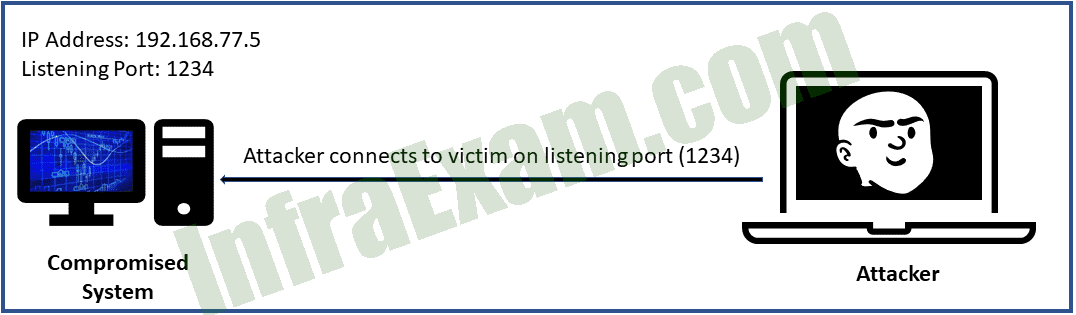
Refer to the exhibit. An attacker opens a port or a listener on the compromised system and waits for a connection. The goal is to connect to the victim from any system, execute commands, and further manipulate the victim. What type of malicious activity is being performed?
- reverse shell
- horizontal privilege escalation
- bind shell
- vertical privilege escalation
|
Explanation & Hint: With a bind shell, an attacker opens a port or a listener on the compromised system and waits for a connection. This is done to connect to the victim from any system, execute commands, and further manipulate the victim. In this case, the attacker opens port 1234 on the compromised system with an IP address 192.168.77.5. |