AZ-500 : Microsoft Azure Security Technologies : Part 04
-
HOTSPOT
You have an Azure subscription that contains the custom roles shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q01 111 In the Azure portal, you plan to create new custom roles by cloning existing roles. The new roles will be configured as shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q01 112 Which roles can you clone to create each new role? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 04 Q01 113 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q01 113 Answer -
HOTSPOT
You have an Azure subscription that contains the Azure Active Directory (Azure AD) resources shown in the following table.
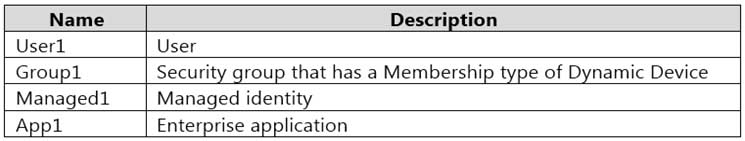
AZ-500 Microsoft Azure Security Technologies Part 04 Q02 114 You create the groups shown in the following table.
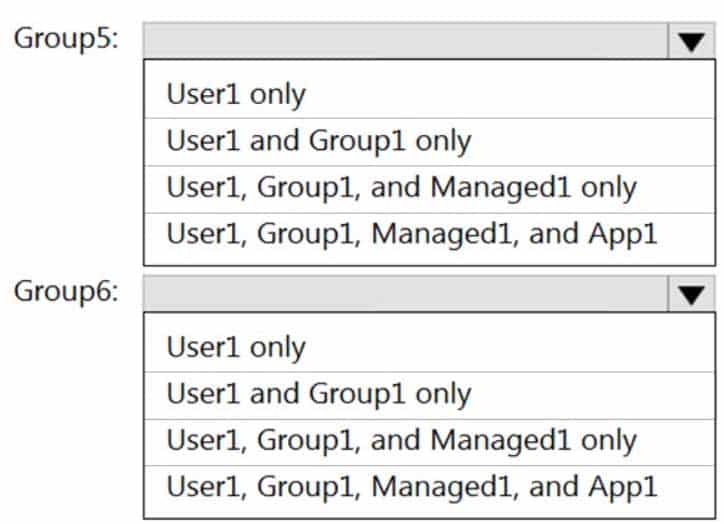
AZ-500 Microsoft Azure Security Technologies Part 04 Q02 115 Which resources can you add to Group5 and Group6? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
AZ-500 Microsoft Azure Security Technologies Part 04 Q02 116 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q02 116 Answer -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant named contoso.com that contains three security groups named Group1, Group2, and Group3 and the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q03 117 Group3 is a member of Group2.
In contoso.com, you register an enterprise application named App1 that has the following settings:
– Owners: User1
– Users and groups: Group2You configure the properties of App1 as shown in the following exhibit.

AZ-500 Microsoft Azure Security Technologies Part 04 Q03 118 For each of the following statements, select Yes if the statement is true. Otherwise, select no.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 04 Q03 119 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q03 119 Answer -
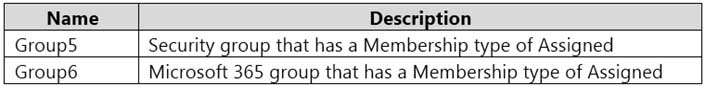
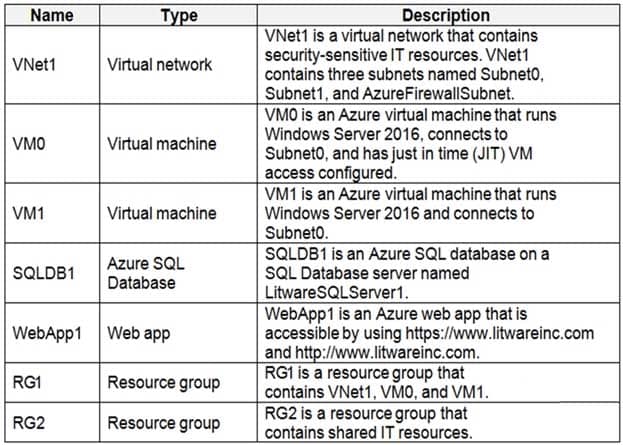
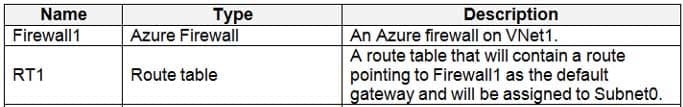
You have an Azure subscription that contains the resources shown in the following table.
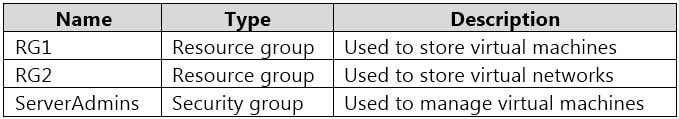
AZ-500 Microsoft Azure Security Technologies Part 04 Q04 120 You need to ensure that ServerAdmins can perform the following tasks:
– Create virtual machines in RG1 only.
– Connect the virtual machines to the existing virtual networks in RG2 only.The solution must use the principle of least privilege.
Which two role-based access control (RBAC) roles should you assign to ServerAdmins? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- a custom RBAC role for RG2
- the Network Contributor role for RG2
- the Contributor role for the subscription
- a custom RBAC role for the subscription
- the Network Contributor role for RG1
- the Virtual Machine Contributor role for RG1
-
HOTSPOT
Your network contains an on-premises Active Directory domain named adatum.com that syncs to Azure Active Directory (Azure AD).
The Azure AD tenant contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q05 121 You configure the Authentication methods – Password Protection settings for adatum.com as shown in the following exhibit.

AZ-500 Microsoft Azure Security Technologies Part 04 Q05 122 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 04 Q05 123 Question 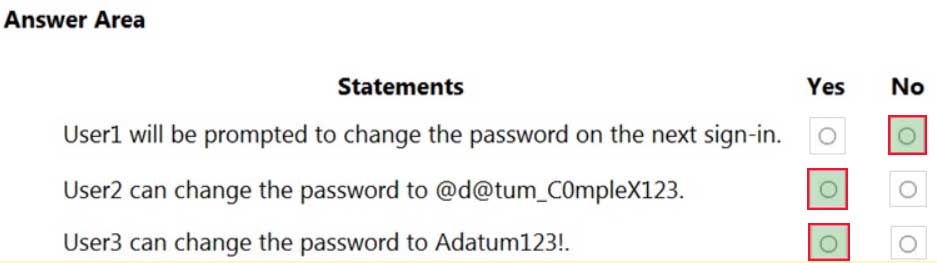
AZ-500 Microsoft Azure Security Technologies Part 04 Q05 123 Answer -
HOTSPOT
Your company has an Azure subscription named Subscription1. Subscription1 is associated with the Azure Active Directory tenant that includes the users shown in the following table.
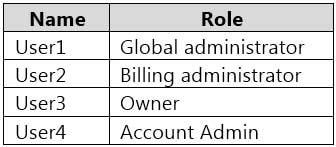
AZ-500 Microsoft Azure Security Technologies Part 04 Q06 124 The company is sold to a new owner.
The company needs to transfer ownership of Subscription1.
Which user can transfer the ownership and which tool should the user use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
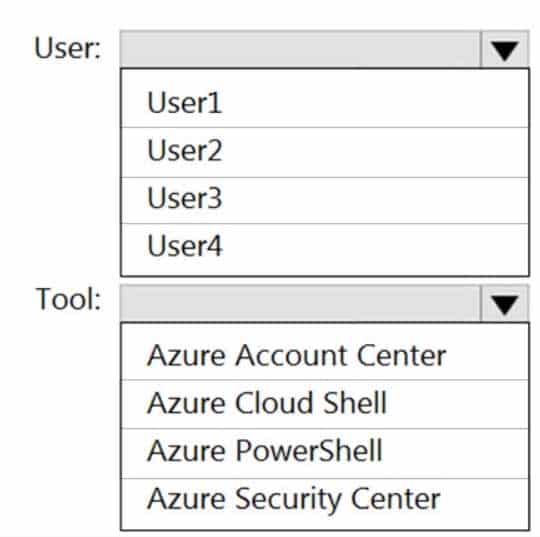
AZ-500 Microsoft Azure Security Technologies Part 04 Q06 125 Question 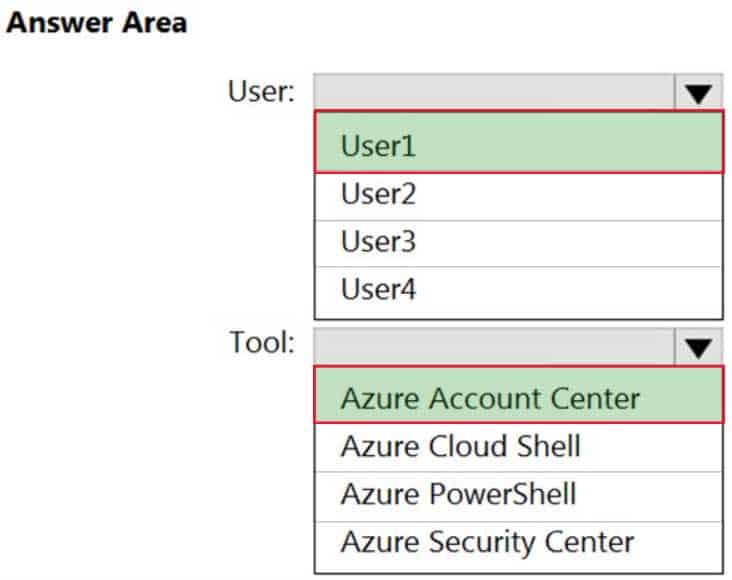
AZ-500 Microsoft Azure Security Technologies Part 04 Q06 125 Answer -
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Litware, Inc. is a digital media company that has 500 employees in the Chicago area and 20 employees in the San Francisco area.
Existing Environment
Litware has an Azure subscription named Sub1 that has a subscription ID of 43894a43-17c2-4a39-8cfc-3540c2653ef4.
Sub1 is associated to an Azure Active Directory (Azure AD) tenant named litwareinc.com. The tenant contains the user objects and the device objects of all the Litware employees and their devices. Each user is assigned an Azure AD Premium P2 license. Azure AD Privileged Identity Management (PIM) is activated.
The tenant contains the groups shown in the following table.

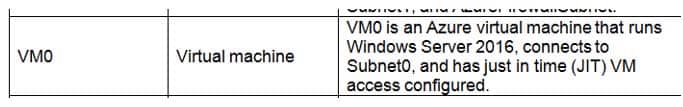
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 126 The Azure subscription contains the objects shown in the following table.
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 127 Identity and Access Requirements
Azure Security Center is set to the Standard tier.
Requirements
Planned Changes
Litware plans to deploy the Azure resources shown in the following table.
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 128 Litware identifies the following identity and access requirements:
All San Francisco users and their devices must be members of Group1.
The members of Group2 must be assigned the Contributor role to RG2 by using a permanent eligible assignment.
Users must be prevented from registering applications in Azure AD and from consenting to applications that access company information on the users’ behalf.Platform Protection Requirements
Litware identifies the following platform protection requirements:
– Microsoft Antimalware must be installed on the virtual machines in RG1.
– The members of Group2 must be assigned the Azure Kubernetes Service Cluster Admin Role.
– Azure AD users must be able to authenticate to AKS1 by using their Azure AD credentials.
– Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
– A new custom RBAC role named Role1 must be used to delegate the administration of the managed disks in RG1. Role1 must be available only for RG1.Security Operations Requirements
Litware must be able to customize the operating system security configurations in Azure Security Center.
Data and Application Requirements
Litware identifies the following data and applications requirements:
– The users in Group2 must be able to authenticate to SQLDB1 by using their Azure AD credentials.
– WebApp1 must enforce mutual authentication.General Requirements
Litware identifies the following general requirements:
– Whenever possible, administrative effort must be minimized.
– Whenever possible, use of automation must be maximized.-
DRAG DROP
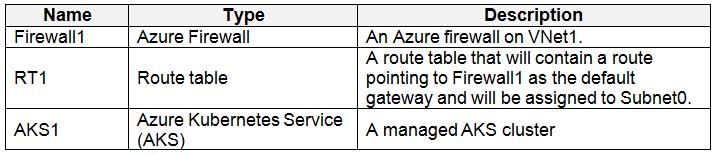
You need to deploy AKS1 to meet the platform protection requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.

AZ-500 Microsoft Azure Security Technologies Part 04 Q07 129 Question 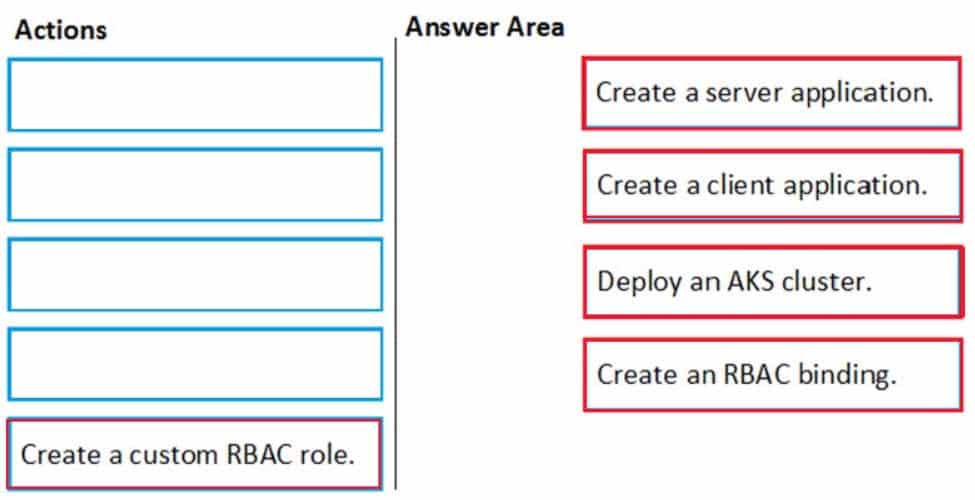
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 129 Answer Explanation:Scenario: Azure AD users must be able to authenticate to AKS1 by using their Azure AD credentials.
Litware plans to deploy AKS1, which is a managed AKS (Azure Kubernetes Services) cluster.
Step 1: Create a server application
To provide Azure AD authentication for an AKS cluster, two Azure AD applications are created. The first application is a server component that provides user authentication.Step 2: Create a client application
The second application is a client component that’s used when you’re prompted by the CLI for authentication. This client application uses the server application for the actual authentication of the credentials provided by the client.Step 3: Deploy an AKS cluster.
Use the az group create command to create a resource group for the AKS cluster.
Use the az aks create command to deploy the AKS cluster.Step 4: Create an RBAC binding.
Before you use an Azure Active Directory account with an AKS cluster, you must create role-binding or cluster role-binding. Roles define the permissions to grant, and bindings apply them to desired users. These assignments can be applied to a given namespace, or across the entire cluster. -
You need to ensure that users can access VM0. The solution must meet the platform protection requirements.
What should you do?
- Move VM0 to Subnet1.
- On Firewall, configure a network traffic filtering rule.
- Assign RT1 to AzureFirewallSubnet.
- On Firewall, configure a DNAT rule.
Explanation:Azure Firewall has the following known issue:
Conflict with Azure Security Center (ASC) Just-in-Time (JIT) feature.If a virtual machine is accessed using JIT, and is in a subnet with a user-defined route that points to Azure Firewall as a default gateway, ASC JIT doesn’t work. This is a result of asymmetric routing – a packet comes in via the virtual machine public IP (JIT opened the access), but the return path is via the firewall, which drops the packet because there is no established session on the firewall.
Solution: To work around this issue, place the JIT virtual machines on a separate subnet that doesn’t have a user-defined route to the firewall.
Scenario:
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 130 Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 131 -
HOTSPOT
You need to deploy Microsoft Antimalware to meet the platform protection requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 04 Q07 132 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q07 132 Answer Explanation:Scenario: Microsoft Antimalware must be installed on the virtual machines in RG1.
RG1 is a resource group that contains Vnet1, VM0, and VM1.Box 1: DeployIfNotExists
DeployIfNotExists executes a template deployment when the condition is met.
Azure policy definition AntimalwareIncorrect Answers:
Append:
Append is used to add additional fields to the requested resource during creation or update. A common example is adding tags on resources such as costCenter or specifying allowed IPs for a storage resource.Deny:
Deny is used to prevent a resource request that doesn’t match defined standards through a policy definition and fails the request.Box 2: The Create a Managed Identity setting
When Azure Policy runs the template in the deployIfNotExists policy definition, it does so using a managed identity. Azure Policy creates a managed identity for each assignment, but must have details about what roles to grant the managed identity.
-
-
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and two branch offices in Seattle and New York.
The company hosts its entire server infrastructure in Azure.
Contoso has two Azure subscriptions named Sub1 and Sub2. Both subscriptions are associated to an Azure Active Directory (Azure AD) tenant named contoso.com.
Existing Environment
Azure AD
Contoso.com contains the users shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 133 Contoso.com contains the security groups shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 134 Sub1
Sub1 contains six resource groups named RG1, RG2, RG3, RG4, RG5, and RG6.
User9 creates the virtual networks shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 135 Sub1 contains the locks shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 136 Sub1 contains the Azure policies shown in the following table.
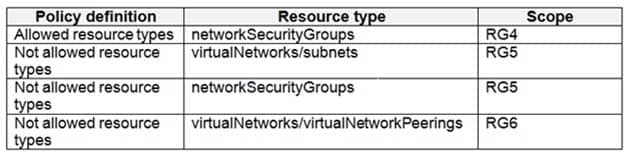
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 137 Sub2
Sub2 contains the virtual networks shown in the following table.
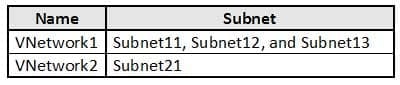
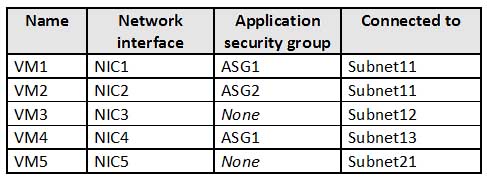
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 138 Sub2 contains the virtual machines shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 139 All virtual machines have public IP addresses and the Web Server (IIS) role installed. The firewalls for each virtual machine allow ping requests and web requests.
Sub2 contains the network security groups (NSGs) shown in the following table.

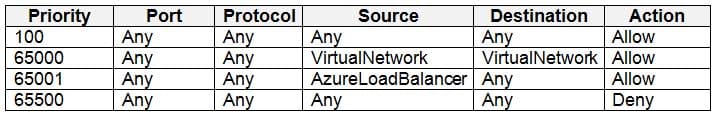
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 140 NSG1 has the inbound security rules shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 141 NSG2 has the inbound security rules shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 142 NSG3 has the inbound security rules shown in the following table.
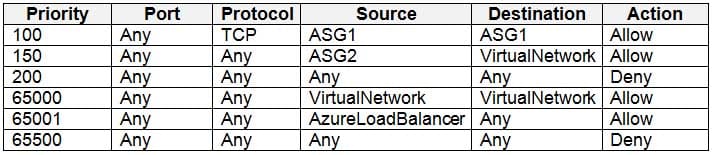
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 143 NSG4 has the inbound security rules shown in the following table.
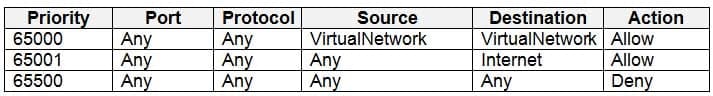
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 144 NSG1, NSG2, NSG3, and NSG4 have the outbound security rules shown in the following table.
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 145 Technical Requirements
Contoso identifies the following technical requirements:
– Deploy Azure Firewall to VNetwork1 in Sub2.
– Register an application named App2 in contoso.com.
– Whenever possible, use the principle of least privilege.
– Enable Azure AD Privileged Identity Management (PIM) for contoso.com.-
HOTSPOT
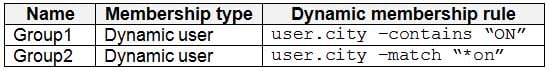
What is the membership of Group1 and Group2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 146 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 146 Answer Explanation:Box 1: User1, User2, User3, User4
Contains “ON” is true for Montreal (User1), MONTREAL (User2), London (User 3), and Ontario (User4) as string and regex operations are not case sensitive.Box 2: Only User3
Match “*on” is only true for London (User3) as ‘London’ is the only word that ends with ‘on’.Scenario:
Contoso.com contains the users shown in the following table.
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 147 Contoso.com contains the security groups shown in the following table.
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 148 -
HOTSPOT
You are evaluating the security of the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
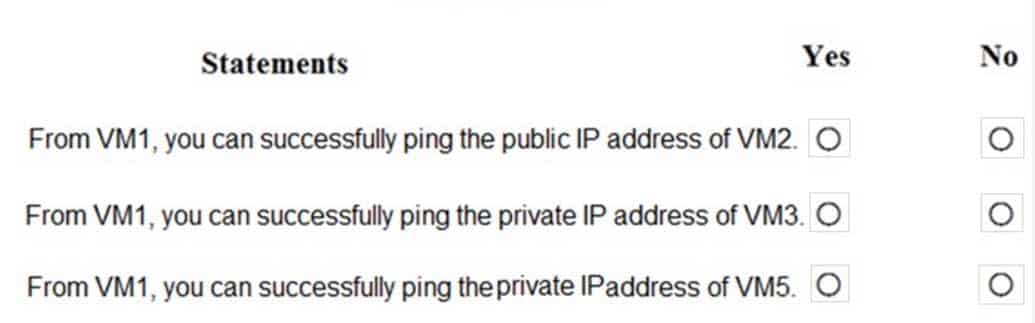
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 149 Question 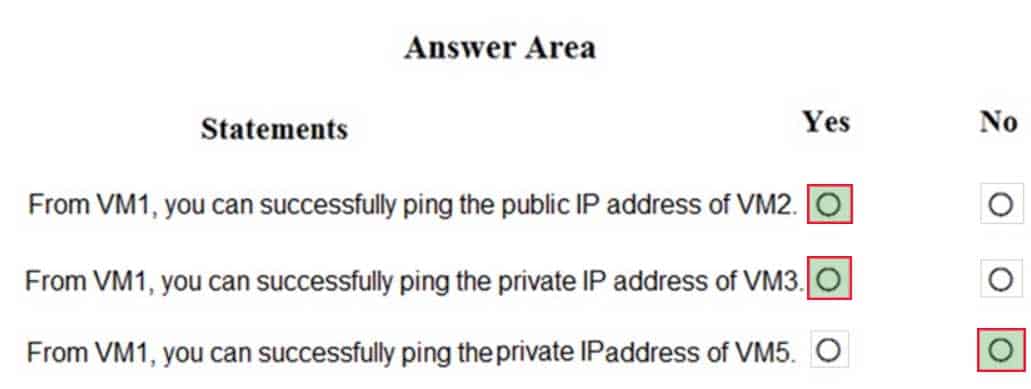
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 149 Answer Explanation:Box 1: Yes. All traffic is allowed out to the Internet so you can ping the public IP.
NSG1, NSG2, NSG3, and NSG4 have the outbound security rules shown in the following table.
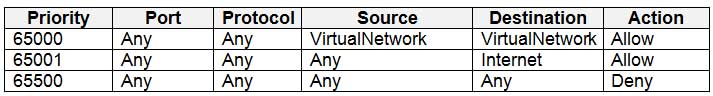
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 150 Box 2: Yes. VM3 is on Subnet12. There is no NSG attached to Subnet12 so the traffic will be allowed by default.
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 151 
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 152 Box 3: No (because VM5 is in a separate VNet).
Note: Sub2 contains the virtual machines shown in the following table.
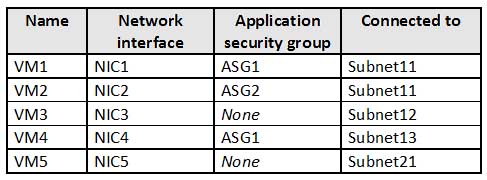
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 153 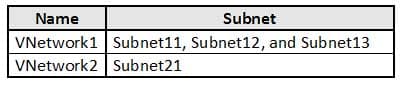
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 154 -
HOTSPOT
You are evaluating the effect of the application security groups on the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
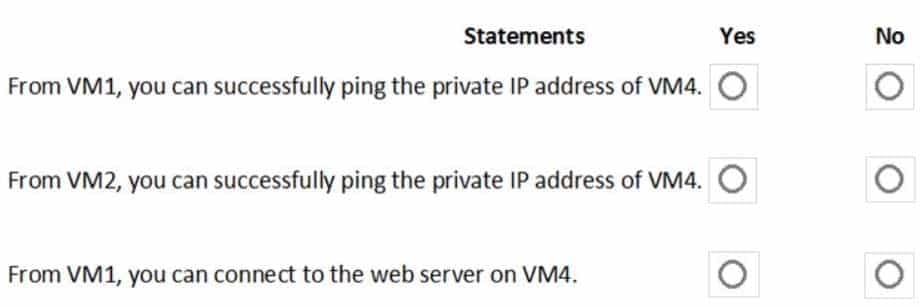
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 155 Question 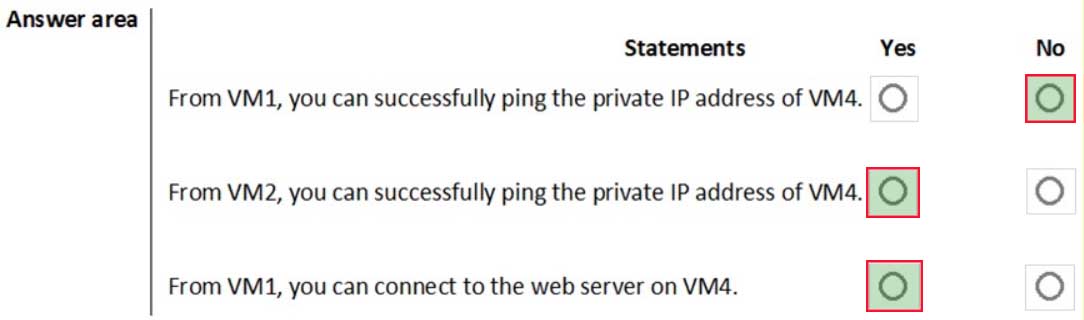
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 155 Answer Explanation:Box 1: No. VM4 is in Subnet13 which has NSG3 attached to it.
VM1 is in ASG1. NSG3 would only allow ICMP pings from ASG2 but not ASG1. Only TCP traffic is allowed from ASG1.
NSG3 has the inbound security rules shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q08 156 Box 2: Yes.
VM2 is in ASG2. Any protocol is allowed from ASG2 so ICMP ping would be allowed.Box3. VM1 is in ASG1. TCP traffic is allowed from ASG1 so VM1 could connect to the web server as connections to the web server would be on ports TCP 80 or TCP 443.
-
You need to meet the technical requirements for VNetwork1.
What should you do first?
- Create a new subnet on VNetwork1.
- Remove the NSGs from Subnet11 and Subnet13.
- Associate an NSG to Subnet12.
- Configure DDoS protection for VNetwork1.
Explanation:From scenario: Deploy Azure Firewall to VNetwork1 in Sub2.
Azure firewall needs a dedicated subnet named AzureFirewallSubnet.
-
HOTSPOT
You are evaluating the security of VM1, VM2, and VM3 in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
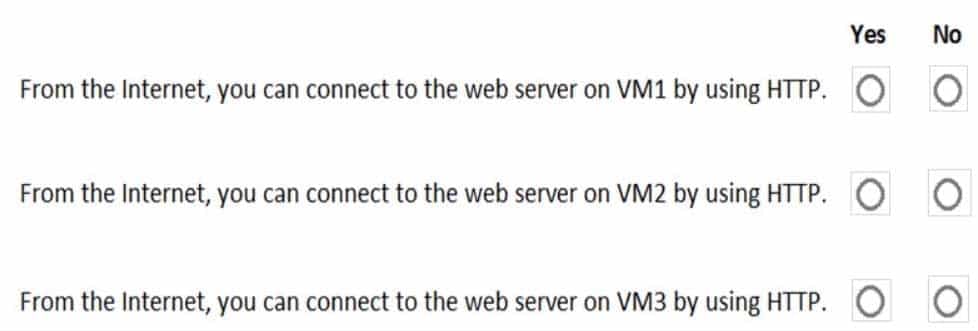
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 157 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q08 157 Answer Explanation:VM1: Yes. NSG2 applies to VM1 and this allows inbound traffic on port 80.
VM2: No. NSG2 and NSG1 apply to VM2. NSG2 allows the inbound traffic on port 80 but NSG1 does not allow it.
VM3: Yes. There are no NSGs applying to VM3 so all ports will be open.
-
-
You have an Azure Kubernetes Service (AKS) cluster that will connect to an Azure Container Registry.
You need to use the automatically generated service principal for the AKS cluster to authenticate to the Azure Container Registry.
What should you create?
- a secret in Azure Key Vault
- a role assignment
- an Azure Active Directory (Azure AD) user
- an Azure Active Directory (Azure AD) group
-
You have an Azure subscription that contains two virtual machines named VM1 and VM2 that run Windows Server 2019.
You are implementing Update Management in Azure Automation.
You plan to create a new update deployment named Update1.
You need to ensure that Update1 meets the following requirements:
Automatically applies updates to VM1 and VM2.
Automatically adds any new Windows Server 2019 virtual machines to Update1.What should you include in Update1?
- a security group that has a Membership type of Assigned
- a security group that has a Membership type of Dynamic Device
- a dynamic group query
- a Kusto query language query
-
You have the Azure virtual machines shown in the following table.

AZ-500 Microsoft Azure Security Technologies Part 04 Q11 158 For which virtual machines can you enable Update Management?
- VM2 and VM3 only
- VM2, VM3, and VM4 only
- VM1, VM2, and VM4 only
- VM1, VM2, VM3, and VM4
- VM1, VM2, and VM3 only
-
DRAG DROP
You have an Azure subscription named Sub1.
You have an Azure Active Directory (Azure AD) group named Group1 that contains all the members of your IT team.
You need to ensure that the members of Group1 can stop, start, and restart the Azure virtual machines in Sub1. The solution must use the principle of least privilege.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.

AZ-500 Microsoft Azure Security Technologies Part 04 Q12 159 Question 
AZ-500 Microsoft Azure Security Technologies Part 04 Q12 159 Answer -
DRAG DROP
You have an Azure subscription that contains the following resources:
A virtual network named VNET1 that contains two subnets named Subnet1 and Subnet2.
A virtual machine named VM1 that has only a private IP address and connects to Subnet1.You need to ensure that Remote Desktop connections can be established to VM1 from the internet.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange then in the correct order.

AZ-500 Microsoft Azure Security Technologies Part 04 Q13 160 Question 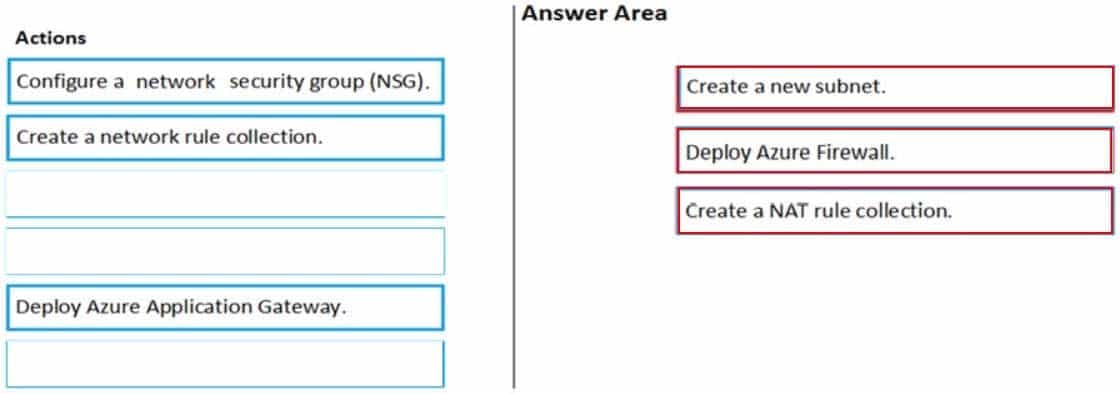
AZ-500 Microsoft Azure Security Technologies Part 04 Q13 160 Answer -
You have an Azure subscription that contains a user named User1 and an Azure Container Registry named ContReg1.
You enable content trust for ContReg1.
You need to ensure that User1 can create trusted images in ContReg1. The solution must use the principle of least privilege.
Which two roles should you assign to User1? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- AcrQuarantineReader
- Contributor
- AcrPush
- AcrImageSigner
- AcrQuarantineWriter
-
You have an Azure Container Registry named ContReg1 that contains a container image named image1.
You enable content trust for ContReg1.
After content trust is enabled, you push two images to ContReg1 as shown in the following table.
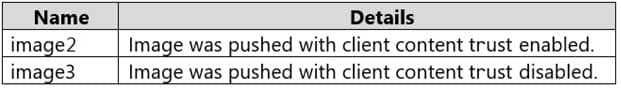
AZ-500 Microsoft Azure Security Technologies Part 04 Q14 161 Which images are trusted images?
- image1 and image2 only
- image2 only
- image1, image2, and image3
Explanation:Azure Container Registry implements Docker’s content trust model, enabling pushing and pulling of signed images.
To push a trusted image tag to your container registry, enable content trust and push the image with docker push.
To work with trusted images, both image publishers and consumers need to enable content trust for their Docker clients. As a publisher, you can sign the images you push to a content trust-enabled registry.
-
SIMULATION
You need to configure Azure to allow RDP connections from the Internet to a virtual machine named VM1. The solution must minimize the attack surface of VM1.
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:To enable the RDP port in an NSG, follow these steps:
1. Sign in to the Azure portal.
2. In Virtual Machines, select VM1
3. In Settings, select Networking.
4. In Inbound port rules, check whether the port for RDP is set correctly. The following is an example of the configuration:Priority: 300
Name: Port_3389
Port(Destination): 3389
Protocol: TCP
Source: Any
Destinations: Any
Action: Allow -
SIMULATION
You need to add the network interface of a virtual machine named VM1 to an application security group named ASG1.
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:
1. In the Search resources, services, and docs box at the top of the portal, begin typing the name of a virtual machine, VM1 that has a network interface that you want to add to, or remove from, an application security group.
2. When the name of your VM appears in the search results, select it.
3. Under SETTINGS, select Networking. Select Configure the application security groups, select the application security groups that you want to add the network interface to, or unselect the application security groups that you want to remove the network interface from, and then select Save. -
SIMULATION
You need to perform a full malware scan every Sunday at 02:00 on a virtual machine named VM1 by using Microsoft Antimalware for Virtual Machines.
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:Deploy the Microsoft Antimalware Extension using the Azure Portal for single VM deployment
1. In Azure Portal, go to the Azure VM1’s blade, navigate to the Extensions section and press Add.

AZ-500 Microsoft Azure Security Technologies Part 04 Q18 162 2. Select the Microsoft Antimalware extension and press Create.
3. Fill the “Install extension” form as desired and press OK.
Scheduled: Enable
Scan type: Full
Scan day: Sunday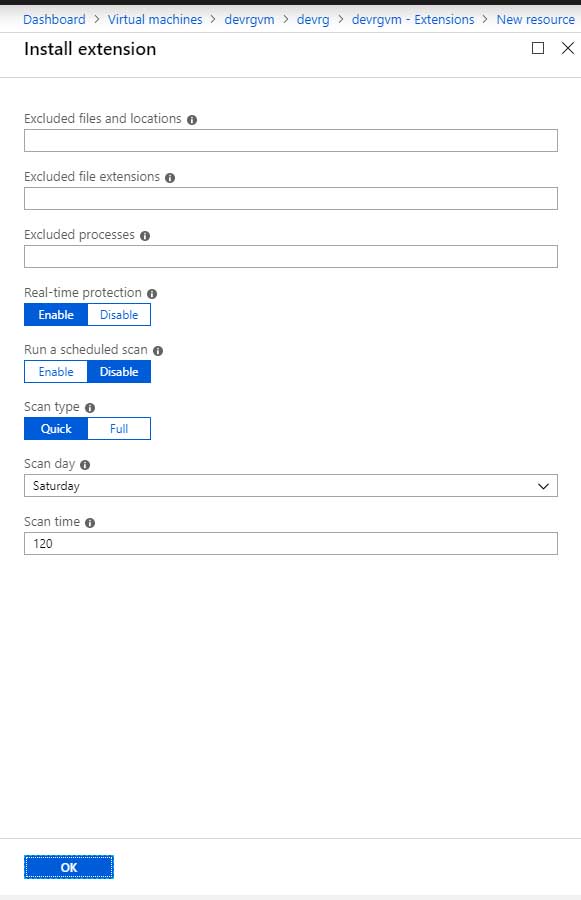
AZ-500 Microsoft Azure Security Technologies Part 04 Q18 163 -
SIMULATION
You need to prevent administrative users from accidentally deleting a virtual network named VNET1. The administrative users must be allowed to modify the settings of VNET1.
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:Explanation:
Locking prevents other users in your organization from accidentally deleting or modifying critical resources, such as Azure subscription, resource group, or resource.Note: In Azure, the term resource refers to an entity managed by Azure. For example, virtual machines, virtual networks, and storage accounts are all referred to as Azure resources.
1. In the Settings blade for virtual network VNET, select Locks.
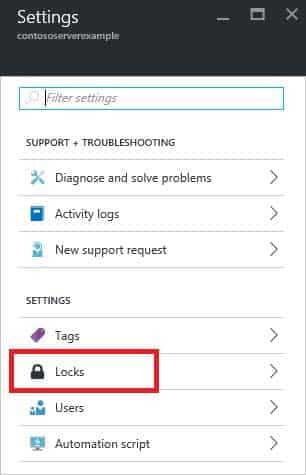
AZ-500 Microsoft Azure Security Technologies Part 04 Q19 164 2. To add a lock, select Add.
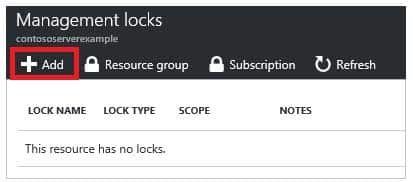
AZ-500 Microsoft Azure Security Technologies Part 04 Q19 165 3. For Lock type select Delete lock, and click OK
-
SIMULATION
You need to grant the required permissions to a user named User211641655 to manage the virtual networks in the RG1lod11641655 resource group. The solution must use the principle of least privilege.
To complete this task, sign in to the Azure portal.
- See the explanation below.
Explanation:1. In Azure portal, locate and select the RG1lod10598168 resource group.
2. Click Access control (IAM).
3. Click the Role assignments tab to view all the role assignments at this scope.
4. Click Add > Add role assignment to open the Add role assignment pane.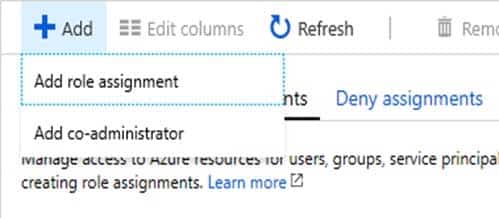
AZ-500 Microsoft Azure Security Technologies Part 04 Q20 166 5. In the Role drop-down list, select the role Virtual Machine Contributor.
Virtual Machine Contributor lets you manage virtual machines, but not access to them, and not the virtual network or storage account they’re connected to.
6. In the Select list, select user user21059868
7. Click Save to assign the role.