CV1-003 : CompTIA Cloud+ : Part 01
CV1-003 : CompTIA Cloud+ : Part 01
-
SIMULATION
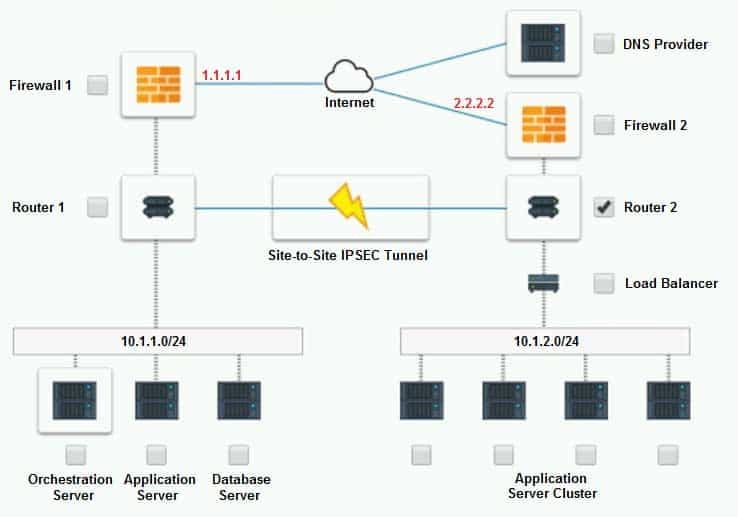
A company has decided to scale its e-commerce application from its corporate datacenter to a commercial cloud provider to meet an anticipated increase in demand during an upcoming holiday.
The majority of the application load takes place on the application server under normal conditions. For this reason, the company decides to deploy additional application servers into a commercial cloud provider using the on-premises orchestration engine that installs and configures common software and network configurations.
The remote computing environment is connected to the on-premises datacenter via a site-to-site IPSec tunnel. The external DNS provider has been configured to use weighted round-robin routing to load balance connections from the Internet.
During testing, the company discovers that only 20% of connections completed successfully.
INSTRUCTIONS
Review the network architecture and supporting documents and fulfill these requirements:
Part 1:
Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
Identify the problematic device(s).Part 2:
Identify the correct options to provide adequate configuration for hybrid cloud architecture.If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1:
Cloud Hybrid Network Diagram
CV1-003 Part 01 Q01 001 
CV1-003 Part 01 Q01 002 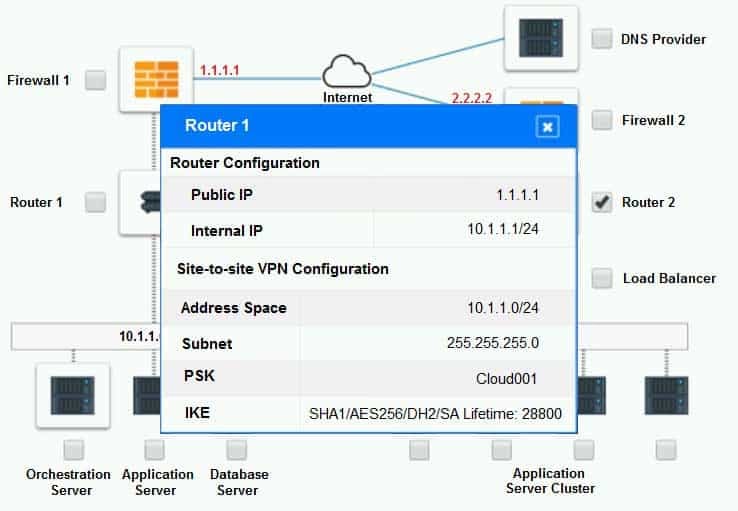
CV1-003 Part 01 Q01 003 
CV1-003 Part 01 Q01 004 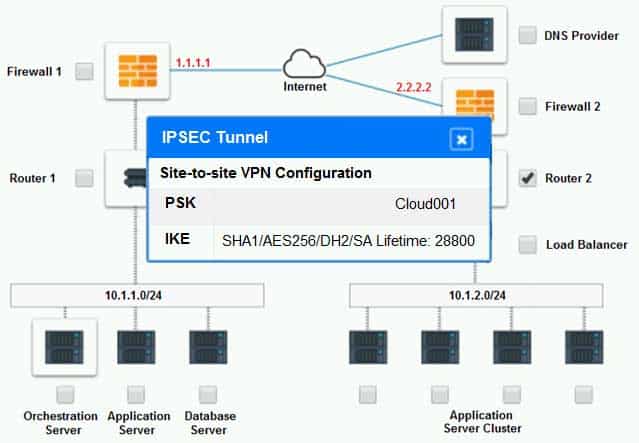
CV1-003 Part 01 Q01 005 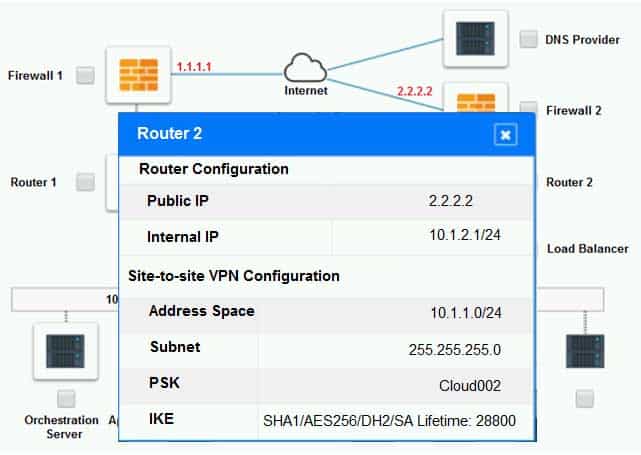
CV1-003 Part 01 Q01 006 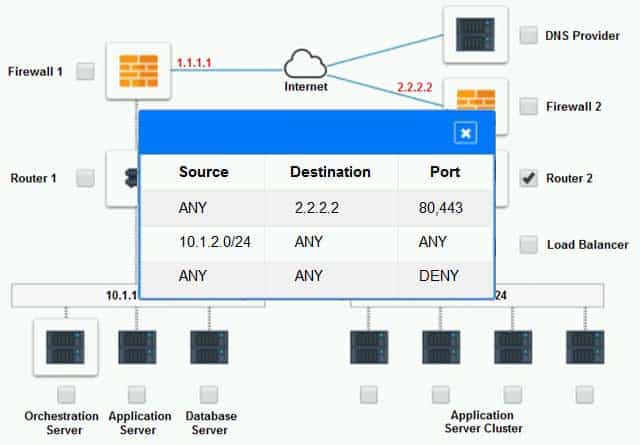
CV1-003 Part 01 Q01 007 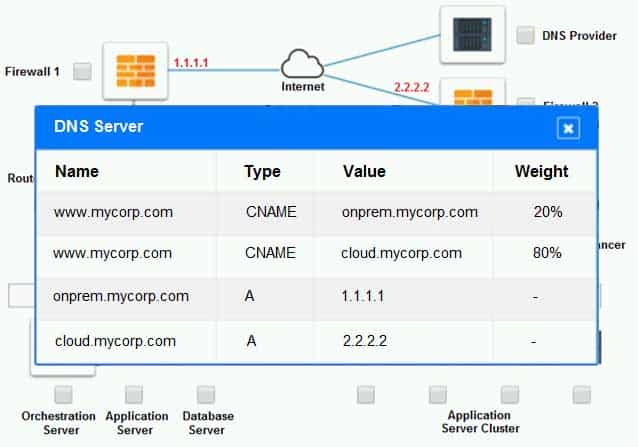
CV1-003 Part 01 Q01 008 Part 2:
Only select a maximum of TWO options from the multiple choice question
CV1-003 Part 01 Q01 009 - See explanation below.
Explanation:
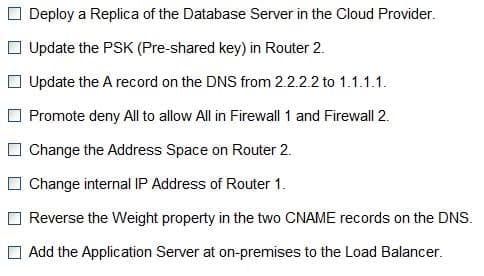
1. Change the Address Space on Router2
2. Update the PSK (Pre-shared key in Router2) -
SIMULATION
The QA team is testing a newly implemented clinical trial management (CTM) SaaS application that uses a business intelligence application for reporting. The UAT users were instructed to use HTTP and HTTPS.
Refer to the application dataflow:
1A – The end user accesses the application through a web browser to enter and view clinical data.
2A – The CTM application server reads/writes data to/from the database server.
1B – The end user accesses the application through a web browser to run reports on clinical data.
2B – The CTM application server makes a SOAP call on a non-privileged port to the BI application server.
3B – The BI application server gets the data from the database server and presents it to the CTM application server.
When UAT users try to access the application using https://ctm.app.com or http://ctm.app.com, they get a message stating: “Browser cannot display the webpage.” The QA team has raised a ticket to troubleshoot the issue.
INSTRUCTIONS
You are a cloud engineer who is tasked with reviewing the firewall rules as well as virtual network settings.
You should ensure the firewall rules are allowing only the traffic based on the dataflow.
You have already verified the external DNS resolution and NAT are working.
Verify and appropriately configure the VLAN assignments and ACLs. Drag and drop the appropriate VLANs to each tier from the VLAN Tags table. Click on each Firewall to change ACLs as needed.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

CV1-003 Part 01 Q02 010 
CV1-003 Part 01 Q02 011 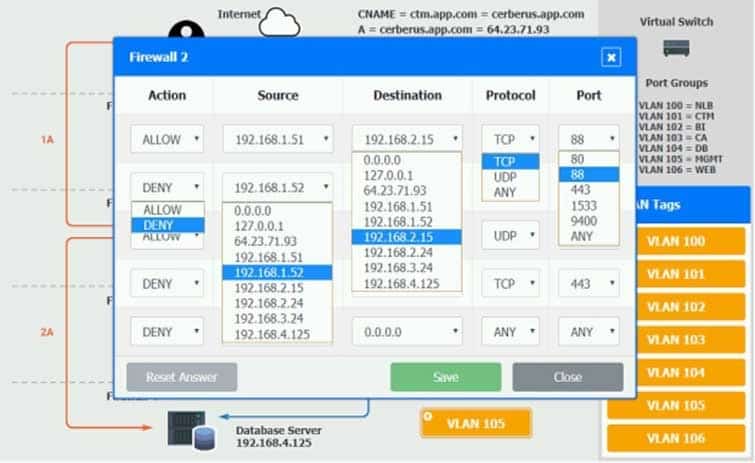
CV1-003 Part 01 Q02 012 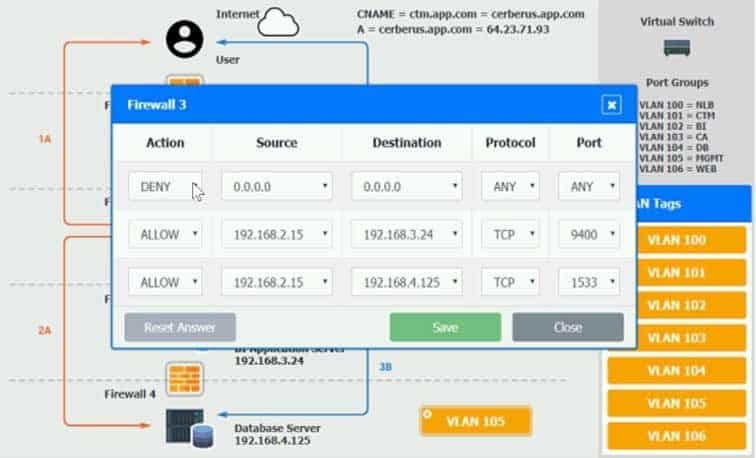
CV1-003 Part 01 Q02 013 
CV1-003 Part 01 Q02 014 - See explanation below.
Explanation:
On firewall 3, change the DENY 0.0.0.0 entry to rule 3 not rule 1.
-
A DevOps administrator is automating an existing software development workflow. The administrator wants to ensure that prior to any new code going into production, tests confirm the new code does not negatively impact existing automation activities.
Which of the following testing techniques would be BEST to use?
- Usability testing
- Regression testing
- Vulnerability testing
- Penetration testing
-
A marketing team is using a SaaS-based service to send emails to large groups of potential customers. The internally managed CRM system is configured to generate a list of target customers automatically on a weekly basis, and then use that list to send emails to each customer as part of a marketing campaign. Last week, the first email campaign sent emails successfully to 3,000 potential customers. This week, the email campaign attempted to send out 50,000 emails, but only 10,000 were sent.
Which of the following is the MOST likely reason for not sending all the emails?
- API request limit
- Incorrect billing account
- Misconfigured auto-scaling
- Bandwidth limitation
-
A VDI administrator has received reports of poor application performance.
Which of the following should the administrator troubleshoot FIRST?
- The network environment
- Container resources
- Client devices
- Server resources
-
Due to a policy change, a few of a customer’s application VMs have been migrated to synchronously replicated storage. The customer now reports that performance is lower. The systems administrator checks the resource usage and discovers CPU utilization is at 60% and available memory is at 30%.
Which of the following is the MOST likely cause?
- There is not enough vCPU assigned
- The application is not compatible with the new settings
- The new configuration is adding latency
- The memory of the VM is underallocated
-
An organization requires the following to be achieved between the finance and marketing departments:
– Allow HTTPS/HTTP.
– Disable FTP and SMB traffic.Which of the following is the MOST suitable method to meet the requirements?
- Implement an ADC solution to load balance the VLAN traffic
- Configure an ACL between the VLANs
- Implement 802.1X in these VLANs
- Configure on-demand routing between the VLANs
-
A systems administrator is building a new virtualization cluster. The cluster consists of five virtual hosts, which each have flash and spinning disks. This storage is shared among all the virtual hosts, where a virtual machine running on one host may store data on another host.
This is an example of:
- a storage area network
- a network file system
- hyperconverged storage
- thick-provisioned disks
-
A company is utilizing a private cloud solution that is hosted within its datacenter. The company wants to launch a new business application, which requires the resources below:
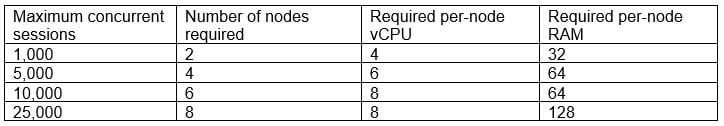
CV1-003 Part 01 Q09 015 The current private cloud has 30 vCPUs and 512GB RAM available. The company is looking for a quick solution to launch this application, with expected maximum sessions to be close to 24,000 at launch and an average of approximately 5,000 sessions.
Which of the following solutions would help the company accommodate the new workload in the SHORTEST amount of time and with the maximum financial benefits?
- Configure auto-scaling within the private cloud
- Set up cloud bursting for the additional resources
- Migrate all workloads to a public cloud provider
- Add more capacity to the private cloud
-
A systems administrator recently upgraded the processors in a web application host. Upon the next login, the administrator sees a new alert regarding the license being out of compliance.
Which of the following licensing models is the application MOST likely using?
- Per device
- Per user
- Core-based
- Volume-based
-
A systems administrator is informed that a database server containing PHI and PII is unencrypted. The environment does not support VM encryption, nor does it have a key management system. The server needs to be able to be rebooted for patching without manual intervention.
Which of the following will BEST resolve this issue?
- Ensure all database queries are encrypted
- Create an IPSec tunnel between the database server and its clients
- Enable protocol encryption between the storage and the hypervisor
- Enable volume encryption on the storage
- Enable OS encryption
-
An OS administrator is reporting slow storage throughput on a few VMs in a private IaaS cloud. Performance graphs on the host show no increase in CPU or memory. However, performance graphs on the storage show a decrease of throughput in both IOPS and MBps but not much increase in latency. There is no increase in workload, and latency is stable on the NFS storage arrays that are used by those VMs.
Which of the following should be verified NEXT?
- Application
- SAN
- VM GPU settings
- Network
-
An organization has multiple VLANs configured to segregate the network traffic. Following is the breakdown of the network segmentation:
– Production traffic (10.10.0.0/24)
– Network backup (10.20.0.0/25)
– Virtual IP network (10.20.0.128/25)The following configuration exists on the server:
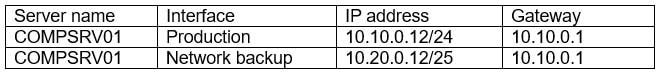
CV1-003 Part 01 Q13 016 The backup administrator observes that the weekly backup is failing for this server.
Which of the following commands should the administrator run to identify the issue?
- ROUTE PRINT
- NETSTAT -A
- IPCONFIG /ALL
- NET SM
-
A systems administrator is configuring RAID for a new server. This server will host files for users and replicate to an identical server. While redundancy is necessary, the most important need is to maximize storage.
Which of the following RAID types should the administrator choose?
- 5
- 6
- 10
- 50
-
Which of the following will mitigate the risk of users who have access to an instance modifying the system configurations?
- Implement whole-disk encryption
- Deploy the latest OS patches
- Deploy an anti-malware solution
- Implement mandatory access control
-
A systems administrator recently deployed a VDI solution in a cloud environment; however, users are now experiencing poor rendering performance when trying to display 3-D content on their virtual desktops, especially at peak times.
Which of the following actions will MOST likely solve this issue?
- Update the quest graphics drivers from the official repository
- Add more vGPU licenses to the host
- Instruct users to access virtual workstations only on the VLAN
- Select vGPU profiles with higher video RAM
-
An organization purchased new servers with GPUs for render farms. The servers have limited CPU resources.
Which of the following GPU configurations will be the MOST optimal for virtualizing this environment?
- Dedicated
- Shared
- Passthrough
- vGPU
-
A systems administrator needs to configure a set of policies to protect the data to comply with mandatory regulations.
Which of the following should the administrator implement to ensure DLP efficiently prevents the exposure of sensitive data in a cloud environment?
- Integrity
- Versioning
- Classification
- Segmentation
-
A systems administrator wants to have near-real-time information on the volume of data being exchanged between an application server and its clients on the Internet.
Which of the following should the systems administrator implement to achieve this objective?
- A stateful firewall
- DLP
- DNSSEC
- Network flows
-
A company needs to rehost its ERP system to complete a datacenter migration to the public cloud. The company has already migrated other systems and configured VPN connections.
Which of the following MOST likely needs to be analyzed before rehosting the ERP?
- Software
- Licensing
- Right-sizing
- The network