N10-007 : CompTIA Network+ : Part 06
NS – Modules 20 – 22
-
Which of the following is a system of notation that uses base 16 rather than base 10?
- Hex
- Octal
- Binary
- CIDR
-
A network administrator would like to collect information from several networking devices using SNMP. Which of the following SNMP options should a network administrator use to ensure the data transferred is confidential?
- authpriv
- SHA
- MD5
- Authentication passphrase
-
The IT manager at a small firm is in the process of renegotiating an SLA with the organization’s ISP. As part of the agreement, the organization will agree to a dynamic bandwidth plan to provide 150Mbps of bandwidth. However, if the ISP determines that a host on the organization’s internal network produces malicious traffic, the ISP reserves the right to reduce available bandwidth to 1.5 Mbps. Which of the following policies is being agreed to in the SLA?
- Session hijacking
- Blocking
- Throttling
- Data usage limits
- Bandwidth quotas
-
A network technician has just configured NAC for connections using Cat 6 cables. However, none of the Windows clients can connect to the network.
Which of the following components should the technician check on the Windows workstations? (Choose two.)
- Start the Wired AutoConfig service in the Services console
- Enable IEEE 802.1q Authentication in Network Interface Card Properties
- Enable IEEE 802.1x Authentication in Network Interface Card Properties
- Start the Wireless AutoConfig service in the Services console
- Enable IEEE 802.3 Ethernet IPv6 in Network Interface Card Properties
-
The security manager reports that individual systems involved in policy or security violations or incidents cannot be located quickly. The security manager notices the hostnames all appear to be randomly generated characters. Which of the following would BEST assist the security manager identifying systems involved in security incidents?
- Enforce port security to require system authentication
- Implement a standardized UNC
- Label existing systems with current hostnames
- Forward the DHCP logs to the security manager every day
-
A building is equipped with light sensors that turn off the fluorescent lights when natural light is above a certain brightness. Users report experiencing network connection issues only during certain hours. The west side of the building experiences connectivity issues in the morning hours and the east side near the end of the day. At night the connectivity issues affect the entire building. Which of the following could be the cause of the connectivity issues?
- Light sensors are interfering with the network
- EMI from the lights is interfering with the network cables
- Network wiring is run perpendicular to electrical conduit
- Temperature changes are causing attenuation in copper cabling
-
A network technician configures a firewall’s ACL to allow outgoing traffic for several popular services such as email and web browsing. However, after the firewall’s deployment, users are still unable to retrieve their emails. Which of the following would BEST resolve this issue?
- Allow the firewall to accept inbound traffic to ports 25, 67, 179, and 3389
- Allow the firewall to accept inbound traffic to ports 80, 110, 143, and 443
- Set the firewall to operate in transparent mode
- Allow the firewall to accept inbound traffic to ports 21, 53, 69, and 123
-
A network security technician observes multiple attempts to scan network hosts and devices. All the attempts originate from a single host on the network. Which of the following threats is MOST likely involved?
- Smurf attack
- Rogue AP
- Compromised system
- Unintentional DoS
-
Which of the following would be the MOST efficient subnet mask for a point-to-point link?
- /28
- /29
- /31
- /32
-
An office user cannot access local network drives but has full access to the Internet. A technician troubleshoots the issue and observes the following output of the ipconfig command:
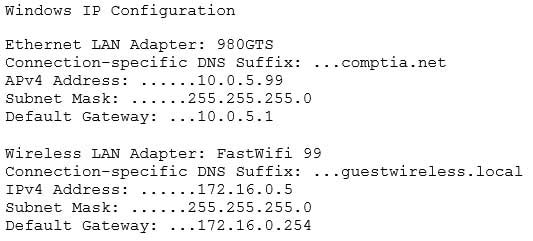
N10-007 Part 06 Q10 004 Which of the following would MOST likely allow the network drives to be accessed?
- Update the WLAN adapter driver
- Disable the WLAN adapter
- Check the wireless DHCP configuration
- Disable the LAN adapter
-
Ann, a network technician, has just installed a fiber switch in a datacenter. To run the fiber cabling, Ann plans the cable route over the top of the rack using the cable trays, down to the switch, coiling up any excess cable. As Ann configures the switch, she notices several messages in the logging buffer stating the receive signal of the SFP is too weak. Which of the following is MOST likely the cause of the errors in the logging buffer?
- Bend radius exceeded
- Fiber cable mismatch
- Fiber type mismatch
- Bad fiber switch
-
Which of the following wireless connection types utilize MIMO on non-overlapping channels? (Choose two.)
- 802.11a
- 802.11ac
- 802.11b
- 802.11g
- 802.11n
-
A network technician is creating a new subnet for 488 host machines. The technician is told to use a class B address scheme when making the subnet and is instructed to leave as much room as possible for additional subnets of the same size. Which of the following subnets would fulfill these requirements?
- 10.5.4.0/22
- 10.233.2.0/23
- 172.16.0.0/22
- 172.18.0.0/23
- 192.168.25.0/24
-
A network engineer is designing a new IDF in an old building. The engineer determines the equipment will fit in a two-post rack, and there is power available for this equipment. Which of the following would be the FIRST issue to remediate?
- Air flow and cooling
- UPS capability
- Circuit labeling
- Power redundancy
-
Which of the following DNS records needs to be configured for SMTP traffic?
- MX
- CNAME
- AAAA
- PTR
-
In which of the following ways does a DDoS attack differ from a spoofing attack?
- DDoS attacks target multiple networks
- Spoofing attacks originate from a single host
- DDoS attacks are launched from multiple hosts
- Spoofing attacks require physical presence
-
A user checks an IP address using an external website. The address is different than the one the user sees when opening a command prompt and typing in ipconfig/all. The user does not understand why the two tools show different IP addresses. This is BEST explained by the interworking of:
- network devices
- packet flow
- public/private networks
- traffic-routing protocols
-
Which of the following communication media can carry many voice, data, and video channels simultaneously over multiple frequencies?
- Broadband
- Baseband
- Analog modem
- CSMA
-
To replace a defective UPS, the network administrator must take the switch offline. The administrator wants to be able to perform maintenance UPS in the future without affecting the availability of the attached switch. Which of the following would BEST allow this to happen?
- Add a redundant power supply to the switch
- Implement stacking on the switches in the rack
- Add a second UPS into the rack
- Install a power converter for the switch
-
A forensic first responder arrives at the scene where an employee is suspected to have committed a computer-based crime. Which of the following should the first responder do FIRST?
- Document the scene
- Take pictures upon arrival
- Secure the area
- Implement chain of custody
NS – Modules 20 – 22
Subscribe
0 Comments
Newest