SY0-501 : CompTIA Security+ Certification : Part 05
-
A company has three divisions, each with its own networks and services. The company decides to make its secure web portal accessible to all employees utilizing their existing usernames and passwords. The security administrator has elected to use SAML to support authentication. In this scenario, which of the following will occur when users try to authenticate to the portal? (Choose two.)
- The portal will function as a service provider and request an authentication assertion.
- The portal will function as an identity provider and issue an authentication assertion.
- The portal will request an authentication ticket from each network that is transitively trusted.
- The back-end networks will function as an identity provider and issue an authentication assertion.
- The back-end networks will request authentication tickets from the portal, which will act as the third-party service provider authentication store.
- The back-end networks will verify the assertion token issued by the portal functioning as the identity provider.
-
Which of the following is the BEST explanation of why control diversity is important in a defense-in-depth architecture?
- Social engineering is used to bypass technical controls, so having diversity in controls minimizes the risk of demographic exploitation
- Hackers often impact the effectiveness of more than one control, so having multiple copies of individual controls provides redundancy
- Technical exploits to defeat controls are released almost every day; control diversity provides overlapping protection.
- Defense-in-depth relies on control diversity to provide multiple levels of network hierarchy that allow user domain segmentation
-
A system administrator wants to provide balance between the security of a wireless network and usability. The administrator is concerned with wireless encryption compatibility of older devices used by some employees. Which of the following would provide strong security and backward compatibility when accessing the wireless network?
- Open wireless network and SSL VPN
- WPA using a preshared key
- WPA2 using a RADIUS back-end for 802.1x authentication
- WEP with a 40-bit key
-
An information security specialist is reviewing the following output from a Linux server.
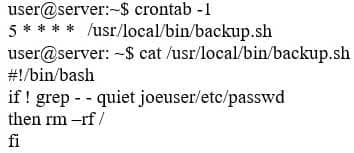
SY0-501 Part 05 Q04 014 Based on the above information, which of the following types of malware was installed on the server?
- Logic bomb
- Trojan
- Backdoor
- Ransomware
- Rootkit
-
In terms of encrypting data, which of the following is BEST described as a way to safeguard password data by adding random data to it in storage?
- Using salt
- Using hash algorithms
- Implementing elliptical curve
- Implementing PKI
-
A system administrator wants to provide for and enforce wireless access accountability during events where external speakers are invited to make presentations to a mixed audience of employees and non-employees. Which of the following should the administrator implement?
- Shared accounts
- Preshared passwords
- Least privilege
- Sponsored guest
-
Which of the following would MOST likely appear in an uncredentialed vulnerability scan?
- Self-signed certificates
- Missing patches
- Auditing parameters
- Inactive local accounts
-
A security analyst observes the following events in the logs of an employee workstation:
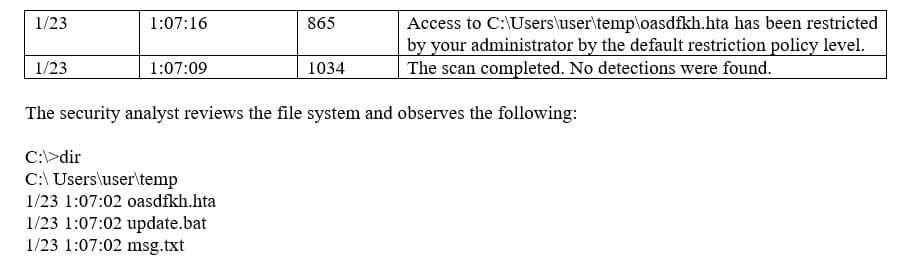
SY0-501 Part 05 Q08 015 Given the information provided, which of the following MOST likely occurred on the workstation?
- Application whitelisting controls blocked an exploit payload from executing.
- Antivirus software found and quarantined three malware files.
- Automatic updates were initiated but failed because they had not been approved.
- The SIEM log agent was not tuned properly and reported a false positive.
-
When identifying a company’s most valuable assets as part of a BIA, which of the following should be the FIRST priority?
- Life
- Intellectual property
- Sensitive data
- Public reputation
-
An organization needs to implement a large PKI. Network engineers are concerned that repeated transmission of the OCSP will impact network performance. Which of the following should the security analyst recommend is lieu of an OCSP?
- CSR
- CRL
- CA
- OID
-
When considering a third-party cloud service provider, which of the following criteria would be the BEST to include in the security assessment process? (Choose two.)
- Use of performance analytics
- Adherence to regulatory compliance
- Data retention policies
- Size of the corporation
- Breadth of applications support
-
Which of the following occurs when the security of a web application relies on JavaScript for input validation?
- The integrity of the data is at risk.
- The security of the application relies on antivirus.
- A host-based firewall is required.
- The application is vulnerable to race conditions.
-
An analyst is reviewing a simple program for potential security vulnerabilities before being deployed to a Windows server. Given the following code:
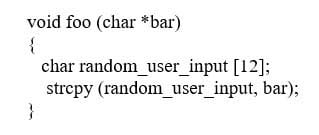
SY0-501 Part 05 Q13 016 Which of the following vulnerabilities is present?
- Bad memory pointer
- Buffer overflow
- Integer overflow
- Backdoor
-
An organization’s file server has been virtualized to reduce costs. Which of the following types of backups would be MOST appropriate for the particular file server?
- Snapshot
- Full
- Incremental
- Differential
-
A wireless network uses a RADIUS server that is connected to an authenticator, which in turn connects to a supplicant. Which of the following represents the authentication architecture in use?
- Open systems authentication
- Captive portal
- RADIUS federation
- 802.1x
-
An employer requires that employees use a key-generating app on their smartphones to log into corporate applications. In terms of authentication of an individual, this type of access policy is BEST defined as:
- Something you have.
- Something you know.
- Something you do.
- Something you are.
-
Adhering to a layered security approach, a controlled access facility employs security guards who verify the authorization of all personnel entering the facility. Which of the following terms BEST describes the security control being employed?
- Administrative
- Corrective
- Deterrent
- Compensating
-
A security analyst is hardening a web server, which should allow a secure certificate-based session using the organization’s PKI infrastructure. The web server should also utilize the latest security techniques and standards. Given this set of requirements, which of the following techniques should the analyst implement to BEST meet these requirements? (Choose two.)
- Install an X- 509-compliant certificate.
- Implement a CRL using an authorized CA.
- Enable and configure TLS on the server.
- Install a certificate signed by a public CA.
- Configure the web server to use a host header.
-
A manager wants to distribute a report to several other managers within the company. Some of them reside in remote locations that are not connected to the domain but have a local server. Because there is sensitive data within the report and the size of the report is beyond the limit of the email attachment size, emailing the report is not an option. Which of the following protocols should be implemented to distribute the report securely? (Choose three.)
- S/MIME
- SSH
- SNMPv3
- FTPS
- SRTP
- HTTPS
- LDAPS
-
An auditor is reviewing the following output from a password-cracking tool:
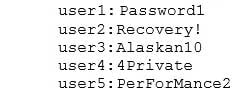
SY0-501 Part 05 Q20 017 Which of the following methods did the auditor MOST likely use?
- Hybrid
- Dictionary
- Brute force
- Rainbow table
Subscribe
0 Comments
Newest