SC-300 : Microsoft Identity and Access Administrator : Part 02
-
HOTSPOT
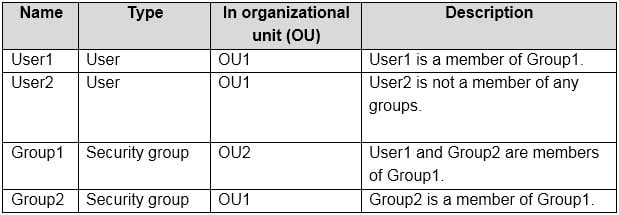
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains the objects shown in the following table.
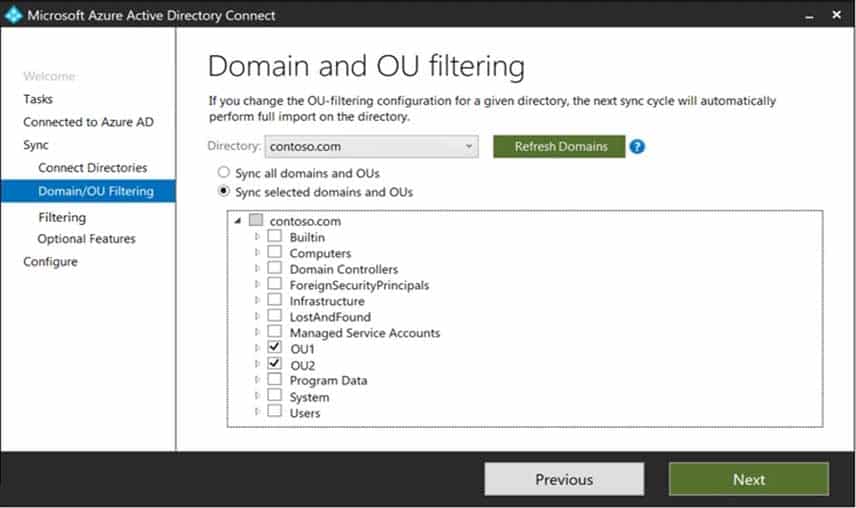
SC-300 Microsoft Identity and Access Administrator Part 02 Q01 021 You install Azure AD Connect. You configure the Domain and OU filtering settings as shown in the Domain and OU Filtering exhibit. (Click the Domain and OU Filtering tab.)
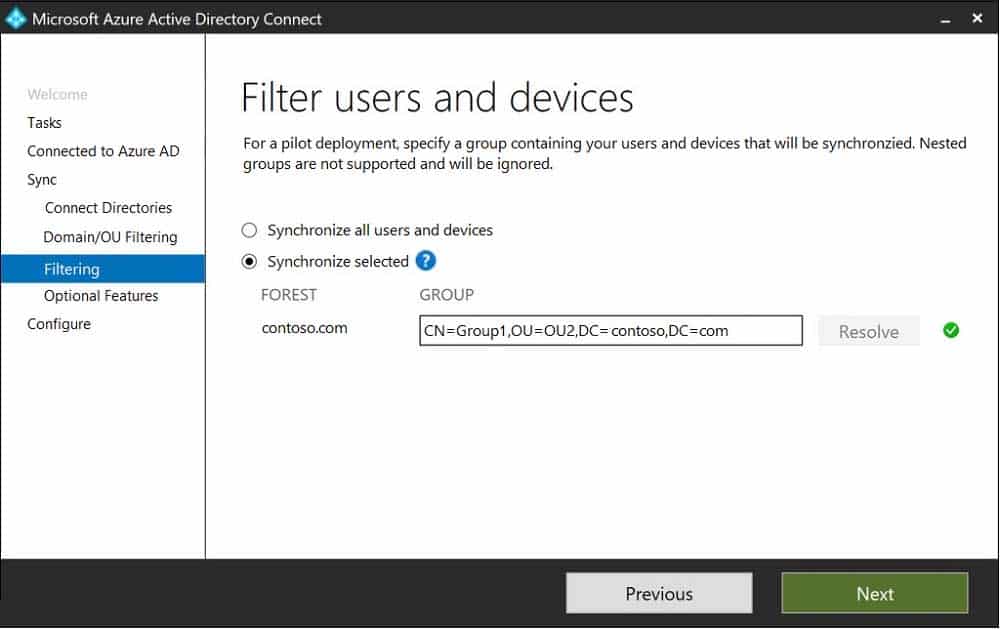
SC-300 Microsoft Identity and Access Administrator Part 02 Q01 022 You configure the Filter users and devices settings as shown in the Filter Users and Devices exhibit. (Click the Filter Users and Devices tab.)
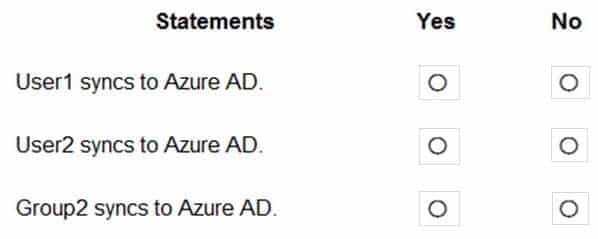
SC-300 Microsoft Identity and Access Administrator Part 02 Q01 023 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
SC-300 Microsoft Identity and Access Administrator Part 02 Q01 024 Question 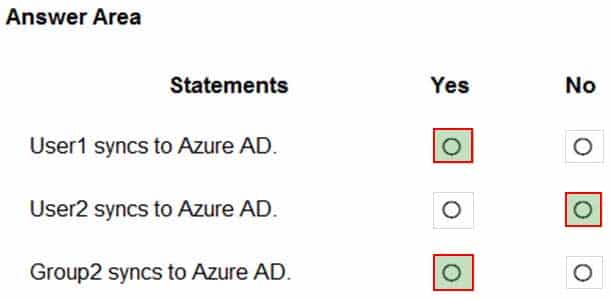
SC-300 Microsoft Identity and Access Administrator Part 02 Q01 024 Answer Explanation:Only direct members of Group1 are synced. Group2 will sync as it is a direct member of Group1 but the members of Group2 will not sync.
-
You have an Azure Active Directory (Azure AD) tenant named contoso.com.
You need to ensure that Azure AD External Identities pricing is based on monthly active users (MAU).
What should you configure?
- a user flow
- the terms of use
- a linked subscription
- an access review
-
DRAG DROP
You have a new Microsoft 365 tenant that uses a domain name of contoso.onmicrosoft.com.
You register the name contoso.com with a domain registrar.
You need to use contoso.com as the default domain name for new Microsoft 365 users.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
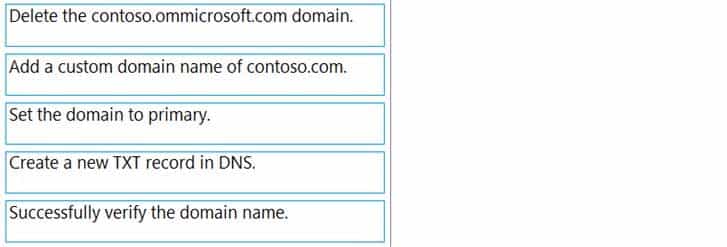
SC-300 Microsoft Identity and Access Administrator Part 02 Q03 025 Question 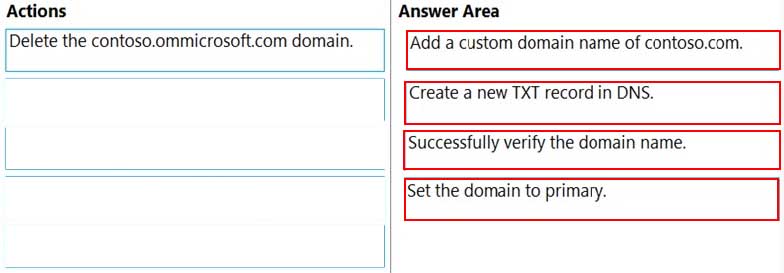
SC-300 Microsoft Identity and Access Administrator Part 02 Q03 025 Answer -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that has an Azure Active Directory Premium Plan 2 license. The tenant contains the users shown in the following table.
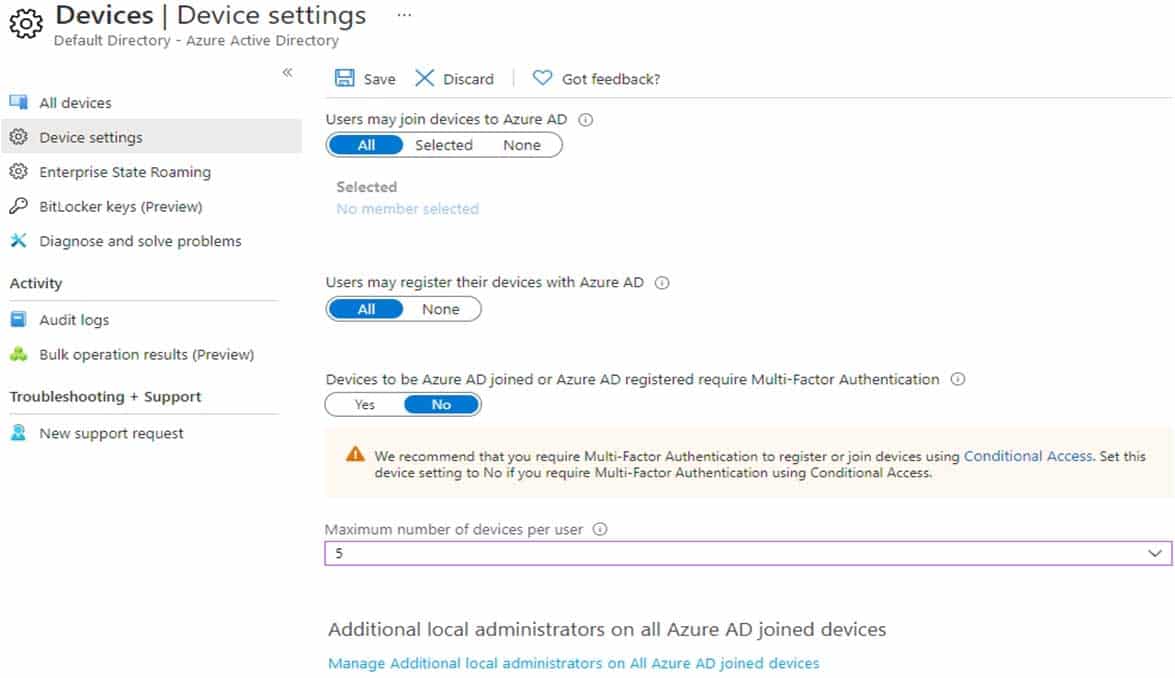
SC-300 Microsoft Identity and Access Administrator Part 02 Q04 026 You have the Device Settings shown in the following exhibit.
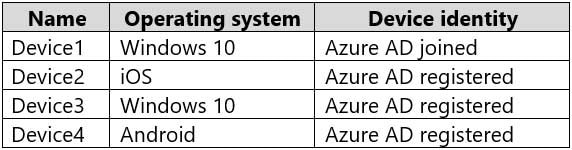
SC-300 Microsoft Identity and Access Administrator Part 02 Q04 027 User1 has the devices shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 02 Q04 028 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
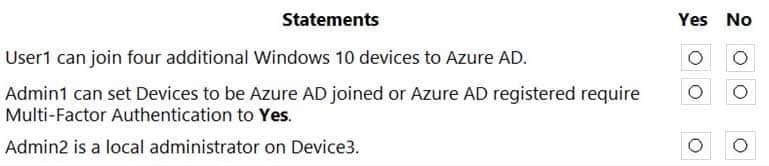
SC-300 Microsoft Identity and Access Administrator Part 02 Q04 029 Question 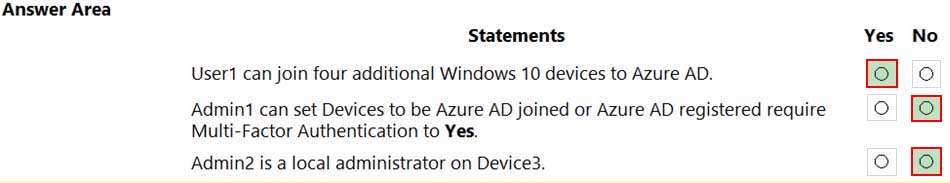
SC-300 Microsoft Identity and Access Administrator Part 02 Q04 029 Answer Explanation:Box 1: Yes
Users may join 5 devices to Azure AD.Box 2: No
Cloud device administrator an enable, disable, and delete devices in Azure AD and read Windows 10 BitLocker keys in the Azure portal. The role does not grant permissions to manage any other properties on the device.Box 3: No
An additional local device administrator has not been applied -
Case Study
Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and branch offices in London and Seattle.
Contoso has a partnership with a company named Fabrikam, Inc. Fabrikam has an Azure Active Directory (Azure AD) tenant named fabrikam.com.
Existing Environment. Existing Environment
The on-premises network of Contoso contains an Active Directory domain named contoso.com. The domain contains an organizational unit (OU) named Contoso_Resources. The Contoso_Resources OU contains all users and computers.
The contoso.com Active Directory domain contains the relevant users shown in the following table.
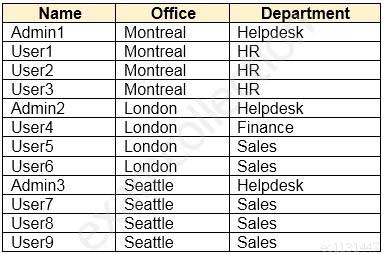
SC-300 Microsoft Identity and Access Administrator Part 02 Q05 030 Contoso also includes a marketing department that has users in each office.
Existing Environment. Microsoft 365/Azure Environment
Contoso has an Azure AD tenant named contoso.com that has the following associated licenses:
– Microsoft Office 365 Enterprise E5
– Enterprise Mobility + Security E5
– Windows 10 Enterprise E3
– Project Plan 3Azure AD Connect is configured between Azure AD and Active Directory Domain Services (AD DS). Only the Contoso_Resources OU is synced.
Helpdesk administrators routinely use the Microsoft 365 admin center to manage user settings.
User administrators currently use the Microsoft 365 admin center to manually assign licenses. All users have all licenses assigned besides the following exceptions:
– The users in the London office have the Microsoft 365 Phone System license unassigned.
– The users in the Seattle office have the Yammer Enterprise license unassigned.Security defaults are disabled for contoso.com.
Contoso uses Azure AD Privileged Identity Management (PIM) to protect administrative roles.
Existing Environment. Problem Statements
Contoso identifies the following issues:
– Currently, all the helpdesk administrators can manage user licenses throughout the entire Microsoft 365 tenant.
– The user administrators report that it is tedious to manually configure the different license requirements for each Contoso office.
– The helpdesk administrators spend too much time provisioning internal and guest access to the required Microsoft 365 services and apps.
– Currently, the helpdesk administrators can perform tasks by using the User administrator role without justification or approval.
– When the Logs node is selected in Azure AD, an error message appears stating that Log Analytics integration is not enabled.Requirements. Planned Changes
Contoso plans to implement the following changes:
– Implement self-service password reset (SSPR).
– Analyze Azure audit activity logs by using Azure Monitor.
– Simplify license allocation for new users added to the tenant.
– Collaborate with the users at Fabrikam on a joint marketing campaign.
– Configure the User administrator role to require justification and approval to activate.
– Implement a custom line-of-business Azure web app named App1. App1 will be accessible from the internet and authenticated by using Azure AD accounts.
– For new users in the marketing department, implement an automated approval workflow to provide access to a Microsoft SharePoint Online site, group, and app.Contoso plans to acquire a company named ADatum Corporation. One hundred new ADatum users will be created in an Active Directory OU named Adatum. The users will be located in London and Seattle.
Requirements. Technical Requirements
Contoso identifies the following technical requirements:
– All users must be synced from AD DS to the contoso.com Azure AD tenant.
– App1 must have a redirect URI pointed to https://contoso.com/auth-response.
– License allocation for new users must be assigned automatically based on the location of the user.
– Fabrikam users must have access to the marketing department’s SharePoint site for a maximum of 90 days.
– Administrative actions performed in Azure AD must be audited. Audit logs must be retained for one year.
– The helpdesk administrators must be able to manage licenses for only the users in their respective office.
– Users must be forced to change their password if there is a probability that the users’ identity was compromised.-
HOTSPOT
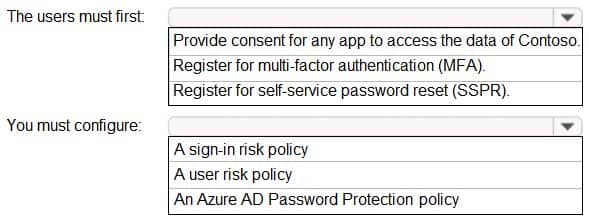
You need to meet the technical requirements for the probability that user identities were compromised.
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
SC-300 Microsoft Identity and Access Administrator Part 02 Q05 031 Question 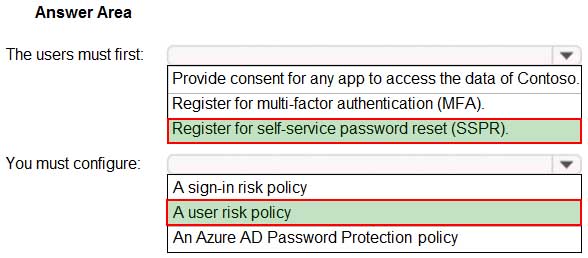
SC-300 Microsoft Identity and Access Administrator Part 02 Q05 031 Answer
-
-
Case Study
Overview
Litware, Inc. is a pharmaceutical company that has a subsidiary named Fabrikam, Inc.
Litware has offices in Boston and Seattle, but has employees located across the United States. Employees connect remotely to either office by using a VPN connection.
Existing Environment. Identity Environment
The network contains an Active Directory forest named litware.com that is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Azure AD Connect uses pass-through authentication and has password hash synchronization disabled.
Litware.com contains a user named User1 who oversees all application development.
Litware implements Azure AD Application Proxy.
Fabrikam has an Azure AD tenant named fabrikam.com. The users at Fabrikam access the resources in litware.com by using guest accounts in the litware.com tenant.
Existing Environment. Cloud Environment
All the users at Litware have Microsoft 365 Enterprise E5 licenses. All the built-in anomaly detection policies in Microsoft Cloud App Security are enabled.
Litware has an Azure subscription associated to the litware.com Azure AD tenant. The subscription contains an Azure Sentinel instance that uses the Azure Active Directory connector and the Office 365 connector. Azure Sentinel currently collects the Azure AD sign-ins logs and audit logs.
Existing Environment. On-premises Environment
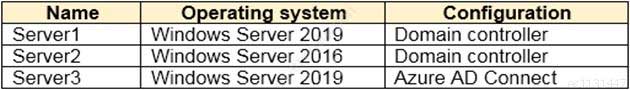
The on-premises network contains the servers shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 02 Q06 032 Both Litware offices connect directly to the internet. Both offices connect to virtual networks in the Azure subscription by using a site-to-site VPN connection. All on-premises domain controllers are prevented from accessing the internet.
Requirements. Delegation Requirements
Litware identifies the following delegation requirements:
– Delegate the management of privileged roles by using Azure AD Privileged Identity Management (PIM).
– Prevent nonprivileged users from registering applications in the litware.com Azure AD tenant.
– Use custom programs for Identity Governance.
– Ensure that User1 can create enterprise applications in Azure AD.
– Use the principle of least privilege.Requirements. Licensing Requirements
Litware recently added a custom user attribute named LWLicenses to the litware.com Active Directory forest. Litware wants to manage the assignment of Azure AD licenses by modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to a Microsoft 365 group that has the appropriate licenses assigned.
Requirements. Management Requirements
Litware wants to create a group named LWGroup1 that will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Requirements. Authentication Requirements
Litware identifies the following authentication requirements:
– Implement multi-factor authentication (MFA) for all Litware users by using conditional access policies.
– Exempt users from using MFA to authenticate to Azure AD from the Boston office of Litware.
– Implement a banned password list for the litware.com forest.
– Enforce MFA when accessing on-premises applications.
– Automatically detect and remediate externally leaked credentials.Requirements. Access Requirements
Litware identifies the following access requirements:
– Control all access to all Azure resources and Azure AD applications by using conditional access policies.
– Implement a conditional access policy that has session controls for Microsoft SharePoint Online.
– Control privileged access to applications by using access reviews in Azure AD.Requirements. Monitoring Requirements
Litware wants to use the Fusion rule in Azure Sentinel to detect multi-staged attacks that include a combination of suspicious Azure AD sign-ins followed by anomalous Microsoft Office 365 activity.
-
You need to configure the MFA settings for users who connect from the Boston office. The solution must meet the authentication requirements and the access requirements.
What should you include in the configuration?
- named locations that have a private IP address range
- named locations that have a public IP address range
- trusted IPs that have a public IP address range
- trusted IPs that have a private IP address range
-
-
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that has Security defaults disabled.
You are creating a conditional access policy as shown in the following exhibit.
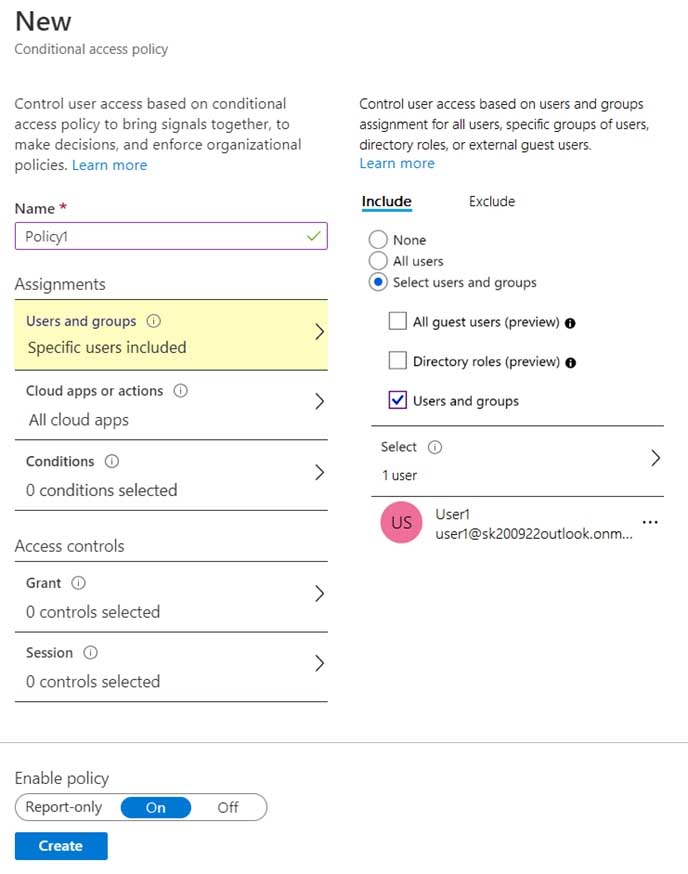
SC-300 Microsoft Identity and Access Administrator Part 02 Q07 033 Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
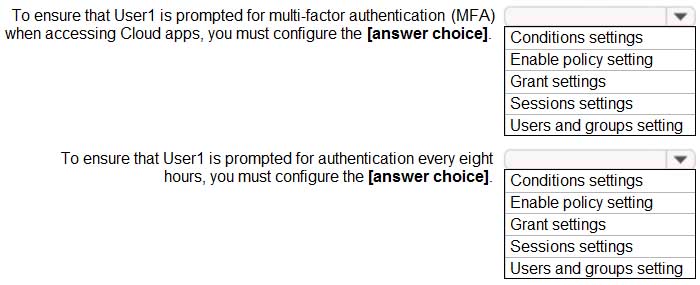
SC-300 Microsoft Identity and Access Administrator Part 02 Q07 034 Question 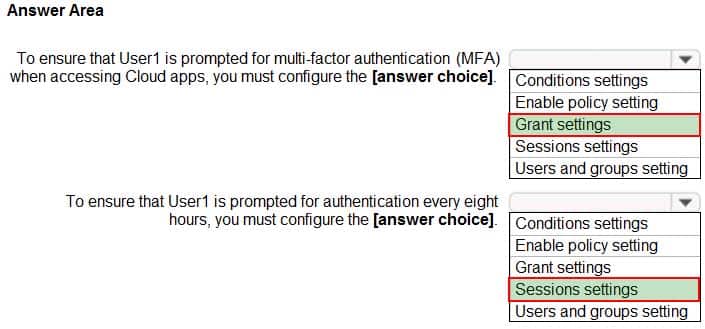
SC-300 Microsoft Identity and Access Administrator Part 02 Q07 034 Answer -
You have an Azure Active Directory (Azure AD) tenant that contains a user named SecAdmin1. SecAdmin1 is assigned the Security administrator role.
SecAdmin1 reports that she cannot reset passwords from the Azure AD Identity Protection portal.
You need to ensure that SecAdmin1 can manage passwords and invalidate sessions on behalf of non-administrative users. The solution must use the principle of least privilege.
Which role should you assign to SecAdmin1?
- Authentication administrator
- Helpdesk administrator
- Privileged authentication administrator
- Security operator
-
You configure Azure Active Directory (Azure AD) Password Protection as shown in the exhibit. (Click the Exhibit tab.)
SC-300 Microsoft Identity and Access Administrator Part 02 Q09 035 You are evaluating the following passwords:
– Pr0jectlitw@re
– T@ilw1nd
– C0nt0s0Which passwords will be blocked?
- Pr0jectlitw@re and T@ilw1nd only
- C0nt0s0 only
- C0nt0s0, Pr0jectlitw@re, and T@ilw1nd
- C0nt0s0 and T@ilw1nd only
- C0nt0s0 and Pr0jectlitw@re only
-
You have a Microsoft 365 tenant.
All users have mobile phones and laptops.
The users frequently work from remote locations that do not have Wi-Fi access or mobile phone connectivity. While working from the remote locations, the users connect their laptop to a wired network that has internet access.
You plan to implement multi-factor authentication (MFA).
Which MFA authentication method can the users use from the remote location?
- a verification code from the Microsoft Authenticator app
- security questions
- voice
- SMS
Explanation:An automated voice call is made to the phone number registered by the user. To complete the sign-in process, the user is prompted to press # on their keypad.
Incorrect Answers:
A: The Microsoft Authenticator app requires a mobile phone that runs Android or iOS
B: Security questions are not used as an authentication method but can be used during the self-service password reset (SSPR) process.
D: SMS requires a mobile phone -
You configure a new Microsoft 365 tenant to use a default domain name of contoso.com.
You need to ensure that you can control access to Microsoft 365 resources by using conditional access policies.
What should you do first?
- Disable the User consent settings.
- Disable Security defaults.
- Configure a multi-factor authentication (MFA) registration policy.
- Configure password protection for Windows Server Active Directory.
-
Your company has a Microsoft 365 tenant.
The company has a call center that contains 300 users. In the call center, the users share desktop computers and might use a different computer every day. The call center computers are NOT configured for biometric identification.
The users are prohibited from having a mobile phone in the call center.
You need to require multi-factor authentication (MFA) for the call center users when they access Microsoft 365 services.
What should you include in the solution?
- a named network location
- the Microsoft Authenticator app
- Windows Hello for Business authentication
- FIDO2 tokens
-
You have an Azure Active Directory (Azure AD) tenant named contoso.com.
All users who run applications registered in Azure AD are subject to conditional access policies.
You need to prevent the users from using legacy authentication.
What should you include in the conditional access policies to filter out legacy authentication attempts?
- a cloud apps or actions condition
- a user risk condition
- a client apps condition
- a sign-in risk condition
-
You have an Azure Active Directory (Azure AD) tenant.
You open the risk detections report.
Which risk detection type is classified as a user risk?
- impossible travel
- anonymous IP address
- atypical travel
- leaked credentials
-
You have a Microsoft 365 tenant.
All users have computers that run Windows 10. Most computers are company-owned and joined to Azure Active Directory (Azure AD). Some computers are user-owned and are only registered in Azure AD.
You need to prevent users who connect to Microsoft SharePoint Online on their user-owned computer from downloading or syncing files. Other users must NOT be restricted.
Which policy type should you create?
- a Microsoft Cloud App Security activity policy that has Microsoft Office 365 governance actions configured
- an Azure AD conditional access policy that has session controls configured
- an Azure AD conditional access policy that has client apps conditions configured
- a Microsoft Cloud App Security app discovery policy that has governance actions configured
-
You have an Active Directory domain that syncs to an Azure Active Directory (Azure AD) tenant.
The on-premises network contains a VPN server that authenticates to the on-premises Active Directory domain. The VPN server does NOT support Azure Multi-Factor Authentication (MFA).
You need to recommend a solution to provide Azure MFA for VPN connections.
What should you include in the recommendation?
- Azure AD Application Proxy
- an Azure AD Password Protection proxy
- Network Policy Server (NPS)
- a pass-through authentication proxy
-
You have a Microsoft 365 tenant.
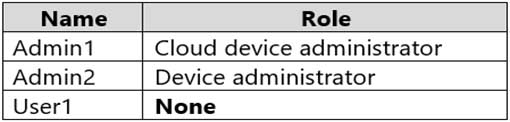
The Azure Active Directory (Azure AD) tenant is configured to sync with an on-premises Active Directory domain. The domain contains the servers shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 02 Q17 036 The domain controllers are prevented from communicating to the internet.
You implement Azure AD Password Protection on Server1 and Server2.
You deploy a new server named Server4 that runs Windows Server 2019.
You need to ensure that Azure AD Password Protection will continue to work if a single server fails.
What should you implement on Server4?
- Azure AD Connect
- Azure AD Application Proxy
- Password Change Notification Service (PCNS)
- the Azure AD Password Protection proxy service
-
DRAG DROP
You have a Microsoft 365 E5 tenant.
You purchase a cloud app named App1.
You need to enable real-time session-level monitoring of App1 by using Microsoft Cloud App Security.
In which order should you perform the actions? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
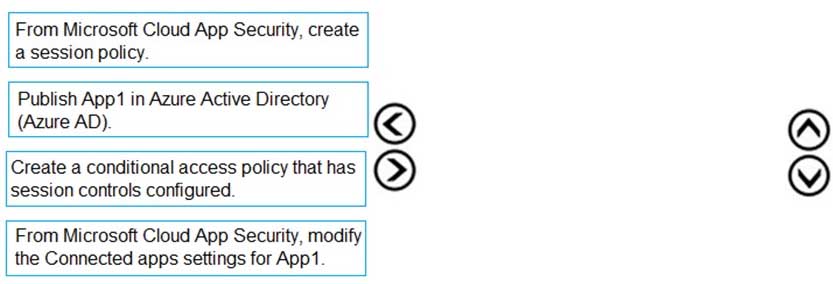
SC-300 Microsoft Identity and Access Administrator Part 02 Q18 037 Question 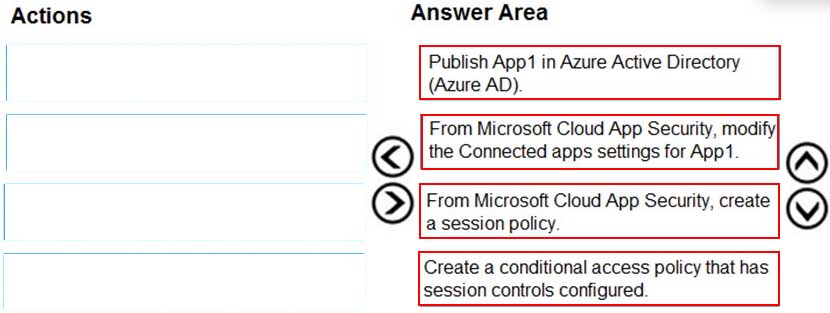
SC-300 Microsoft Identity and Access Administrator Part 02 Q18 037 Answer -
You have a Microsoft 365 tenant.
All users have mobile phones and laptops.
The users frequently work from remote locations that do not have Wi-Fi access or mobile phone connectivity. While working from the remote locations, the users connect their laptop to a wired network that has internet access.
You plan to implement multi-factor authentication (MFA).
Which MFA authentication method can the users use from the remote location?
- a notification through the Microsoft Authenticator app
- an app password
- Windows Hello for Business
- SMS
Explanation:In Windows 10, Windows Hello for Business replaces passwords with strong two-factor authentication on PCs and mobile devices. This authentication consists of a new type of user credential that is tied to a device and uses a biometric or PIN.
After an initial two-step verification of the user during enrollment, Windows Hello is set up on the user’s device and Windows asks the user to set a gesture, which can be a biometric, such as a fingerprint, or a PIN. The user provides the gesture to verify their identity. Windows then uses Windows Hello to authenticate users.Incorrect Answers:
A: The Microsoft Authenticator app requires a mobile phone that runs Android or iOS
B: An app password can be used to open an application but it cannot be used to sign in to a computer.
D: SMS requires a mobile phone -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant.
All users must use the Microsoft Authenticator app for multi-factor authentication (MFA) when accessing Microsoft 365 services.
Some users report that they received an MFA prompt on their Microsoft Authenticator app without initiating a sign-in request.
You need to block the users automatically when they report an MFA request that they did not initiate.
Solution: From the Azure portal, you configure the Notifications settings for multi-factor authentication (MFA).
Does this meet the goal?
- Yes
- No
Explanation:
You need to configure the fraud alert settings.