MD-100 : Windows 10 : Part 04
-
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.Overview
General Overview
Litware, Inc. is a consulting company that has a main office in Montreal and branch offices in Seattle and New York.
Environment
Existing Environment
The network contains an on-premises Active Directory domain named litware.com. The domain contains the computers shown in the following table.
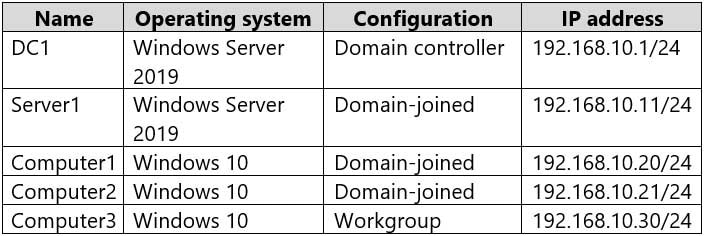
MD-100 Windows 10 Part 04 Q01 048 The network that uses 192.168.10.0/24 connects to the internet by using a Network Address Translation (NAT) device.
Windows Admin Center is installed on Server1.
The domain contains the groups shown in the following table.

MD-100 Windows 10 Part 04 Q01 049 The domain contains the users shown in the following table.

MD-100 Windows 10 Part 04 Q01 050 Computer1 Configuration
Computer1 contains the local user accounts shown in the following table.

MD-100 Windows 10 Part 04 Q01 051 Computer1 contains a folder named D:\Folder1 that has permission inheritance disabled.
Computer1 contains a file named D:\Folder1\Report.docx that has the permissions shown in the following table.
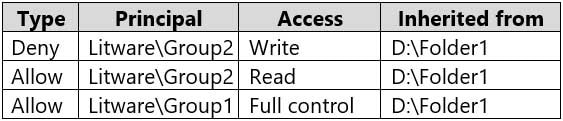
MD-100 Windows 10 Part 04 Q01 052 D:\Folder1\Report.docx has auditing configured as shown in the following table.
MD-100 Windows 10 Part 04 Q01 053 The Local Computer Policy for Computer1 is configured as shown in the following table.

MD-100 Windows 10 Part 04 Q01 054 Windows Defender Firewall for Computer1 has the rules shown in the following table.
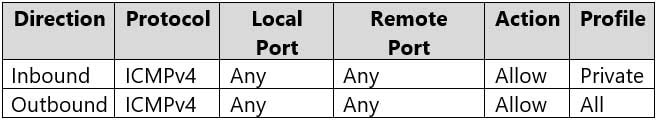
MD-100 Windows 10 Part 04 Q01 055 Computer2 Configuration
Computer2 contains the local user accounts shown in the following table.
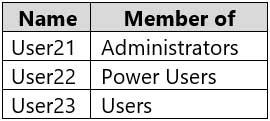
MD-100 Windows 10 Part 04 Q01 056 Group1 and Group2 are members of the Remote Desktop Users group.
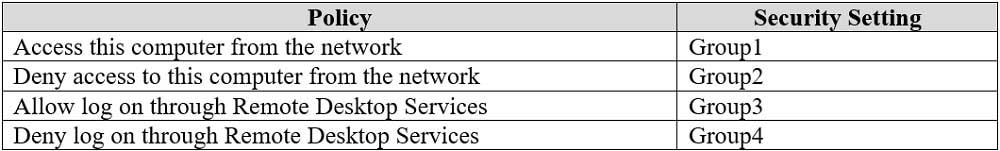
The Local Computer Policy for Computer2 is configured as shown in the following table.

MD-100 Windows 10 Part 04 Q01 057 Windows Defender Firewall for Computer2 has the rules shown in the following table.
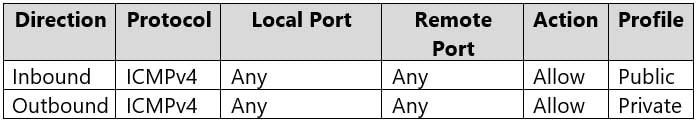
MD-100 Windows 10 Part 04 Q01 058 Computer3 Configuration
Computer3 contains the local user accounts shown in the following table.
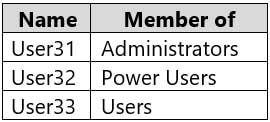
MD-100 Windows 10 Part 04 Q01 059 Windows Defender Firewall for Computer3 has the rules shown in the following table.

MD-100 Windows 10 Part 04 Q01 060 Requirements and Planned Changes
Planned Changes
Litware plans to make the following changes on Computer1:
– Grant User1 Allow Full control permissions to D:\Folder1\Report.docx.
– Grant User2 Allow Full control permissions to D:\Folder1\Report.docx.
– Grant User3 Allow Full control permissions to D:\Folder1.Technical Requirements
Litware identifies the following technical requirements:
– Configure custom Visual Effect performance settings for Computer1.
– Manage Computer2 by using Windows Admin Center.
– Minimize administrative effort.Delivery Optimization on the computers that run Windows 10 must be configured to meet the following requirements:
– Content must be downloaded only from an original source.
– Downloading content from peer cache clients must be prevented.
– Downloads must be optimized by using the Delivery Optimization cloud service.-
On Computer1, you need to configure the custom Visual Effects performance settings.
Which user accounts can you use?
- Admin1, User11, and User13 only
- Admin1 only
- Admin1, User11, User12, and User13
- Admin1, User11, and User12 only
- Admin1 and User 11 only
-
Which users can sign in to Computer2 by using Remote Desktop?
- User2 only
- Admin1 only
- User1 only
- Admin1 and User2 only
- Admin1, User1, User2, and User3
-
-
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam times as you would like to complete each case. However, there may be additional studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.Overview
Fabrikam, Inc. is a distribution company that has 500 employees and 100 contractors.
Existing Environment
Active Directory
The network contains an Active Directory forest named fabrikam.com. The forest is synced to Microsoft Azure Active Directory (Azure AD). All the employees are assigned Microsoft 365 E3 licenses.
The domain contains a user account for an employee named User10.
Client Computers
All the employees have computers that run Windows 10 Enterprise. All the computers are installed without Volume License Keys. Windows 10 license keys are never issued.
All the employees register their computer to Azure AD when they first receive the computer.
User10 has a computer named Computer10.
All the contractors have their own computer that runs Windows 10. None of the computers are joined to Azure AD.
Operational Procedures
Fabrikam has the following operational procedures:
Updates are deployed by using Windows Update for Business.
When new contractors are hired, administrators must help the contactors configure the following settings on their computer:
– User certificates
– Browser security and proxy settings
– Wireless network connection settingsSecurity Policies
The following security policies are enforced on all the client computers in the domain:
– All the computers are encrypted by using BitLocker Drive Encryption (BitLocker). BitLocker recovery information is stored in Active Directory and Azure AD.
– The local Administrators group on each computer contains an enabled account named LocalAdmin.
– The LocalAdmin account is managed by using Local Administrator Password Solution (LAPS).Problem Statements
Fabrikam identifies the following issues:
– Employees in the finance department use an application named Application1. Application1 frequently crashes due to a memory error. When Application1 crashes, an event is written to the application log and an administrator runs a script to delete the temporary files and restart the application.
– When employees attempt to connect to the network from their home computer, they often cannot establish a VPN connection because of misconfigured VPN settings.
– An employee has a computer named Computer11. Computer11 has a hardware failure that prevents the computer from connecting to the network.
– User10 reports that Computer10 is not activated.Technical Requirements
Fabrikam identifies the following technical requirements for managing the client computers:
– Provide employees with a configuration file to configure their VPN connection.
– Use the minimum amount of administrative effort to implement the technical requirements.
– Identify which employees’ computers are noncompliant with the Windows Update baseline of the company.
– Ensure that the service desk uses Quick Assist to take remote control of an employee’s desktop during support calls.
– Automate the configuration of the contractors’ computers. The solution must provide a configuration file that the contractors can open from a Microsoft SharePoint site to apply the required configurations.-
You need to sign in as LocalAdmin on Computer11.
What should you do first?
- From the LAPS UI tool, view the administrator account password for the computer object of Computer11.
- From Windows Configuration Designer, create a configuration package that sets the password of the LocalAdmin account on Computer11.
- Use a Group Policy object (GPO) to set the local administrator password.
- From Microsoft Intune, set the password of the LocalAdmin account on Computer11.
-
An employee reports that she must perform a BitLocker recovery on her laptop. The employee does not have her BitLocker recovery key but does have a Windows 10 desktop computer.
What should you instruct the employee to do from the desktop computer?
- Run the manage-bde.exe –status command
- From BitLocker Recovery Password Viewer, view the computer object of the laptop
- Go to https://aad.portal.azure.com and view the object of the laptop
- Run the Enable-BitLocker Auto Unlock cmdlet
Explanation:
The BitLocker recovery key is stored in Azure Active Directory.
-
-
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and two branch offices in Seattle and New York.
Contoso has IT, human resources (HR), and finance departments.
Contoso recently opened a new branch office in San Diego. All the users in the San Diego office work from home.
Existing environment
Contoso uses Microsoft 365.
The on-premises network contains an Active Directory domain named contoso.com. The domain is synced to Microsoft Azure Active Directory (Azure AD).
All computers run Windows 10 Enterprise.
You have four computers named Computer1, Computer2, Computer3, and ComputerA. ComputerA is in a workgroup on an isolated network segment and runs the Long Term Servicing Channel version of Windows 10. ComputerA connects to a manufacturing system and is business critical. All the other computers are joined to the domain and run the Semi-Annual Channel version of Windows 10.
In the domain, you create four groups named Group1, Group2, Group3, and Group4.
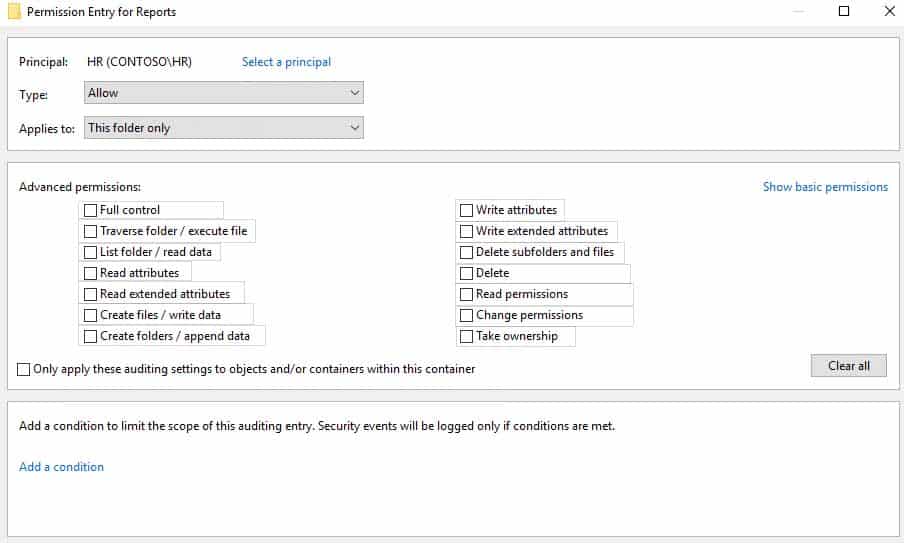
Computer2 has the local Group Policy settings shown in the following table.
MD-100 Windows 10 Part 04 Q03 061 The computers are updated by using Windows Update for Business.
The domain has the users shown in the following table.
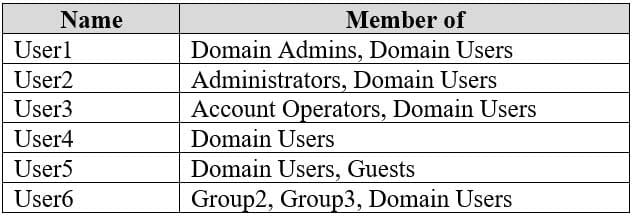
MD-100 Windows 10 Part 04 Q03 062 Computer1 has the local users shown in the following table.
MD-100 Windows 10 Part 04 Q03 063 Requirements
Planned Changes
Contoso plans to purchase computers preinstalled with Windows 10 Pro for all the San Diego office users.
Technical requirements
Contoso identifies the following technical requirements:
– The computers in the San Diego office must be upgraded automatically to Windows 10 Enterprise and must be joined to Azure AD the first time a user starts each new computer. End users must not be required to accept the End User License Agreement (EULA).
– Helpdesk users must be able to troubleshoot Group Policy object (GPO) processing on the Windows 10 computers. The helpdesk users must be able to identify which Group Policies are applied to the computers.
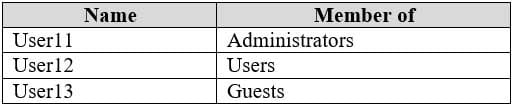
– Users in the HR department must be able to view the list of files in a folder named D:\Reports on Computer3.
– ComputerA must be configured to have an Encrypting File System (EFS) recovery agent.
– Quality update installations must be deferred as long as possible on ComputerA.
– Users in the IT department must use dynamic lock on their primary device.
– User6 must be able to connect to Computer2 by using Remote Desktop.
– The principle of least privilege must be used whenever possible.
– Administrative effort must be minimized whenever possible.
– Kiosk (assigned access) must be configured on Computer1.-
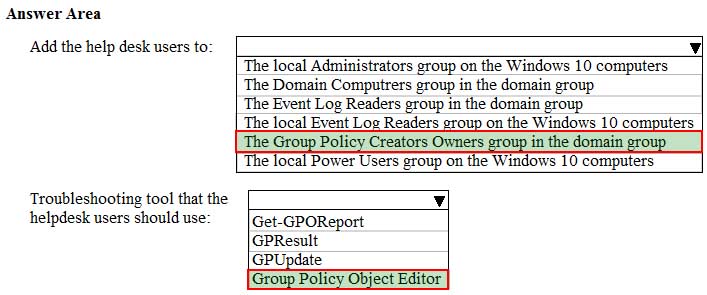
HOTSPOT
You need to meet the technical requirements for the helpdesk users.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

MD-100 Windows 10 Part 04 Q03 064 Question -
HOTSPOT
You need to meet the technical requirements for the HR department users.
Which permissions should you assign to the HR department users for the D:\Reports folder? To answer, select the appropriate permissions in the answer area.
NOTE: Each correct selection is worth one point.
MD-100 Windows 10 Part 04 Q03 065 Question -
You need to meet the technical requirements for EFS on ComputerA.
What should you do?
- Run certutil.exe, and then add a certificate to the local computer certificate store.
- Run cipher.exe, and then add a certificate to the local computer certificate store.
- Run cipher.exe, and then add a certificate to the local Group Policy.
- Run certutil.exe, and then add a certificate to the local Group Policy.
-
-
You have a computer named Computer1 that runs Windows 10.
You need to configure User Account Control (UAC) to prompt administrators for their credentials.
Which settings should you modify?
- Administrators Properties in Local Users and Groups
- User Account Control Settings in Control Panel
- Security Options in Local Group Policy Editor
- User Rights Assignment in Local Group Policy Editor
-
You have several computers that run Windows 10. The computers are in a workgroup.
You need to prevent users from using Microsoft Store apps on their computer.
What are two possible ways to achieve the goal? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
- From Security Settings in the local Group Policy, configure Security Options.
- From Administrative Templates in the local Group Policy, configure the Store settings.
- From Security Settings in the local Group Policy, configure Software Restriction Policies.
- From Security Settings in the local Group Policy, configure Application Control Policies.
-
You have a computer named Computer1 that runs Windows 10.
You need to prevent standard users from changing the wireless network settings on Computer1. The solution must allow administrators to modify the wireless network settings.
What should you use?
- Windows Configuration Designer
- MSConfig
- Local Group Policy Editor
- an MMC console that has the Group Policy Object Editor snap-in
-
HOTSPOT
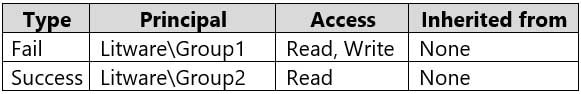
You have three computers that run Windows 10 as shown in the following table.
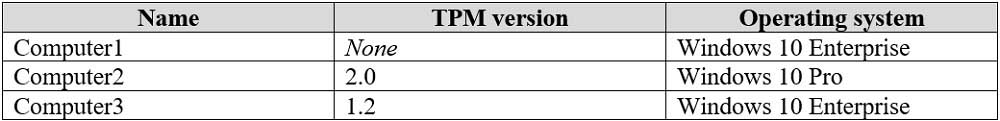
MD-100 Windows 10 Part 04 Q07 067 All the computers have C and D volumes. The Require additional authentication at startup Group Policy settings is disabled on all the computers.
Which volumes can you encrypt by using BitLocker Drive Encryption (BitLocker)? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

MD-100 Windows 10 Part 04 Q07 068 Question -
Your network contains an Active Directory domain named contoso.com. The domain contains a computer named Computer1 that runs Windows 10.
On Computer1, you create a folder and assign Full control permissions to Everyone.
You share the folder as Share1 and assign the permissions shown in the following table.

MD-100 Windows 10 Part 04 Q08 069 When accessing Share1, which two actions can be performed by User1 but not by User2? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- Delete a file created by another user.
- Set the permissions for a file.
- Rename a file created by another user.
- Take ownership of file.
- Copy a file created by another user to a subfolder.
-
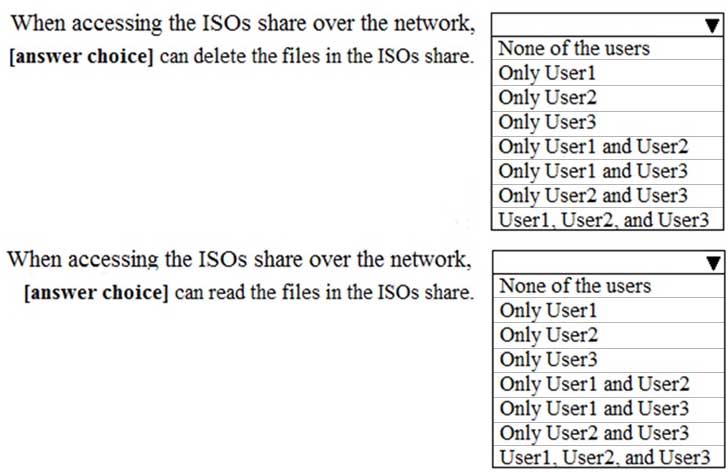
HOTSPOT
You have a computer that runs Windows 10. The computer contains a folder named C:\ISOs that is shared as ISOs.
You run several commands on the computer as shown in the following exhibit.
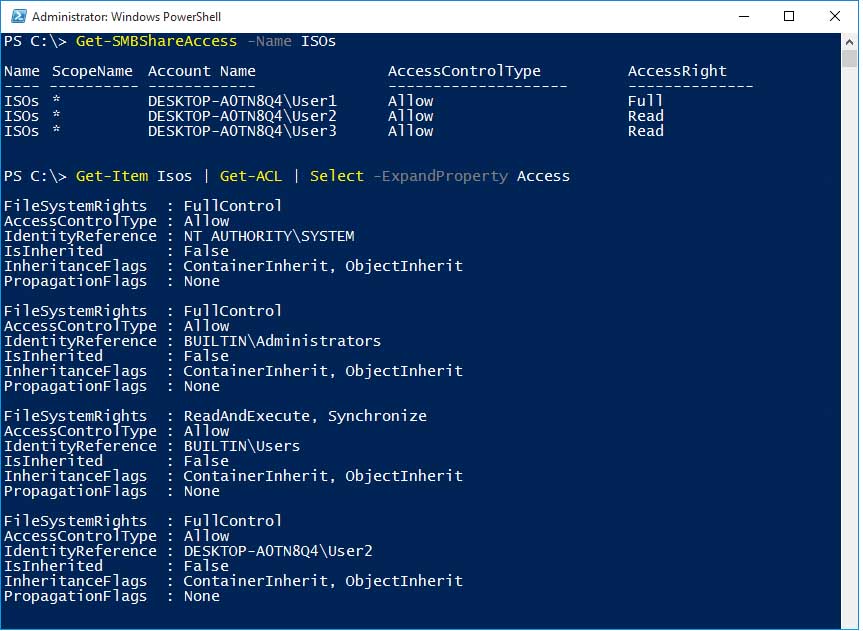
MD-100 Windows 10 Part 04 Q09 070 Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
MD-100 Windows 10 Part 04 Q09 071 Question 
MD-100 Windows 10 Part 04 Q09 071 Answer Explanation:
When you are using share and NTFS permissions together, the most restrictive permission is applied. -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
A user named User1 has a computer named Computer1 that runs Windows 10. Computer1 is joined to an Azure Active Directory (Azure AD) tenant named contoso.com. User1 joins Computer1 to contoso.com by using [email protected].
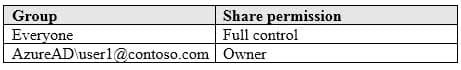
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission shown in the following table.

MD-100 Windows 10 Part 04 Q10 072 A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected].
User2 attempts to access Share1 and receives the following error message: “The username or password is incorrect.”
You need to ensure that User2 can connect to Share1.
Solution: In Azure AD, you create a group named Group1 that contains User1 and User2. You grant Group1 Change access to Share1.
Does this meet the goal?
- Yes
- No
Explanation:
Azure AD cannot be used to control Share permissions on on-premisses computer folders. -
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
A user named User1 has a computer named Computer1 that runs Windows 10. Computer1 is joined to an Azure Active Directory (Azure AD) tenant named contoso.com. User1 joins Computer1 to contoso.com by using [email protected].
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission shown in the following table.
MD-100 Windows 10 Part 04 Q11 073 A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected].
User2 attempts to access Share1 and receives the following error message: “The username or password is incorrect.”
You need to ensure that User2 can connect to Share1.
Solution: You create a local user account on Computer1 and instruct User2 to use the local account to connect to Share1.
Does this meet the goal?
- Yes
- No
-
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
A user named User1 has a computer named Computer1 that runs Windows 10. Computer1 is joined to an Azure Active Directory (Azure AD) tenant named contoso.com. User1 joins Computer1 to contoso.com by using [email protected].
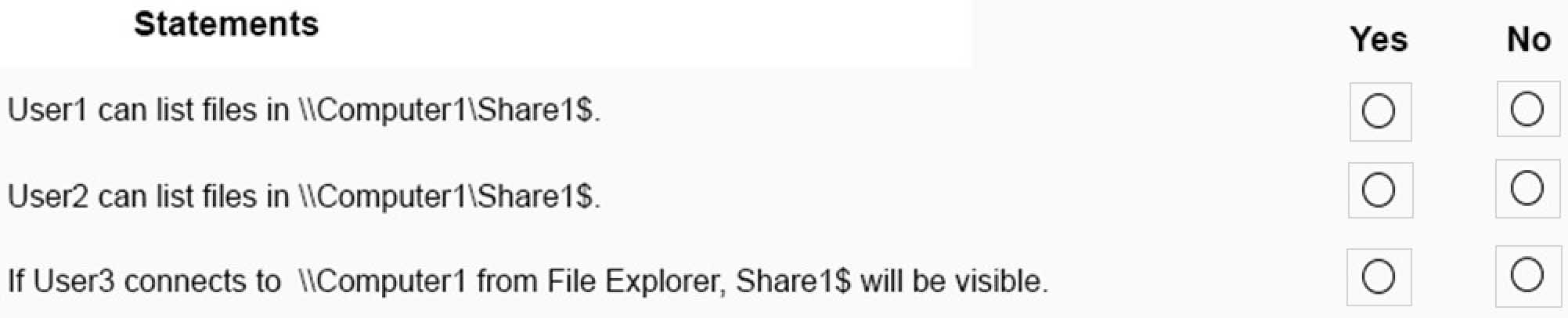
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission shown in the following table.

MD-100 Windows 10 Part 04 Q12 074 A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected].
User2 attempts to access Share1 and receives the following error message: “The username or password is incorrect.”
You need to ensure that User2 can connect to Share1.
Solution: In Azure AD, you create a group named Group1 that contains User1 and User2. You grant Group1 Modify access to Folder1.
Does this meet the goal?
- Yes
- No
-
You have a computer named Computer1 that runs Windows 10. Computer1 contains a folder named Folder1.
You need to log any users who take ownership of the files in Folder1.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- Modify the folder attributes of Folder1.
- Modify the Advanced Security Settings for Folder1.
- From a Group Policy object (GPO), configure the Audit Sensitive Privilege Use setting.
- From a Group Policy object (GPO), configure the Audit File System setting.
- Install the Remote Server Administration Tools (RSAT).
-
HOTSPOT
Your network contains an Active Directory domain. The domain contains the users shown in the following table.
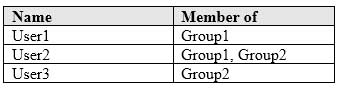
MD-100 Windows 10 Part 04 Q14 075 The domain contains a computer named Computer1 that runs Windows 10. Computer1 contains a folder named Folder1 that has the following permissions:
– User2: Deny Write
– Group1: Allow Read
– Group2: Allow ModifyFolder1 is shared as Share1$. Share1$ has the following configurations:
– Everyone: Allow Full control
– Access-based enumeration: EnabledFor each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
MD-100 Windows 10 Part 04 Q14 076 Question 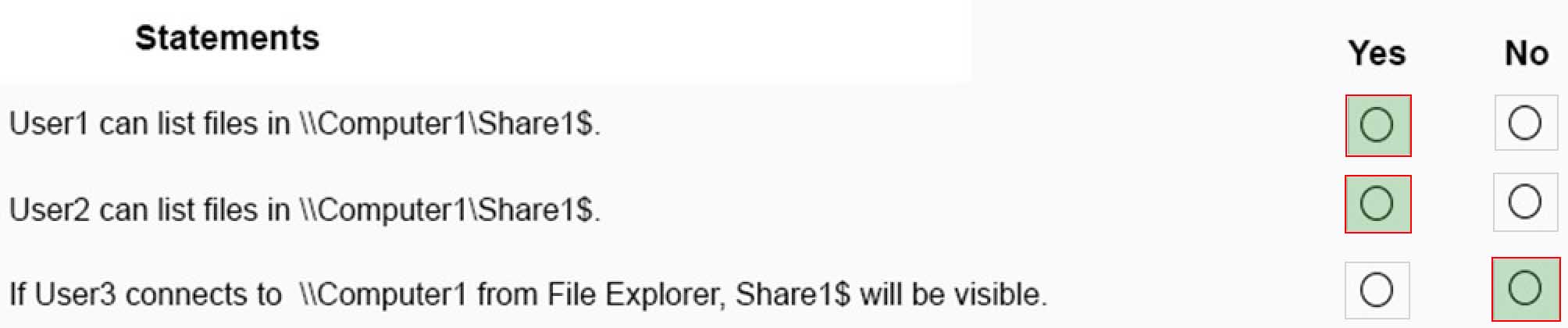
MD-100 Windows 10 Part 04 Q14 076 Answer Explanation:Box 1: Yes
Box 2: Yes
Box 3: No
Share1$ is a hidden share and is therefore not visible in File Explorer, even with access based enumeration enabled. -
You are a network administrator at your company.
The company uses an application that checks for network connectivity to a server by sending a ping request to the IPv6 address of the server. If the server replies, the application loads.
A user cannot open the application.
You manually send the ping request from the computer of the user and the server does not reply. You send the ping request from your computer and the server replies.
You need to ensure that the ping request works from the user’s computer.
Which Windows Defender firewall rule is a possible cause of the issue?
- File and Printer Sharing (NB-Datagram-In)
- File and Printer Sharing (Echo Request ICMPv6-Out)
- File and Printer Sharing (NB-Datagram-Out)
- File and Printer Sharing (Echo Request ICMPv6-In)
-
You have a workgroup computer that runs Windows 10.
You create a local user named User1.
User1 needs to be able to share and manage folders located in a folder named C:\Share by using the Shared Folders snap-in. The solution must use the principle of least privilege.
To which group should you add User1?
- Administrators
- Device Owners
- Users
- Power Users
-
HOTSPOT
You have a computer named Computer5 that runs Windows 10 that is used to share documents in a workgroup.
You create three users named User-a, User-b, and User-c by using Computer Management. The users plan to access Computer5 from the network only.
You have a folder named Data. The Advanced Security Settings for the Data folder are shown in the Security exhibit. (Click the Security tab).
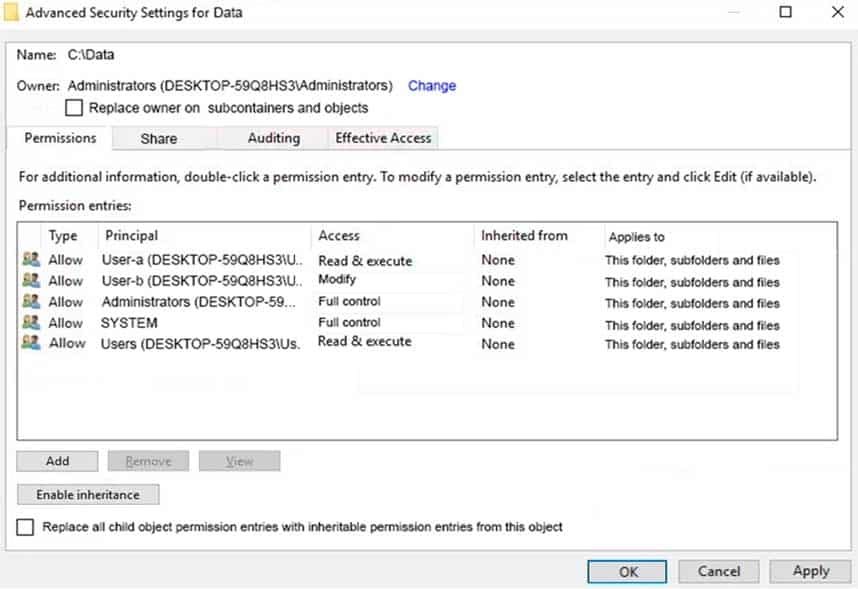
MD-100 Windows 10 Part 04 Q17 077 You share the Data folder. The permissions for User-a are shown in the User-a exhibit (Click the User-a tab.)

MD-100 Windows 10 Part 04 Q17 078 The permissions for User-b are shown in the User-b exhibit. (Click the User-b tab.)

MD-100 Windows 10 Part 04 Q17 079 The permissions for User-c are shown in the User-c exhibit. (Click the User-c tab.)

MD-100 Windows 10 Part 04 Q17 080 For each of the following statements, select Yes if the statements is true. Otherwise, select No.
NOTE: Reach correct selection is worth one point.
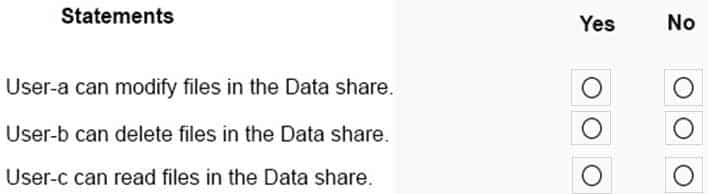
MD-100 Windows 10 Part 04 Q17 081 Question 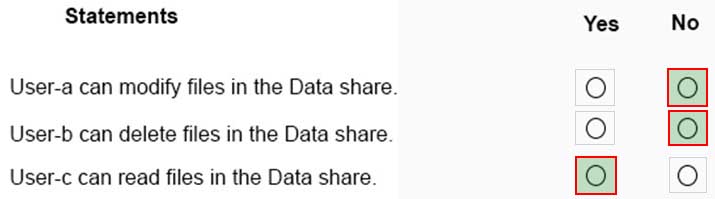
MD-100 Windows 10 Part 04 Q17 081 Answer Explanation:Box 1: No
User-a only has Read share permission so he cannot modify files in the Data share.Box 2: No
User-b only has Read share permission so he cannot delete files in the Data share.Box 3: Yes
User-c has Read and Change share permission so he can read files in the Data share. User-c does not have an entry in the Advanced Security Settings for the Data folder. However, User-c would be a member of the Users group by default and that group has Full Control permission to the folder. -
HOTSPOT
You have a computer that runs Windows 10 and contains the folders shown in the following table.
MD-100 Windows 10 Part 04 Q18 082 You create the groups shown in the following table.
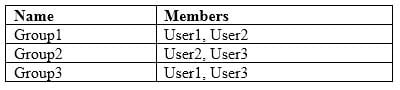
MD-100 Windows 10 Part 04 Q18 083 On FolderA, you disable permission inheritance and select the option to remove all inherited permissions. To each folder, you assign the NTFS permissions shown in the following table.
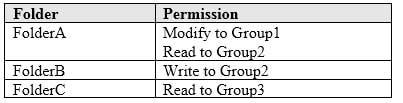
MD-100 Windows 10 Part 04 Q18 084 For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
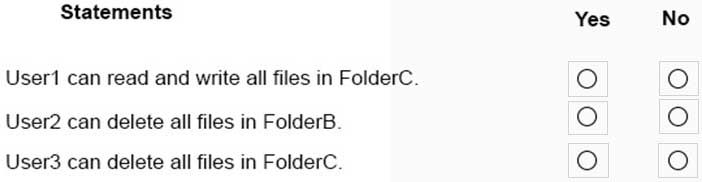
MD-100 Windows 10 Part 04 Q18 085 Question 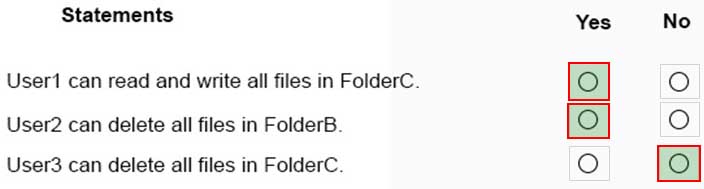
MD-100 Windows 10 Part 04 Q18 085 Answer Explanation:Inheritance was turned off for FolderA and to all inherited permissions have been removed. Therefore, permissions on FolderA do not filter down to FolderB and FolderC.
Box 1: Yes
Box 2: Yes
Box 3: No
-
Your network contains an Active Directory domain. The domain contains a computer named Computer1 that runs Windows 10.
You need to view the settings to Computer1 by Group Policy objects (GPOs) in the domain and local Group Policies.
Which command should you run?
- gpresult
- secedit
- gpupdate
- gpfixup
-
Your network contains an Active Directory domain. The domain contains computers that run Windows 10.
You need to provide a user with the ability to remotely create and modify shares on the computers. The solution must use the principle of least privilege.
To which group should you add the user?
- Power Users
- Remote Management Users
- Administrators
- Network Configuration Operators