SC-200 : Microsoft Security Operations Analyst : Part 05
SC-200 : Microsoft Security Operations Analyst : Part 05
-
You are investigating an incident in Azure Sentinel that contains more than 127 alerts.
You discover eight alerts in the incident that require further investigation.
You need to escalate the alerts to another Azure Sentinel administrator.
What should you do to provide the alerts to the administrator?
- Create a Microsoft incident creation rule
- Share the incident URL
- Create a scheduled query rule
- Assign the incident
-
You are configuring Azure Sentinel.
You need to send a Microsoft Teams message to a channel whenever an incident representing a sign-in risk event is activated in Azure Sentinel.
Which two actions should you perform in Azure Sentinel? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- Enable Entity behavior analytics.
- Associate a playbook to the analytics rule that triggered the incident.
- Enable the Fusion rule.
- Add a playbook.
- Create a workbook.
-
DRAG DROP
You need to use an Azure Sentinel analytics rule to search for specific criteria in Amazon Web Services (AWS) logs and to generate incidents.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
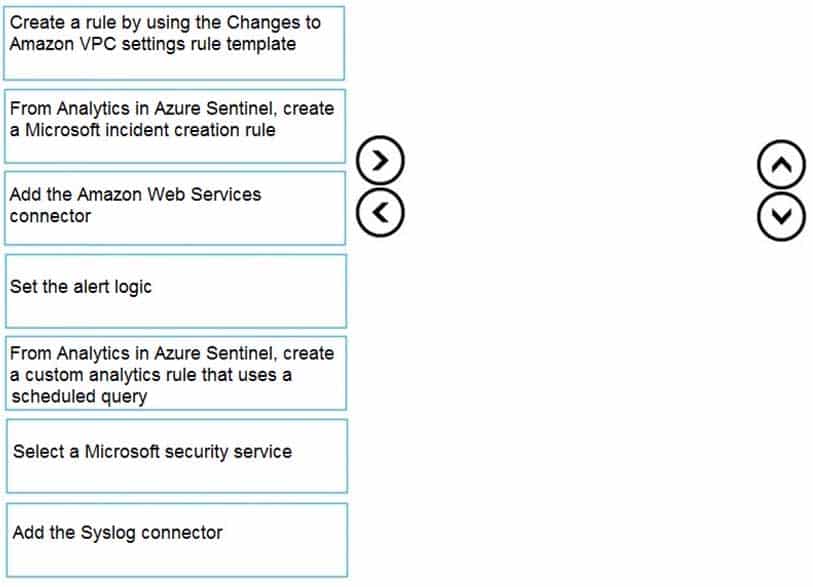
SC-200 Microsoft Security Operations Analyst Part 05 Q03 048 Question 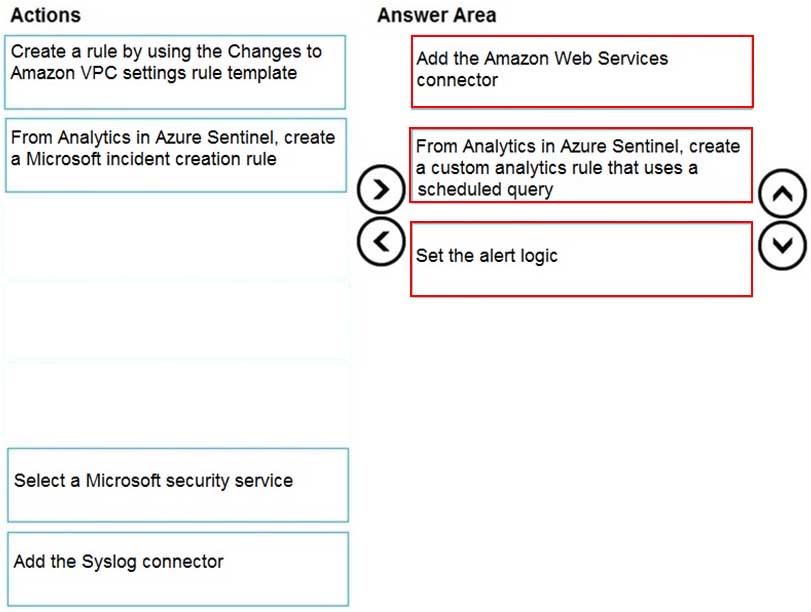
SC-200 Microsoft Security Operations Analyst Part 05 Q03 048 Answer -
You have the following environment:
– Azure Sentinel
– A Microsoft 365 subscription
– Microsoft Defender for Identity
– An Azure Active Directory (Azure AD) tenantYou configure Azure Sentinel to collect security logs from all the Active Directory member servers and domain controllers.
You deploy Microsoft Defender for Identity by using standalone sensors.
You need to ensure that you can detect when sensitive groups are modified in Active Directory.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- Configure the Advanced Audit Policy Configuration settings for the domain controllers.
- Modify the permissions of the Domain Controllers organizational unit (OU).
- Configure auditing in the Microsoft 365 compliance center.
- Configure Windows Event Forwarding on the domain controllers.
-
You use Azure Sentinel.
You need to use a built-in role to provide a security analyst with the ability to edit the queries of custom Azure Sentinel workbooks. The solution must use the principle of least privilege.
Which role should you assign to the analyst?
- Azure Sentinel Contributor
- Security Administrator
- Azure Sentinel Responder
- Logic App Contributor
Explanation:
Azure Sentinel Contributor can create and edit workbooks, analytics rules, and other Azure Sentinel resources. -
You create a hunting query in Azure Sentinel.
You need to receive a notification in the Azure portal as soon as the hunting query detects a match on the query. The solution must minimize effort.
What should you use?
- a playbook
- a notebook
- a livestream
- a bookmark
Explanation:Use livestream to run a specific query constantly, presenting results as they come in.
-
You have an Azure subscription named Sub1 and a Microsoft 365 subscription. Sub1 is linked to an Azure Active Directory (Azure AD) tenant named contoso.com.
You create an Azure Sentinel workspace named workspace1. In workspace1, you activate an Azure AD connector for contoso.com and an Office 365 connector for the Microsoft 365 subscription.
You need to use the Fusion rule to detect multi-staged attacks that include suspicious sign-ins to contoso.com followed by anomalous Microsoft Office 365 activity.
Which two actions should you perform? Each correct answer present part of the solution.
NOTE: Each correct selection is worth one point.
- Create custom rule based on the Office 365 connector templates.
- Create a Microsoft incident creation rule based on Azure Security Center.
- Create a Microsoft Cloud App Security connector.
- Create an Azure AD Identity Protection connector.
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is detected.
Solution: You create a livestream from a query.
Does this meet the goal?
- Yes
- No