220-1002 : CompTIA A+ Certification Exam: Core 2 : Part 01
220-1002 : CompTIA A+ Certification Exam: Core 2 : Part 01
-
SIMULATION
A technician has installed two new drives in one of the computers in the computer lab. Disk1 will be utilized for user and application data. Disk 2 has already been properly configured and has production data on in. The technician has been unable to format the appropriate disk from the command prompt.
The lab requires that Disk1 be a dynamic disk configured with two partitions. The first partition must be 256,000 MB in size and mapped to drive F. The second partition must be 512,000 MB in size and mapped to drive G.
The new partitions must be formatted to ensure that user’s files can be secured from other users and that the disk must be configured to account for future redundancy.
Make sure to maintain a consistent file system.
The lab requires that Disk1 be a dynamic disk configured with two partitions. The first partition must be 256,000 MB in size and mapped to drive F. The second partition must be 512,000 MB in size and mapped to drive G.
The new partitions must be formatted to ensure that user’s files can be secured from other users and that the disk must be configured to account for future redundancy.
Make sure to maintain a consistent file system.INSTRUCTIONS:
Conduct the necessary steps within the Disk Manager to accomplish these tasks.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.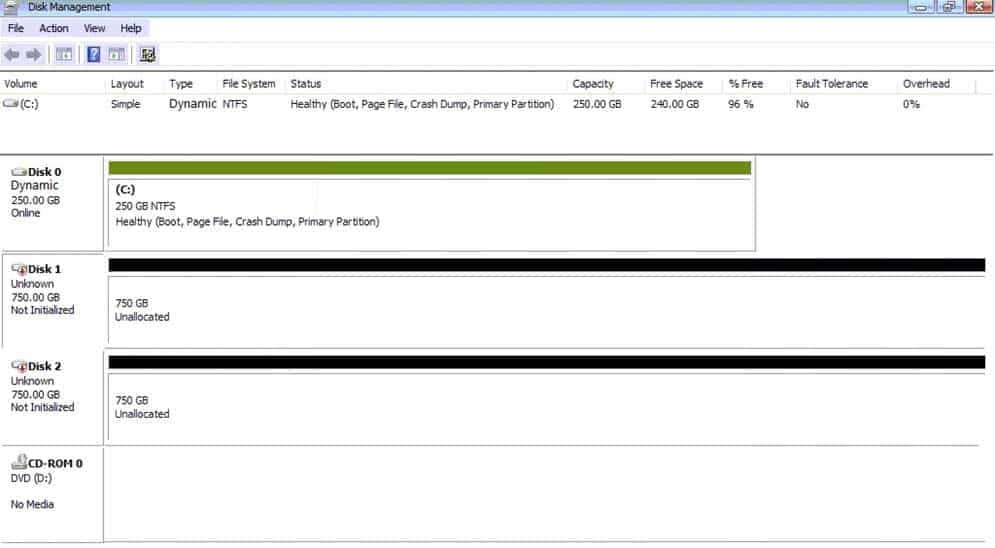
220-1002 Part 01 Q01 001 
220-1002 Part 01 Q01 002 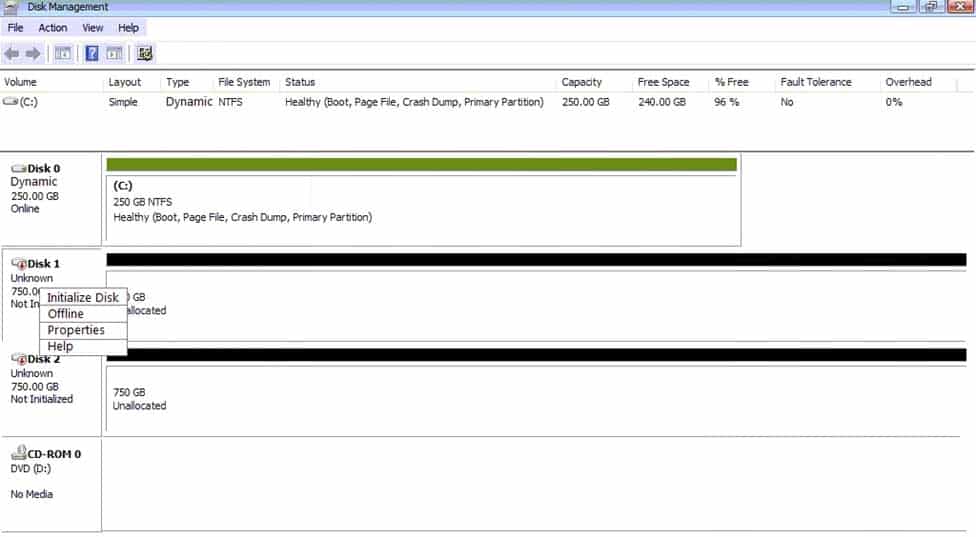
220-1002 Part 01 Q01 003 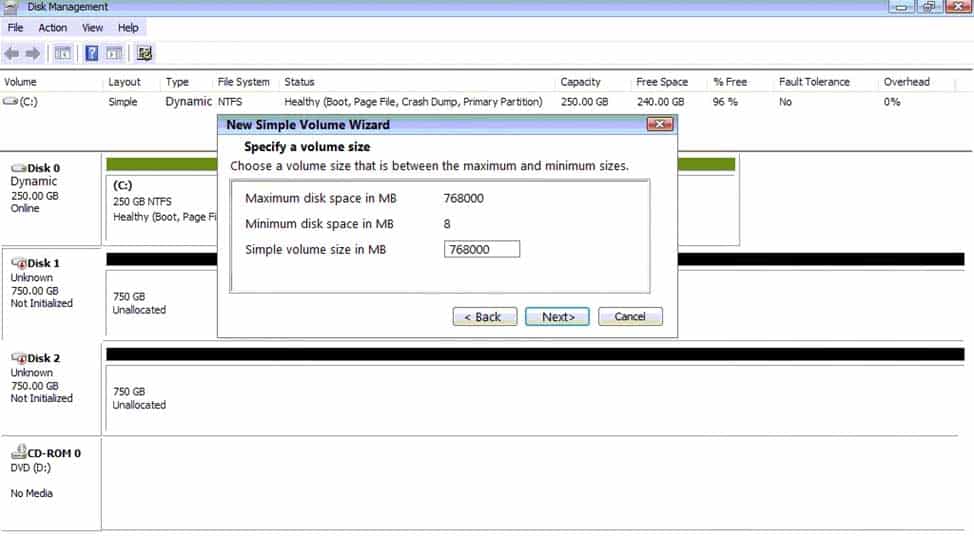
220-1002 Part 01 Q01 004 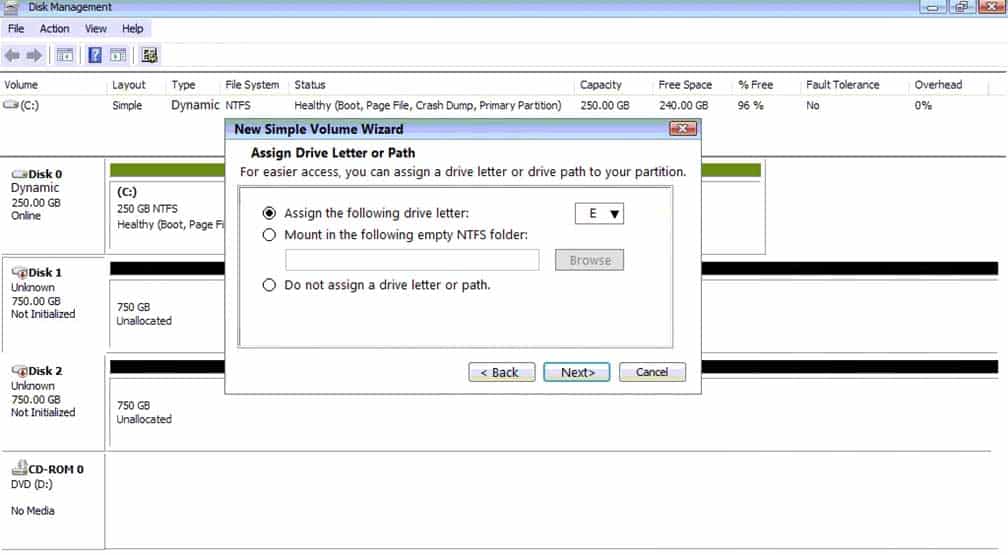
220-1002 Part 01 Q01 005 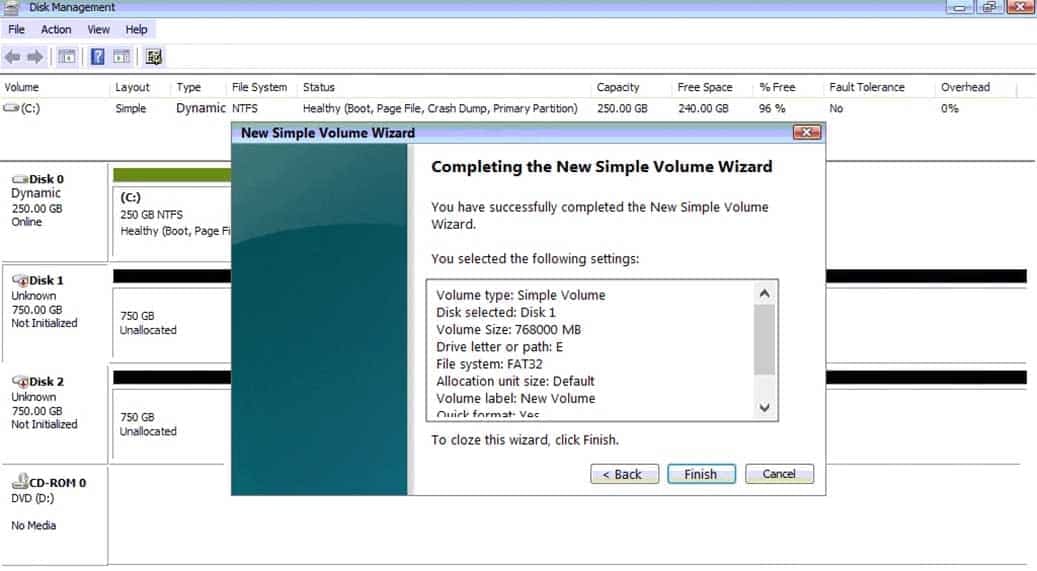
220-1002 Part 01 Q01 006 - Please review explanation for detailed answer.
Explanation:
Please review explanation for detailed answer.
Right click on disk 1, click on initialize
Choose disk and option as MBR. Hit ok.
Again, right click on disk 1 and choose convert to dynamic disk.
Now right click on disk 1 and choose new simple volume.
Specify storage as 256000 and assign a drive letter F and choose file system as NTFS and click finish.
Do the same thing for rest of space of disk 1, assigning 512000MB and using Disc GHere are the screen shots showing this process:

220-1002 Part 01 Q01 007 
220-1002 Part 01 Q01 008 
220-1002 Part 01 Q01 009 
220-1002 Part 01 Q01 010 
220-1002 Part 01 Q01 011 
220-1002 Part 01 Q01 012 
220-1002 Part 01 Q01 013 
220-1002 Part 01 Q01 014 
220-1002 Part 01 Q01 015 -
A technician arrives on site to find that two users who have the same model on Android smartphone are having the same issue with a specific application.
Whenever they attempt to launch the application, it fails and gives an error message. Which of the following should the technician do FIRST?
- Reinstall the application
- Roll back the application to the earlier version
- Clear the application cache
- Update the OS of the smartphones
-
A technician is working on a Windows 10 PC that is running slowly.
Which of the following commands should the technician use to correct this issue? (Choose two.)
-
dir
-
chkdsk -
dism -
ipconfig
-
format
-
diskpart
-
-
An administrator is setting up a Windows terminal server.
Which of the following settings should the administrator modify to increase server security? (Choose two.)
- Change the default access port
- Enforce password complexity
- Put the terminal server into the router’s DMZ
- Disable logon time restrictions
- Block all unused ports on the LAN smart switch
- Use the local client certificate for server authentication
-
A company has hired a new IT firm to manage its network switches and routers. The firm is geographically separated from the company and will need to able to securely access the devices.
Which of the following will provide the ability to access these devices?
- Telnet
- SSH
- RDP
- VNC
-
A small office’s wireless network was compromised recently by an attacker who brute forced a PIN to gain access. The attacker then modified the DNS settings on the router and spread malware to the entire network.
Which of the following configurations MOST likely allowed the attack to take place? (Choose two.)
- Guest network
- TKIP
- Default login
- Outdated firmware
- WPS
- WEP
-
A client wants a technician to create a PC naming convention that will make the client’s PCs easier to track and identify while in use.
Which of the following naming convention formats should the technician follow?
- Domain name, location, IP address
- Domain name, location, asset ID
- Asset ID, MAC address
- Location, RFID
-
Which of the following provide the BEST security for a server room? (Choose two.)
- Badge reader
- Bollard
- Biometric lock
- Cable lock
- USB token
- Privacy window shades
-
Which of the following threats uses personalized information in an attempt at obtaining information?
- Whaling
- Impersonation
- Spoofing
- Spear phishing
-
A technician receives an invalid certificate error when visiting a website with port 443 enabled. Other computers on the same LAN do not exhibit this symptom.
Which of the following needs to be adjusted on the workstation to fix the issue?
- Date and time
- UEFI boot mode
- Logon times
- User access control
-
A department in an organization set up a proxy server to manage its Internet stage. A technician is configuring the Windows workstations to use the new proxy server.
Which of the following Control Panel utilities should the technician use to configure the setting?
- Internet Options – Advanced
- Internet Options – Connections
- Internet Options – Security
- Internet Options – Content
- Internet Options – Privacy
-
Which of the following is the amount of memory a user is limited to with a 32-bit version of Windows?
- 2GB
- 4GB
- 8GB
- 16GB
-
A technician is working at a help desk firm and receives a call from a user who has experienced repeated BSODs. The technician is scheduled to take a break just after the call comes in.
Which of the following is the BEST choice for the technician to make?
- Politely ask the user to call back
- Ask another technician to take the call
- Troubleshoot the issue for the user
- Input the issue as a ticket and escalate to Tier 2
- Put the user on hold and troubleshoot after the scheduled break
-
A user’s phone contains customer’s PII. The user cannot have the phone automatically wiped because the data is very valuable.
Which of the following is the BEST method of securing the phone?
- Fingerprint lock
- Passcode lock
- Swipe lock
- PIN lock
-
Which of the following devices are MOST likely to have a grounding wire attached to them based on the manufacturer’s design? (Choose two.)
- UPS
- Server rack
- PoE phone
- Desktop printer
- Modem
- Patch panel
-
A technician has just finished installing a secondary OS on a workstation. After rebooting the computer, the technician receives the following error: No OS found. The technician confirms the boot.ini file is correct.
Which of the following is MOST likely causing this error?
- The computer has GRUB Legacy installed
- Windows Startup services are not running
- An incompatible partition is marked as active
- An unsupported version of Windows is installed
-
A technician is installing a private PC in a public workspace.
Which of the following password practices should the technician implement on the PC to secure network access?
- Remove the guest account from the administrators group
- Disable single sign-on
- Issue a default strong password for all users
- Require authentication on wake-up
-
Joe, an employee, took a company-issued Windows laptop home, but is having trouble connecting to any of the shares hosted on his home media server. Joe has verified he is connected to the Internet.
Which of the following would explain why Joe cannot access his personal shares?
- An IP conflict is present
- A corporate VPN is enabled
- A firewall exception must be set
- HomeGroup must be enabled
-
A user believes there is a virus on a laptop. The user installs additional real-time protection antivirus software but is now experiencing extremely slow performance on the laptop.
Which of the following should a technician do to resolve the issue and avoid recurrence?
- Activate real-time protection on both antivirus software programs
- Uninstall one antivirus software program and install a different one
- Run OS updates
- Enable the quarantine feature on both antivirus software programs
- Remove the user-installed antivirus software
-
A user who is running Windows XP calls a technician to upgrade the computer to a newer Windows OS. The user states the computer has only 1GB of RAM and 16GB of hard drive space with a 1.7GHz processor.
Which of the following OSs should the technician recommended to ensure the BEST performance on this computer?
- Windows 7
- Windows 8
- Windows 8.1
- Windows 10