AZ-500 : Microsoft Azure Security Technologies : Part 02
-
DRAG DROP
You create an Azure subscription with Azure AD Premium P2.
You need to ensure that you can use Azure Active Directory (Azure AD) Privileged Identity Management (PIM) to secure Azure AD roles.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.

AZ-500 Microsoft Azure Security Technologies Part 02 Q01 045 Question 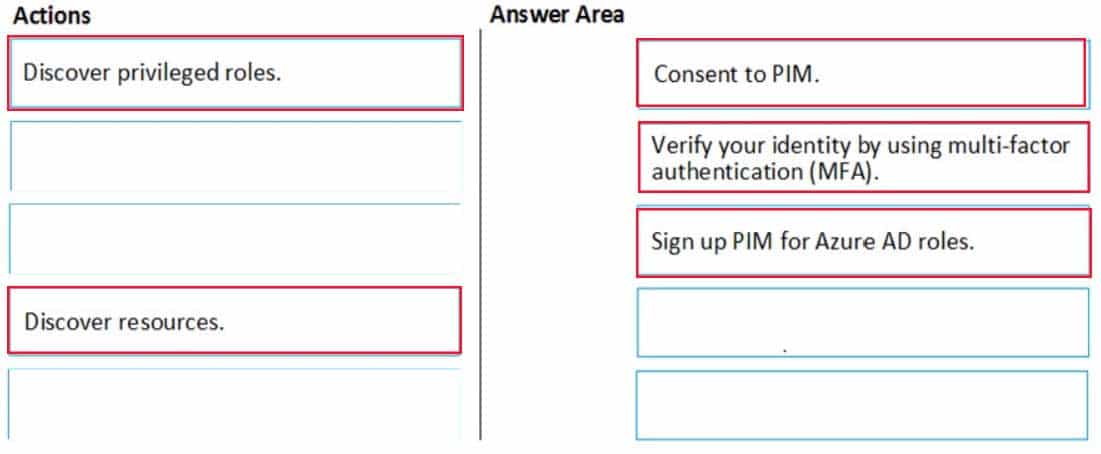
AZ-500 Microsoft Azure Security Technologies Part 02 Q01 045 Answer Explanation:Step: 2 Verify your identity by using multi-factor authentication (MFA)
Click Verify my identity to verify your identity with Azure MF
You’ll be asked to pick an account.Step 3: Sign up PIM for Azure AD roles
Once you have enabled PIM for your directory, you’ll need to sign up PIM to manage Azure AD roles. -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a hybrid configuration of Azure Active Directory (Azure AD).
You have an Azure HDInsight cluster on a virtual network.
You plan to allow users to authenticate to the cluster by using their on-premises Active Directory credentials.
You need to configure the environment to support the planned authentication.
Solution: You deploy an Azure AD Application Proxy.
Does this meet the goal?
- Yes
- No
Explanation:Instead, you connect HDInsight to your on-premises network by using Azure Virtual Networks and a VPN gateway.
Note: To allow HDInsight and resources in the joined network to communicate by name, you must perform the following actions:
– Create Azure Virtual Network.
– Create a custom DNS server in the Azure Virtual Network.
– Configure the virtual network to use the custom DNS server instead of the default Azure Recursive Resolver.
– Configure forwarding between the custom DNS server and your on-premises DNS server. -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure subscription named Sub1.
You have an Azure Storage account named sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in sa1 by using several shared access signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to sa1.
Solution: You regenerate the Azure storage account access keys.
Does this meet the goal?
- Yes
- No
Explanation:
Generating new storage account keys will invalidate all SAS’s that were based on the previous keys. -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant named contoso.com that contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q04 046 Azure AD Privileged Identity Management (PIM) is enabled for the tenant.
In PIM, the Password Administrator role has the following settings:
Maximum activation duration (hours): 2
Send email notifying admins of activation: Disable
Require incident/request ticket number during activation: Disable
Require Azure Multi-Factor Authentication for activation: Enable
Require approval to activate this role: Enable
Selected approver: Group1You assign users the Password Administrator role as shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q04 047 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 02 Q04 048 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q04 048 Answer Explanation:Box 1: Yes
Active assignments don’t require the member to perform any action to use the role. Members assigned as active have the privileges assigned to the role at all times.Box 2: Yes
While Multi-Factor Authentication is disabled for User2 and the setting Require Azure Multi-Factor Authentication for activation is enabled, User2 can request the role but will need to enable MFA to use the role.Note: Eligible assignments require the member of the role to perform an action to use the role. Actions might include performing a multi-factor authentication (MFA) check, providing a business justification, or requesting approval from designated approvers.
Box 3: No
User3 is Group1, which is a Selected Approver Group, however, self-approval is not allowed and someone else from group is required to approve the request. -
You have a hybrid configuration of Azure Active Directory (Azure AD) that has Single Sign-On (SSO) enabled. You have an Azure SQL Database instance that is configured to support Azure AD authentication.
Database developers must connect to the database instance from the domain joined device and authenticate by using their on-premises Active Directory account.
You need to ensure that developers can connect to the instance by using Microsoft SQL Server Management Studio. The solution must minimize authentication prompts.
Which authentication method should you recommend?
- Active Directory – Password
- Active Directory – Universal with MFA support
- SQL Server Authentication
- Active Directory – Integrated
Explanation:
Active Directory – Integrated
Azure Active Directory Authentication is a mechanism of connecting to Microsoft Azure SQL Database by using identities in Azure Active Directory (Azure AD). Use this method for connecting to SQL Database if you are logged in to Windows using your Azure Active Directory credentials from a federated domain. -
You plan to use Azure Resource Manager templates to perform multiple deployments of identically configured Azure virtual machines. The password for the administrator account of each deployment is stored as a secret in different Azure key vaults.
You need to identify a method to dynamically construct a resource ID that will designate the key vault containing the appropriate secret during each deployment. The name of the key vault and the name of the secret will be provided as inline parameters.
What should you use to construct the resource ID?
- a key vault access policy
- a linked template
- a parameters file
- an automation account
-
HOTSPOT
You create a new Azure subscription that is associated to a new Azure Active Directory (Azure AD) tenant.
You create one active conditional access policy named Portal Policy. Portal Policy is used to provide access to the Microsoft Azure Management cloud app.
The Conditions settings for Portal Policy are configured as shown in the Conditions exhibit. (Click the Conditions tab.)
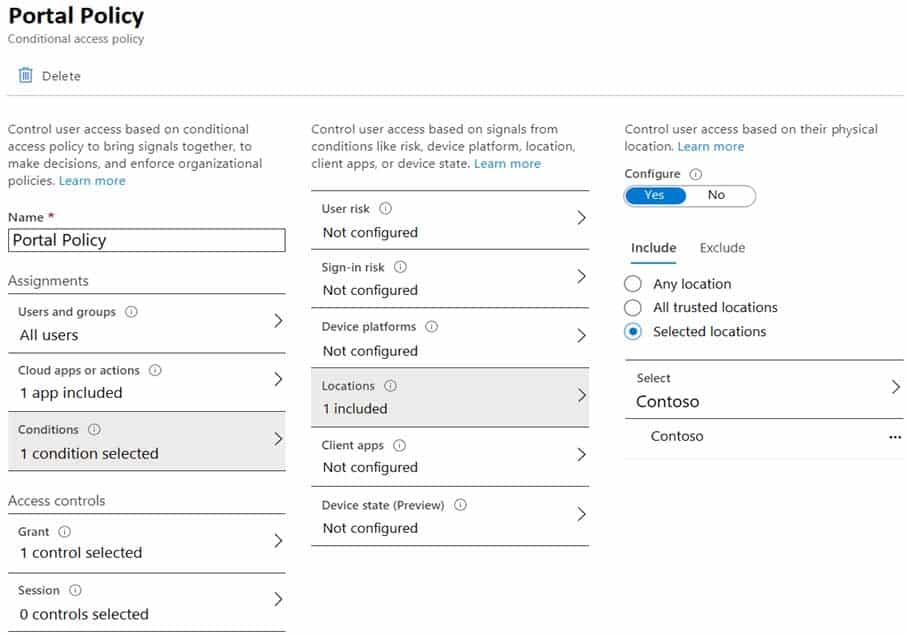
AZ-500 Microsoft Azure Security Technologies Part 02 Q07 050 The Grant settings for Portal Policy are configured as shown in the Grant exhibit. (Click the Grant tab.)
AZ-500 Microsoft Azure Security Technologies Part 02 Q07 051 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 02 Q07 052 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q07 052 Answer Explanation:Box 1: Yes
The Contoso location is included in the policy and MFA is required.Box 2: No
The policy applies to the Azure portal and Azure management endpoints. The policy does not apply to web services host in Azure.Box 3: No
The policy applies only to users in the Contoso location. The policy does not apply to users external to the Contoso location. -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q08 053 The tenant contains the named locations shown in the following table.
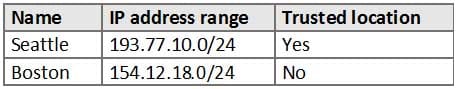
AZ-500 Microsoft Azure Security Technologies Part 02 Q08 054 You create the conditional access policies for a cloud app named App1 as shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q08 055 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
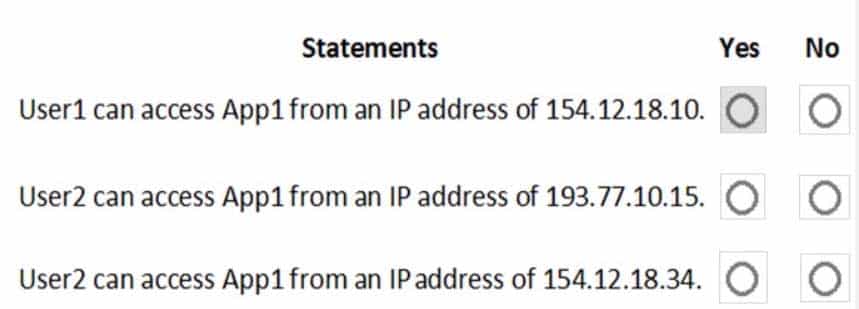
AZ-500 Microsoft Azure Security Technologies Part 02 Q08 056 Question 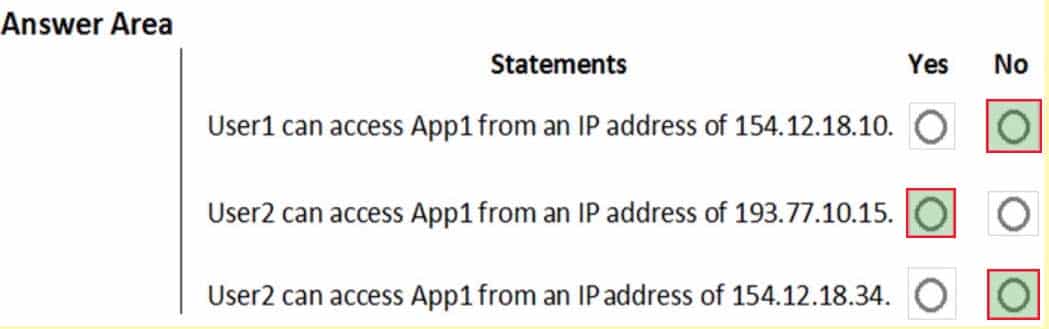
AZ-500 Microsoft Azure Security Technologies Part 02 Q08 056 Answer -
HOTSPOT
You have an Azure subscription named Sub 1 that is associated to an Azure Active Directory (Azure AD) tenant named contoso.com. The tenant contains the users shown in the following table.
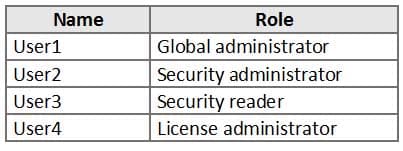
AZ-500 Microsoft Azure Security Technologies Part 02 Q09 057 Each user is assigned an Azure AD Premium P2 license.
You plan to onboard and configure Azure AD Identity Protection.
Which users can onboard Azure AD Identity Protection, remediate users, and configure policies? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 02 Q09 058 Question 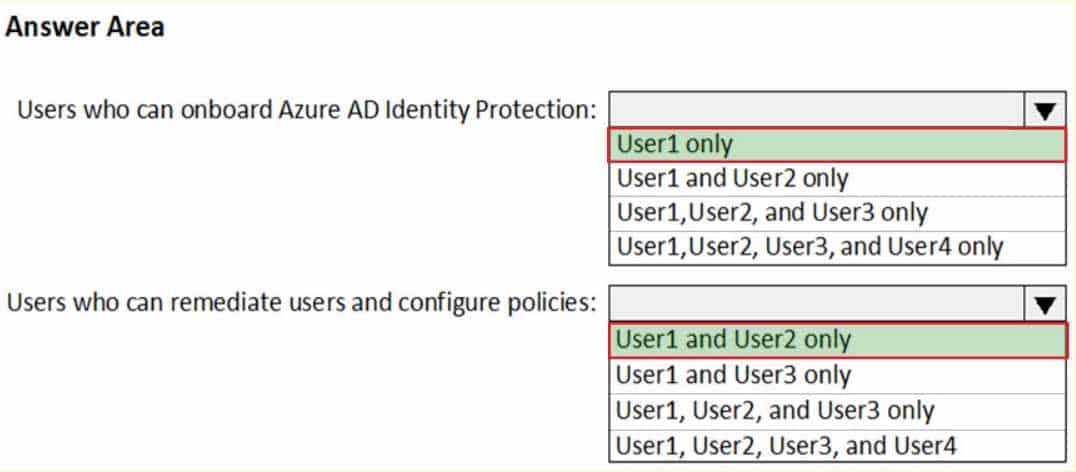
AZ-500 Microsoft Azure Security Technologies Part 02 Q09 058 Answer -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q10 059 From Azure AD Privileged Identity Management (PIM), you configure the settings for the Security Administrator role as shown in the following exhibit.
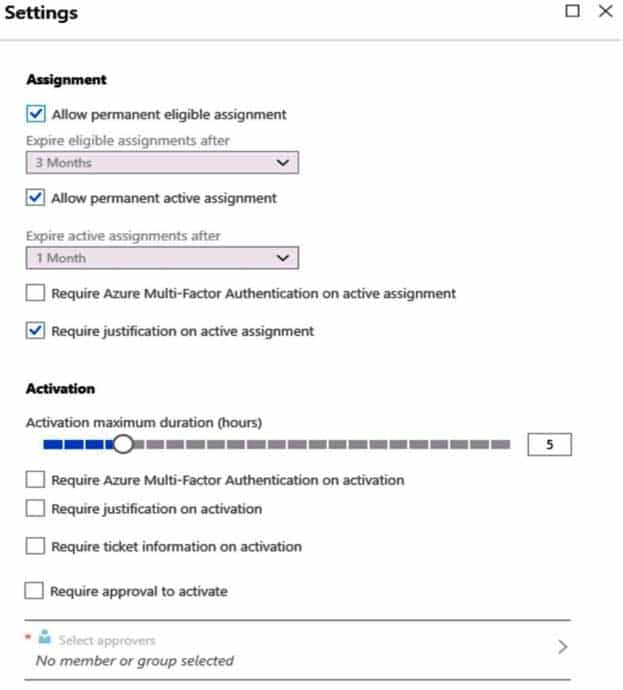
AZ-500 Microsoft Azure Security Technologies Part 02 Q10 060 From PIM, you assign the Security Administrator role to the following groups:
– Group1: Active assignment type, permanently assigned
– Group2: Eligible assignment type, permanently eligibleFor each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 02 Q10 061 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q10 061 Answer -
HOTSPOT
Your company has an Azure subscription named Subscription1 that contains the users shown in the following table.
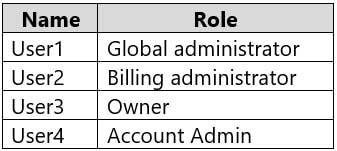
AZ-500 Microsoft Azure Security Technologies Part 02 Q11 062 The company is sold to a new owner.
The company needs to transfer ownership of Subscription1.
Which user can transfer the ownership and which tool should the user use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
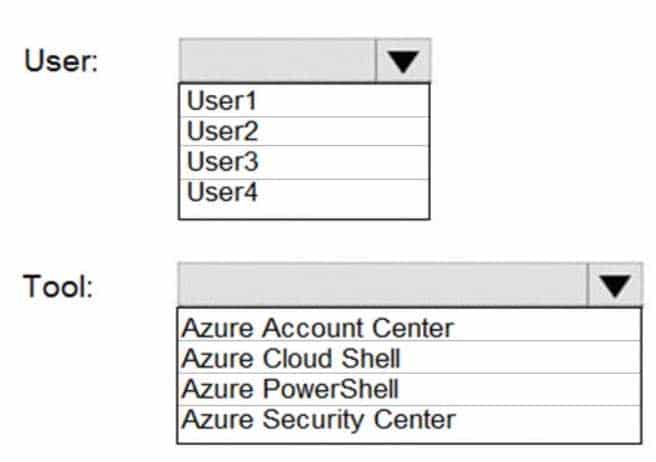
AZ-500 Microsoft Azure Security Technologies Part 02 Q11 063 Question 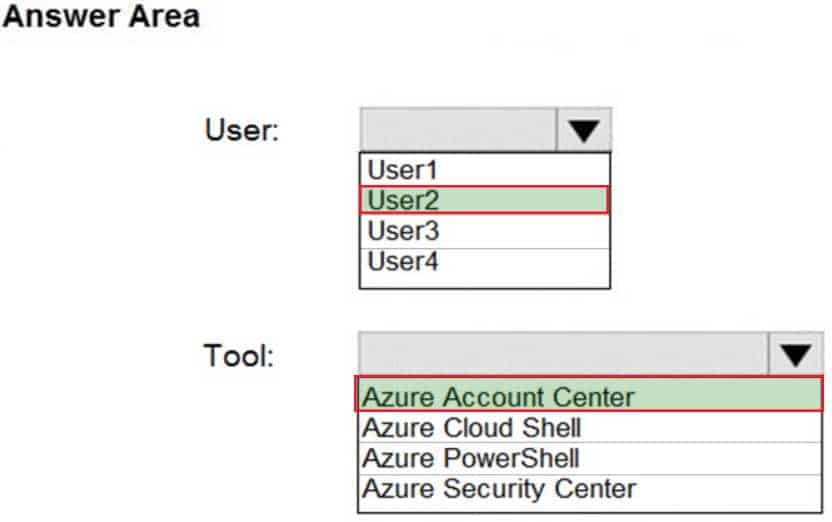
AZ-500 Microsoft Azure Security Technologies Part 02 Q11 063 Answer Explanation:Box 1; User2
Billing AdministratorSelect Transfer billing ownership for the subscription that you want to transfer.
Enter the email address of a user who’s a billing administrator of the account that will be the new owner for the subscription.Box 2: Azure Account Center
Azure Account Center can be used. -
SIMULATION
The developers at your company plan to create a web app named App10598168 and to publish the app to https://www.contoso.com.
You need to perform the following tasks:
– Ensure that App10598168 is registered to Azure Active Directory (Azure AD).
– Generate a password for App10598168.To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:Step 1: Register the Application
1. Sign in to your Azure Account through the Azure portal.
2. Select Azure Active Directory.
3. Select App registrations.
4. Select New registration.
5. Name the application App10598168 . Select a supported account type, which determines who can use the application. Under Redirect URI, select Web for the type of application you want to create. Enter the URI: https://www.contoso.com , where the access token is sent to.
AZ-500 Microsoft Azure Security Technologies Part 02 Q12 064 6. Click Register
Step 2: Create a new application secret
If you choose not to use a certificate, you can create a new application secret.
7 Select Certificates & secrets.
8. Select Client secrets -> New client secret.
9. Provide a description of the secret, and a duration. When done, select Add.After saving the client secret, the value of the client secret is displayed. Copy this value because you aren’t able to retrieve the key later. You provide the key value with the application ID to sign in as the application. Store the key value where your application can retrieve it.
-
SIMULATION
You need to create a new Azure Active Directory (Azure AD) directory named 11641655.onmicrosoft.com and a user named User1 in the new directory. The solution must ensure that User1 is enabled for Azure Multi-Factor Authentication (MFA).
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:Step 1: Create an Azure Active Directory tenant
1. Browse to the Azure portal and sign in with an account that has an Azure subscription.
2. Select the plus icon (+) and search for Azure Active Directory.
AZ-500 Microsoft Azure Security Technologies Part 02 Q13 065 3. Select Azure Active Directory in the search results.

AZ-500 Microsoft Azure Security Technologies Part 02 Q13 066 4. Select Create.
5. Provide an Organization name and an Initial domain name (10598168). Then select Create. Your directory is created.
AZ-500 Microsoft Azure Security Technologies Part 02 Q13 067 6. After directory creation is complete, select the information box to manage your new directory.
Next, you’re going to add tenant users.Step 2: Create an Azure Active Directory tenant user
7. In the Azure portal, make sure you are on the Azure Active Directory fly out.
AZ-500 Microsoft Azure Security Technologies Part 02 Q13 068 8. Under Manage, select Users.
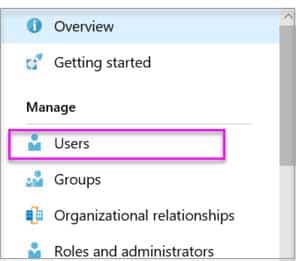
AZ-500 Microsoft Azure Security Technologies Part 02 Q13 069 9. Select All users and then select + New user.
10. Provide a Name and User name (user1) for the regular user tenant You can also show the temporary password. When you’re done, select Create.Name: user1
User name: [email protected]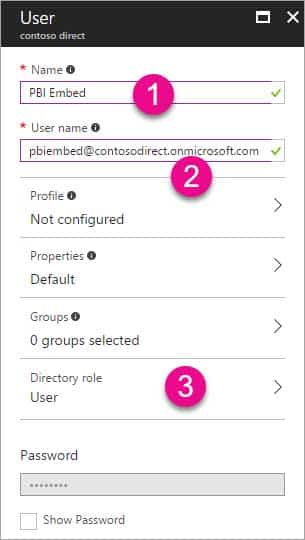
AZ-500 Microsoft Azure Security Technologies Part 02 Q13 070 -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q14 071 You create and enforce an Azure AD Identity Protection sign-in risk policy that has the following settings:
– Assignments: Include Group1, exclude Group2
– Conditions: Sign-in risk level: Medium and above
– Access Allow access, Require multi-factor authenticationYou need to identify what occurs when the users sign in to Azure AD.
What should you identify for each user? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
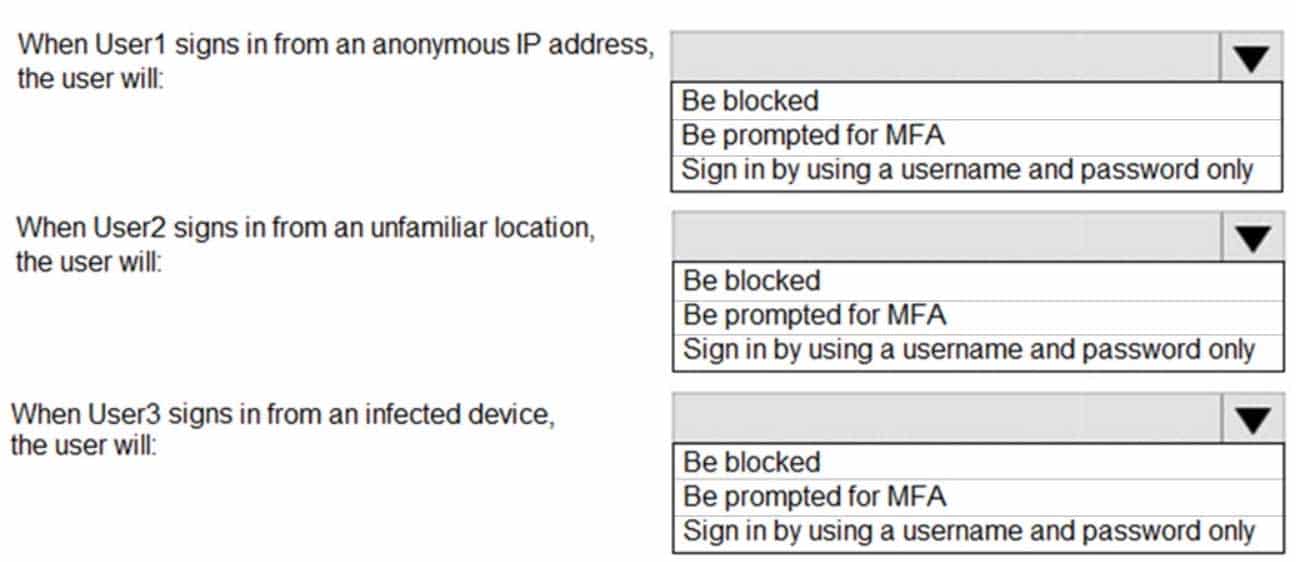
AZ-500 Microsoft Azure Security Technologies Part 02 Q14 072 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q14 072 Answer -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.
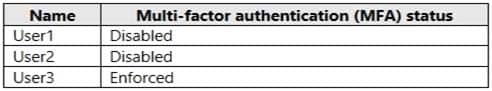
AZ-500 Microsoft Azure Security Technologies Part 02 Q15 073 In Azure AD Privileged Identity Management (PIM), the Role settings for the Contributor role are configured as shown in the exhibit. (Click the Exhibit tab.)

AZ-500 Microsoft Azure Security Technologies Part 02 Q15 074 You assign users the Contributor role on May 1, 2019 as shown in the following table.
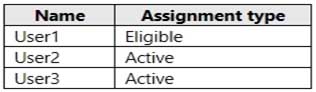
AZ-500 Microsoft Azure Security Technologies Part 02 Q15 075 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
AZ-500 Microsoft Azure Security Technologies Part 02 Q15 076 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q15 076 Answer -
HOTSPOT
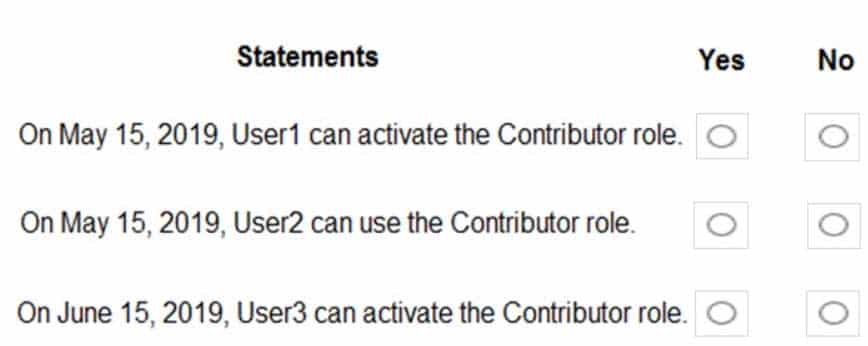
You work at a company named Contoso, Ltd. that has the offices shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q16 077 Contoso has an Azure Active Directory (Azure AD) tenant named contoso.com. All contoso.com users have Azure Multi-Factor Authentication (MFA) enabled. The tenant contains the users shown in the following table.
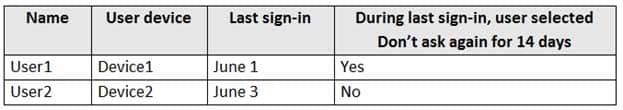
AZ-500 Microsoft Azure Security Technologies Part 02 Q16 078 The multi-factor authentication settings for contoso.com are configured as shown in the following exhibit.

AZ-500 Microsoft Azure Security Technologies Part 02 Q16 079 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 02 Q16 080 Question 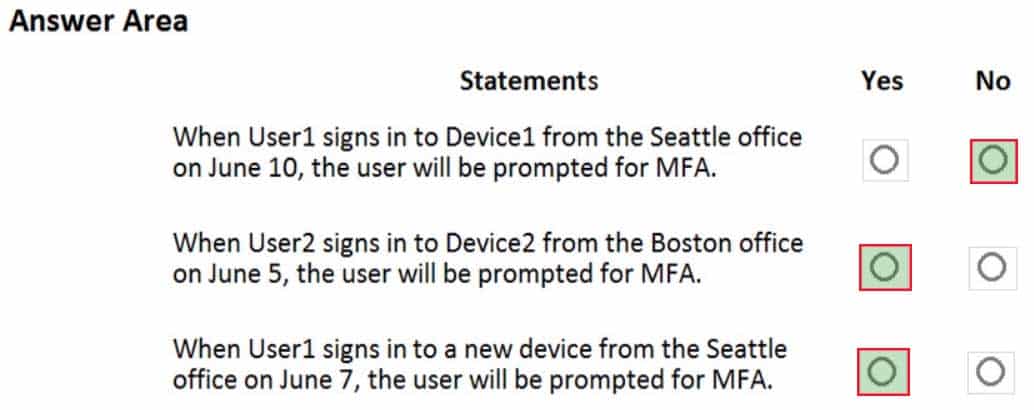
AZ-500 Microsoft Azure Security Technologies Part 02 Q16 080 Answer -
You have an Azure subscription.
You configure the subscription to use a different Azure Active Directory (Azure AD) tenant.
What are two possible effects of the change? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
- Role assignments at the subscription level are lost.
- Virtual machine managed identities are lost.
- Virtual machine disk snapshots are lost.
- Existing Azure resources are deleted.
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure subscription named Sub1.
You have an Azure Storage account named sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in sa1 by using several shared access signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to sa1.
Solution: You generate new SASs.
Does this meet the goal?
- Yes
- No
Explanation:Instead you should create a new stored access policy.
To revoke a stored access policy, you can either delete it, or rename it by changing the signed identifier. Changing the signed identifier breaks the associations between any existing signatures and the stored access policy. Deleting or renaming the stored access policy immediately affects all of the shared access signatures associated with it.
-
You have an Azure subscription that contains virtual machines.
You enable just in time (JIT) VM access to all the virtual machines.
You need to connect to a virtual machine by using Remote Desktop.
What should you do first?
- From Azure Directory (Azure AD) Privileged Identity Management (PIM), activate the Security administrator user role.
- From Azure Active Directory (Azure AD) Privileged Identity Management (PIM), activate the Owner role for the virtual machine.
- From the Azure portal, select the virtual machine, select Connect, and then select Request access.
- From the Azure portal, select the virtual machine and add the Network Watcher Agent virtual machine extension.
-
HOTSPOT
Your network contains an on-premises Active Directory domain that syncs to an Azure Active Directory (Azure AD) tenant. The tenant contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q20 081 The tenant contains the groups shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 02 Q20 082 You configure a multi-factor authentication (MFA) registration policy that has the following settings:
Assignments:
– Include: Group1
– Exclude: Group2
Controls: Require Azure MFA registration
Enforce Policy: OnFor each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
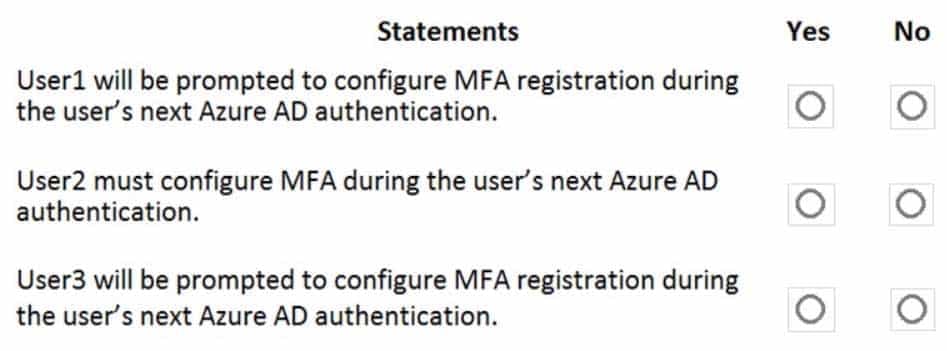
AZ-500 Microsoft Azure Security Technologies Part 02 Q20 083 Question 
AZ-500 Microsoft Azure Security Technologies Part 02 Q20 083 Answer