CyberOps Associate 1.02 & CA v1.0 Modules 5 – 10: Network Fundamentals Group Exam Answers Full 100% 2023 2024
These are both versions of NetAcad Cisco CA 1.02 and CyberOps Associate (Version 1.0) – Modules 5 – 10: Network Fundamentals Group Exam Full 100% in 2023 and 2024 verified by experts with explanations and hints.
-
Which statement describes the ping and tracert commands?
- Tracert shows each hop, while ping shows a destination reply only.
- Tracert uses IP addresses; ping does not.
- Both ping and tracert can show results in a graphical display.
- Ping shows whether the transmission is successful; tracert does not.
Answers Explanation & Hints: The ping utility tests end-to-end connectivity between the two hosts. However, if the message does not reach the destination, there is no way to determine where the problem is located. On the other hand, the traceroute utility ( tracert in Windows) traces the route a message takes from its source to the destination. Traceroute displays each hop along the way and the time it takes for the message to get to that network and back.
-
A large corporation has modified its network to allow users to access network resources from their personal laptops and smart phones. Which networking trend does this describe?
- cloud computing
- online collaboration
- bring your own device
- video conferencing
Answers Explanation & Hints: BYOD allows end users to use personal tools to access the corporate network. Allowing this trend can have major impacts on a network, such as security and compatibility with corporate software and devices.
-
Which networking model is being used when an author uploads one chapter document to a file server of a book publisher?
- peer-to-peer
- master-slave
- client/server
- point-to-point
Answers Explanation & Hints: In the client/server network model, a network device assumes the role of server in order to provide a particular service such as file transfer and storage. In the client/server network model, a dedicated server does not have to be used, but if one is present, the network model being used is the client/server model. In contrast, a peer-to-peer network does not have a dedicated server.
-
Match each description to its corresponding term. (Not all options are used.)
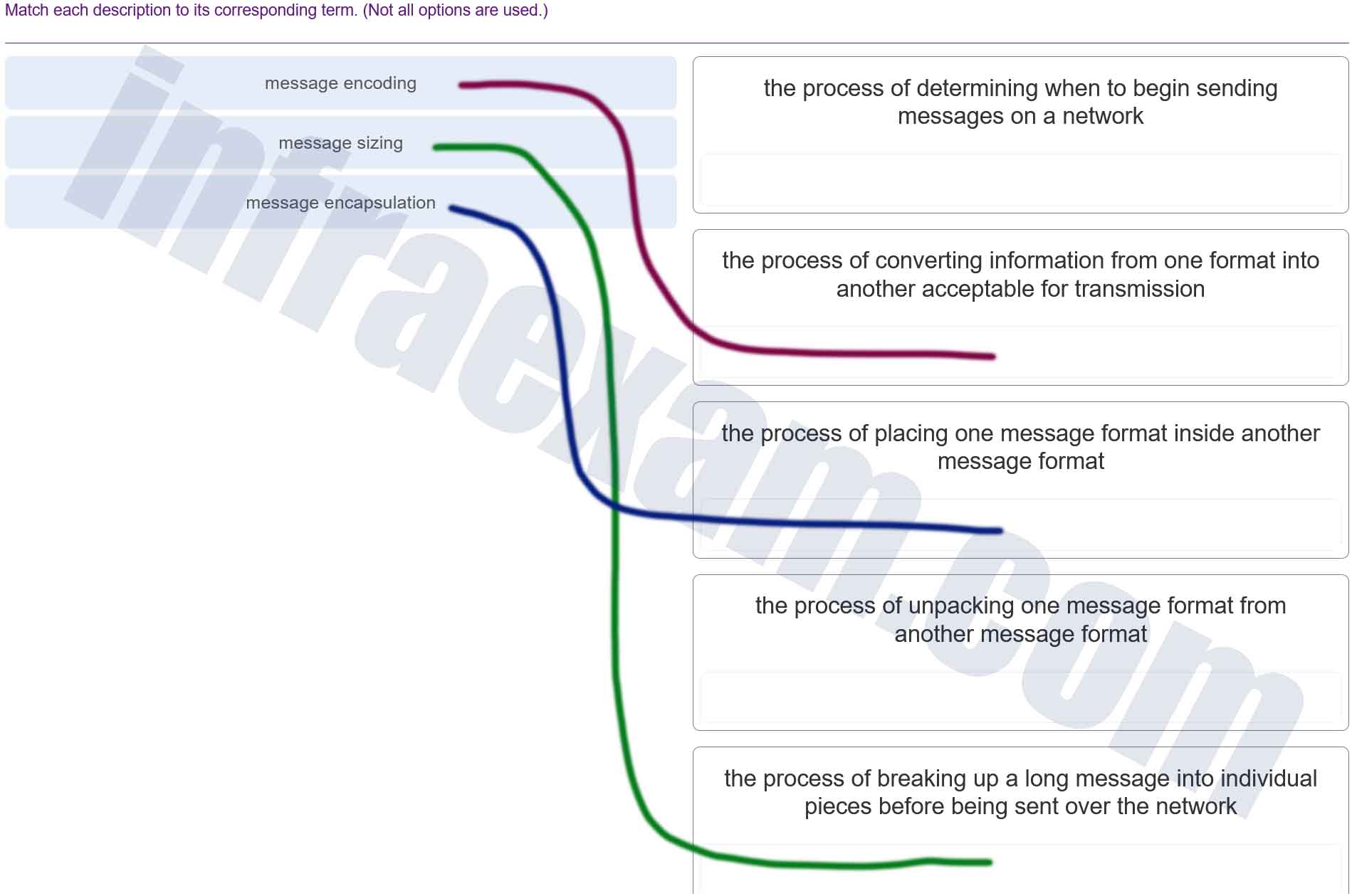
Modules 5 – 10 Network Fundamentals Group Exam Answers 001 Explanation & Hint: - Message Encoding – This is the process of converting information from one format into another acceptable for transmission. When data is sent over a network, it must be encoded into signals that can be transmitted over the network medium. This encoding can involve converting text characters to binary numbers or analog audio signals to digital signals.
- Message Encapsulation – This refers to the process of placing one message format inside another message format. In networking, encapsulation involves wrapping data with the necessary protocol information before network transmission. For instance, when you send an email, the email message is encapsulated within the Simple Mail Transfer Protocol (SMTP) envelope, which is then further encapsulated within TCP/IP packets for transmission over the internet.
- Message Sizing – Although not directly mentioned in the image, this could refer to segmenting a message into smaller pieces that are suitable for transmission over the network. Networks often have a maximum transmission unit (MTU), which is the largest size packet or frame that can be sent in a single network transaction. Larger messages need to be divided into smaller segments that do not exceed this size.
- Unpacking or Decapsulation – This is the process of extracting a message from another message format, which is the reverse of encapsulation. When a message reaches its destination, the receiving device removes the protocol information, layer by layer, to access the original data.
- Determining when to begin sending messages on a network – This description might relate to network protocols that manage the timing and order of message transmission, such as collision detection with Carrier Sense Multiple Access with Collision Detection (CSMA/CD) or synchronization processes in network protocols.
-
Which type of transmission is used to transmit a single video stream such as a web-based video conference to a select number of users?
- anycast
- broadcast
- multicast
- unicast
Answers Explanation & Hints: An anycast is used with IPv6 transmissions. A unicast is a transmission to a single host destination. A broadcast is a transmission sent to all hosts on a destination network.
-
What three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)
- ARP
- DHCP
- DNS
- FTP
- NAT
- PPP
Answers Explanation & Hints: DNS, DHCP, and FTP are all application layer protocols in the TCP/IP protocol suite. ARP and PPP are network access layer protocols, and NAT is an internet layer protocol in the TCP/IP protocol suite.
-
Which PDU is processed when a host computer is de-encapsulating a message at the transport layer of the TCP/IP model?
- bits
- frame
- packet
- segment
Answers Explanation & Hints: At the transport layer, a host computer will de-encapsulate a segment to reassemble data to an acceptable format by the application layer protocol of the TCP/IP model.
-
What is done to an IP packet before it is transmitted over the physical medium?
- It is tagged with information guaranteeing reliable delivery.
- It is segmented into smaller individual pieces.
- It is encapsulated into a TCP segment.
- It is encapsulated in a Layer 2 frame.
Answers Explanation & Hints: When messages are sent on a network, the encapsulation process works from the top of the OSI or TCP/IP model to the bottom. At each layer of the model, the upper layer information is encapsulated into the data field of the next protocol. For example, before an IP packet can be sent, it is encapsulated in a data link frame at Layer 2 so that it can be sent over the physical medium.
-
At which OSI layer is a source MAC address added to a PDU during the encapsulation process?
- data link layer
- application layer
- transport layer
- presentation layer
-
Explanation & Hint: The source MAC (Media Access Control) address is added to a PDU (Protocol Data Unit) during the encapsulation process at the Data Link layer of the OSI (Open Systems Interconnection) model.
The Data Link layer, which is the second layer in the OSI model, is responsible for node-to-node data transfer and handles the packaging of data into frames. Each frame includes the hardware addresses of the source and destination network cards, which in the context of Ethernet networks, are the MAC addresses.
-
Which two functions or operations are performed by the MAC sublayer? (Choose two.)
- It is responsible for Media Access Control.
- It performs the function of NIC driver software.
- It adds a header and trailer to form an OSI Layer 2 PDU.
- It handles communication between upper and lower layers.
- It adds control information to network protocol layer data.
Answers Explanation & Hints: The MAC sublayer is the lower of the two data link sublayers and is closest to the physical layer. The two primary functions of the MAC sublayer are to encapsulate the data from the upper layer protocols and to control access to the media.
-
What are the two sizes (minimum and expected maximum) of an Ethernet frame? (Choose two.)
- 56 bytes
- 64 bytes
- 128 bytes
- 1024 bytes
- 1518 bytes
Answers Explanation & Hints: The minimum Ethernet frame is 64 bytes. The maximum Ethernet frame is 1518 bytes. A network technician must know the minimum and maximum frame size in order to recognize runt and jumbo frames.
-
Which value, that is contained in an IPv4 header field, is decremented by each router that receives a packet?
- Differentiated Services
- Fragment Offset
- Header Length
- Time-to-Live
Answers Explanation & Hints: When a router receives a packet, the router will decrement the Time-to-Live (TTL) field by one. When the field reaches zero, the receiving router will discard the packet and will send an ICMP Time Exceeded message to the sender.
-
Which statement describes a feature of the IP protocol?
- IP encapsulation is modified based on network media.
- IP relies on Layer 2 protocols for transmission error control.
- MAC addresses are used during the IP packet encapsulation.
- IP relies on upper layer services to handle situations of missing or out-of-order packets.
Answers Explanation & Hints: IP protocol is a connection-less protocol, considered unreliable in terms of end-to-end delivery. It does not provide error control in the cases where receiving packets are out-of-order or in cases of missing packets. It relies on upper layer services, such as TCP, to resolve these issues.
-
Which field in an IPv4 packet header will typically stay the same during its transmission?
- Flag
- Time-to-Live
- Packet Length
- Destination Address
Answers Explanation & Hints: The value in the Destination Address field in an IPv4 header will stay the same during its transmission. The other options might change during its transmission.
-
What is a basic characteristic of the IP protocol?
- connectionless
- media dependent
- user data segmentation
- reliable end-to-end delivery
Answers Explanation & Hints: Internet Protocol (IP) is a network layer protocol that does not require initial exchange of control information to establish an end-to-end connection before packets are forwarded. Thus, IP is connectionless and does not provide reliable end-to-end delivery by itself. IP is media independent. User data segmentation is a service provided at the transport layer.
-
Which two parts are components of an IPv4 address? (Choose two.)
- subnet portion
- network portion
- logical portion
- host portion
- physical portion
- broadcast portion
Answers Explanation & Hints: An IPv4 address is divided into two parts: a network portion – to identify the specific network on which a host resides, and a host portion – to identify specific hosts on a network. A subnet mask is used to identify the length of each portion.
-
How many host addresses are available on the 192.168.10.128/26 network?
- 30
- 32
- 60
- 62
- 64
Answers Explanation & Hints: A /26 prefix gives 6 host bits, which provides a total of 64 addresses, because 2 6 = 64. Subtracting the network and broadcast addresses leaves 62 usable host addresses.
-
Match each IPv4 address to the appropriate address category. (Not all options are used.)
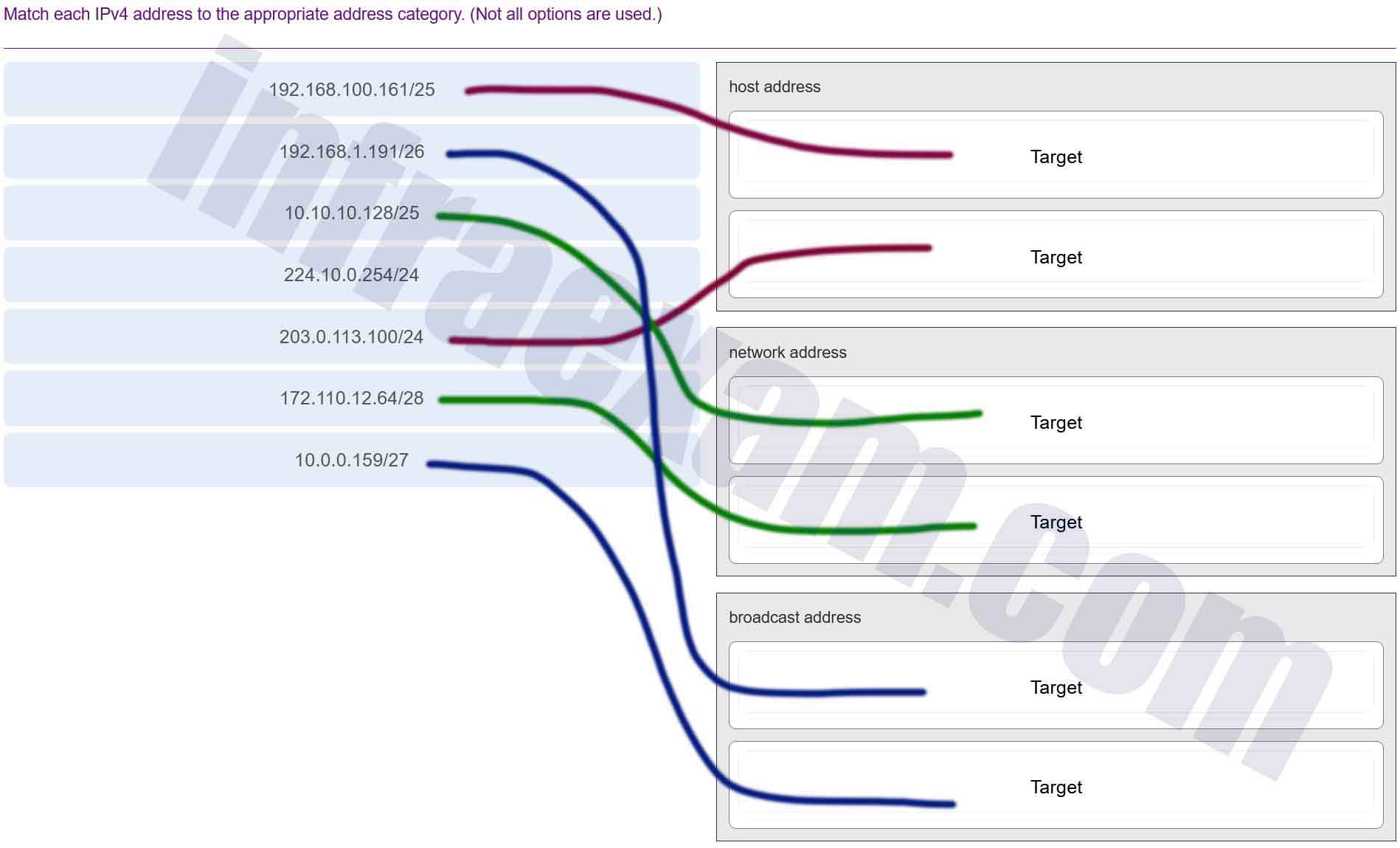
Modules 5 – 10 Network Fundamentals Group Exam Answers 002 Answers Explanation & Hints: To determine whether a given IPv4 address is a network, host, or broadcast address, first determine the address space based on the subnet mask. Convert the address and mask to binary values, then perform the ANDing function to determine the network address. To calculate the of the address space, use the number of host bits in the subnet mask as an exponent of 2. The number of valid host addresses in the space is that number minus 2. The network address will have all zeroes in the host portion, and the broadcast address will have all ones. For example, 10.0.50.10/30 yields a network IP address of 10.0.50.8 when the mask is ANDed with the given address. Because there are only 2 host bits in the mask, there are only 2 valid host addresses (4-2). 10.0.50.10 is one of the two valid host IP addresses.
-
What are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)
- 10.0.0.0/8
- 64.100.0.0/14
- 127.16.0.0/12
- 172.16.0.0/12
- 192.31.7.0/24
- 192.168.0.0/16
Answers Explanation & Hints: The private IP address blocks that are used inside companies are as follows:10.0.0.0 /8 (any address that starts with 10 in the first octet)
172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
-
An employee complains that a Windows PC cannot connect to the Internet. A network technician issues the ipconfig command on the PC and is shown an IP address of 169.254.10.3. Which two conclusions can be drawn? (Choose two.)
- The PC cannot contact a DHCP server.
- The DNS server address is misconfigured.
- The default gateway address is not configured.
- The PC is configured to obtain an IP address automatically.
- The enterprise network is misconfigured for dynamic routing.
Answers Explanation & Hints: When a Windows PC is configured to obtain an IP address automatically, the PC will try to obtain an IP address from a DHCP server. When the PC cannot contact a DHCP server, Windows will automatically assign an address belonging to the 169.254.0.0/16 range.
-
When a wireless network in a small office is being set up, which type of IP addressing is typically used on the networked devices?
- public
- private
- network
- wireless
Answers Explanation & Hints: In setting up the wireless network in a small office, it is a best practice to use private IP addressing because of the flexibility and easy management it offers.
-
Which process failed if a computer cannot access the internet and received an IP address of 169.254.142.5?
- IP
- DNS
- DHCP
- HTTP
Answers Explanation & Hints: When a Windows computer cannot communicate with an IPv4 DHCP server, the computer automatically assigns itself an IP address in the169.254.0.0/16 range. Linux and Apple computers do not automatically assign an IP address.
-
A computer can access devices on the same network but cannot access devices on other networks. What is the probable cause of this problem?
- The cable is not connected properly to the NIC.
- The computer has an invalid IP address.
- The computer has an incorrect subnet mask.
- The computer has an invalid default gateway address.
Answers Explanation & Hints: The default gateway is the address of the device a host uses to access the Internet or another network. If the default gateway is missing or incorrect, that host will not be able to communicate outside the local network. Because the host can access other hosts on the local network, the network cable and the other parts of the IP configuration are working.
-
Which two commands can be used on a Windows host to display the routing table? (Choose two.)
- netstat -s
- route print
- show ip route
- netstat -r
- tracert
Answers Explanation & Hints: On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –s command is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination.
-
A device has been assigned the IPv6 address of 2001:0db8:cafe:4500:1000:00d8:0058:00ab/64. Which is the host identifier of the device?
- 2001:0db8:cafe:4500:1000:00d8:0058:00ab
- 2001:0db8:cafe:4500
- 1000:00d8:0058:00ab
- 00ab
Answers Explanation & Hints: The address has a prefix length of /64. Thus the first 64 bits represent the network portion, whereas the last 64 bits represent the host portion of the IPv6 address.
-
What is the full decompressed form of the IPv6 address 2001:420:59:0:1::a/64?
- 2001:420:59:0:1:0:0:a
- 2001:0420:0059:0000:0001:0000:0000:000a
- 2001:4200:5900:0000:1000:0000:0000:a000
- 2001:4200:5900:0:1:0:0:a000
- 2001:0420:0059:0000:0001:000a
- 2001:0420:0059:0000:0001:0000:000a
Answers Explanation & Hints: To decompress an IPv6 address, the two rules of compression must be reversed. Any 16-bit hextet that has less than four hex characters is missing the leading zeros that were removed. An IPv6 address should have a total of 8 groups of 16-bit hextets, a (::) can be replaced with consecutive zeros that were removed.
-
Which two ICMP messages are used by both IPv4 and IPv6 protocols? (Choose two.)
- router solicitation
- route redirection
- neighbor solicitation
- protocol unreachable
- router advertisement
Answers Explanation & Hints: The ICMP messages common to both ICMPv4 and ICMPv6 include: host confirmation, destination (net, host, protocol, port) or service unreachable, time exceeded, and route redirection. Router solicitation, neighbor solicitation, and router advertisement are new protocols implemented in ICMPv6.
-
What is the purpose of ICMP messages?
- to inform routers about network topology changes
- to ensure the delivery of an IP packet
- to provide feedback of IP packet transmissions
- to monitor the process of a domain name to IP address resolution
Answers Explanation & Hints: The purpose of ICMP messages is to provide feedback about issues that are related to the processing of IP packets.
-
What mechanism is used by a router to prevent a received IPv4 packet from traveling endlessly on a network?
- It checks the value of the TTL field and if it is 0, it discards the packet and sends a Destination Unreachable message to the source host.
- It checks the value of the TTL field and if it is 100, it discards the packet and sends a Destination Unreachable message to the source host.
- It decrements the value of the TTL field by 1 and if the result is 0, it discards the packet and sends a Time Exceeded message to the source host.
- It increments the value of the TTL field by 1 and if the result is 100, it discards the packet and sends a Parameter Problem message to the source host.
Answers Explanation & Hints: To prevent an IPv4 packet to travel in the network endlessly, TCP/IP protocols use ICMPv4 protocol to provide feedback about issues. When a router receives a packet and decrements the TTL field in the IPv4 packet by 1 and if the result is zero, it discards the packet and sends a Time Exceeded message to the source host.
-
What message informs IPv6 enabled interfaces to use stateful DHCPv6 for obtaining an IPv6 address?
- the ICMPv6 Router Advertisement
- the ICMPv6 Router Solicitation
- the DHCPv6 Reply message
- the DHCPv6 Advertise message
Answers Explanation & Hints: Before an IPv6 enabled interface will use stateful DHCPv6 to obtain an IPv6 address, the interface must receive an ICMPv6 Router Advertisement with the managed configuration flag (M flag) set to 1.
-
Which method would an IPv6-enabled host using SLAAC employ to learn the address of the default gateway?
- router advertisement messages received from the link router
- neighbor solicitation messages sent to link neighbors
- neighbor advertisement messages received from link neighbors
- router solicitation messages received from the link router
Answers Explanation & Hints: When using SLAAC, a host will learn from the router advertisement that is sent by the link router the address to use as a default gateway.
-
A user issues a ping 192.168.250.103 command and receives a response that includes a code of 1 . What does this code represent?
- host unreachable
- protocol unreachable
- port unreachable
- network unreachable
Answers Explanation & Hints: When a host or gateway receives a packet that it cannot deliver, it can use an ICMP Destination Unreachable message to notify the source that the destination or service is unreachable. The message will include a code that indicates why the packet could not be delivered. These are some of the Destination Unreachable codes for ICMPv4:
0 : net unreachable
1 : host unreachable
2 : protocol unreachable
3 : port unreachable
-
A user issues a ping 2001:db8:FACE:39::10 command and receives a response that includes a code of 2 . What does this code represent?
- port unreachable
- host unreachable
- protocol unreachable
- network unreachable
Answers Explanation & Hints: When a host or gateway receives a packet that it cannot deliver, it can use an ICMP Destination Unreachable message to notify the source that the destination or service is unreachable. The message will include a code that indicates why the packet could not be delivered. These are some of the Destination Unreachable codes for ICMPv4:
0 : net unreachable
1 : host unreachable
2 : protocol unreachable
3 : port unreachable
-
What is a function of the tracert command that differs from the ping command when they are used on a workstation?
- The tracert command reaches the destination faster.
- The tracert command shows the information of routers in the path.
- The tracert command sends one ICMP message to each hop in the path.
- The tracert command is used to test the connectivity between two devices.
Answers Explanation & Hints: The tracert command sends three pings to each hop (router) in the path toward the destination and displays the domain name and IP address of hops from their responses. Because tracert uses the ping command, the travel time is the same as a standalone ping command. The primary function of a standalone ping command is to test the connectivity between two hosts.
-
Refer to the exhibit. This PC is unable to communicate with the host at 172.16.0.100. What information can be gathered from the displayed output?
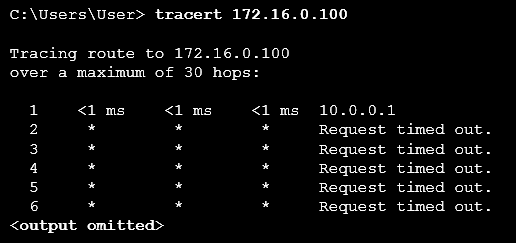
Modules 5 – 10 Network Fundamentals Group Exam Answers 03 - The target host is turned off.
- 172.16.0.100 is only a single hop away.
- This PC has the wrong subnet configured on its NIC.
- The communication fails after the default gateway.
Answers Explanation & Hints: The tracert command shows the path a packet takes through the network to the destination. In this example, only a response from the first router in the path is received, and all other responses time out. The first router is the default gateway for this host, and because a response is received from the router, it can be assumed that this host is on the same subnet as the router.
-
A user is executing a tracert to a remote device. At what point would a router, which is in the path to the destination device, stop forwarding the packet?
- when the router receives an ICMP Time Exceeded message
- when the RTT value reaches zero
- when the host responds with an ICMP Echo Reply message
- when the value in the TTL field reaches zero
- when the values of both the Echo Request and Echo Reply messages reach zero
Answers Explanation & Hints: When a router receives a traceroute packet, the value in the TTL field is decremented by 1. When the value in the field reaches zero, the receiving router will not forward the packet, and will send an ICMP Time Exceeded message back to the source.
-
A user who is unable to connect to the file server contacts the help desk. The helpdesk technician asks the user to ping the IP address of the default gateway that is configured on the workstation. What is the purpose for this ping command?
- to obtain a dynamic IP address from the server
- to request that gateway forward the connection request to the file server
- to test that the host has the capability to reach hosts on other networks
- to resolve the domain name of the file server to its IP address
Answers Explanation & Hints: The ping command is used to test connectivity between hosts. The other options describe tasks not performed by ping . Pinging the default gateway will test whether the host has the capability to reach hosts on its own network and on other networks.
-
A network administrator is testing network connectivity by issuing the ping command on a router. Which symbol will be displayed to indicate that a time expired during the wait for an ICMP echo reply message?
- !
- .
- U
- $
Answers Explanation & Hints: When the ping command is issued on a router, the most common indicators are as follows: ! – indicates receipt of an ICMP echo reply message
. – indicates a time expired while waiting for an ICMP echo reply message
U – an ICMP message of unreachability was received
-
A user sends an HTTP request to a web server on a remote network. During encapsulation for this request, what information is added to the address field of a frame to indicate the destination?
- the MAC address of the destination host
- the network domain of the destination host
- the MAC address of the default gateway
- the IP address of the default gateway
Answers Explanation & Hints: A frame is encapsulated with source and destination MAC addresses. The source device will not know the MAC address of the remote host. An ARP request will be sent by the source and will be responded to by the router. The router will respond with the MAC address of its interface, the one which is connected to the same network as the source.
-
Refer to the exhibit. PC1 attempts to connect to File_server1 and sends an ARP request to obtain a destination MAC address. Which MAC address will PC1 receive in the ARP reply?
Modules 5 – 10 Network Fundamentals Group Exam Answers 01 - the MAC address of S1
- the MAC address of the G0/0 interface on R1
- the MAC address of the G0/0 interface on R2
- the MAC address of S2
- the MAC address of File_server1
Answers Explanation & Hints: PC1 must have a MAC address to use as a destination Layer 2 address. PC1 will send an ARP request as a broadcast and R1 will send back an ARP reply with its G0/0 interface MAC address. PC1 can then forward the packet to the MAC address of the default gateway, R1.
-
Refer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC3. In this scenario, what will happen next?

Modules 5 – 10 Network Fundamentals Group Exam Answers 02 - RT1 will forward the ARP request to PC3.
- RT1 will send an ARP reply with its own Fa0/0 MAC address.
- RT1 will send an ARP reply with the PC3 MAC address.
- SW1 will send an ARP reply with its Fa0/1 MAC address.
- RT1 will send an ARP reply with its own Fa0/1 MAC address.
Answers Explanation & Hints: When a network device has to communicate with a device on another network, it broadcasts an ARP request asking for the default gateway MAC address. The default gateway (RT1) unicasts an ARP reply with the Fa0/0 MAC address.
-
What addresses are mapped by ARP?
- destination MAC address to a destination IPv4 address
- destination IPv4 address to the source MAC address
- destination IPv4 address to the destination host name
- destination MAC address to the source IPv4 address
Answers Explanation & Hints: ARP, or the Address Resolution Protocol, works by mapping a destination MAC address to a destination IPv4 address. The host knows the destination IPv4 address and uses ARP to resolve the corresponding destination MAC address.
-
What type of information is contained in an ARP table?
- switch ports associated with destination MAC addresses
- domain name to IP address mappings
- routes to reach destination networks
- IP address to MAC address mappings
Answers Explanation & Hints: ARP tables are used to store mappings of IP addresses to MAC addresses. When a network device needs to forward a packet, the device knows only the IP address. To deliver the packet on an Ethernet network, a MAC address is needed. ARP resolves the MAC address and stores it in an ARP table.
-
A cybersecurity analyst believes an attacker is spoofing the MAC address of the default gateway to perform a man-in-the-middle attack. Which command should the analyst use to view the MAC address a host is using to reach the default gateway?
- ipconfig /all
- route print
- netstat -r
- arp -a
Answers Explanation & Hints: ARP is a protocol used with IPv4 to map a MAC address to an associated specific IP address. The command arp -a will display the MAC address table on a Windows PC.
-
What is the result of an ARP poisoning attack?
- Client information is stolen.
- Client memory buffers are overwhelmed.
- Network clients experience a denial of service.
- Network clients are infected with a virus.
Answers Explanation & Hints: ARP poisoning is a technique used by an attacker to reply to an ARP request for an IPv4 address belonging to another device, such as the default gateway. The attacker, who is effectively doing an MITM attack, pretends to be the default gateway and sends an ARP reply to the transmitter of the ARP request. The receiver of the ARP reply will add the wrong MAC address to the ARP table and will send the packets to the attacker. Therefore, all traffic to the default gateway will funnel through the attacker device.
-
Match the characteristic to the protocol category. (Not all options are used.)
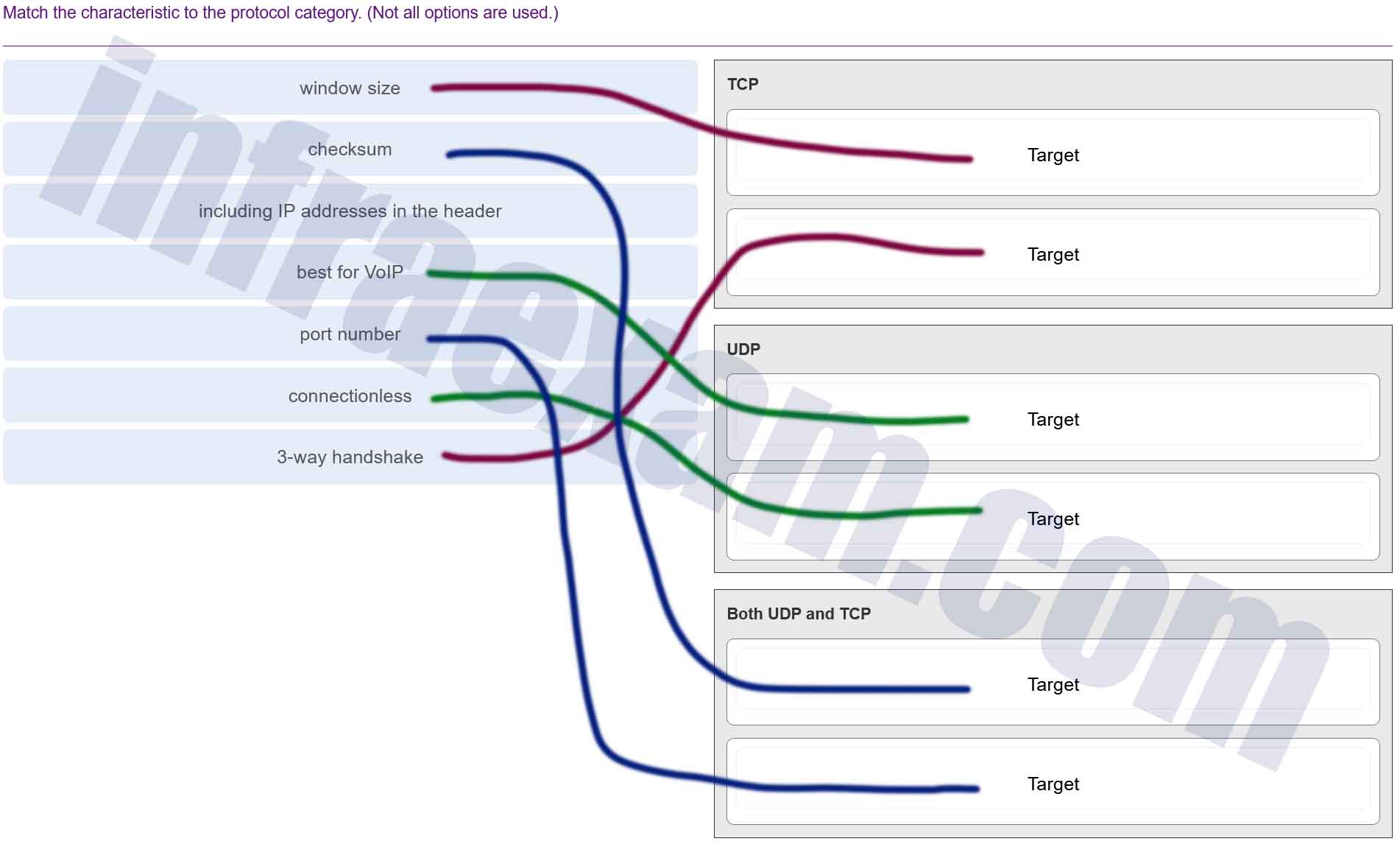
Modules 5 – 10 Network Fundamentals Group Exam Answers 003 Answers Explanation & Hints: TCP uses 3-way handshaking as part of being able to provide reliable communication and window size to provide data flow control. UDP is a connectionless protocol that is great for video conferencing. Both TCP and UDP have port numbers to distinguish between applications and application windows and a checksum field for error detection.
-
What are three responsibilities of the transport layer? (Choose three.)
- meeting the reliability requirements of applications, if any
- multiplexing multiple communication streams from many users or applications on the same network
- identifying the applications and services on the client and server that should handle transmitted data
- directing packets towards the destination network
- formatting data into a compatible form for receipt by the destination devices
- conducting error detection of the contents in frames
Answers Explanation & Hints: The transport layer has several responsibilities. Some of the primary responsibilities include the following:
Tracking the individual communication streams between applications on the source and destination hosts
Segmenting data at the source and reassembling the data at the destination
Identifying the proper application for each communication stream through the use of port numbers
Multiplexing the communications of multiple users or applications over a single network
Managing the reliability requirements of applications
-
Which two operations are provided by TCP but not by UDP? (Choose two.)
- identifying the applications
- acknowledging received data
- tracking individual conversations
- retransmitting any unacknowledged data
- reconstructing data in the order received
Answers Explanation & Hints: Numbering and tracking data segments, acknowledging received data, and retransmitting any unacknowledged data are reliability operations to ensure that all of the data arrives at the destination. UDP does not provide reliability. Both TCP and UDP identify the applications and track individual conversations. UDP does not number data segments and reconstructs data in the order that it is received.
-
A PC is downloading a large file from a server. The TCP window is 1000 bytes. The server is sending the file using 100-byte segments. How many segments will the server send before it requires an acknowledgment from the PC?
- 1 segment
- 10 segments
- 100 segments
- 1000 segments
Answers Explanation & Hints: With a window of 1000 bytes, the destination host accepts segments until all 1000 bytes of data have been received. Then the destination host sends an acknowledgment.
-
Refer to the exhibit. A network security analyst is examining captured data using Wireshark. The captured frames indicate that a host is downloading malware from a server. Which source port is used by the host to request the download?
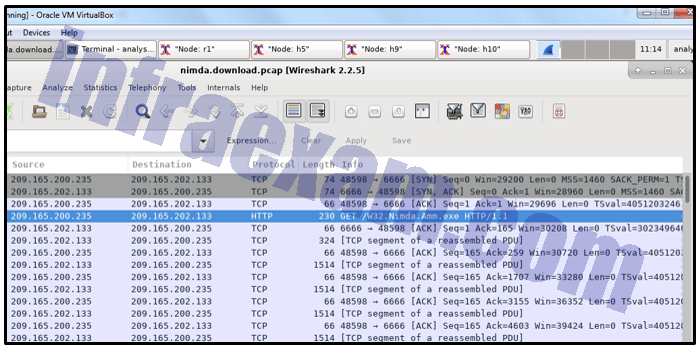
Modules 5 – 10 Network Fundamentals Group Exam Answers 06 - 66
- 1514
- 6666
- 48598
Answers Explanation & Hints: During the TCP three-way handshake process, the output shows that the host uses source port 48598 to initiate the connection and request the download.
-
Match the application protocols to the correct transport protocols.
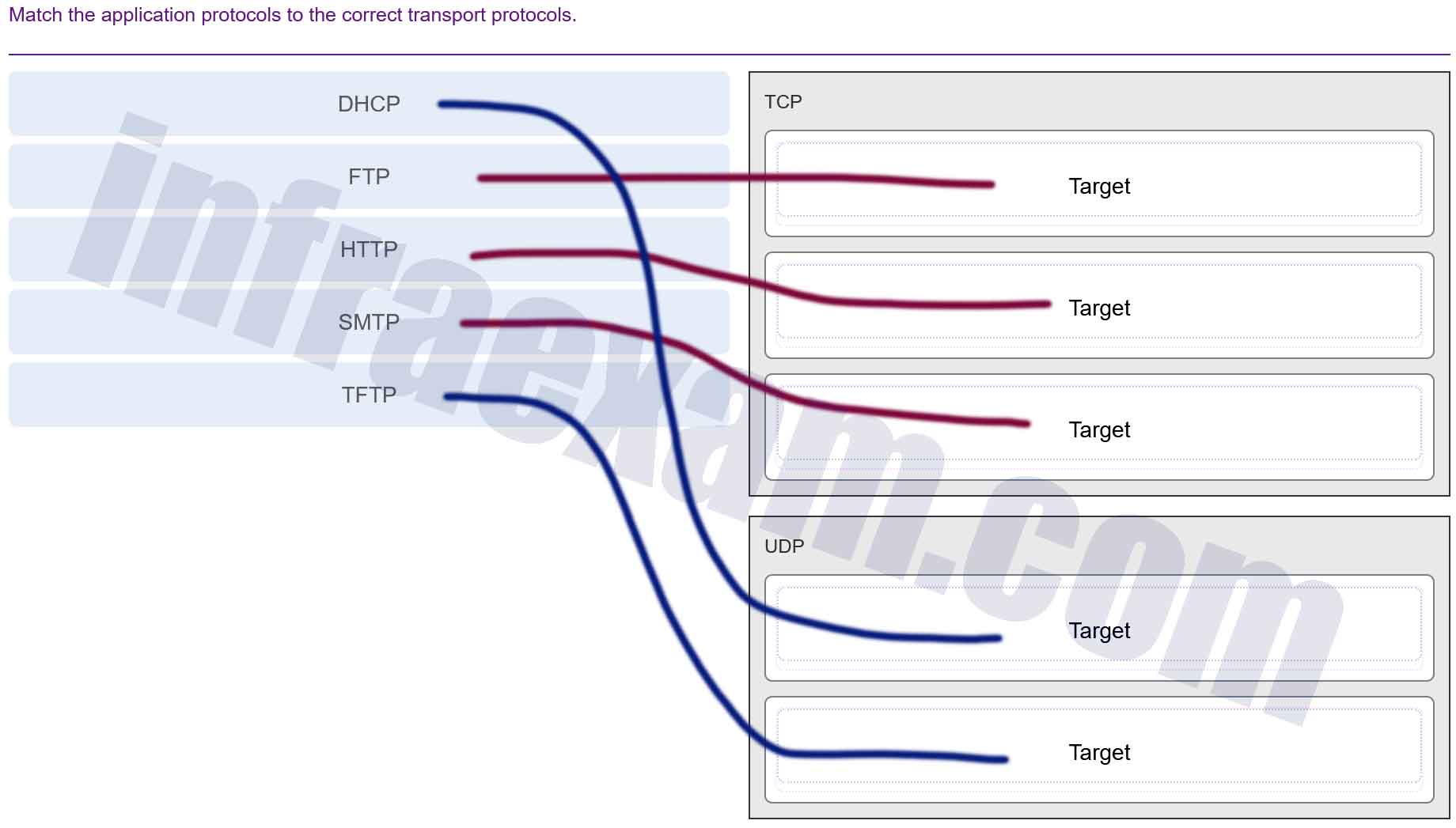
Modules 5 – 10 Network Fundamentals Group Exam Answers 004 Explanation & Hint: - DHCP (Dynamic Host Configuration Protocol) – uses UDP (User Datagram Protocol) as it is a service that needs to be fast and can tolerate some loss of data. It assigns IP addresses to devices on a network.
- FTP (File Transfer Protocol) – uses TCP (Transmission Control Protocol) as it requires reliable transmission to ensure files are transferred accurately and completely.
- HTTP (Hypertext Transfer Protocol) – uses TCP because it’s important that web pages are loaded correctly and completely.
- SMTP (Simple Mail Transfer Protocol) – also uses TCP since it is essential that emails are delivered reliably.
- TFTP (Trivial File Transfer Protocol) – uses UDP because it is designed for simplicity and speed, used in situations where high reliability isn’t as critical.
These application protocols are designed to utilize either TCP or UDP at the transport layer depending on the need for reliability and speed in the transmission of data. TCP provides a reliable connection-oriented service, whereas UDP provides an unreliable connectionless service which is faster but does not guarantee the delivery of packets.
-
How does network scanning help assess operations security?
- It can log abnormal activity.
- It can detect weak or blank passwords.
- It can detect open TCP ports on network systems.
- It can simulate attacks from malicious sources.
Answers Explanation & Hints: Network scanning can help a network administrator strengthen the security of the network and systems by identifying open TCP and UDP ports that could be targets of an attack.
-
A host PC is attempting to lease an address through DHCP. What message is sent by the server to let the client know it is able to use the provided IP information?
- DHCPDISCOVER
- DHCPOFFER
- DHCPREQUEST
- DHCPACK
- DHCPNACK
Answers Explanation & Hints: When a host uses DHCP to automatically configure an IP address, the typically sends two messages: the DHCPDISCOVER message and the DHCPREQUEST message. These two messages are usually sent as broadcasts to ensure that all DHCP servers receive them. The servers respond to these messages using DHCPOFFER, DHCPACK, and DHCPNACK messages, depending on the circumstance.
-
What action does a DHCPv4 client take if it receives more than one DHCPOFFER from multiple DHCP servers?
- It discards both offers and sends a new DHCPDISCOVER.
- It sends a DHCPREQUEST that identifies which lease offer the client is accepting.
- It sends a DHCPNAK and begins the DHCP process over again.
- It accepts both DHCPOFFER messages and sends a DHCPACK.
Answers Explanation & Hints: If there are multiple DHCP servers in a network, it is possible for a client to receive more than one DHCPOFFER. In this scenario, the client will only send one DHCPREQUEST, which includes the server from which the client is accepting the offer.
-
How is a DHCPDISCOVER transmitted on a network to reach a DHCP server?
- A DHCPDISCOVER message is sent with the IP address of the DHCP server as the destination address.
- A DHCPDISCOVER message is sent with a multicast IP address that all DHCP servers listen to as the destination address.
- A DHCPDISCOVER message is sent with the broadcast IP address as the destination address.
- A DHCPDISCOVER message is sent with the IP address of the default gateway as the destination address.
Answers Explanation & Hints: The DHCPDISCOVER message is sent by a DHCPv4 client and targets a broadcast IP along with the destination port 67. The DHCPv4 server or servers respond to the DHCPv4 clients by targeting port 68.
-
What type of information is contained in a DNS MX record?
- the FQDN of the alias used to identify a service
- the IP address for an FQDN entry
- the domain name mapped to mail exchange servers
- the IP address of an authoritative name server
Answers Explanation & Hints: MX, or mail exchange messages, are used to map a domain name to several mail exchange servers that all belong to the same domain.
-
What is a description of a DNS zone transfer?
- forwarding a request from a DNS server in a subdomain to an authoritative source
- the action taken when a DNS server sends a query on behalf of a DNS resolver
- transferring blocks of DNS data from a DNS server to another server
- finding an address match and transferring the numbered address from a DNS server to the original requesting client
Answers Explanation & Hints: When a server requires data for a zone, it will request a transfer of that data from an authoritative server for that zone. The process of transferring blocks of DNS data between servers is known as a zone transfer.
-
What network service uses the WHOIS protocol?
- HTTPS
- FTP
- DNS
- SMTP
Answers Explanation & Hints: WHOIS is a TCP-based protocol that is used to identify the owners of internet domains through the DNS system.
-
A user gets an IP address of 192.168.0.1 from the company network administrator. A friend of the user at a different company gets the same IP address on another PC. How can two PCs use the same IP address and still reach the Internet, send and receive email, and search the web?
- Both users must be using the same Internet Service Provider.
- ISPs use Network Address Translation to change a user IP address into an address that can be used on the Internet.
- ISPs use Domain Name Service to change a user IP address into a public IP address that can be used on the Internet.
- Both users must be on the same network.
Answers Explanation & Hints: As user traffic from behind an ISP firewall reaches the gateway device, Network Address Translation changes private IP addresses into a public, routable IP address. Private user addresses remain hidden from the public Internet, and thus more than one user can have the same private IP address, regardless of ISP.
-
Refer to the exhibit. From the perspective of users behind the NAT router, what type of NAT address is 209.165.201.1?
Modules 5 – 10 Network Fundamentals Group Exam Answers 04 - outside global
- outside local
- inside local
- inside global
Answers Explanation & Hints: From the perspective of users behind NAT, inside global addresses are used by external users to reach internal hosts. Inside local addresses are the addresses assigned to internal hosts. Outside global addresses are the addresses of destinations on the external network. Outside local addresses are the actual private addresses of destination hosts behind other NAT devices.
-
Refer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device has the MAC address 50:6a:03:96:71:22?

Modules 5 – 10 Network Fundamentals Group Exam Answers 05 - router DG
- router ISP
- DSN server
- web server
- PC-A
Answers Explanation & Hints: The Wireshark capture is of a DNS query from PC-A to the DNS server. Because the DNS server is on a remote network, the PC will send the query to the default gateway router, router DG, using the MAC address of the router G0/0 interface on the router.
-
Match each statement about FTP communications to the connection it describes. (Not all options are used.)
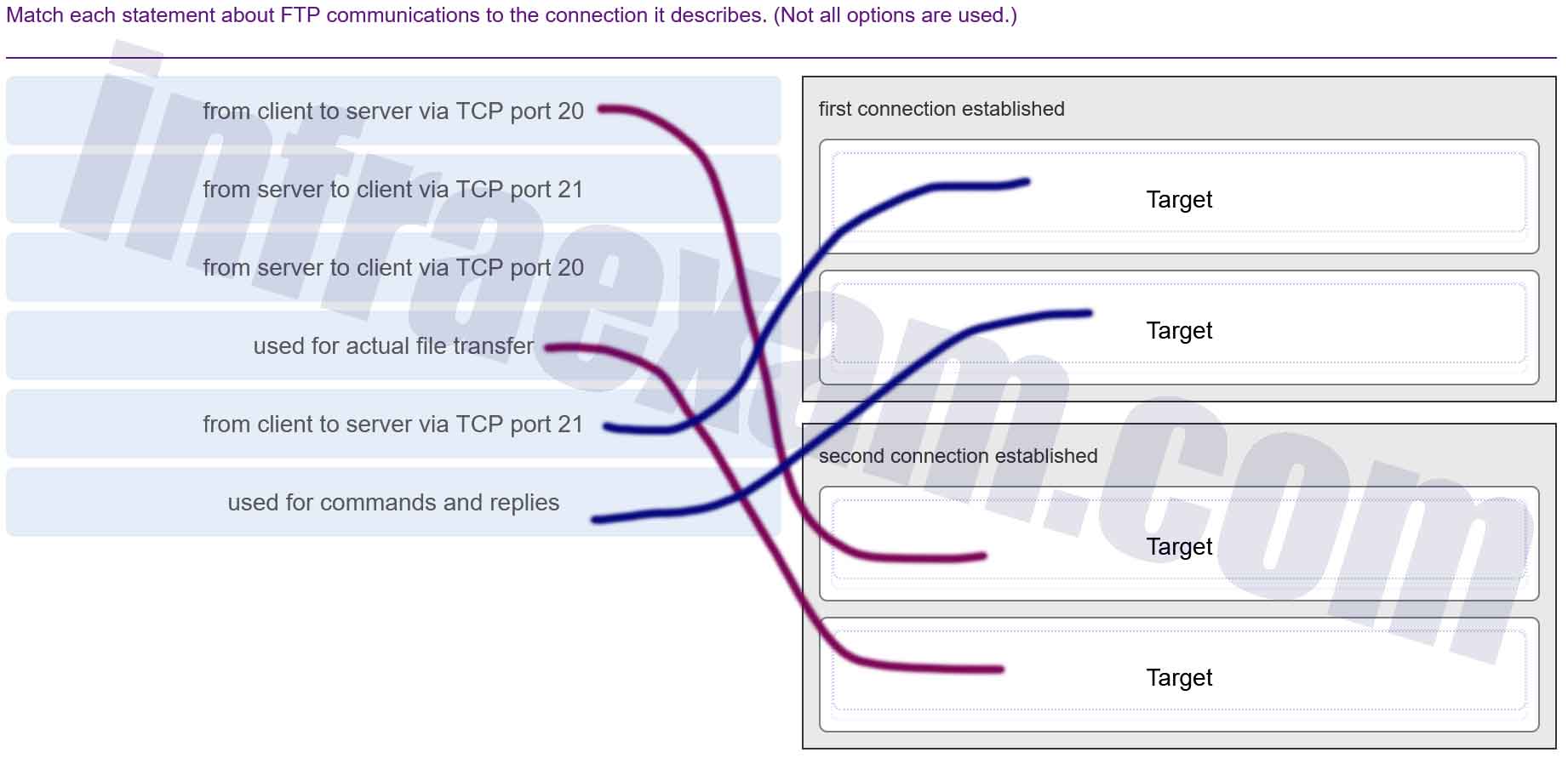
Modules 5 – 10 Network Fundamentals Group Exam Answers 005 Answers Explanation & Hints: Both connections that are required for FTP operations are established from the client to the FTP server. The client first opens a control connection via TCP port 21. The client then opens a data connection for the actual file transfer via TCP port 20.
-
Which protocol is a client/server file sharing protocol and also a request/response protocol?
- FTP
- SMB
- TCP
- UDP
Answers Explanation & Hints: The Server Message Block (SMB) is a client/server file sharing protocol that describes the structure of shared network resources such as directories, files, printers, and serial ports. SMB is also a request/response protocol.
-
A technician is configuring email on a mobile device. The user wants to be able to keep the original email on the server, organize it into folders, and synchronize the folders between the mobile device and the server. Which email protocol should the technician use?
- POP3
- IMAP
- MIME
- SMTP
Answers Explanation & Hints: The IMAP protocol allows email data to be synchronized between a client and server. Changes made in one location, such as marking an email as read, are automatically applied to the other location. POP3 is also an email protocol. However, the data is not synchronized between the client and the server. SMTP is used for sending email, and is typically used in conjunction with the POP3 protocol. MIME is an email standard that is used to define attachment types, and allows extra content like pictures and documents to be attached to email messages.
-
Match each characteristic to the appropriate email protocol. (Not all options are used.)
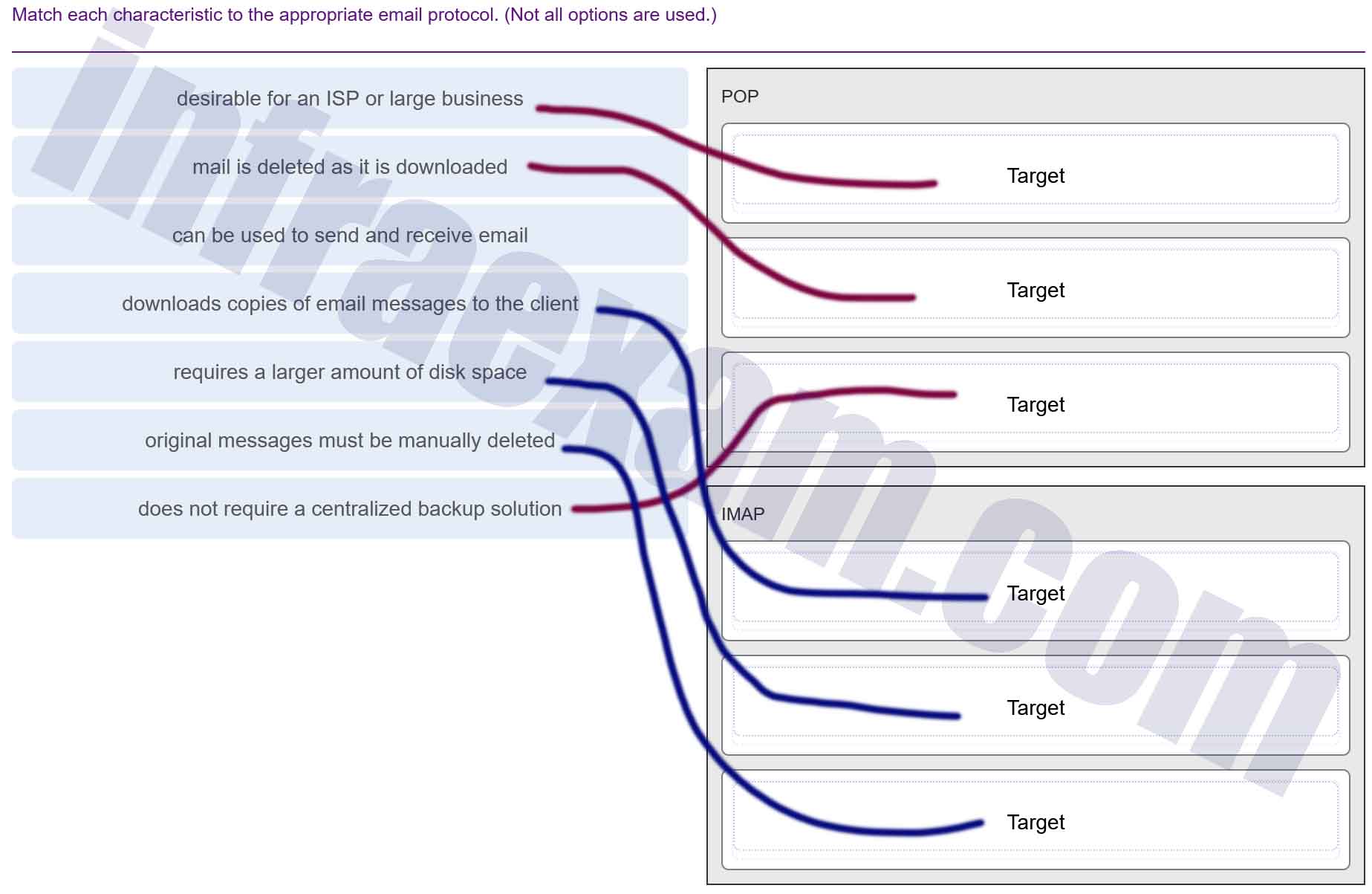
Modules 5 – 10 Network Fundamentals Group Exam Answers 006 Answers Explanation & Hints: Both POP and IMAP are used to retrieve email messages. SMTP is the default protocol used to send email. However, POP does not store messages and automatically deletes them as they are downloaded. A large business or ISP would prefer this, not a small business. It is the responsibility of the client to store and organize messages. IMAP requires a centralized backup because it stores all messages until they are manually deleted. This means that more disk space must be allocated to IMAP.
-
What is the function of the HTTP GET message?
- to request an HTML page from a web server
- to send error information from a web server to a web client
- to upload content to a web server from a web client
- to retrieve client email from an email server using TCP port 110
Answers Explanation & Hints: There are three common HTTP message types:
- GET – used by clients to request data from the web server
- POST – used by clients to upload data to a web server
- PUT – used by clients to upload data to a web server
-
Match the HTTP status code group to the type of message generated by the HTTP server.

Modules 5 – 10 Network Fundamentals Group Exam Answers 007 Explanation & Hint: - 1xx (Informational): These status codes indicate a provisional response, consisting only of the status line and optional headers, and is terminated by an empty line. For example, “100 Continue” indicates that the initial part of a request has been received and has not yet been rejected by the server.
- 2xx (Success): This class of status codes indicates that the client’s request was successfully received, understood, and accepted. For example, “200 OK” is the standard response for successful HTTP requests.
- 3xx (Redirection): This group of status codes indicates that further action needs to be taken by the user agent in order to fulfill the request. For example, “301 Moved Permanently” indicates that the requested resource has been assigned a new permanent URI.
- 4xx (Client Error): These status codes are intended for situations in which the client seems to have erred. For instance, “404 Not Found” means that the server has not found anything matching the Request-URI.
- 5xx (Server Error): The server failed to fulfill an apparently valid request, indicated by these status codes. An example would be “500 Internal Server Error,” which is a generic error message given when an unexpected condition was encountered and no more specific message is suitable.
Each range of codes serves a different function in the HTTP communication process, indicating different types of responses that a server might return.