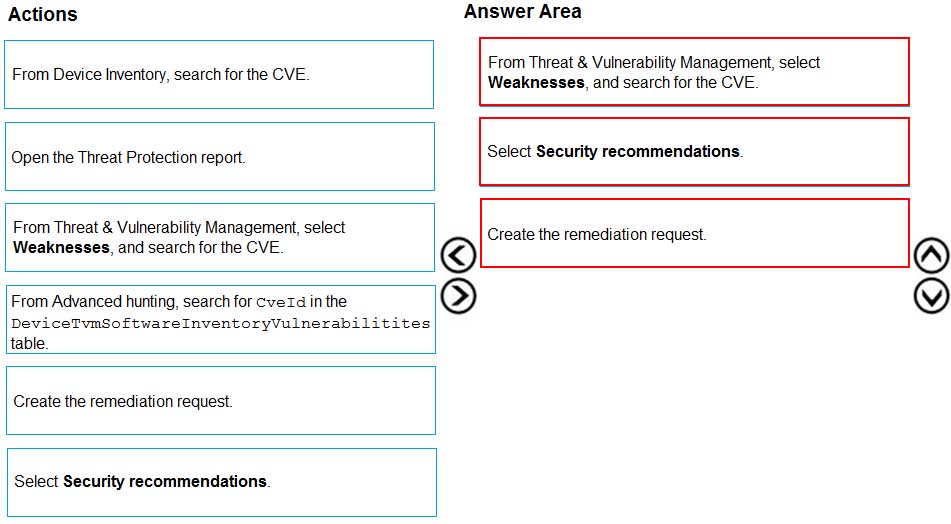
SC-200 Microsoft Security Operations Analyst Part 03 Q04 027 Answer -
You use Azure Security Center.
You receive a security alert in Security Center.
You need to view recommendations to resolve the alert in Security Center.
What should you do?
- From Security alerts, select the alert, select Take Action, and then expand the Prevent future attacks section.
- From Security alerts, select Take Action, and then expand the Mitigate the threat section.
- From Regulatory compliance, download the report.
- From Recommendations, download the CSV report.
-
You have a suppression rule in Azure Security Center for 10 virtual machines that are used for testing. The virtual machines run Windows Server.
You are troubleshooting an issue on the virtual machines.
In Security Center, you need to view the alerts generated by the virtual machines during the last five days.
What should you do?
- Change the rule expiration date of the suppression rule.
- Change the state of the suppression rule to Disabled.
- Modify the filter for the Security alerts page.
- View the Windows event logs on the virtual machines.
-
HOTSPOT
You have an Azure Storage account that will be accessed by multiple Azure Function apps during the development of an application.
You need to hide Azure Defender alerts for the storage account.
Which entity type and field should you use in a suppression rule? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
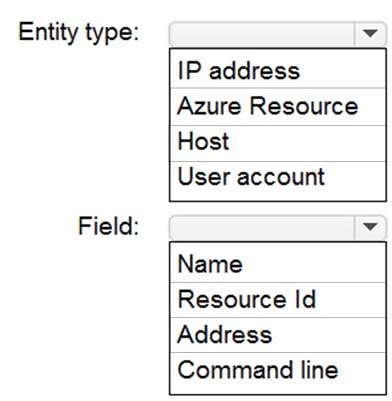
SC-200 Microsoft Security Operations Analyst Part 03 Q07 028 Question 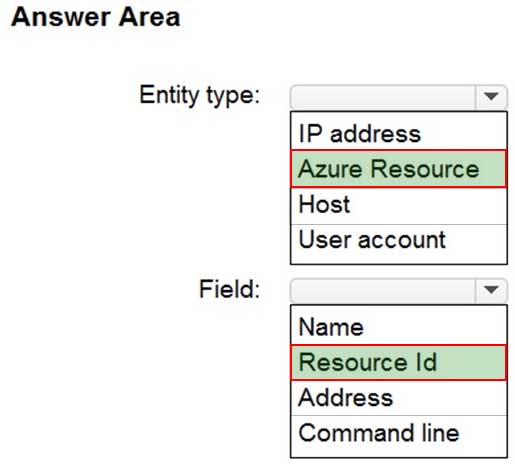
SC-200 Microsoft Security Operations Analyst Part 03 Q07 028 Answer -
You create an Azure subscription.
You enable Azure Defender for the subscription.
You need to use Azure Defender to protect on-premises computers.
What should you do on the on-premises computers?
- Install the Log Analytics agent.
- Install the Dependency agent.
- Configure the Hybrid Runbook Worker role.
- Install the Connected Machine agent.
Explanation:Security Center collects data from your Azure virtual machines (VMs), virtual machine scale sets, IaaS containers, and non-Azure (including on-premises) machines to monitor for security vulnerabilities and threats.
Data is collected using:
– The Log Analytics agent, which reads various security-related configurations and event logs from the machine and copies the data to your workspace for analysis. Examples of such data are: operating system type and version, operating system logs (Windows event logs), running processes, machine name, IP addresses, and logged in user.
– Security extensions, such as the Azure Policy Add-on for Kubernetes, which can also provide data to Security Center regarding specialized resource types. -
A security administrator receives email alerts from Azure Defender for activities such as potential malware uploaded to a storage account and potential successful brute force attacks.
The security administrator does NOT receive email alerts for activities such as antimalware action failed and suspicious network activity. The alerts appear in Azure Security Center.
You need to ensure that the security administrator receives email alerts for all the activities.
What should you configure in the Security Center settings?
- the severity level of email notifications
- a cloud connector
- the Azure Defender plans
- the integration settings for Threat detection
-
DRAG DROP
You have an Azure Functions app that generates thousands of alerts in Azure Security Center each day for normal activity.
You need to hide the alerts automatically in Security Center.
Which three actions should you perform in sequence in Security Center? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
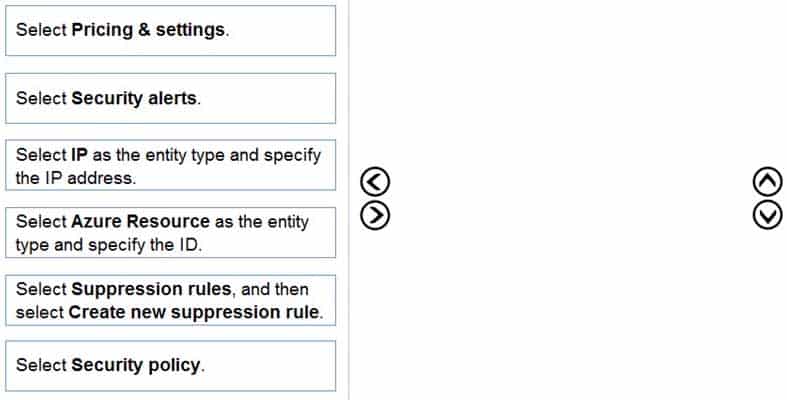
SC-200 Microsoft Security Operations Analyst Part 03 Q10 029 Question 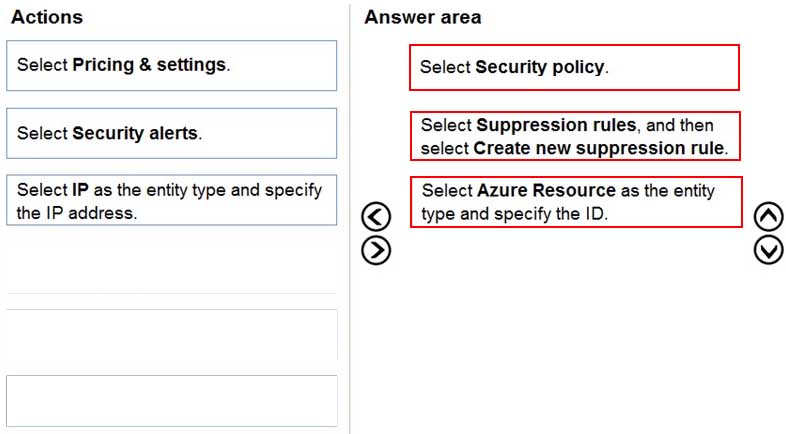
SC-200 Microsoft Security Operations Analyst Part 03 Q10 029 Answer -
DRAG DROP
You have an Azure subscription.
You need to delegate permissions to meet the following requirements:
– Enable and disable Azure Defender.
– Apply security recommendations to resource.The solution must use the principle of least privilege.
Which Azure Security Center role should you use for each requirement? To answer, drag the appropriate roles to the correct requirements. Each role may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
SC-200 Microsoft Security Operations Analyst Part 03 Q11 030 Question 
SC-200 Microsoft Security Operations Analyst Part 03 Q11 030 Answer -
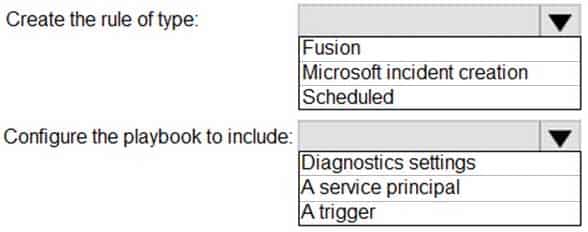
HOTSPOT
You have an Azure subscription that uses Azure Defender.
You plan to use Azure Security Center workflow automation to respond to Azure Defender threat alerts.
You need to create an Azure policy that will perform threat remediation automatically.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
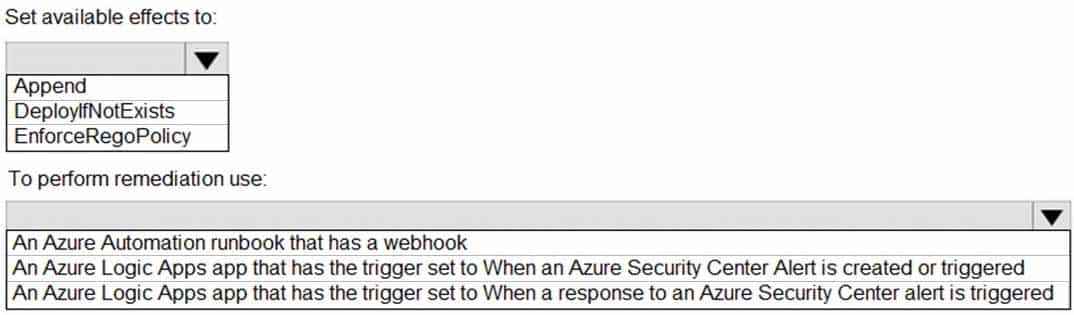
SC-200 Microsoft Security Operations Analyst Part 03 Q12 031 Question 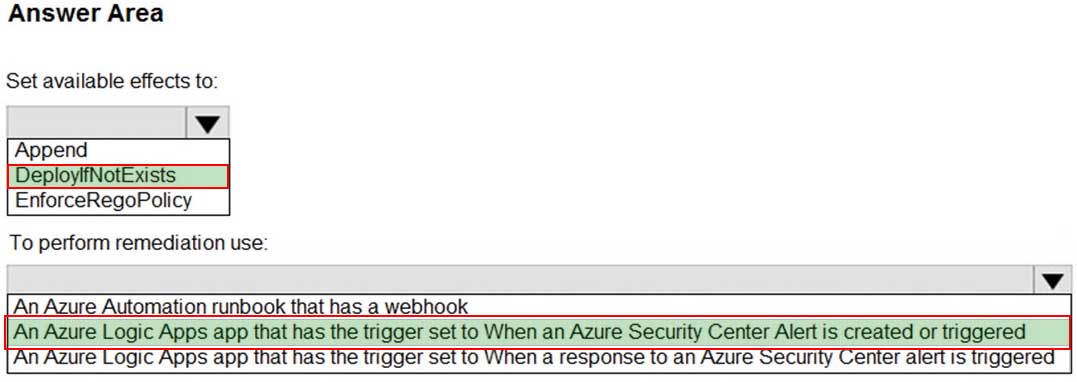
SC-200 Microsoft Security Operations Analyst Part 03 Q12 031 Answer -
Case study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
A company named Contoso Ltd. has a main office and five branch offices located throughout North America. The main office is in Seattle. The branch offices are in Toronto, Miami, Houston, Los Angeles, and Vancouver.
Contoso has a subsidiary named Fabrikam, Ltd. that has offices in New York and San Francisco.
Existing Environment
End-User Environment
All users at Contoso use Windows 10 devices. Each user is licensed for Microsoft 365. In addition, iOS devices are distributed to the members of the sales team at Contoso.
Cloud and Hybrid Infrastructure
All Contoso applications are deployed to Azure.
You enable Microsoft Cloud App Security.
Contoso and Fabrikam have different Azure Active Directory (Azure AD) tenants. Fabrikam recently purchased an Azure subscription and enabled Azure Defender for all supported resource types.
Current Problems
The security team at Contoso receives a large number of cybersecurity alerts. The security team spends too much time identifying which cybersecurity alerts are legitimate threats, and which are not.
The Contoso sales team uses only iOS devices. The sales team members exchange files with customers by using a variety of third-party tools. In the past, the sales team experienced phishing attacks on their devices.
The marketing team at Contoso has several Microsoft SharePoint Online sites for collaborating with external vendors. The marketing team has had several incidents in which vendors uploaded files that contain malware.
The executive team at Contoso suspects a security breach. The executive team requests that you identify which files had more than five activities during the past 48 hours, including data access, download, or deletion for Microsoft Cloud App Security-protected applications.
Requirements
Planned Changes
Contoso plans to integrate the security operations of both companies and manage all security operations centrally.
Technical Requirements
Contoso identifies the following technical requirements:
– Receive alerts if an Azure virtual machine is under brute force attack.
– Use Azure Sentinel to reduce organizational risk by rapidly remediating active attacks on the environment.
– Implement Azure Sentinel queries that correlate data across the Azure AD tenants of Contoso and Fabrikam.
– Develop a procedure to remediate Azure Defender for Key Vault alerts for Fabrikam in case of external attackers and a potential compromise of its own Azure AD applications.
– Identify all cases of users who failed to sign in to an Azure resource for the first time from a given country. A junior security administrator provides you with the following incomplete query.BehaviorAnalytics | where ActivityType == "FailedLogOn" | where ________ == True
-
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
- Security alerts in Azure Security Center
- Activity log in Azure
- Azure Advisor
- the query windows of the Log Analytics workspace
-
You need to remediate active attacks to meet the technical requirements.
What should you include in the solution?
- Azure Automation runbooks
- Azure Logic Apps
- Azure Functions
- Azure Sentinel livestreams
-
HOTSPOT
You need to create an advanced hunting query to investigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
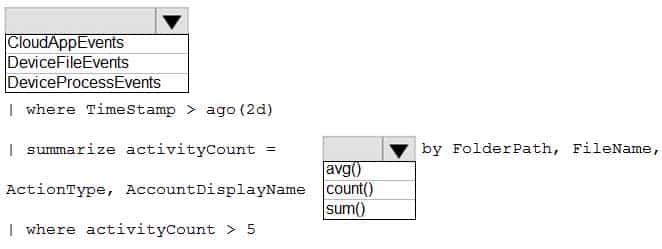
SC-200 Microsoft Security Operations Analyst Part 03 Q13 032 Question 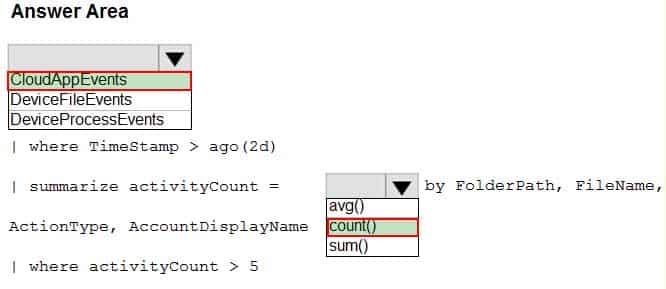
SC-200 Microsoft Security Operations Analyst Part 03 Q13 032 Answer -
HOTSPOT
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
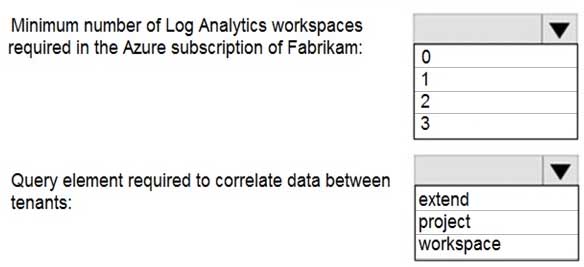
SC-200 Microsoft Security Operations Analyst Part 03 Q13 033 Question 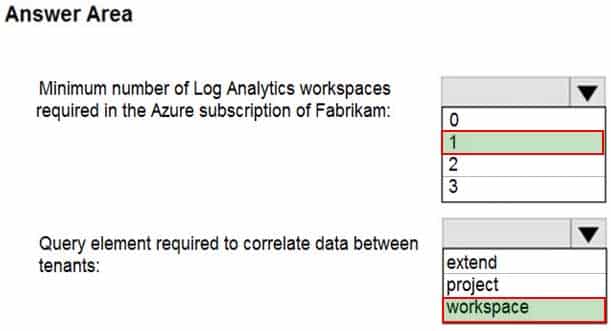
SC-200 Microsoft Security Operations Analyst Part 03 Q13 033 Answer
-
-
Case study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Litware Inc. is a renewable company.
Litware has offices in Boston and Seattle. Litware also has remote users located across the United States. To access Litware resources, including cloud resources, the remote users establish a VPN connection to either office.
Existing Environment
Identity Environment
The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com.
Microsoft 365 Environment
Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled.
Azure Environment
Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table.
SC-200 Microsoft Security Operations Analyst Part 03 Q14 035 Network Environment
Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription.
On-premises Environment
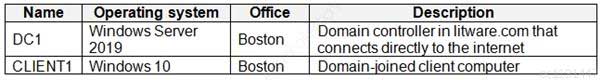
The on-premises network contains the computers shown in the following table.
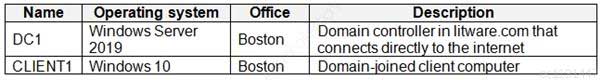
SC-200 Microsoft Security Operations Analyst Part 03 Q14 035 Current problems
Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously.
Planned Changes
Litware plans to implement the following changes:
– Create and configure Azure Sentinel in the Azure subscription.
– Validate Azure Sentinel functionality by using Azure AD test user accounts.Business Requirements
Litware identifies the following business requirements:
– The principle of least privilege must be used whenever possible.
– Costs must be minimized, as long as all other requirements are met.
– Logs collected by Log Analytics must provide a full audit trail of user activities.
– All domain controllers must be protected by using Microsoft Defender for Identity.Azure Information Protection Requirements
All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection – Data discovery dashboard.
Microsoft Defender for Endpoint requirements
All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint.
Microsoft Cloud App Security requirements
Cloud App Security must identify whether a user connection is anomalous based on tenant-level data.
Azure Defender Requirements
All servers must send logs to the same Log Analytics workspace.
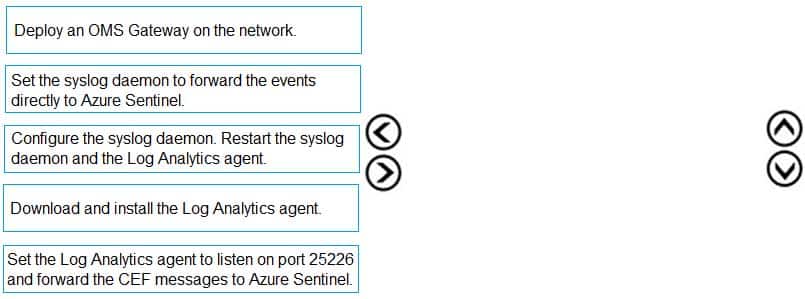
Azure Sentinel Requirements
Litware must meet the following Azure Sentinel requirements:
– Integrate Azure Sentinel and Cloud App Security.
– Ensure that a user named admin1 can configure Azure Sentinel playbooks.
– Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook.
– Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting.
– Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account.-
You need to restrict cloud apps running on CLIENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answer present part of the solution.
NOTE: Each correct selection is worth one point.
- the Onboarding settings from Device management in Microsoft Defender Security Center
- Cloud App Security anomaly detection policies
- Advanced features from Settings in Microsoft Defender Security Center
- the Cloud Discovery settings in Cloud App Security
Explanation:All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint.
-
DRAG DROP
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
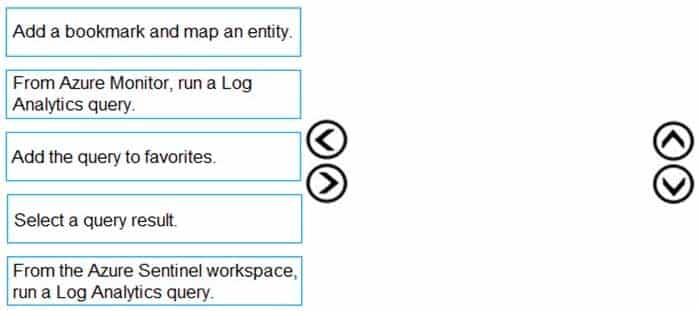
SC-200 Microsoft Security Operations Analyst Part 03 Q14 036 Question 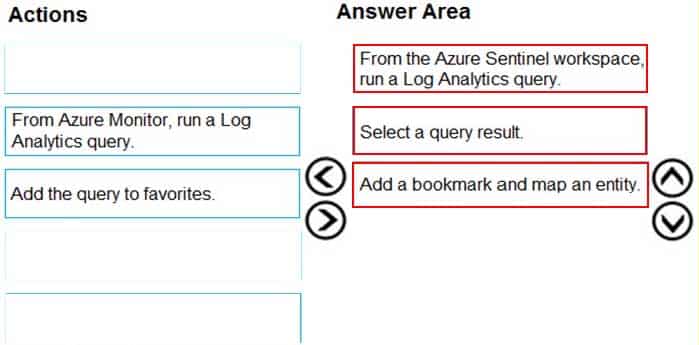
SC-200 Microsoft Security Operations Analyst Part 03 Q14 036 Answer -
HOTSPOT
You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
SC-200 Microsoft Security Operations Analyst Part 03 Q14 037 Question 
SC-200 Microsoft Security Operations Analyst Part 03 Q14 037 Answer -
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the business requirements.
Which role should you assign?
- Automation Operator
- Automation Runbook Operator
- Azure Sentinel Contributor
- Azure Sentinel Responder
Explanation:Litware must meet the following requirements:
– Ensure that a user named admin1 can configure Azure Sentinel playbooks.
– The principle of least privilege must be used whenever possible.Azure Sentinel Contributor can view data, incidents, workbooks, and other Azure Sentinel resources, manage incidents (assign, dismiss, etc.), create and edit workbooks, analytics rules, and other Azure Sentinel resources.
-
Which rule setting should you configure to meet the Azure Sentinel requirements?
- From Set rule logic, turn off suppression.
- From Analytics rule details, configure the tactics.
- From Set rule logic, map the entities.
- From Analytics rule details, configure the severity.
-
HOTSPOT
You need to create the analytics rule to meet the Azure Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
SC-200 Microsoft Security Operations Analyst Part 03 Q14 038 Question 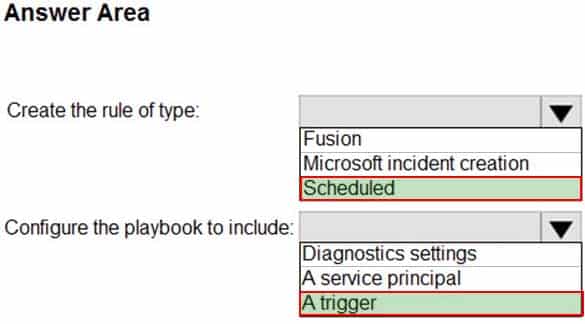
SC-200 Microsoft Security Operations Analyst Part 03 Q14 038 Answer
-
-
DRAG DROP
You plan to connect an external solution that will send Common Event Format (CEF) messages to Azure Sentinel.
You need to deploy the log forwarder.
Which three actions should you perform in sequence? To answer, move the appropriate actions form the list of actions to the answer area and arrange them in the correct order.
SC-200 Microsoft Security Operations Analyst Part 03 Q15 039 Question 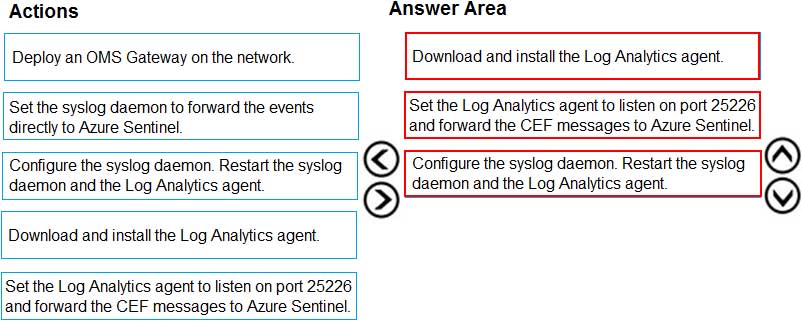
SC-200 Microsoft Security Operations Analyst Part 03 Q15 039 Answer -
HOTSPOT
From Azure Sentinel, you open the Investigation pane for a high-severity incident as shown in the following exhibit.
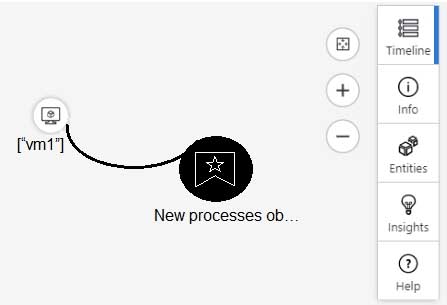
SC-200 Microsoft Security Operations Analyst Part 03 Q16 040 Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
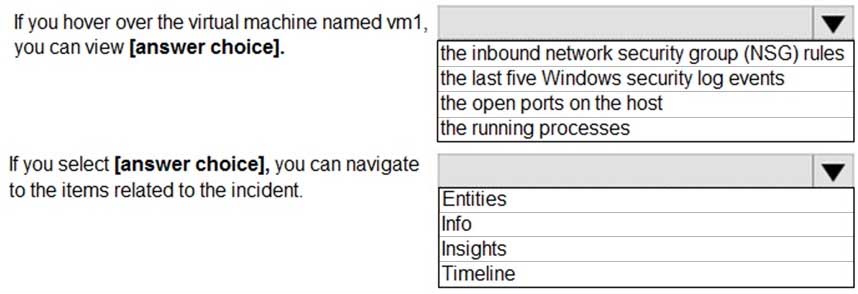
SC-200 Microsoft Security Operations Analyst Part 03 Q16 041 Question 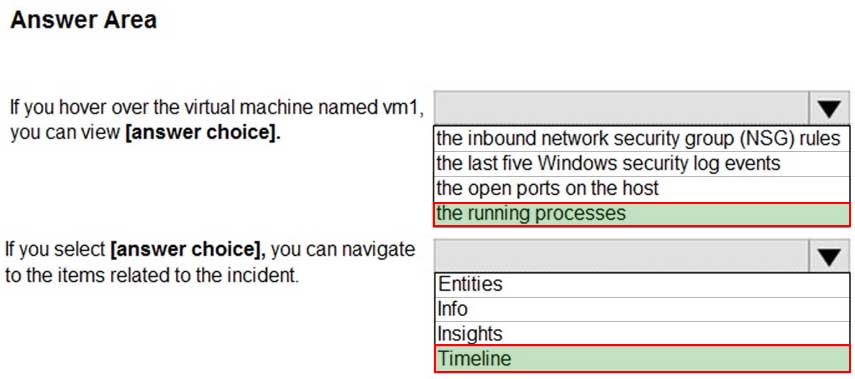
SC-200 Microsoft Security Operations Analyst Part 03 Q16 041 Answer -
DRAG DROP
You have an Azure Sentinel deployment.
You need to query for all suspicious credential access activities.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
SC-200 Microsoft Security Operations Analyst Part 03 Q17 042 Question 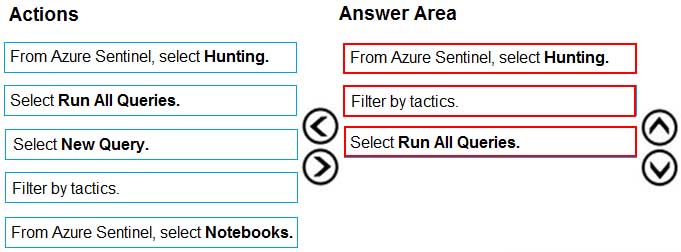
SC-200 Microsoft Security Operations Analyst Part 03 Q17 042 Answer -
You have an existing Azure logic app that is used to block Azure Active Directory (Azure AD) users. The logic app is triggered manually.
You deploy Azure Sentinel.
You need to use the existing logic app as a playbook in Azure Sentinel.
What should you do first?
- And a new scheduled query rule.
- Add a data connector to Azure Sentinel.
- Configure a custom Threat Intelligence connector in Azure Sentinel.
- Modify the trigger in the logic app.
-
Your company uses Azure Sentinel to manage alerts from more than 10,000 IoT devices.
A security manager at the company reports that tracking security threats is increasingly difficult due to the large number of incidents.
You need to recommend a solution to provide a custom visualization to simplify the investigation of threats and to infer threats by using machine learning.
What should you include in the recommendation?
- built-in queries
- livestream
- notebooks
- bookmarks
-
You have a playbook in Azure Sentinel.
When you trigger the playbook, it sends an email to a distribution group.
You need to modify the playbook to send the email to the owner of the resource instead of the distribution group.
What should you do?
- Add a parameter and modify the trigger.
- Add a custom data connector and modify the trigger.
- Add a condition and modify the action.
- Add a parameter and modify the action.