SC-300 : Microsoft Identity and Access Administrator : Part 04
-
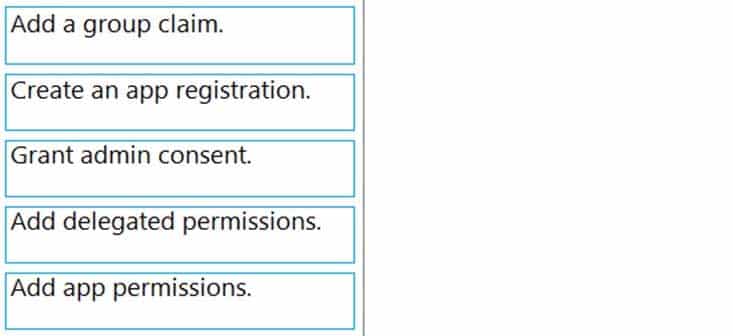
DRAG DROP
Your company has an Azure Active Directory (Azure AD) tenant named contoso.com.
The company is developing a web service named App1.
You need to ensure that App1 can use Microsoft Graph to read directory data in contoso.com.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange then in the correct order.
SC-300 Microsoft Identity and Access Administrator Part 04 Q01 063 Question 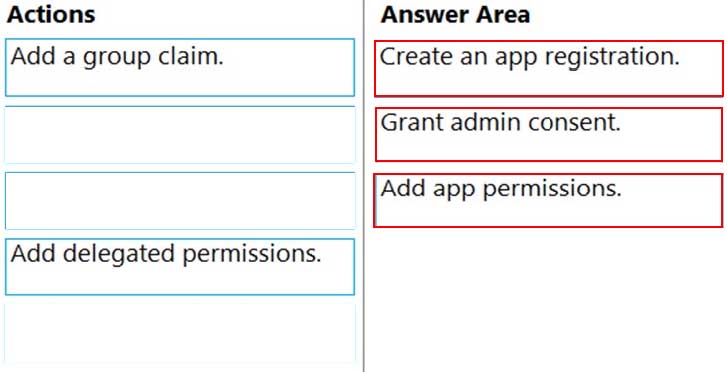
SC-300 Microsoft Identity and Access Administrator Part 04 Q01 063 Answer Explanation:1. Create an app registration:
Your app must be registered with the Microsoft identity platform and be authorized by either a user or an administrator for access to the Microsoft Graph resources it needs.
2. Grant admin consent:
Higher-privileged permissions require administrator consent.
3. Add app permissions:
After the consents to permissions for your app, your app can acquire access tokens that represent the app’s permission to access a resource in some capacity. Encoded inside the access token is every permission that your app has been granted for that resource. -
Case Study
Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and branch offices in London and Seattle.
Contoso has a partnership with a company named Fabrikam, Inc. Fabrikam has an Azure Active Directory (Azure AD) tenant named fabrikam.com.
Existing Environment. Existing Environment
The on-premises network of Contoso contains an Active Directory domain named contoso.com. The domain contains an organizational unit (OU) named Contoso_Resources. The Contoso_Resources OU contains all users and computers.
The contoso.com Active Directory domain contains the relevant users shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 04 Q02 064 Contoso also includes a marketing department that has users in each office.
Existing Environment. Microsoft 365/Azure Environment
Contoso has an Azure AD tenant named contoso.com that has the following associated licenses:
– Microsoft Office 365 Enterprise E5
– Enterprise Mobility + Security E5
– Windows 10 Enterprise E3
– Project Plan 3Azure AD Connect is configured between Azure AD and Active Directory Domain Services (AD DS). Only the Contoso_Resources OU is synced.
Helpdesk administrators routinely use the Microsoft 365 admin center to manage user settings.
User administrators currently use the Microsoft 365 admin center to manually assign licenses. All users have all licenses assigned besides the following exceptions:
– The users in the London office have the Microsoft 365 Phone System license unassigned.
– The users in the Seattle office have the Yammer Enterprise license unassigned.Security defaults are disabled for contoso.com.
Contoso uses Azure AD Privileged Identity Management (PIM) to protect administrative roles.
Existing Environment. Problem Statements
Contoso identifies the following issues:
– Currently, all the helpdesk administrators can manage user licenses throughout the entire Microsoft 365 tenant.
– The user administrators report that it is tedious to manually configure the different license requirements for each Contoso office.
– The helpdesk administrators spend too much time provisioning internal and guest access to the required Microsoft 365 services and apps.
– Currently, the helpdesk administrators can perform tasks by using the User administrator role without justification or approval.
– When the Logs node is selected in Azure AD, an error message appears stating that Log Analytics integration is not enabled.Requirements. Planned Changes
Contoso plans to implement the following changes:
– Implement self-service password reset (SSPR).
– Analyze Azure audit activity logs by using Azure Monitor.
– Simplify license allocation for new users added to the tenant.
– Collaborate with the users at Fabrikam on a joint marketing campaign.
– Configure the User administrator role to require justification and approval to activate.
– Implement a custom line-of-business Azure web app named App1. App1 will be accessible from the internet and authenticated by using Azure AD accounts.
– For new users in the marketing department, implement an automated approval workflow to provide access to a Microsoft SharePoint Online site, group, and app.Contoso plans to acquire a company named ADatum Corporation. One hundred new ADatum users will be created in an Active Directory OU named Adatum. The users will be located in London and Seattle.
Requirements. Technical Requirements
Contoso identifies the following technical requirements:
– All users must be synced from AD DS to the contoso.com Azure AD tenant.
– App1 must have a redirect URI pointed to https://contoso.com/auth-response.
– License allocation for new users must be assigned automatically based on the location of the user.
– Fabrikam users must have access to the marketing department’s SharePoint site for a maximum of 90 days.
– Administrative actions performed in Azure AD must be audited. Audit logs must be retained for one year.
– The helpdesk administrators must be able to manage licenses for only the users in their respective office.
– Users must be forced to change their password if there is a probability that the users’ identity was compromised.-
You create a Log Analytics workspace.
You need to implement the technical requirements for auditing.
What should you configure in Azure AD?
- Company branding
- Diagnostics settings
- External Identities
- App registrations
-
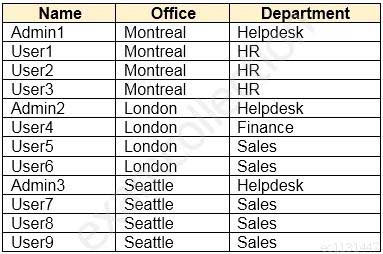
HOTSPOT
You need to implement the planned changes and technical requirements for the marketing department.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
SC-300 Microsoft Identity and Access Administrator Part 04 Q02 065 Question 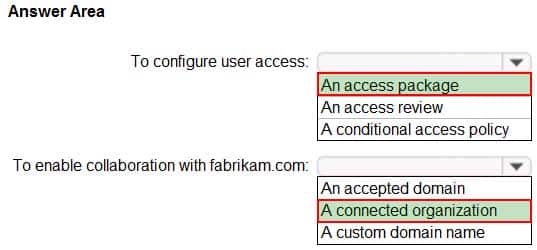
SC-300 Microsoft Identity and Access Administrator Part 04 Q02 065 Answer -
You need to meet the planned changes for the User administrator role.
What should you do?
- Create an access review.
- Create an administrative unit.
- Modify Active assignments.
- Modify Role settings.
-
-
Case Study
Overview
Litware, Inc. is a pharmaceutical company that has a subsidiary named Fabrikam, Inc.
Litware has offices in Boston and Seattle, but has employees located across the United States. Employees connect remotely to either office by using a VPN connection.
Existing Environment. Identity Environment
The network contains an Active Directory forest named litware.com that is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Azure AD Connect uses pass-through authentication and has password hash synchronization disabled.
Litware.com contains a user named User1 who oversees all application development.
Litware implements Azure AD Application Proxy.
Fabrikam has an Azure AD tenant named fabrikam.com. The users at Fabrikam access the resources in litware.com by using guest accounts in the litware.com tenant.
Existing Environment. Cloud Environment
All the users at Litware have Microsoft 365 Enterprise E5 licenses. All the built-in anomaly detection policies in Microsoft Cloud App Security are enabled.
Litware has an Azure subscription associated to the litware.com Azure AD tenant. The subscription contains an Azure Sentinel instance that uses the Azure Active Directory connector and the Office 365 connector. Azure Sentinel currently collects the Azure AD sign-ins logs and audit logs.
Existing Environment. On-premises Environment
The on-premises network contains the servers shown in the following table.
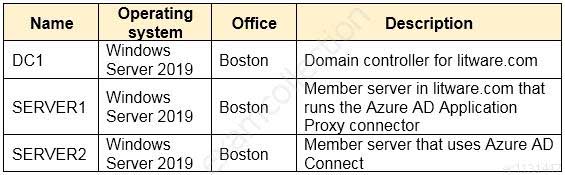
SC-300 Microsoft Identity and Access Administrator Part 04 Q03 066 Both Litware offices connect directly to the internet. Both offices connect to virtual networks in the Azure subscription by using a site-to-site VPN connection. All on-premises domain controllers are prevented from accessing the internet.
Requirements. Delegation Requirements
Litware identifies the following delegation requirements:
– Delegate the management of privileged roles by using Azure AD Privileged Identity Management (PIM).
– Prevent nonprivileged users from registering applications in the litware.com Azure AD tenant.
– Use custom programs for Identity Governance.
– Ensure that User1 can create enterprise applications in Azure AD.
– Use the principle of least privilege.Requirements. Licensing Requirements
Litware recently added a custom user attribute named LWLicenses to the litware.com Active Directory forest. Litware wants to manage the assignment of Azure AD licenses by modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to a Microsoft 365 group that has the appropriate licenses assigned.
Requirements. Management Requirements
Litware wants to create a group named LWGroup1 that will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Requirements. Authentication Requirements
Litware identifies the following authentication requirements:
– Implement multi-factor authentication (MFA) for all Litware users by using conditional access policies.
– Exempt users from using MFA to authenticate to Azure AD from the Boston office of Litware.
– Implement a banned password list for the litware.com forest.
– Enforce MFA when accessing on-premises applications.
– Automatically detect and remediate externally leaked credentials.Requirements. Access Requirements
Litware identifies the following access requirements:
– Control all access to all Azure resources and Azure AD applications by using conditional access policies.
– Implement a conditional access policy that has session controls for Microsoft SharePoint Online.
– Control privileged access to applications by using access reviews in Azure AD.Requirements. Monitoring Requirements
Litware wants to use the Fusion rule in Azure Sentinel to detect multi-staged attacks that include a combination of suspicious Azure AD sign-ins followed by anomalous Microsoft Office 365 activity.
-
You need to configure the detection of multi-staged attacks to meet the monitoring requirements.
What should you do?
- Customize the Azure Sentinel rule logic.
- Create a workbook.
- Add Azure Sentinel data connectors.
- Add an Azure Sentinel playbook.
-
You need to track application access assignments by using Identity Governance. The solution must meet the delegation requirements.
What should you do first?
- Modify the User consent settings for the enterprise applications.
- Create a catalog.
- Create a program.
- Modify the Admin consent requests settings for the enterprise applications.
-
-
You have a Microsoft 365 tenant.
In Azure Active Directory (Azure AD), you configure the terms of use.
You need to ensure that only users who accept the terms of use can access the resources in the tenant. Other users must be denied access.
What should you configure?
- an access policy in Microsoft Cloud App Security.
- Terms and conditions in Microsoft Endpoint Manager.
- a conditional access policy in Azure AD
- a compliance policy in Microsoft Endpoint Manager
-
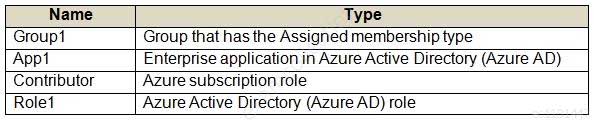
You have an Azure Active Directory (Azure AD) tenant that contains the groups shown in the following table.
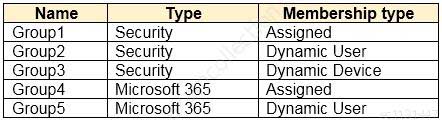
SC-300 Microsoft Identity and Access Administrator Part 04 Q05 067 For which groups can you create an access review?
- Group1 only
- Group1 and Group4 only
- Group1 and Group2 only
- Group1, Group2, Group4, and Group5 only
- Group1, Group2, Group3, Group4 and Group5
Explanation:
You cannot create access reviews for device groups. -
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.
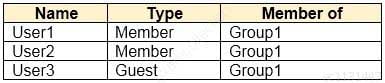
SC-300 Microsoft Identity and Access Administrator Part 04 Q06 068 User1 is the owner of Group1.
You create an access review that has the following settings:
– Users to review: Members of a group
– Scope: Everyone
– Group: Group1
– Reviewers: Members (self)Which users can perform access reviews for User3?
- User1, User2, and User3
- User3 only
- User1 only
- User1 and User2 only
-
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains Azure AD Privileged Identity Management (PIM) role settings for the User administrator role as shown in the following exhibit.
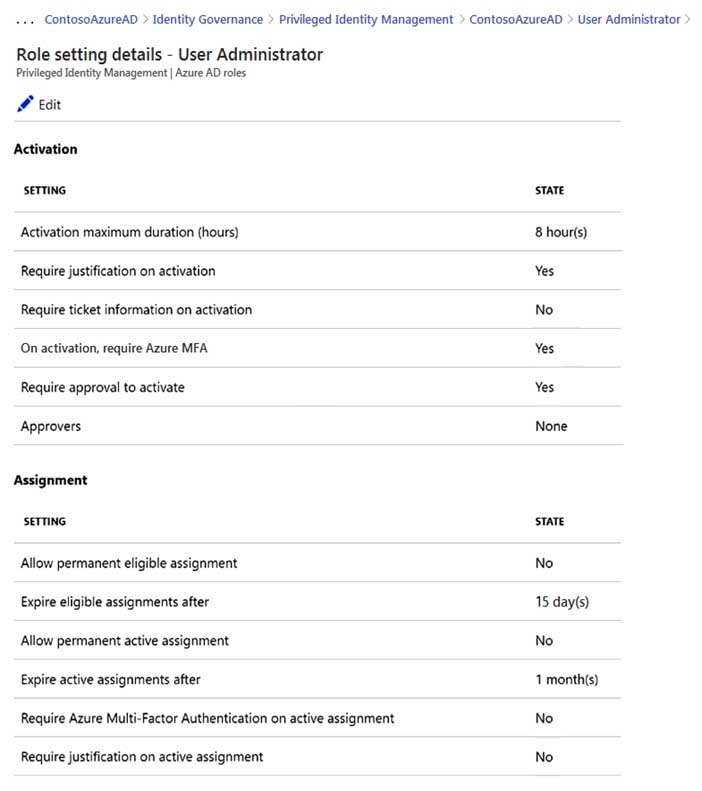
SC-300 Microsoft Identity and Access Administrator Part 04 Q07 069 Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
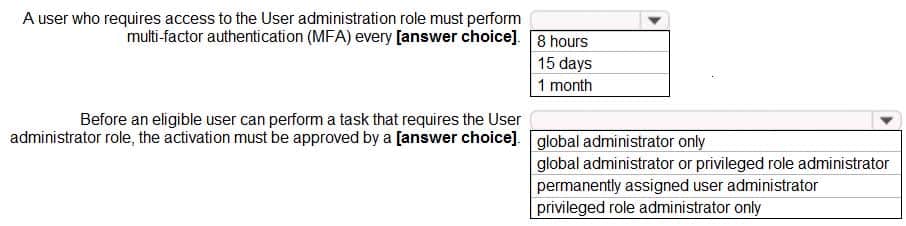
SC-300 Microsoft Identity and Access Administrator Part 04 Q07 070 Question 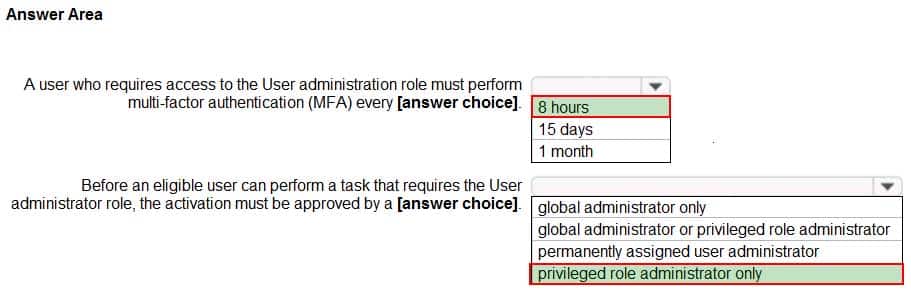
SC-300 Microsoft Identity and Access Administrator Part 04 Q07 070 Answer -
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant named contoso.com that contains a user named User1.
User1 has the devices shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 04 Q08 071 On November 5, 2020, you create and enforce terms of use in contoso.com that has the following settings:
– Name: Terms1
– Display name: Contoso terms of use
– Require users to expand the terms of use: On
– Require users to consent on every device: On
– Expire consents: On
– Expire starting on: December 10, 2020
– Frequency: MonthlyOn November 15, 2020, User1 accepts Terms1 on Device3.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
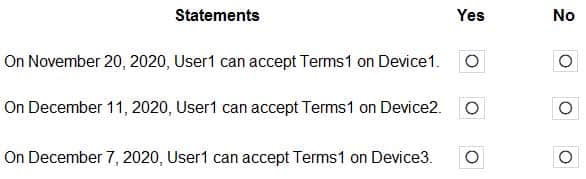
SC-300 Microsoft Identity and Access Administrator Part 04 Q08 072 Question 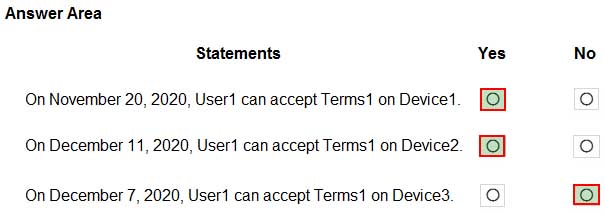
SC-300 Microsoft Identity and Access Administrator Part 04 Q08 072 Answer Explanation:Box 1: Yes because User1 has not yet accepted the terms on Device1.
Box 2: Yes because User1 has not yet accepted the terms on Device2. User1 will be prompted to register the device before the terms can be accepted.
Box 3: No because User1 has already accepted the terms on Device3. The terms do not expire until December 10th and then monthly after that.
-
Your company recently implemented Azure Active Directory (Azure AD) Privileged Identity Management (PIM).
While you review the roles in PIM, you discover that all 15 users in the IT department at the company have permanent security administrator rights.
You need to ensure that the IT department users only have access to the Security administrator role when required.
What should you configure for the Security administrator role assignment?
- Expire eligible assignments after from the Role settings details
- Expire active assignments after from the Role settings details
- Assignment type to Active
- Assignment type to Eligible
-
You have a Microsoft 365 tenant.
The Sign-ins activity report shows that an external contractor signed in to the Exchange admin center.
You need to review access to the Exchange admin center at the end of each month and block sign-ins if required.
What should you create?
- an access package that targets users outside your directory
- an access package that targets users in your directory
- a group-based access review that targets guest users
- an application-based access review that targets guest users
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant.
You have 100 IT administrators who are organized into 10 departments.
You create the access review shown in the exhibit. (Click the Exhibit tab.)
SC-300 Microsoft Identity and Access Administrator Part 04 Q11 073 You discover that all access review requests are received by Megan Bowen.
You need to ensure that the manager of each department receives the access reviews of their respective department.
Solution: You create a separate access review for each role.
Does this meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
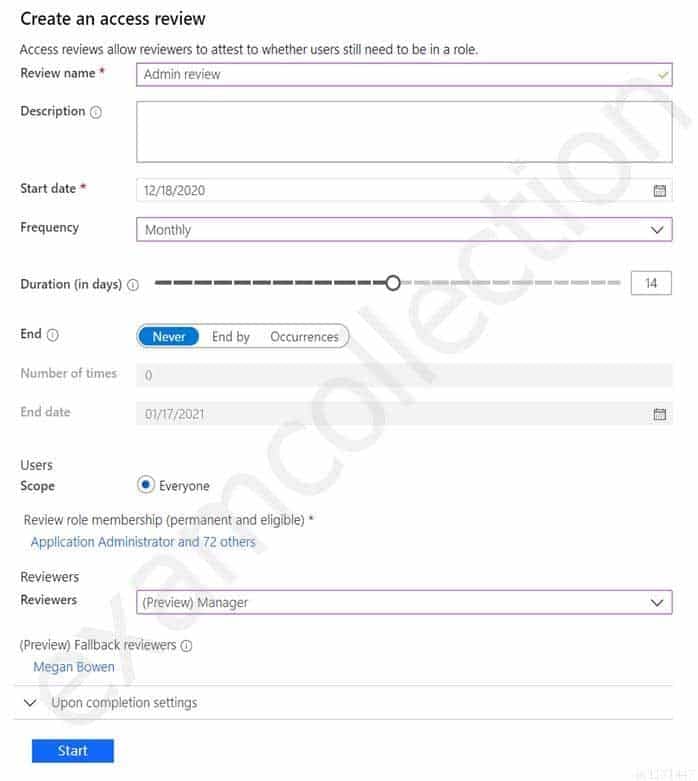
You have a Microsoft 365 tenant.
You have 100 IT administrators who are organized into 10 departments.
You create the access review shown in the exhibit. (Click the Exhibit tab.)
SC-300 Microsoft Identity and Access Administrator Part 04 Q12 074 You discover that all access review requests are received by Megan Bowen.
You need to ensure that the manager of each department receives the access reviews of their respective department.
Solution: You modify the properties of the IT administrator user accounts.
Does this meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant.
You have 100 IT administrators who are organized into 10 departments.
You create the access review shown in the exhibit. (Click the Exhibit tab.)
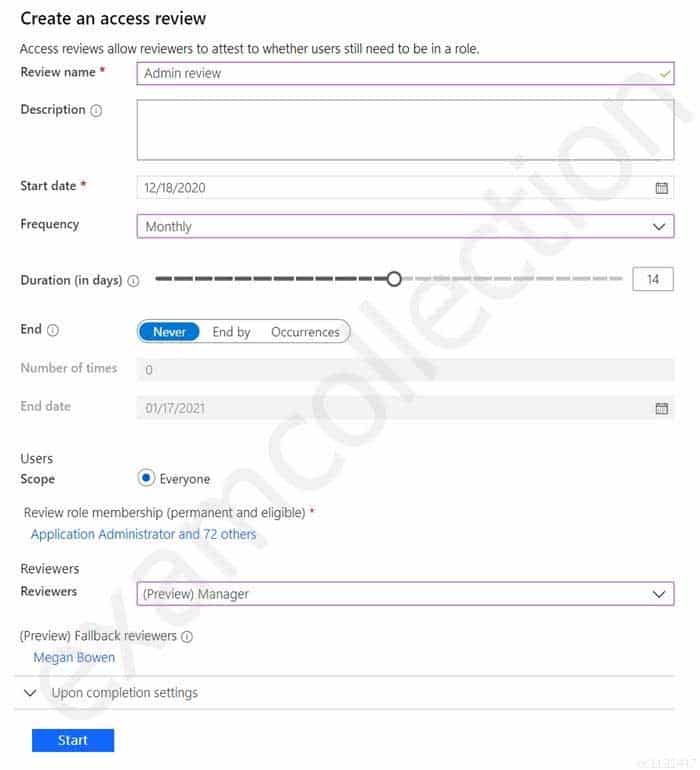
SC-300 Microsoft Identity and Access Administrator Part 04 Q13 075 You discover that all access review requests are received by Megan Bowen.
You need to ensure that the manager of each department receives the access reviews of their respective department.
Solution: You set Reviewers to Member (self).
Does this meet the goal?
- Yes
- No
-
You have a Microsoft 365 tenant.
The Azure Active Directory (Azure AD) tenant syncs to an on-premises Active Directory domain.
You plan to create an emergency-access administrative account named Emergency1. Emergency1 will be assigned the Global administrator role in Azure AD. Emergency1 will be used in the event of Azure AD functionality failures and on-premises infrastructure failures.
You need to reduce the likelihood that Emergency1 will be prevented from signing in during an emergency.
What should you do?
- Configure Azure Monitor to generate an alert if Emergency1 is modified or signs in.
- Require Azure AD Privileged Identity Management (PIM) activation of the Global administrator role for Emergency1.
- Configure a conditional access policy to restrict sign-in locations for Emergency1 to only the corporate network.
- Configure a conditional access policy to require multi-factor authentication (MFA) for Emergency1.
-
You have an Azure Active Directory (Azure AD) tenant named contoso.com.
You implement entitlement management to provide resource access to users at a company named Fabrikam, Inc. Fabrikam uses a domain named fabrikam.com.
Fabrikam users must be removed automatically from the tenant when access is no longer required.
You need to configure the following settings:
– Block external user from signing in to this directory: No
– Remove external user: Yes
– Number of days before removing external user from this directory: 90What should you configure on the Identity Governance blade?
- Access packages
- Settings
- Terms of use
- Access reviews
-
You have an Azure Active Directory (Azure AD) tenant.
You need to review the Azure AD sign-in logs to investigate sign-ins that occurred in the past.
For how long does Azure AD store events in the sign-in logs?
- 14 days
- 30 days
- 90 days
- 365 days
-
You have an Azure subscription that contains the resources shown in the following table.
SC-300 Microsoft Identity and Access Administrator Part 04 Q17 076 For which resources can you create an access review?
- Group1, Role1, and Contributor only
- Group1 only
- Group1, App1, Contributor, and Role1
- Role1 and Contributor only
Explanation:Access reviews require an Azure AD Premium P2 license.
Access reviews for Group1 and App1 can be configured in Azure AD Access Reviews.
Access reviews for the Contributor role and Role1 would need to be configured in Privileged Identity Management (PIM). PIM is included in Azure AD Premium P2.
-
You have an Azure Active Directory (Azure AD) tenant that uses conditional access policies.
You plan to use third-party security information and event management (SIEM) to analyze conditional access usage.
You need to download the Azure AD log by using the administrative portal. The log file must contain changes to conditional access policies.
What should you export from Azure AD?
- audit logs in CSV format
- sign-ins in CSV format
- audit logs in JSON format
- sign-ins in JSON format
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
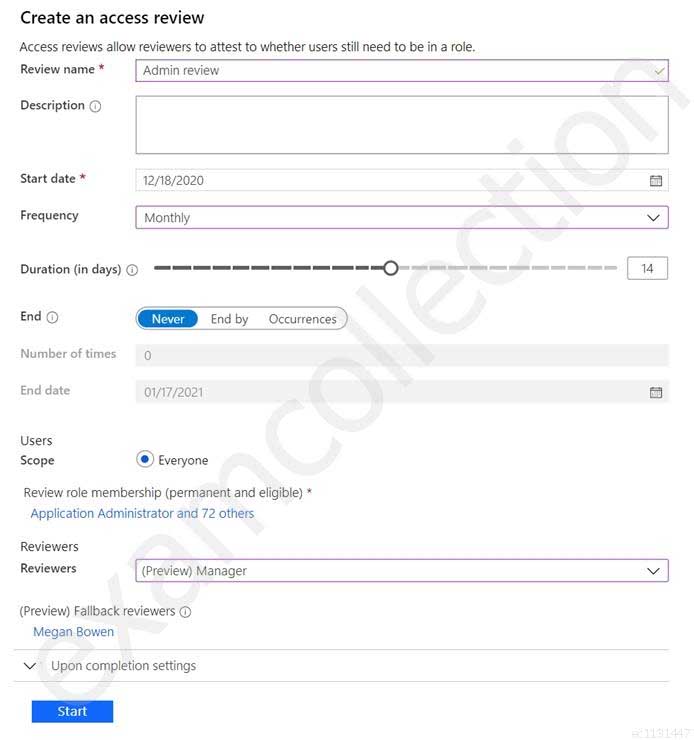
You have a Microsoft 365 tenant.
You have 100 IT administrators who are organized into 10 departments.
You create the access review shown in the exhibit. (Click the Exhibit tab.)
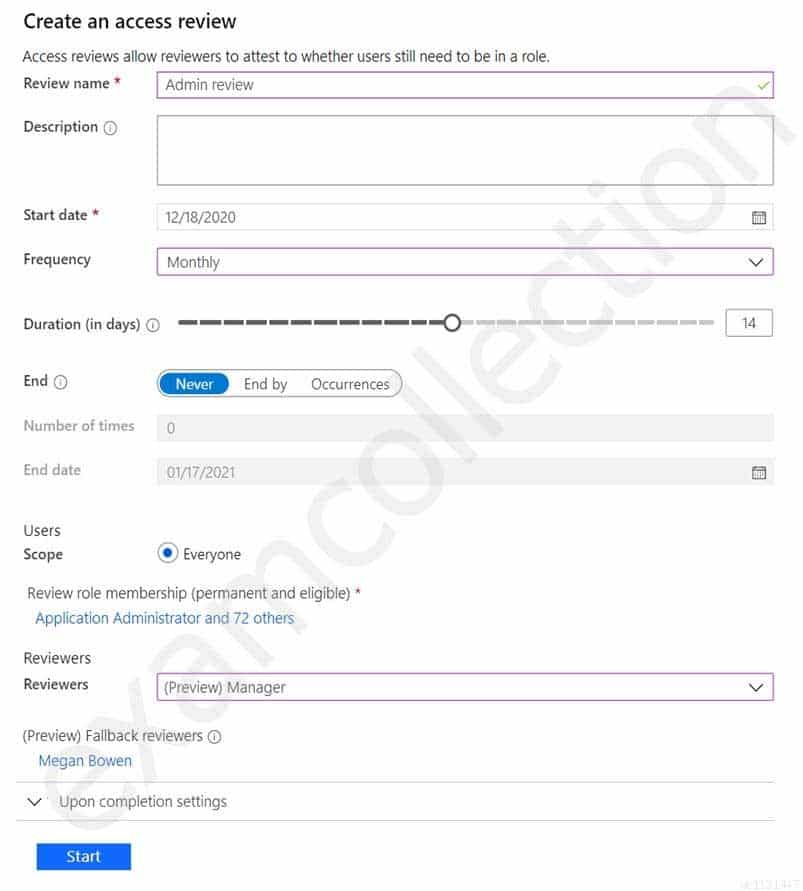
SC-300 Microsoft Identity and Access Administrator Part 04 Q19 077 You discover that all access review requests are received by Megan Bowen.
You need to ensure that the manager of each department receives the access reviews of their respective department.
Solution: You add each manager as a fallback reviewer.
Does this meet the goal?
- Yes
- No
-
You have an Azure Active Directory (Azure AD) tenant that contains the objects shown in the following table.
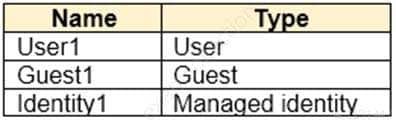
SC-300 Microsoft Identity and Access Administrator Part 04 Q20 078 Which objects can you add as eligible in Azure AD Privileged Identity Management (PIM) for an Azure AD role?
- User1, Guest1, and Identity1
- User1 and Guest1 only
- User1 only
- User1 and Identity1 only
-
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains the following group:
– Name: Group1
– Members: User1, User2
– Owner: User3On January 15, 2021, you create an access review as shown in the exhibit. (Click the Exhibit tab.)
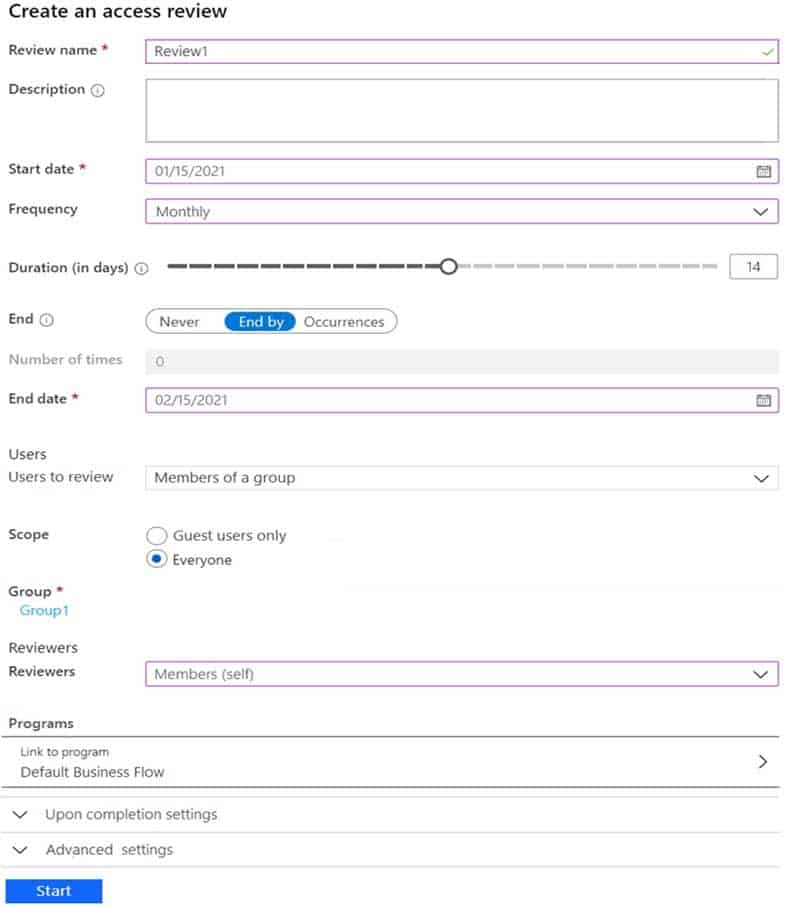
SC-300 Microsoft Identity and Access Administrator Part 04 Q21 079 Users answer the Review1 question as shown in the following table.
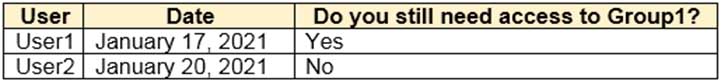
SC-300 Microsoft Identity and Access Administrator Part 04 Q21 080 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
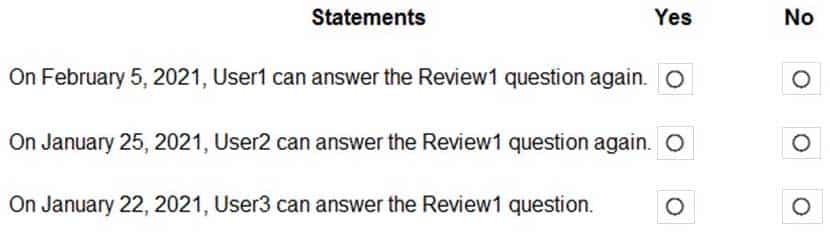
SC-300 Microsoft Identity and Access Administrator Part 04 Q21 081 Question 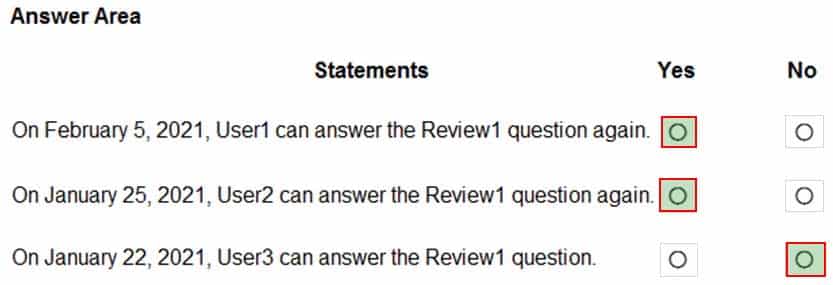
SC-300 Microsoft Identity and Access Administrator Part 04 Q21 081 Answer -
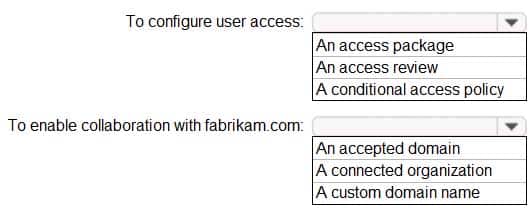
HOTSPOT
Your company has an Azure Active Directory (Azure AD) tenant named contoso.com. The company has a business partner named Fabrikam, Inc.
Fabrikam uses Azure AD and has two verified domain names of fabrikam.com and litwareinc.com. Both domain names are used for Fabrikam email addresses.
You plan to create an access package named package1 that will be accessible only to the users at Fabrikam.
You create a connected organization for Fabrikam.
You need to ensure that the package1 will be accessible only to users who have fabrikam.com email addresses.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
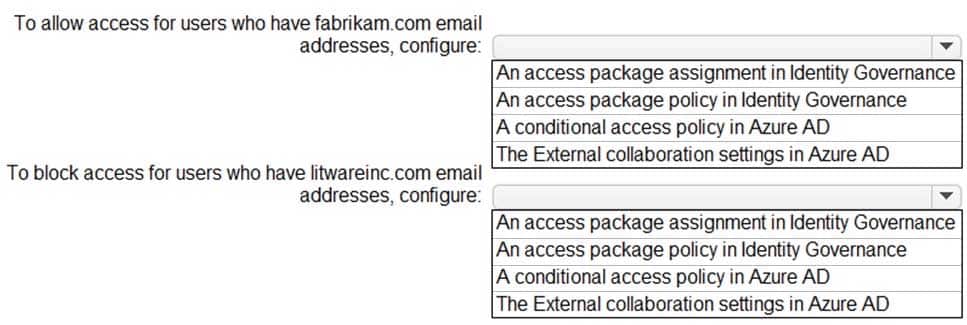
SC-300 Microsoft Identity and Access Administrator Part 04 Q22 082 Question 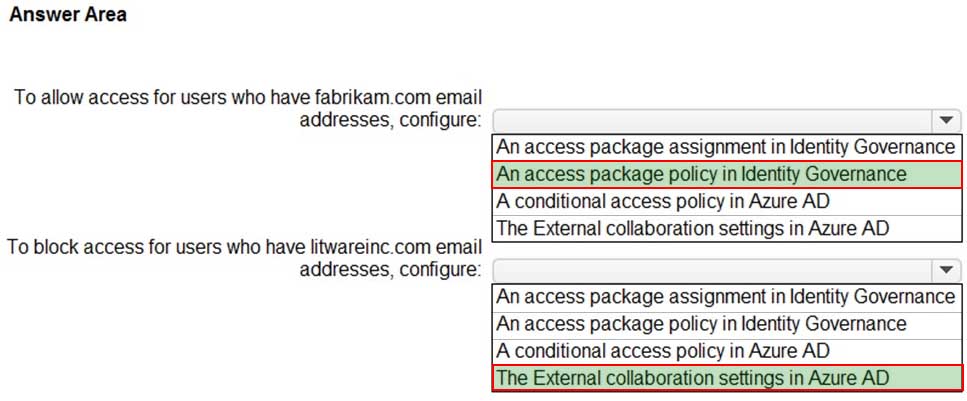
SC-300 Microsoft Identity and Access Administrator Part 04 Q22 082 Answer -
You have an Azure Active Directory (Azure AD) tenant named contoso.com that has Azure AD Identity Protection policies enforced.
You create an Azure Sentinel instance and configure the Azure Active Directory connector.
You need to ensure that Azure Sentinel can generate incidents based on the risk alerts raised by Azure AD Identity Protection.
What should you do first?
- Add an Azure Sentinel data connector.
- Configure the Notify settings in Azure AD Identity Protection.
- Create an Azure Sentinel playbook.
- Modify the Diagnostics settings in Azure AD.