SY0-601 : CompTIA Security+ 2021 : Part 03
-
A startup company is using multiple SaaS and IaaS platforms to stand up a corporate infrastructure and build out a customer-facing web application. Which of the following solutions would be BEST to provide security, manageability, and visibility into the platforms?
- SIEM
- DLP
- CASB
- SWG
-
A root cause analysis reveals that a web application outage was caused by one of the company’s developers uploading a newer version of the third-party libraries that were shared among several applications. Which of the following implementations would be BEST to prevent the issue from reoccurring?
- CASB
- SWG
- Containerization
- Automated failover
-
A security administrator suspects there may be unnecessary services running on a server. Which of the following tools will the administrator MOST likely use to confirm the suspicions?
- Nmap
- Wireshark
- Autopsy
- DNSEnum
-
A company has drafted an insider-threat policy that prohibits the use of external storage devices. Which of the following would BEST protect the company from data exfiltration via removable media?
- Monitoring large data transfer transactions in the firewall logs
- Developing mandatory training to educate employees about the removable media policy
- Implementing a group policy to block user access to system files
- Blocking removable-media devices and write capabilities using a host-based security tool
-
A network administrator has been alerted that web pages are experiencing long load times. After determining it is not a routing or DNS issue, the administrator logs in to the router, runs a command, and receives the following output:
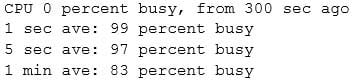
SY0-601 Part 03 Q05 010 Which of the following is the router experiencing?
- DDoS attack
- Memory leak
- Buffer overflow
- Resource exhaustion
-
A company provides mobile devices to its users to permit access to email and enterprise applications. The company recently started allowing users to select from several different vendors and device models. When configuring the MDM, which of the following is a key security implication of this heterogeneous device approach?
- The most common set of MDM configurations will become the effective set of enterprise mobile security controls.
- All devices will need to support SCEP-based enrollment; therefore, the heterogeneity of the chosen architecture may unnecessarily expose private keys to adversaries.
- Certain devices are inherently less secure than others, so compensatory controls will be needed to address the delta between device vendors.
- MDMs typically will not support heterogeneous deployment environments, so multiple MDMs will need to be installed and configured.
-
An organization with a low tolerance for user inconvenience wants to protect laptop hard drives against loss or data theft. Which of the following would be the MOST acceptable?
- SED
- HSM
- DLP
- TPM
-
A security analyst receives a SIEM alert that someone logged in to the appadmin test account, which is only used for the early detection of attacks. The security analyst then reviews the following application log:
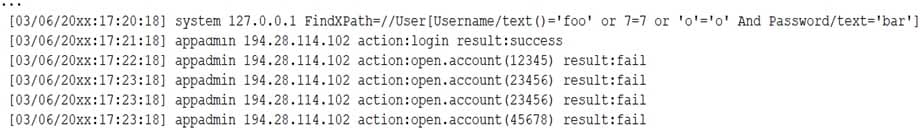
SY0-601 Part 03 Q08 011 Which of the following can the security analyst conclude?
- A replay attack is being conducted against the application.
- An injection attack is being conducted against a user authentication system.
- A service account password may have been changed, resulting in continuous failed logins within the application.
- A credentialed vulnerability scanner attack is testing several CVEs against the application.
-
In which of the following situations would it be BEST to use a detective control type for mitigation?
- A company implemented a network load balancer to ensure 99.999% availability of its web application.
- A company designed a backup solution to increase the chances of restoring services in case of a natural disaster.
- A company purchased an application-level firewall to isolate traffic between the accounting department and the information technology department.
- A company purchased an IPS system, but after reviewing the requirements, the appliance was supposed to monitor, not block, any traffic.
- A company purchased liability insurance for flood protection on all capital assets.
-
The IT department’s on-site developer has been with the team for many years. Each time an application is released, the security team is able to identify multiple vulnerabilities. Which of the following would BEST help the team ensure the application is ready to be released to production?
- Limit the use of third-party libraries.
- Prevent data exposure queries.
- Obfuscate the source code.
- Submit the application to QA before releasing it.
-
A cybersecurity analyst needs to implement secure authentication to third-party websites without users’ passwords. Which of the following would be the BEST way to achieve this objective?
- OAuth
- SSO
- SAML
- PAP
-
An analyst needs to identify the applications a user was running and the files that were open before the user’s computer was shut off by holding down the power button. Which of the following would MOST likely contain that information?
- NGFW
- Pagefile
- NetFlow
- RAM
-
A remote user recently took a two-week vacation abroad and brought along a corporate-owned laptop. Upon returning to work, the user has been unable to connect the laptop to the VPN. Which of the following is the MOST likely reason for the user’s inability to connect the laptop to the VPN?
- Due to foreign travel, the user’s laptop was isolated from the network.
- The user’s laptop was quarantined because it missed the latest path update.
- The VPN client was blacklisted.
- The user’s account was put on a legal hold.
-
In which of the following common use cases would steganography be employed?
- Obfuscation
- Integrity
- Non-repudiation
- Blockchain
-
To secure an application after a large data breach, an e-commerce site will be resetting all users’ credentials. Which of the following will BEST ensure the site’s users are not compromised after the reset?
- A password reuse policy
- Account lockout after three failed attempts
- Encrypted credentials in transit
- A geofencing policy based on login history
-
In which of the following risk management strategies would cybersecurity insurance be used?
- Transference
- Avoidance
- Acceptance
- Mitigation
-
An organization has implemented a policy requiring the use of conductive metal lockboxes for personal electronic devices outside of a secure research lab. Which of the following did the organization determine to be the GREATEST risk to intellectual property when creating this policy?
- The theft of portable electronic devices
- Geotagging in the metadata of images
- Bluesnarfing of mobile devices
- Data exfiltration over a mobile hotspot
-
A security analyst is using a recently released security advisory to review historical logs, looking for the specific activity that was outlined in the advisory. Which of the following is the analyst doing?
- A packet capture
- A user behavior analysis
- Threat hunting
- Credentialed vulnerability scanning
-
Which of the following would MOST likely support the integrity of a voting machine?
- Asymmetric encryption
- Blockchain
- Transport Layer Security
- Perfect forward secrecy
-
A Chief Information Security Officer (CISO) needs to create a policy set that meets international standards for data privacy and sharing. Which of the following should the CISO read and understand before writing the policies?
- PCI DSS
- GDPR
- NIST
- ISO 31000
Subscribe
0 Comments
Newest