PCNSE : Palo Alto Networks Certified Network Security Engineer : Part 02
-
What are two benefits of nested device groups in Panorama? (Choose two.)
- Reuse of the existing Security policy rules and objects
- Requires configuring both function and location for every device
- All device groups inherit settings from the Shared group
- Overwrites local firewall configuration
-
Which Captive Portal mode must be configured to support MFA authentication?
- NTLM
- Redirect
- Single Sign-On
- Transparent
Explanation:
Reference:
https://www.paloaltonetworks.com/documentation/80/pan-os/pan-os/authentication/configure-multi-factor-authentication
-
An administrator needs to implement an NGFW between their DMZ and Core network. EIGRP Routing between the two environments is required.
Which interface type would support this business requirement?
- Virtual Wire interfaces to permit EIGRP routing to remain between the Core and DMZ
- Layer 3 or Aggregate Ethernet interfaces, but configuring EIGRP on subinterfaces only
- Tunnel interfaces to terminate EIGRP routing on an IPsec tunnel (with the GlobalProtect License to support LSVPN and EIGRP protocols)
- Layer 3 interfaces, but configuring EIGRP on the attached virtual router
-
A speed/duplex negotiation mismatch is between the Palo Alto Networks management port and the switch port to which it connects.
How would an administrator configure the interface to 1Gbps?
- set deviceconfig interface speed-duplex 1Gbps-full-duplex
- set deviceconfig system speed-duplex 1Gbps-duplex
- set deviceconfig system speed-duplex 1Gbps-full-duplex
- set deviceconfig Interface speed-duplex 1Gbps-half-duplex
Explanation:Reference:https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Change-the-Speed-and-Duplex-of-the-Management-Port/ta-p/59034 -
A web server is hosted in the DMZ, and the server is configured to listen for incoming connections only on TCP port 8080. A Security policy rule allowing access from the Trust zone to the DMZ zone need to be configured to enable we browsing access to the server.
Which application and service need to be configured to allow only cleartext web-browsing traffic to thins server on tcp/8080?
- application: web-browsing; service: application-default
- application: web-browsing; service: service-https
- application: ssl; service: any
- application: web-browsing; service: (custom with destination TCP port 8080)
-
If the firewall has the following link monitoring configuration, what will cause a failover?
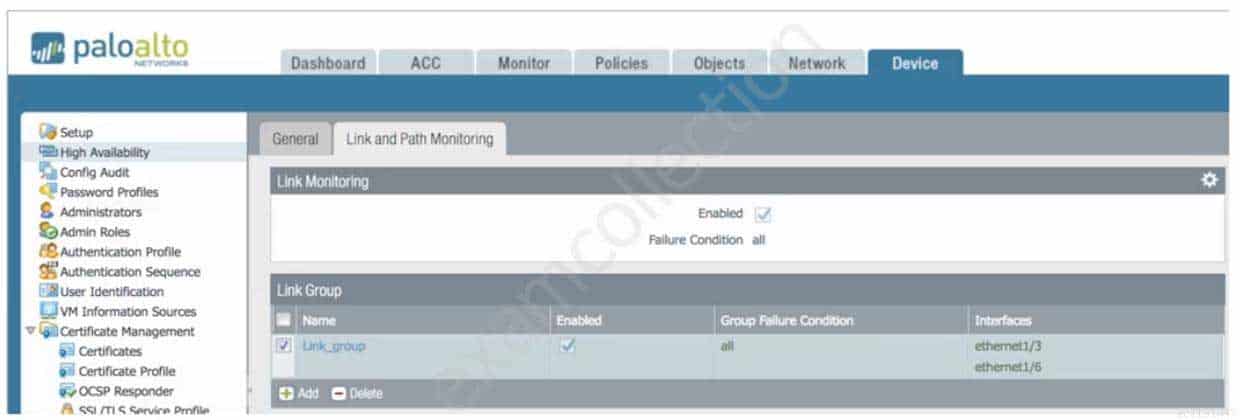
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q06 006 - ethernet1/3 and ethernet1/6 going down
- ethernet1/3 going down
- ethernet1/3 or ethernet1/6 going down
- ethernet1/6 going down
-
In the image, what caused the commit warning?
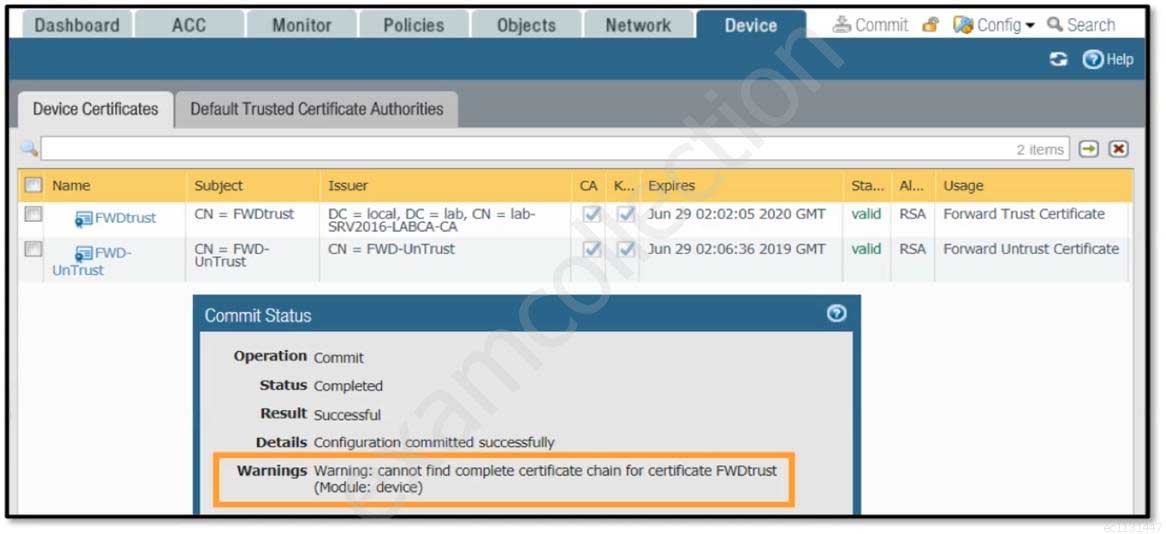
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q07 007 - The CA certificate for FWDtrust has not been imported into the firewall.
- The FWDtrust certificate has not been flagged as Trusted Root CA.
- SSL Forward Proxy requires a public certificate to be imported into the firewall.
- The FWDtrust certificate does not have a certificate chain.
-
Which method does an administrator use to integrate all non-native MFA platforms in PAN-OS® software?
- Okta
- DUO
- RADIUS
- PingID
-
How would an administrator monitor/capture traffic on the management interface of the Palo Alto Networks NGFW?
- Use the debug dataplane packet-diag set capture stage firewall file command.
- Enable all four stages of traffic capture (TX, RX, DROP, Firewall).
- Use the debug dataplane packet-diag set capture stage management file command.
- Use the tcpdump command.
Explanation:Reference:https://live.paloaltonetworks.com/t5/Learning-Articles/How-to-Run-a-Packet-Capture/ta-p/62390 -
An administrator needs to optimize traffic to prefer business-critical applications over non-critical applications.
QoS natively integrates with which feature to provide service quality?
- Port Inspection
- Certificate revocation
- Content-ID
- App-ID
Explanation:Reference:https://www.paloaltonetworks.com/documentation/80/pan-os/pan-os/quality-of-service/qos-concepts/qos-for-applications-and-users#idaed4e749-80b4-4641-a37c-c741aba562e9 -
A session in the Traffic log is reporting the application as “incomplete.”
What does “incomplete” mean?
- The three-way TCP handshake was observed, but the application could not be identified.
- The three-way TCP handshake did not complete.
- The traffic is coming across UDP, and the application could not be identified.
- Data was received but was instantly discarded because of a Deny policy was applied before App-ID could be applied.
-
Refer to the exhibit.
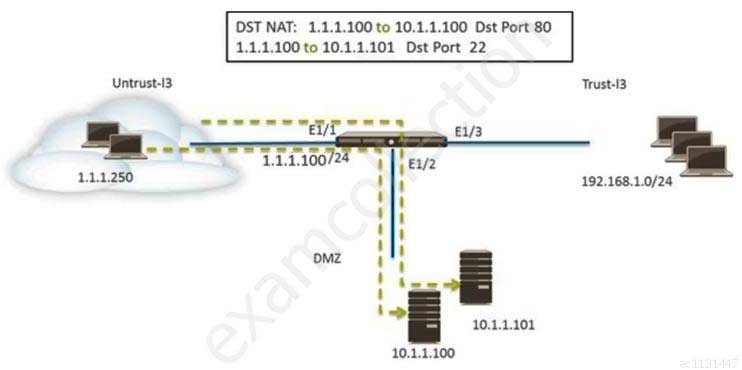
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q12 008 An administrator is using DNAT to map two servers to a single public IP address. Traffic will be steered to the specific server based on the application, where Host A (10.1.1.100) receives HTTP traffic and Host B (10.1.1.101) receives SSH traffic.
Which two Security policy rules will accomplish this configuration? (Choose two.)
- Untrust (Any) to Untrust (10.1.1.1), web-browsing – Allow
- Untrust (Any) to Untrust (10.1.1.1), ssh – Allow
- Untrust (Any) to DMZ (1.1.1.100), web-browsing – Allow
- Untrust (Any) to DMZ (1.1.1.100), ssh – Allow
-
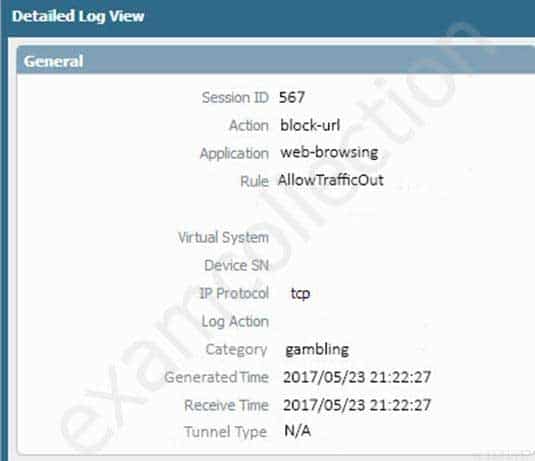
An administrator needs to determine why users on the trust zone cannot reach certain websites. The only information available is shown on the following image.
Which configuration change should the administrator make?
-
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q13 009 -
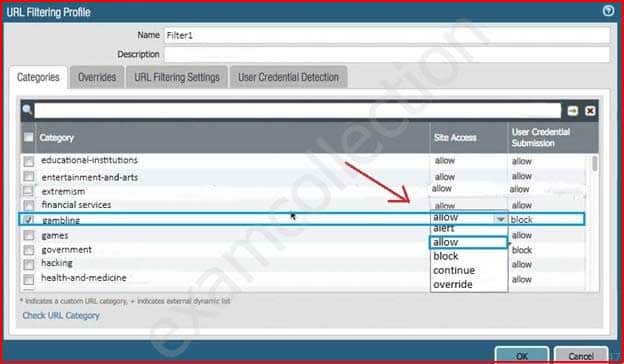
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q13 010 -

PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q13 011 -
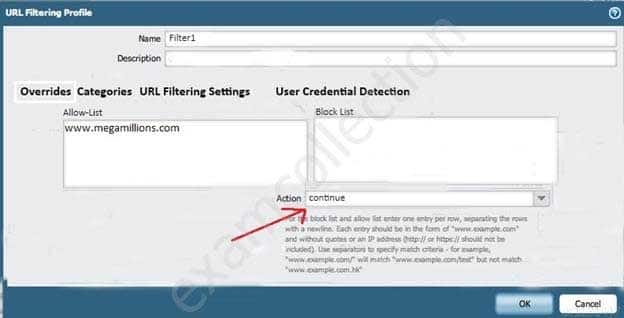
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q13 012 -
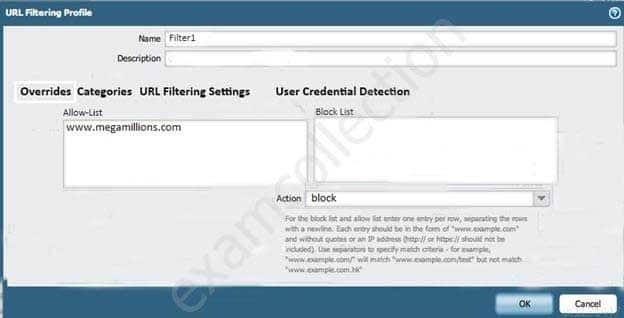
PCNSE Palo Alto Networks Certified Network Security Engineer Part 02 Q13 013
-
-
Which three settings are defined within the Templates object of Panorama? (Choose three.)
- Setup
- Virtual Routers
- Interfaces
- Security
- Application Override
-
A customer has an application that is being identified as unknown-tcp for one of their custom PostgreSQL database connections.
Which two configuration options can be used to correctly categorize their custom database application? (Choose two.)
- Application Override policy.
- Security policy to identify the custom application.
- Custom application.
- Custom Service object.
Explanation:Reference:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clc6CAC -
An administrator logs in to the Palo Alto Networks NGFW and reports that the WebUI is missing the Policies tab.
Which profile is the cause of the missing Policies tab?
- Admin Role
- WebUI
- Authentication
- Authorization
-
An administrator has left a firewall to use the default port for all management services.
Which three functions are performed by the dataplane? (Choose three.)
- WildFire updates
- NAT
- NTP
- antivirus
- file blocking
-
An administrator is using Panorama and multiple Palo Alto Networks NGFWs. After upgrading all devices to the latest PAN-OS® software, the administrator enables log forwarding from the firewalls to Panorama. Pre-existing logs from the firewalls are not appearing in Panorama.
Which action would enable the firewalls to send their pre-existing logs to Panorama?
- Use the import option to pull logs into Panorama.
- A CLI command will forward the pre-existing logs to Panorama.
- Use the ACC to consolidate pre-existing logs.
- The log database will need to exported form the firewalls and manually imported into Panorama.
-
A firewall just submitted a file to WildFire for analysis. Assume a 5-minute window for analysis. The firewall is configured to check for verdicts every 5 minutes.
How quickly will the firewall receive back a verdict?
- More than 15 minutes
- 5 minutes
- 10 to 15 minutes
- 5 to 10 minutes
-
What are the differences between using a service versus using an application for Security Policy match?
- Use of a “service” enables the firewall to take immediate action with the first observed packet based on port numbers. Use of an “application” allows the firewall to take immediate action if the port being used is a member of the application standard port list.
- There are no differences between “service” or “application”. Use of an “application” simplifies configuration by allowing use of a friendly application name instead of port numbers.
- Use of a “service” enables the firewall to take immediate action with the first observed packet based on port numbers. Use of an “application” allows the firewall to take action after enough packets allow for App-ID identification regardless of the ports being used
- Use of a “service” enables the firewall to take action after enough packets allow for App-ID identification
Subscribe
0 Comments
Newest